Sleuthing the SEC’s SIM swap incident: Which carrier was involved?

A little sleuthing on the SEC’s SIM swap attack indicates that the mobile carrier involved in that incident is likely the one that accounted for 98% of the agency’s mobile phone spending in 2020.

On January 9, the Twitter account of Gary Gensler, Chairman of the Securities and Exchange Commission (SEC), notified the public that “The @SECGov Twitter account was compromised, and an unauthorized tweet was posted. The SEC has not approved the listing and trading of spot bitcoin exchange-traded products.”
The errant tweet jumped the gun by two days in announcing the SEC’s much-anticipated approval of a Bitcoin ETF. Twitter’s @Safety account immediately confirmed the breach, pointing the finger mainly at a SIM swapper, saying, “Based on our investigation, the compromise was not due to any breach of X’s systems, but rather due to an unidentified individual obtaining control over a phone number associated with the @SECGov account through a third party. We can also confirm that the account did not have two-factor authentication enabled at the time the account was compromised.”
On January 12, the SEC said it was working with appropriate law enforcement and federal oversight entities, including the SEC’s Office of Inspector General, the Federal Bureau of Investigation, and the Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency, among others, in investigating the incident. On January 22, the SEC confirmed that an unauthorized party “obtained control of the SEC cell phone number associated with the account in an apparent ‘SIM swap’ attack.”
The Commission added, “Access to the phone number occurred via the telecom carrier, not via SEC systems. SEC staff have not identified any evidence that the unauthorized party gained access to SEC systems, data, devices, or other social media accounts.” The SEC further confirmed that it disabled two-factor authentication on X in July of 2023, and it remained disabled until after January 9, but 2FA is now enabled for all accounts that offer it.
For a month now, the SEC has been silent on the details surrounding the SIM swap, including which carrier was involved and how the SIM swap occurred. Although the SEC didn’t identify the phone carrier, a little sleuthing indicates that it’s likely the carrier that accounted for 98% of mobile phone spending for the Commission in 2020.
SIM swap track records of the major carriers
Of the top three mobile carriers in the US, T-Mobile has the worst public track record for enabling SIM swaps. Last August, security consulting giant Kroll pointed to T-Mobile’s transfer of an employee’s phone number to a threat actor without any contact with the company or its employees. This swap led to the theft of user information for multiple cryptocurrency platforms that relied on Kroll services in their ongoing bankruptcy proceedings.
Last November, Ethereum co-founder Vitalik Buterin’s Twitter account was hijacked, and victims were scammed out of $691,000 because T-Mobile enabled the threat actor to take over his account via a SIM swap.
These high-profile incidents cap a long history of complaints against T-Mobile for lax standards that lead to SIM swaps. The company faces a history of SIM swap complaints that ultimately led to a major class-action lawsuit that is still pending.
Verizon and AT&T have better track records regarding SIM swaps but have also experienced their fair share of public incidents and lawsuits, including SIM attacks from an international cybercrime group. In one highly publicized incident, the SIM swapper allegedly bribed an AT&T employee in an incident that led to the theft of $24 million in cryptocurrency.
The growing rash of SIM swaps across all carriers prompted the US Federal Communications Commission to adopt new rules in November 2023 to require wireless providers to adopt more secure authentication methods.
So which telco is it?
On September 20, 2020, the SEC’s Office of Inspector General released the results of its audit of the Commission’s use of mobile devices and services. Primarily focused on the SEC’s management of mobile costs, the IG’s report said that between October 2018 and December 2019, the SEC spent nearly $5 million on about 6,300 mobile devices and associated services.
One passage in that report presents, with names redacted, the three wireless service providers, or WSPs, with which the SEC has contracts under the FSSI’s Wireless Blanket Purchase Agreement. These service providers are designated WSP1, WSP2, and WSP3. The report states that 98% of the total spending went to WSP1.
Given that AT&T, Verizon, and T-Mobile offer 100% coverage in the DC metro area and all three are participants in the blanket purchase agreement, each likely represents the top WSPs cited by the IG.
An examination of the redactions in the IG’s report yields clues that WSP1, the carrier with 98% of the SEC’s mobile phone business, is AT&T. (The Wall Street Journal reported that “records show” AT&T is the main provider of wireless services to the SEC).
Looking at the size of the redaction boxes, WSP1 has the smaller box, corresponding to the four characters in “AT&T.” In contrast, WSP2’s redaction box corresponds to seven characters, matching the number of characters in Verizon, while WSP3’s reaction box corresponds to eight characters, matching the number of characters in T-Mobile.
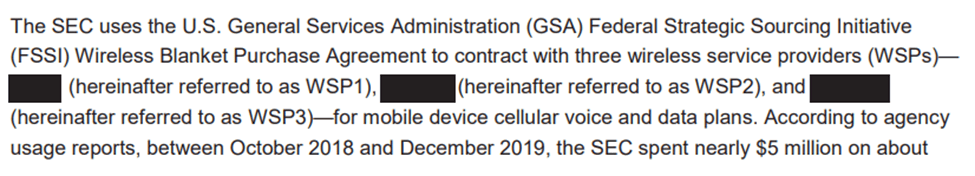
You can judge by counting the characters in the text above the redacted boxes, including spaces. (I also played around with graphical images of the redacted boxes with the matching character number redacted boxes on Redactle.net and lined them up as a not-scientific check.) In any case, WSP1 has the least number of characters redacted, which almost certainly means it’s AT&T.
I contacted an AT&T communications and PR director seeking comment. I told her that based on the carrier’s overwhelming share of the SEC’s mobile communications budget, I could only conclude that the SIM swapper very highly likely gained access to the SEC device via AT&T. She asked what my deadline was and the publication I was writing for, but then never responded after that.
I also shared my conclusion with the SEC. A spokesman responded, “We decline to comment beyond our already promulgated public statements on this matter.”
I point out that AT&T likely executed the SIM swap, not to shame it. It’s a tough hurdle for any carrier to spot SIM swappers working with all the correct account information and data, likely gleaned from data breaches or through social engineering.
But it’s been a month since we last heard from the SEC on this incident, and the odds are that the agency wants this matter to fade away quietly. However, a law enforcement investigation is underway, which could delay the release of any details about the event. However, given that a bad actor duped a powerful government agency into what appeared to be a next-level manipulation of financial assets, more details are warranted.
Greater transparency could help other government offices establish more effective policies on how employees can protect themselves against SIM swap attacks and safeguard the relevant information that led to the swap.
Among the other steps all government agencies could take is more significant guidance to employees on data sharing on internet platforms. Stay tuned for more on this.