Anthropic case puts courts at center of fight over AI supply chain authority
Iran officials tied to cyber ops killed in airstrikes, Bennett and Brassard win Turing Award, Japan to allow offensive operations starting Oct. 1, Tech giants pledge to help open source with AI bug surge, Apple patches WebKit flaw, Chinese hacker group steals $7m posing as a cyber firm, much more


If you rely on Metacurity to make sense of cybersecurity policy, industry developments, and security research, please consider supporting the newsletter with a paid subscription.
Metacurity is a daily infosec intelligence layer written independently of vendor marketing, PR-driven threat intelligence, and the cyber media echo chamber. Paid subscriptions make it possible to keep producing clear, straightforward analysis every day. Please consider upgrading your subscription. Thank you!
The Trump administration defended its decision to ban AI company Anthropic in a US federal court filing, arguing that the designation as a national security or supply chain risk falls squarely within executive authority to restrict technologies deemed sensitive.
Government lawyers said the move was based on classified and open-source intelligence assessments and is consistent with broader efforts to limit potential foreign influence or vulnerabilities in critical AI systems.
Anthropic, which has challenged the designation, contends the ban is arbitrary, economically damaging, and unsupported by sufficient evidence, effectively cutting it off from key government contracts and commercial partnerships. The company argues that the action threatens its business viability and undermines US competitiveness in artificial intelligence, particularly as federal agencies and contractors move to distance themselves from restricted vendors.
The case now centers on whether courts can meaningfully review national security-driven technology restrictions or must defer to the executive branch. Legal experts say the dispute could set an important precedent for how AI companies are evaluated and regulated in national security contexts, especially as governments increasingly scrutinize AI supply chains.
Separately, the Pentagon is preparing for a shift that would allow artificial intelligence companies to train their models on classified government data, according to a senior Defense Department official cited by MIT Technology Review. The goal is to make AI systems more useful for military applications, since models trained only on public or unclassified data lack the context needed for real-world defense scenarios, including intelligence analysis and operational planning.
To enable this, officials envision AI firms working within secure, classified environments where sensitive data can be used to refine models while maintaining strict controls. (Jack Queen / Reuters and James O'Donnell / MIT Tech Review)
Related: Court Listener, Wired, CNN, Bloomberg
US and Israeli airstrikes killed two Iranian officials tied to cyber operations, but the strikes did not significantly disrupt Iran’s ability to conduct hacking campaigns.
One was Mohammad Mehdi Farhadi Ramin, who the Justice Department charged in 2020 with hacking into aerospace and defense companies in America and had been sought by US authorities since then.
The other was Seyed Yahya Hosseiny Panjaki, a deputy minister of intelligence for Israeli affairs at MOIS, who is on the FBI Most Wanted list. Cybersecurity sources say that Panjaki was in charge of the MOIS unit that controlled hacking groups like Handala, long known as a pro-Iranian crew that has successfully targeted Israeli politicians and Western businesses. According to the FBI, Panaki was linked to terror plots and cyberattacks organized by MOIS and Iran's Islamic Revolutionary Guard Corps.
The operation had raised expectations that removing senior cyber-linked figures would weaken Tehran’s digital capabilities.
Instead, Iranian-linked hacking groups continued operations in the aftermath, launching attacks against US and allied targets. The persistence of these campaigns suggests Iran’s cyber ecosystem is distributed across multiple units and affiliated groups that can continue functioning even when key individuals are removed. (Thomas Brewster / Forbes)
Related: Axios, Iran International, National Today
The Association for Computing Machinery, the world’s largest society of computing professionals, announced that Charles Bennett and Gilles Brassard, the creators of quantum computing and related technologies, have won the Turing Award.
The Turing Award, which was introduced in 1966, is often called the Nobel Prize of computing, and it includes a $1 million prize, which the two scientists will share.
In recent years, companies like Google and Microsoft have made great strides toward building a new kind of computer, called a quantum computer, which also relies on the counterintuitive properties of quantum mechanics. Experts believe that such a machine will soon be powerful enough to crack the encryption techniques that have guarded the world’s secrets since the 1970s.
If that happens, governments, businesses, and even individuals will need the cryptographic techniques developed by Dr. Bennett, 82, a researcher at an IBM computer science lab in Yorktown, N.Y., and Dr. Brassard, 70, a professor at the University of Montreal. (Cade Metz / New York Times)
Related: Quanta Magazine, CNN, Wired, IBM Research, Quantum Insider, PR Newswire
Japan will allow its Self-Defense Forces to conduct offensive cyber-operations starting October 1, in a major shift in national security policy.
Chief Cabinet Secretary Minoru Kihara said the move reflects a worsening threat environment and the growing impact of cyberattacks on daily life and the economy.
A government cyber-management committee will approve operations, enabling police and the Self-Defense Forces to attack infrastructure used in cyberattacks while maintaining privacy safeguards. The policy builds on recent legislation and further reinterprets Article 9 of Japan’s 1946 constitution, which limits military activity to self-defense.
The move aligns Japan with other nations that have offensive cyber capabilities, though the International Institute for Strategic Studies ranks it below top-tier cyber powers such as the United States and behind second-tier countries including Australia, Canada, China, France, Israel, Germany, and the Netherlands. (Simon Sharwood / The Register)
Related: Prime Minister's Office of Japan
Six tech giants — Anthropic, AWS, GitHub, Google, Microsoft, and OpenAI — have collectively pledged $12.5 million to help open source maintainers cope with a surge of AI-generated bug reports.
The Linux Foundation's Alpha-Omega project and the Open Source Security Foundation will administer the effort, though specific plans and timelines haven't been disclosed.
The Python Software Foundation raised the alarm in late 2024, and cURL maintainer Daniel Stenberg recently shuttered the project's bug bounty program over AI-generated submission volume. Linux kernel developer Greg Kroah-Hartman welcomed the initiative while noting that money alone won't solve the underlying issue. (Simon Sharwood / The Register)
Related: Developer Tech News, The Keyword, Neowin, Alpha Omega, Phoronix, SecurityWeek
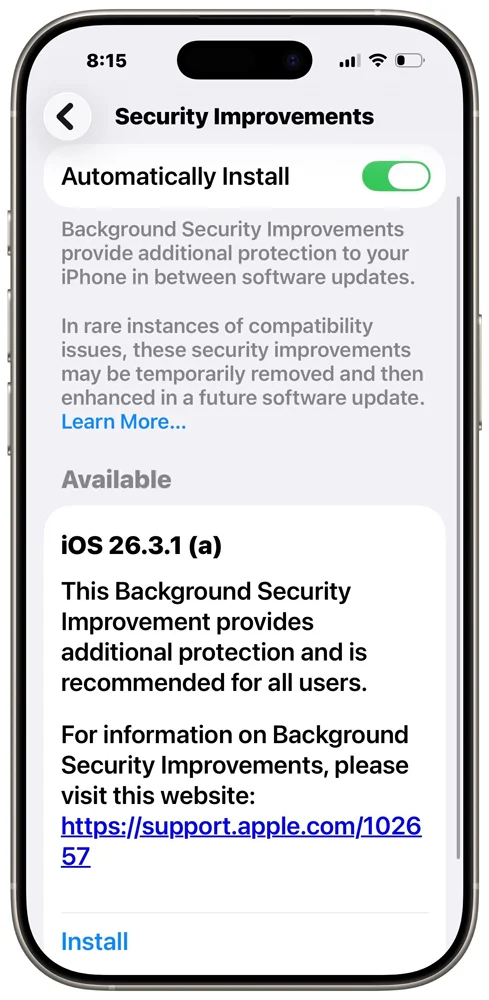
Apple has patched a WebKit flaw — CVE-2026-20643, discovered by researcher Thomas Espach — that allowed malicious web content to bypass the browser's Same Origin Policy.
The fix is notable for being the first delivered via Apple's new Background Security Improvements feature, which pushes lightweight patches to components like Safari and WebKit without requiring a full OS update or device restart.
The update is available on iOS 26.3.1, iPadOS 26.3.1, macOS 26.3.1, and macOS 26.3.2. The feature, introduced in iOS/iPadOS/macOS 26.1, can be found under Privacy & Security in device settings.
Apple warns that uninstalling a background update reverts the device to its baseline OS security level, stripping out any incremental fixes applied through the feature. (Lawrence Abrams / Bleeping Computer)
Related: Apple, 9to5Mac, Apple Insider, MacRumors, TechCrunch, Engadget
A Chinese hacker group operating behind the fake corporate front of a nonexistent cybersecurity company called Wuhan Anshun Technology allegedly stole $7 million in crypto across 37 token types by compromising Electron-based wallet clients and browser plugins to exfiltrate mnemonic phrases.
Targets included Trust Wallet, with funds laundered across Ethereum, BNB Chain, Arbitrum, and other networks.
The operation unraveled after an internal dispute over profit splits and unpaid severance, prompting a disgruntled member to leak details publicly and claim they intend to turn themselves in. Authorities have not confirmed the allegations or disclosed any investigation. (Andrew Folkler / crypto.news)
Related: Binance Square
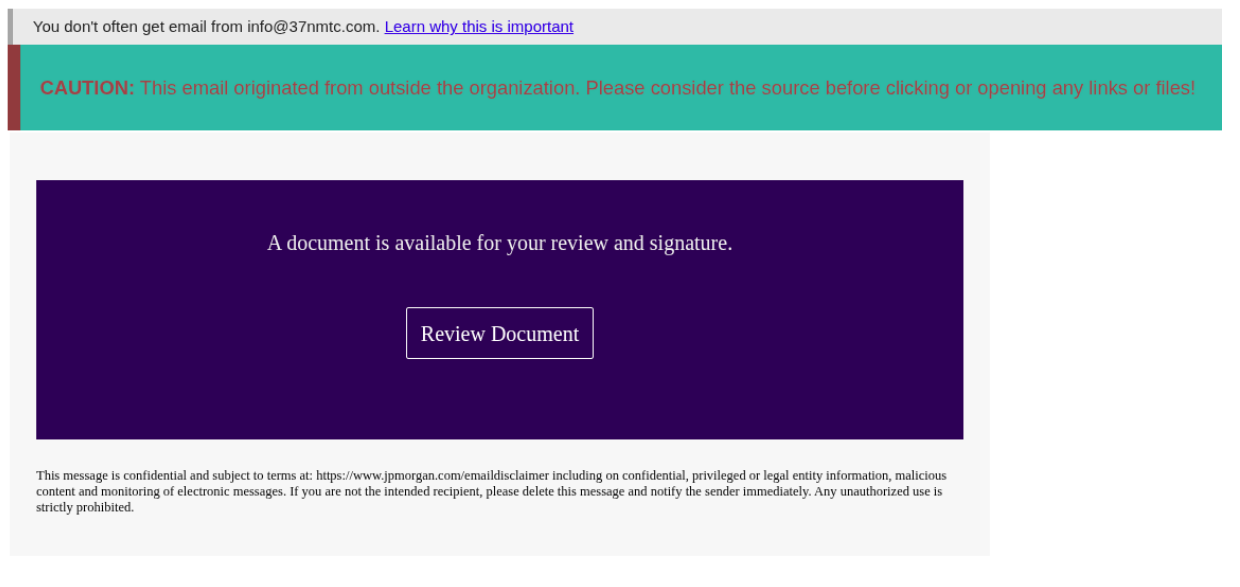
A C-level executive at Swedish security firm Outpost24 was targeted in a sophisticated phishing attack that was detected and blocked before any compromise, according to its subsidiary Specops Software.
The campaign, likely using the Kratos phishing-as-a-service kit, impersonated JP Morgan and used a multi-step chain designed to evade detection.
The attack routed victims through trusted infrastructure, including Cisco’s secure-web.cisco.com and the Nylas email API platform, before passing through a legitimate Indian company’s subdomain and a recently re-registered domain.
It ultimately led to phishing infrastructure hidden behind Cloudflare, where a fake Microsoft 365 login page attempted to harvest credentials.
Specops said the operation’s use of layered redirects, DKIM authentication, and realistic login validation highlights increasing attacker sophistication. While the tactics resemble those used by Iran-linked groups targeting US entities, the company said attribution remains uncertain. (Ionut Arghire / Security Week)
Related: Specops, Dark Reading, SC Media
Health information network Health Gorilla improperly accessed patient records at Pittsburgh-based UPMC by falsely claiming authorization through a national medical data exchange, UPMC said.
Potentially exposed data includes names, ages, diagnoses, and medical histories, though Social Security numbers were not compromised. UPMC has reported the incident to the HHS Office for Civil Rights.
The breach follows a federal lawsuit filed in January by Epic and several health systems accusing Health Gorilla of fraudulently accessing tens of thousands of patient records and allegedly routing them to mass tort litigation marketing services. Health Gorilla has denied the allegations, framing the action as part of Epic's efforts to undermine health data interoperability. (Naomi Diaz / Health IT)
Related: UPMC, Modern Healthcare, WGAL
In March 2026, the online safety service Aura disclosed a data breach that exposed 900,000 unique email addresses.
The data was primarily associated with a marketing tool from a previously acquired company, with fewer than 20k active Aura customers affected. Exposed data included names, phone numbers, physical and IP addresses, and customer service notes. Aura advised that no Social Security numbers, passwords, or financial information were compromised. (HaveIBeenPwned)
Related: Aura
Alex Fitzsimmons, the under secretary of energy at the US Department of Energy and director of its Office of Cybersecurity, Energy Security, and Emergency Response (CESER), said the agency is, for the first time, planning to release a strategic plan to lay out how the department intends to protect the energy grid better.
He said the plan is meant to supplement the recently published national cyber strategy and will focus on how the agency will strengthen the “security and resilience” of the energy sector.
The importance of partnerships with the private sector and how to bolster them will be at the heart of the strategic plan, Fitzsimmons said.
“Private sector [companies] are largely responsible for defending their networks — we have to do that partnership,” Fitzsimmons said at the McCrary Cyber Summit in Washington, DC. “We have to be able to get timely and actionable information out to them so that they can secure their networks.” (Suzanne Smalley / The Record)
Related: Federal News Network
US cyber officials said CISA and the FBI have been working directly with Stryker staff following a recent cyberattack that disrupted systems and wiped devices, as the company continues recovery efforts.
Speaking at the McCrary Cyber Summit, acting CISA Director Nick Andersen said the incident reflects ongoing cyber activity tied to geopolitical tensions, though threat levels remain steady rather than escalating.
The attack, claimed by the pro-Iranian group Handala, underscores the continued risk to private-sector organizations, particularly those tied to critical infrastructure. Andersen emphasized that a range of actors—not just nation-states—are actively conducting cyber operations, reinforcing the need for sustained defensive readiness.
At the same event, National Cyber Director Sean Cairncross outlined the administration’s evolving cyber strategy, centered on a more coordinated, government-led approach to offensive operations. He described plans for closer alignment across agencies, including the Justice Department, State Department, FBI, and Pentagon.
Cairncross stressed that private companies will not be expected to carry out offensive cyber operations themselves, but will play a key role in supporting government efforts through information sharing and stronger defenses, as part of a broader push to integrate public and private sector cyber capabilities. (David DiMolfetta / NextGov/FCW and Tim Starks / CyberScoop)
Related: CyberScoop, Wall Street Journal
Israeli startup Tenzai says its AI hacker outperformed 99% of the 125,000 human competitors across six capture-the-flag cybersecurity competitions earlier this month.
The system, built on tuned models from OpenAI and Anthropic, tackled both traditional web application exploits and newer AI-focused challenges, and cost just $5,000 to run across all six events.
Tenzai CEO Pavel Gurvich says the AI showed unexpected proficiency at chaining together multiple software exploits — previously hard to automate — and argues that AI-driven offensive hacking now works at scale. He warned that the capability is fast-moving beyond governments and intelligence agencies, and called for regulation limiting access to highly capable hacking models. (Thomas Brewster / Forbes)
Related: Access Newswire
Surf AI, a NYC-based provider of an agentic operations platform for modern security teams, raised $57 million in funding.
Accel led the round, with participation from existing investors Cyberstarts and Boldstart Ventures. (Chris Metinko / Axios)
Related: Globes, FinSMEs, The SaaS News, FinTech Global, Security Week, GovInfoSecurity, The Jerusalem Post, Silicon Angle
Best Thing of the Day: Stryker's Restoration Is Going Well
Medtech company Stryker is now in the restoration process, which is "progressing steadily," following its attack by an alleged Iranian hacking group.
Worst Thing of the Day: The EU Is a Heck of a Lot Safer Than the US Congress
The US Congress Judiciary Committee is pushing technology companies to provide access to all communications with European Commission officials that relate to the enforcement of EU digital rules.
Bonus Worst Thing of the Day: Piling Bad on Top of Bad
World, known as WorldCoin until late 2024, announced that it was opening a limited beta of its new AgentKit that will serve as a way to tie AI agents directly to a human to prevent bad actors from abusing agentic AI and "infuse trust into the system."
Closing Thought