Anthropic says Chinese AI companies siphoned its info using 24,000 fake accounts


CrowdStrike’s latest annual Global Threat Report finds AI-driven attacks up 89%, zero-day exploitation surging, and nation-state actors doubling down on cloud and edge device compromise. Check out more in my latest CSO piece on The Rise of the Evasive Adversary.
Metacurity is a daily intelligence layer for people who must stay current on the critical happenings in the cybersecurity realm.
We scan thousands of sources on the web to decode the narrative, surface overlooked signals, and connect the dots others miss.
Every day, Metacurity delivers independent, analytical, and daily intelligence that sits outside the cybersecurity echo chamber and reputation economy of other newsletters. Along with the headline-grabbing news items, Metacurity delivers news of developments you won't see in other cybersecurity newsletters.
Please consider supporting Metacurity's continued existence by upgrading your subscription. Thank you.
US artificial intelligence startup Anthropic said three Chinese AI companies set up more than 24,000 fraudulent accounts with its Claude AI model to help their own systems catch up.
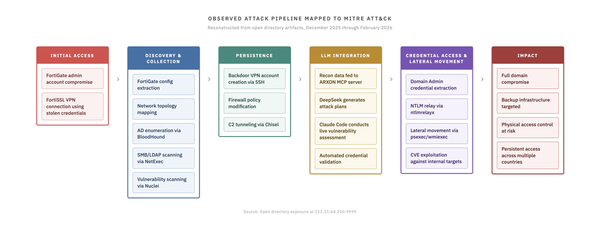
The three companies—DeepSeek, Moonshot AI, and MiniMax—prompted Claude more than 16 million times, siphoning information from Anthropic’s system to train and improve their own products, Anthropic said in a blog post Monday.
Earlier this month, an Anthropic rival, OpenAI, sent a memo to House lawmakers accusing DeepSeek of using the same tactic, called distillation, to mimic OpenAI’s products.
Anthropic said distillation had legitimate uses—companies use it to build smaller versions of their own products, for example—but it could also be used to build competitive products “in a fraction of the time, and at a fraction of the cost.”
The scale of the different companies’ distillation activity varied. DeepSeek engaged in 150,000 interactions with Claude, whereas Moonshot and MiniMax had more than 3.4 million and 13 million, respectively, Anthropic said. (Robert McMillan and Raffaele Huang / Wall Street Journal)
Related: Reuters, Bloomberg, Anthropic, CyberScoop, Insider Paper, Financial Times, New York Times
World Liberty Financial, the digital-asset venture backed by the Trump family, said that it defeated an unspecified “coordinated attack” against its flagship cryptocurrency product.
USD1, the dollar-pegged stablecoin issued by World Liberty, briefly traded below $1 on Monday before climbing back to par, according to crypto data tracker CoinGecko. Stablecoins are typically designed to trade at a rate equal to the dollar to provide users with a stable medium of exchange and to serve as a store of value within the highly volatile crypto market.
The stablecoin, which has a market value of about $5 billion, is the first product launched by the crypto project co-founded by Donald Trump Jr. and Eric Trump alongside the sons of White House special envoy Steve Witkoff. The project lists President Donald Trump as “co-founder emeritus.”
“A coordinated attack was launched against USD1 this morning,” the project said on its official account on X. “Attackers hacked several WLFI cofounder accounts, paid influencers to spread FUD, and opened massive $WLFI shorts to profit from the manufactured chaos.”
“World Liberty’s elite engineering and security teams today successfully repelled a coordinated attack from multiple vectors,” according to a statement from a World Liberty spokesperson. (Muyao Shen / Bloomberg)
Related: Decrypt, CoinDesk, Bitget, The Street, Benzinga, CoinPedia, CryptoBriefing, Bitcoin.com, ZyCrypto
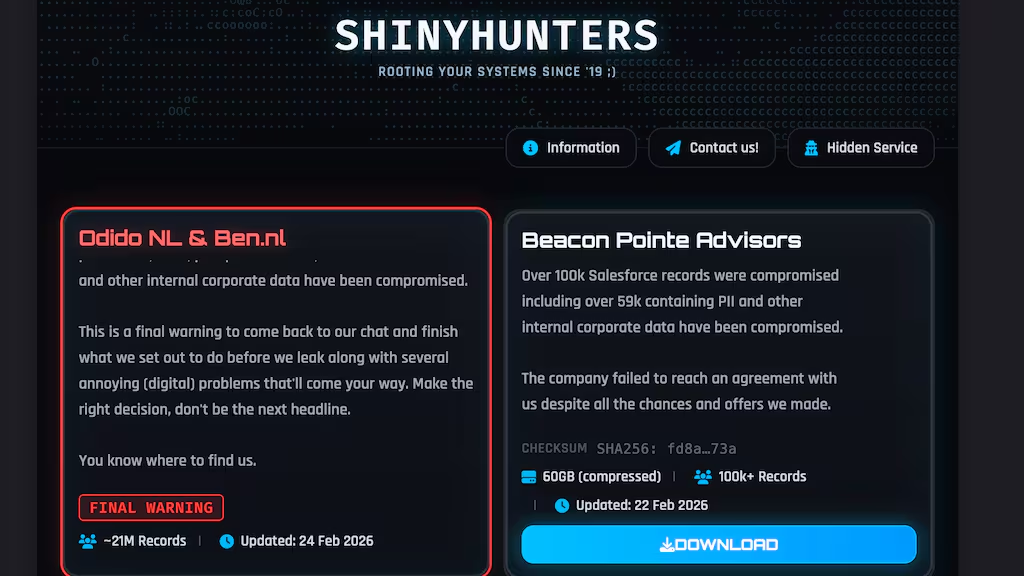
The cybercriminal group Shinyhunters claimed responsibility for hacking the Netherlands largest phone company, Odido, and says it has stolen the data of 8 million people, not 6.2 million like Odido claims, and is pressuring Odido to pay a ransom of over €1 million, or they’ll leak the stolen data.
The group is threatening to publish the stolen customer data, including names, addresses, bank account numbers, and passport numbers, on the dark web. The cybercriminals also claim to have customer passwords. “It affects 8 million customers and a total of 21 million lines of data.”
The hackers have issued a statement to Odido, saying, "Make the right decision, you know where to find us." Shinyhunters says the company's deadline is next Thursday morning. The asking price is "a low seven-figure sum." (Daniel Verlaan / RTL)
Related: Odido, Dutch News, Bleeping Computer, NL Times
Harold Rogers, the interim CEO of e-commerce giant Coupang, gave a closed-door deposition before the US House Judiciary Committee over a data breach affecting more than 33 million Korean users, as the US-listed company faces scrutiny in Seoul over the data leak.
The leak refers to the exposure of personal data — including names, phone numbers, and delivery addresses — of more than 33 million users in a hacking incident that Coupang first detected in November last year. Following the discovery, Korean regulators began a formal investigation into possible violations of domestic data protection laws, ordered the company to submit corrective measures, and considered what penalties to impose on the company.
Rogers appeared at 9:42 a.m. at the Rayburn House Office Building in Washington. Congressional aides, professional staff, and lawyers attended the closed-door deposition, which lasted roughly seven hours. He left the building at around 5 p.m. (KANG TAE-HWA / KoreaJoongAng Daily)
Related: The Korea Herald, The Chosun Daily, The Korea Times, Maeil Business Newspaper, Business Korea, AJP News Agency
Researchers at Abnormal Security have uncovered a new phishing kit that proxies live login pages, bypasses MFA, and includes a full credential-harvesting platform for a monthly fee.
While most phishing kits rely on static HTML clones of login pages, these are inherently fragile, as even minor interface updates from the impersonated brand can reveal the deception immediately.
However, a new framework called Starkiller – not to be confused with the legitimate BC-Security red team tool of the same name – does things differently.
"Sold openly as a commercial-grade cybercrime platform by a threat group calling itself Jinkusu, Starkiller is distributed like a SaaS product," said Abnormal.
"It launches a headless Chrome instance — a browser that operates without a visible window — inside a Docker container, loads the brand’s real website, and acts as a reverse proxy between the target and the legitimate site."
Researchers found that Starkiller's control panel gives cyber criminals a polished dashboard for deploying phishing campaigns, and the core workflow requires almost no technical skill.
The package offers real-time session monitoring, allowing attackers to watch the target interact with the phishing page live.
Along with keylogger capture for every keystroke, it includes cookie and session token theft for direct account takeover, geo-tracking of targets, and automated Telegram alerts when new credentials come in. (Emma Woollacott / IT Pro)
Related: Abnormal, Krebs on Security, Infosecurity Magazine, SC Media, Dark Reading

The Conduent data breach is shaping up to be one of the biggest in history, with at least 25 million people affected in just two states.
A reported 15 million people were affected in Texas. That's roughly half the state's population. In Oregon, meanwhile, the Department of Justice reported more than 10 million people were affected by the breach at the healthcare data management provider. (Tim Marcin / Mashable)
Related: Oregon Justice Department, WFIN, WRDW/WAGT, Cyber Security News, TechRepublic, TechCrunch
New Zealand health portal MediMap was breached on Sunday, and the company has now taken the platform offline while it investigates.
Some users' information had been changed, including to say they were deceased.
MediMap is used by some health providers in aged care, disability, hospice, and the community to record medication doses accurately.
It allows clinics or aged care services to coordinate with people and pharmacies, and can be used for e-prescribing and includes people's medication histories.
"New Zealanders expect that companies involved in healthcare have secure systems and platforms that safeguard their private information," Health New Zealand's Darren Douglass said.
"As a private company, MediMap is solely responsible for ensuring the security of its platform," he said.
Douglass said Health NZ was supporting MediMap with its response and working with other relevant agencies, including the National Cyber Security Sector. (RNZ)
Related: 1News, Stuff, Insurance Business, New Zealand Herald, r/newzealand
A lending pool operated by YieldBlox on the Stellar blockchain was emptied of around $10.2 million in an oracle manipulation attack on the Reflector oracle supplying prices for the USTRY/USDC market.
Reflector has said that there was no flaw with their oracle, and that market illiquidity caused the problem. "Reflector quoted correct prices. ... but it's impossible to quote adequate prices for a market fully handled by a single market-maker with almost zero trading activity." (Molly White / Web3IsGoingJustGreat)
Related: Protos, r/cryptocurrency, Bankless, Crypto News
Researchers at Symantec report that North Korean state-backed hackers associated with the Lazarus threat group are targeting US healthcare organizations in extortion attacks using the Medusa ransomware.
Symantec says that a Lazarus subgroup, possibly Andariel/Stonefly, is now using Medusa in financially motivated cyberattacks targeting US healthcare providers.
According to the researchers, the toolset used in these attacks also shows some association with Diamond Sleet, another North Korean group that typically targets media, defense, and IT industries.
Medusa targeted multiple healthcare and non-profit organizations in the US, as the gang's data leak site lists four such victims since the beginning of November 2025, among them an educational facility for autistic children.
Not all these Medusa attacks can be confidently attributed to Lazarus hackers, though. Medusa can demand ransoms as large as $15 million, but Symantec researchers say that the average is around $260,000. (Bill Toulas / Bleeping Computer)
Related: Security.com, Bank Info Security, The Record
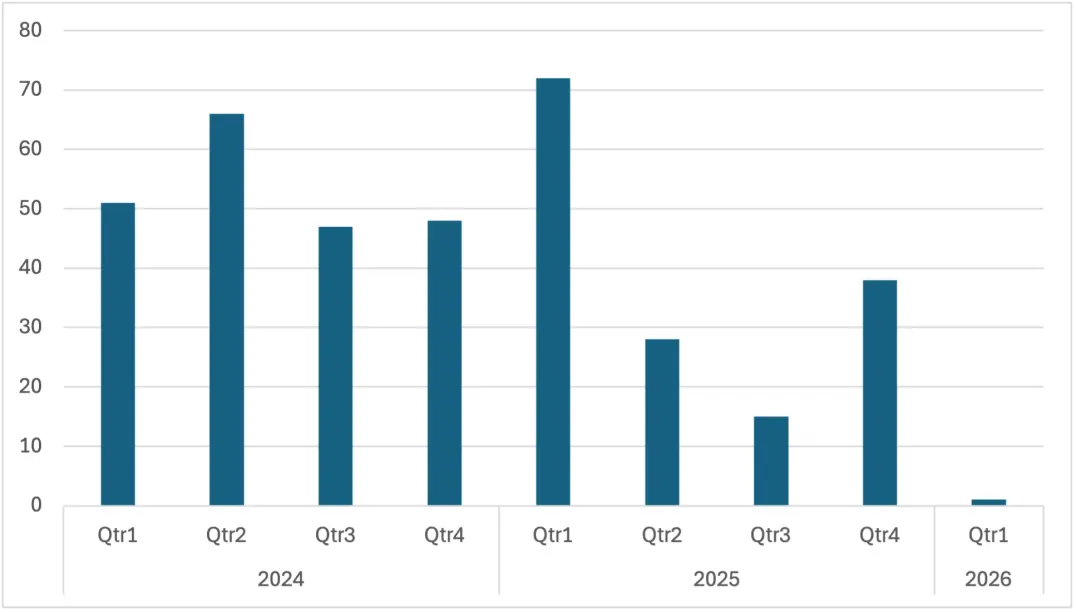
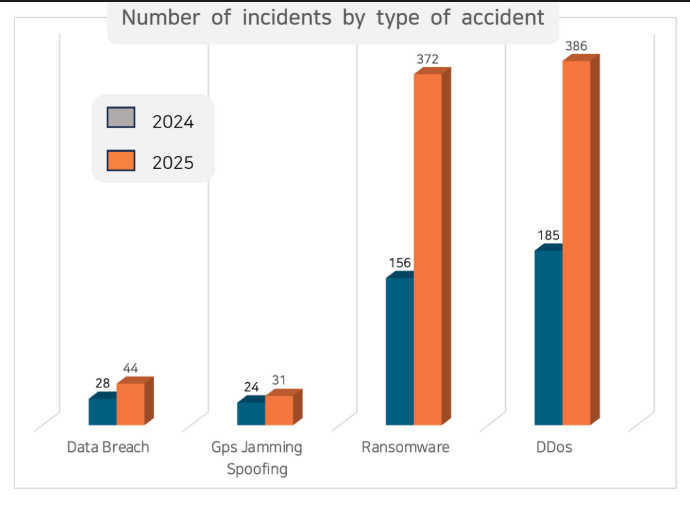
According to Korean security firm Cytu, the prevalence of maritime cyberattacks doubled in 2025, led by an explosion of malware and distributed denial of service (DDoS) incidents.
Some of the most concerning examples involved a high-level penetration of the shoreside supply chain, giving the attackers useful information about systems (or even remote access) at a fleet level. Others extended to worst-case scenarios: destroyed equipment, hacked ECDIS chart systems, and remote control of ballast valves.
Cyber threat actors are finding more ways to monetize vessel information, whether by encrypting it, holding it hostage and demanding a ransom from the operator, or by stealing it and selling it to third parties on the Dark Web.
Another common form of attack is distributed denial of service (DDoS), a brute-force swarm of automated activity that swamps a network and crowds out legitimate traffic.
Cyber threat actors are finding more ways to monetize vessel information, whether by encrypting it, holding it hostage and demanding a ransom from the operator, or by stealing it and selling it to third parties on the Dark Web.
Illicit items found for sale online include voyage logs, cargo manifests, ship design schematics and the personal information of the crew, according to Cytur.
Often, the operator will pay to avoid having their internal records released: one common ransomware attack involves encrypting the ship's Planned Maintenance System (PMS), forcing the operator to pay in order to recover the voyage's logs. Ransomware attacks and data theft are often found in high-traffic regions, like Asian waters and major hub ports, Cytur said.
Another common form of attack is distributed denial of service (DDoS), a brute-force swarm of automated activity that swamps a network and crowds out legitimate traffic. (Maritime Executive)
Related: Cytur, Smart Maritime Network, Digital Ship
Russian cyberattacks targeting Ukraine’s energy infrastructure are increasingly focused on collecting intelligence to guide missile strikes rather than immediately disrupting operations, Ukrainian cybersecurity officials said.
Although the number of major cyber incidents targeting critical infrastructure has declined, the threat itself has not diminished, according to Oleksandr Potii, head of Ukraine’s State Service of Special Communications and Information Protection.
“Cyberattacks on critical infrastructure never happen on their own; they are always part of a broader operation,” Potii said.
He said attackers now appear more focused on mapping facilities, tracking repair crews, and assessing how quickly energy systems can recover after strikes rather than causing immediate power outages.
Natalia Tkachuk, head of cyber and information security at Ukraine’s National Security and Defense Council, said cyber operations against energy facilities increasingly reflect Russia’s long-term strategy in the war. (Daryna Antoniuk / The Record)
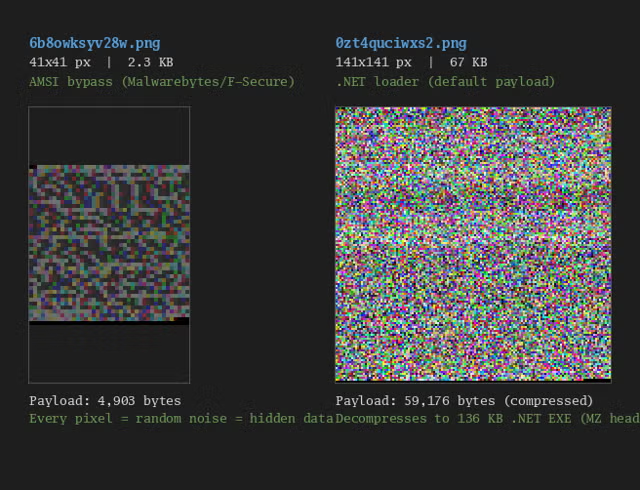
Researchers at Veracode have discovered a new type of cyberattack that uses steganography to hide a dangerous virus after they found a malicious package on NPM.
The package was named buildrunner-dev, the hackers using a typosquatting technique where they gave it a name that is almost the same as a real, safe tool called buildrunner, hoping someone would make a spelling mistake and download it by accident.
Once the package is on a computer, it runs a script that downloads a file called packageloader.bat. The file is full of random words like “raven,” “glacier,” and “monsoon” that don’t actually do anything. Out of the whole file, only about 21 lines are real commands.
The malware downloads a PNG image from a free hosting site, which, to a normal person, looks like fuzzy, grainy “noise.” However, the malware is programmed to read the tiny bits of colour data, known as RGB pixel values, to find hidden code. (Deeba Ahmed / HackRead)
Related: Veracode
Over the weekend, Summer Yue, the director of safety and alignment at Meta’s superintelligence lab, posted on Twitter that OpenClaw deleted her entire inbox despite her pleading messages to stop.
OpenClaw (née Clawdbot and Moltbot) has become a popular open-source AI agent for AI evangelists despite the pretty obvious and troubling security vulnerabilities, and Yue wanted to give it a shot. So, according to her post, she set up a Mac Mini running the agent and offered it access to her inbox.
“Nothing humbles you like telling your OpenClaw ‘confirm before acting’ and watching it speedrun deleting your inbox,” she wrote. “I couldn’t stop it from my phone. I had to RUN to my Mac mini like I was defusing a bomb.”
OpenClaw basically went full HAL 9000 on Yue, pulling up just short of saying, “I’m sorry Summer, I’m afraid I can’t do that.” She shared screenshots of her conversation with the agent, showing her begging it to stop and being ignored, concluding with the bot acknowledging that it remembered being told not to delete anything without approval and “violated” that order anyway. (AJ Dellinger / Gizmodo)
Related: TechCrunch, The Times of India, Business Insider, India Today, Fortune, The Verge, PC Gamer, Dataconomy
The UK's data protection watchdog has scored a small win in a lengthy legal battle against a British retail group that lost millions of data records during a 2017 breach after a British appeals court ruled in its favor.
The Information Commissioner's Office (ICO) originally fined DSG Retail £500,000 ($673,000) in 2020, the maximum financial penalty allowed under the Data Protection Act 1998 (DPA 1998) – the relevant legislation at the pre-GDPR time.
Its monetary penalty notice (MPN) was upheld by the Court of Appeal's first-tier tribunal but later reversed by the upper tribunal [PDF], which sided with DSG Retail and, if that decision were final, would have effectively nullified the ICO's fine. (Connor Jones / The Register)
Related: ICO, Judiciary.uk, SC Media, DataGuidance,
A cyberattack at Hazeldenes chicken meat processing plant in central Victoria, Australia, has stalled production, leaving businesses across the state short on supply.
Hazeldenes says it is working with cybersecurity investigators to identify the cause, although workers say problems with the company's computer systems began last week. (Tyrone Dalton, Timu King, Mildura-Swan Hill / ABC.net.au)
Related: Cyber Daily
Best Thing of the Day: Montana Isn't Taking Any Chances
The Montana National Guard has appointed its first cyber warfare officer, marking a significant advancement in the guard’s cyber capabilities and proactive defense.
Bonus Best Thing of the Day: Better Late Than Never
The Energy Department recently fixed an identity verification flaw in a portal supporting its critical minerals programs after a security researcher found the system allowed outside users to register with email addresses that appeared to belong to the department.
Worst Thing of the Day: Someone Should Tell the Pentagon What DOGE Did to the Civilian Sector
Elon Musk's artificial intelligence company xAI has signed an agreement to allow the military to use its model, Grok, in classified systems.