California uses AI contracts to impose safeguards, teeing up clash with Trump
Italy fines its biggest bank $36.4m over data breach, Oz launches probe into internet giants over social media ban failures, Match Group settles with FTC over unauthorized data access, JavaScript library axios became an attack vector after npm account hijacking, much more
Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting it with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
California will require artificial intelligence companies seeking state contracts to meet new safety, transparency, and civil rights standards under an executive order from Gov. Gavin Newsom, escalating a growing clash with the Trump administration over who sets the rules for AI.
The order directs state agencies to vet vendors based on their ability to prevent harms such as bias, discrimination, unlawful surveillance and the generation of illegal or abusive content, while also developing measures like watermarking to identify AI-generated material. By tying these requirements to procurement, California is using its economic leverage to impose guardrails on companies that want access to one of the world’s largest markets.
Newsom framed the move as both protective and pro-innovation, saying the state will ensure AI is not used “to exploit…data” or “violate…civil rights,” and pledging to use its authority to make companies “protect people’s rights, not exploit them.”
The directive comes as the Trump administration pushes the opposite approach: a national framework aimed at limiting state-level AI regulation in favor of a more uniform, industry-friendly system. Federal officials have argued that a patchwork of state laws could hinder innovation, while California and other states contend that waiting for Washington risks leaving major harms unaddressed.
California’s order signals it will not defer to federal efforts to rein in state authority, and may independently assess which AI companies pose risks, even when the federal government takes a different view. (Cecilia Kang / New York Times, Cecilia Kang / New York Times, Governor Gavin Newsom)
Related: Reuters, Courthouse News Service, CNET, ABC10 on YouTube, The Guardian, Implicator.ai, KTLA
Italy's data protection authority said it fined the country's biggest bank, Intesa Sanpaolo, 31.8 million euros ($36.41 million) over a data breach case that involved around 3,500 customers over two years.
According to the agency's investigation, an Intesa employee accessed banking information of 3,573 customers, carrying out more than 6,600 consultations between February 2022 and April 2024.
"These unauthorised accesses went undetected by the bank’s internal control systems, revealing significant weaknesses in its monitoring and prevention mechanisms," the authority, known in Italy as the 'Garante', said in a statement. (Elvira Pollina /Reuters)
Related: The Record, Intesa San Paolo, Ansa, The Cyber Express
Australia’s online safety regulator has launched investigations into Meta, Snap, TikTok, and YouTube over suspected failures to enforce the country’s under-16 social media ban, marking the first formal test of Big Tech’s compliance with the world-first law.
In its initial report, the eSafety commissioner said it has “significant concerns” about enforcement gaps, including weak safeguards that allow minors to create accounts and repeatedly attempt age-verification checks until they succeed.
The probe exposes persistent workarounds by underage users and raises the prospect of penalties of up to A$49.5 million ($34 million) per company. Regulators said they have begun gathering evidence and could take enforcement action by midyear, emphasizing that platforms have the technical capability to comply but have not yet taken sufficient steps. While the number of under-16 users has declined since the law took effect in December, officials said large numbers of minors remain active on social media.
The scrutiny comes amid rising global pressure on tech companies, days after Meta and Google were found liable in a US case linking social media use to a young woman’s mental health harms—fueling comparisons to a potential “Big Tobacco” moment for the industry. Companies, including Meta, said they are working with regulators but warned that reliably verifying users’ ages remains a broader industry challenge. (Angus Whitley / Bloomberg)
Related: eSafety Commissioner, The Guardian, WION, The Register, Reuters
Match Group agreed to settle a US Federal Trade Commission lawsuit claiming it gave an outside company unauthorized access to personal data belonging to millions of users of the OkCupid dating app.
The FTC said OkCupid users were never told their information - including nearly 3 million photos, demographic information, and location data - would be shared in 2014 with Clarifai, a facial recognition technology company, contrary to OkCupid's privacy policies.
Monday's settlement in Dallas federal court prohibits Match from misrepresenting the privacy of user information and requires the Dallas-based company to certify compliance.
Match and OkCupid neither admitted nor denied wrongdoing, and could face civil fines for future violations. The settlement requires court approval. (Jonathan Stempel and Jody Godoy / Reuters)
Related: Federal Trade Commission, Engadget, Bloomberg Law, Inc.com, MediaPost
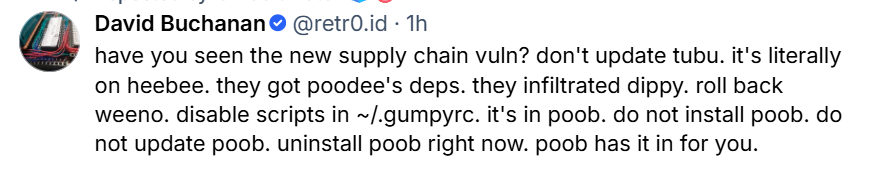
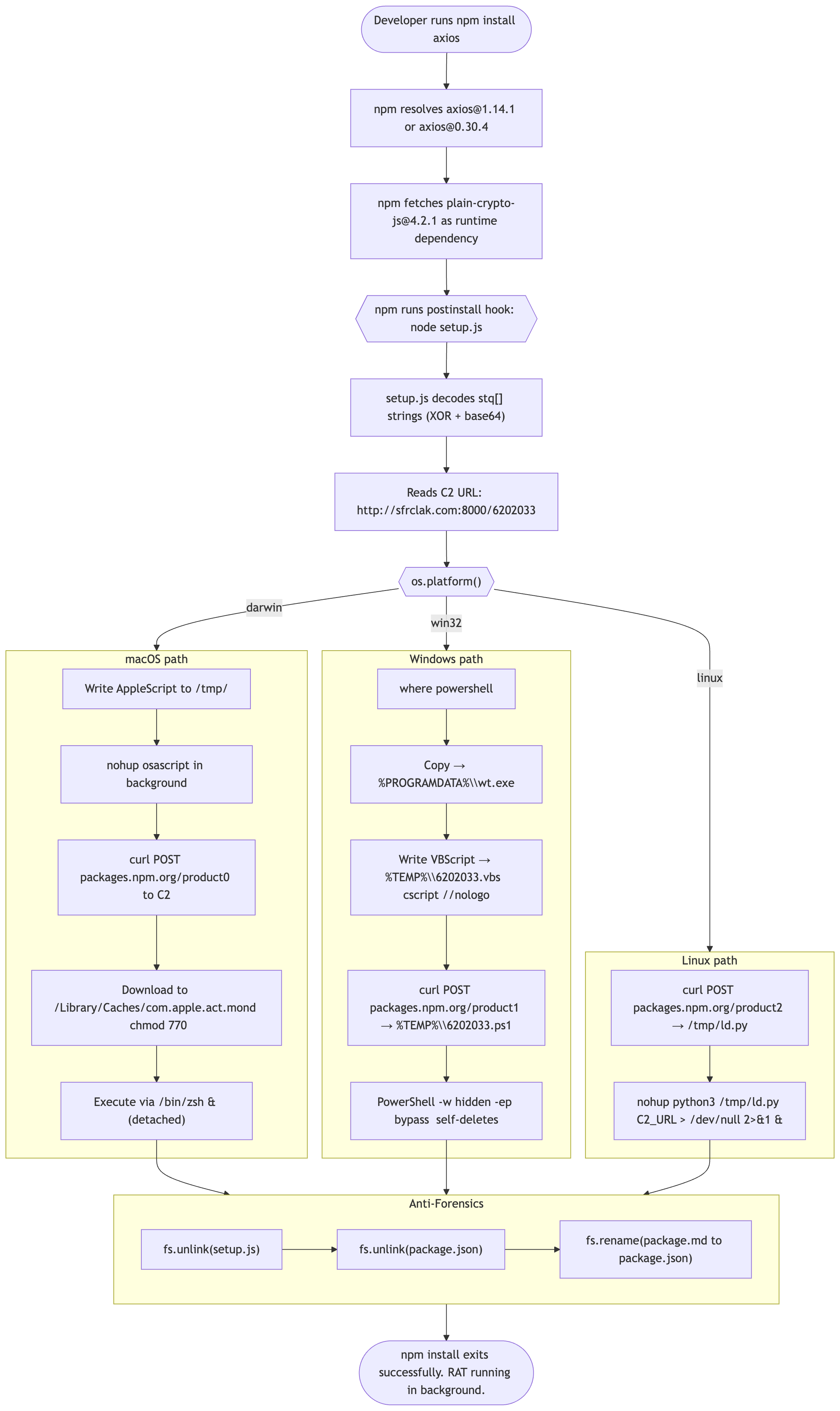
Researchers at Step Security and other firms discovered that a widely used JavaScript library, axios, briefly became a malware distribution vector after attackers hijacked a maintainer’s npm account and published two compromised versions, in what security researchers describe as one of the most significant software supply chain attacks on record.
The tainted releases, axios@1.14.1 and axios@0.30.4, were uploaded outside the project’s normal development pipeline and included a malicious dependency rather than altered core code, allowing them to appear legitimate while delivering a hidden payload.
The injected package acted as a delivery mechanism for a remote-access trojan, using post-install scripts to fetch additional malware tailored to the victim’s operating system. The attack was highly coordinated: the dependency was staged in advance, multiple payloads were prepared for different platforms, and the compromised packages were pushed within minutes of each other after attackers took control of the maintainer’s account and bypassed standard CI/CD safeguards.
The malware also attempted to evade detection by disguising itself and removing traces of its activity.
The incident highlights escalating risks in the open-source ecosystem, where widely used components can quickly propagate compromise across development environments and production systems. Developers who installed the affected versions are being urged to treat their systems as breached, rotate credentials, and potentially rebuild machines. (Carly Page / The Register)
Related: Socket Security, Step Security Blog, Snyk, CyberInsider, The Crypto Times, The Cyber Express, Daily Dark Web, Neowin, Cyber Security News, iTnews, Aikido Security's Blog, CryptoPotato, ABC 11, Piunikaweb.com
Healthcare IT firm CareCloud disclosed a data breach incident that exposed sensitive data and caused a network disruption lasting approximately eight hours.
The New Jersey-based company said in a filing with the US Securities and Exchange Commission (SEC) that the intrusion occurred on March 16 when hackers accessed its IT infrastructure.
“On March 16, 2026, CareCloud, Inc. experienced a temporary network disruption in its CareCloud Health division that partially impacted the functionality and data access to 1 of its 6 electronic health record environments for approximately 8 hours until the Company fully restored all functionality and data access during that evening,” the company says in the SEC filing.
After detecting the intrusion, CareCloud said that it reported the issue to "its cybersecurity carrier and engaged a leading cyber response advisory team, which is part of a Big Four accounting firm, to perform external cybersecurity work and to assist with securing the environment, as well as to conduct a comprehensive IT forensic investigation to determine the nature and scope of this incident.” (Bill Toulas / Bleeping Computer)
Related: The Record, The HIPAA Journal, Security Week, Cyber Press
Researchers at Reliaquest report that a new credential-stealing malware campaign dubbed “DeepLoad” is targeting enterprise IT environments, using AI-driven techniques to bypass traditional security controls and turn a single user action into persistent access.
Delivered through “QuickFix” social engineering tactics like fake browser prompts and error pages, the malware is designed to evade detection at every stage of the attack chain.
Reliaquest says the campaign’s sophistication points to AI involvement, with the loader obscuring its functionality behind massive volumes of meaningless code and running its payload through a Windows lock screen process often ignored by security tools.
The malware enables real-time keylogging and can maintain persistence even after initial remediation, including spreading via USB drives and reactivating days later through hidden mechanisms. (Derek B. Johnson / CyberScoop)
Related: Reliaquest, Dark Reading, Infosecurity Magazine, GBHackers
Hackers are exploiting a critical severity vulnerability, tracked as CVE-2026-3055, in Citrix NetScaler ADC and NetScaler Gateway appliances to obtain sensitive data.
Citrix initially disclosed CVE-2026-3055 in a security bulletin on March 23, alongside a high-severity race condition flaw tracked as CVE-2026-4368. The issue impacts versions of the two products before 14.1-60.58, versions older than 13.1-62.23, and those older than 13.1-37.262.
The vendor underlined that the flaw only affected appliances configured as a SAML identity provider (IDP) and noted that action is required only for administrators running on-premise appliances.
In response to the bulletin, multiple cybersecurity firms highlighted that CVE-2026-3055 has a significant risk, noting technical resemblance to the widely exploited ‘CitrixBleed’ and CitrixBleed2’ from 2023 and 2025, respectively.
watchTowr, a company that provides adversarial simulation and continuous testing services, said on Saturday that it observed reconnaissance activity targeting vulnerable instances and warned that in-the-wild exploitation was imminent.
The next day, the researchers confirmed that threat actors started leveraging the flaw since at least March 27.to extract authentication administration session IDs, potentially enabling a full takeover of NetScaler appliances. (Bill Toulas / Bleeping Computer)
Related: Citrix, The Register, BankInfoSecurity, Security Week, watchTowr
Starting April 1, India will ban the sale of certain Chinese-made CCTV cameras under new security certification rules, effectively blocking major vendors such as Hikvision and Dahua from the market.
The restrictions target internet-connected cameras that fail to meet updated standards, including scrutiny of chipsets and firmware, as part of a broader effort to address national security risks.
The move is expected to accelerate a shift already underway in India’s surveillance market, where domestic manufacturers have gained significant ground during a two-year transition period.
While existing installations will not be removed, non-compliant products will no longer be sold, and users may face reduced support or updates. Industry analysts also expect prices to rise as companies adjust supply chains away from lower-cost Chinese components.
The policy reflects India’s wider push to reduce dependence on Chinese technology in sensitive sectors and strengthen cybersecurity oversight. By enforcing stricter testing and disclosure requirements, authorities aim to limit potential vulnerabilities such as unauthorized remote access, while also boosting local manufacturing and reshaping competition in the surveillance industry. (Economic Times)
Related: The Times of India, First Post, WION, SQ Magazine, DNA India, Cyber Security News, NDTV, Business Standard, India Today
The FBI is investigating a recent incident in Jackson County, Indiana, after portions of the county's computer network were involved in a cyberattack.
The Jackson County Sheriff's Office said officials "began coordinating with state and federal partners to ensure systems remain secure and operational."
Officials said there's no indication any hardware, data, or taxpayer funds were lost or compromised. It's unclear how long the cyberattack impacted the county and if anything was knocked out during it.
The incident is under investigation by the FBI, U.S. Department of Homeland Security, and Indiana Department of Homeland Security, along with Jackson County officials. (WDRB)
Related: The Republic News, WHAS, WBIW
Alamo Heights Independent School District in Texas confirmed that a ransomware attack caused the district's multi-day internet outage last week.
The district first lost internet connection on Monday and announced the restoration of its technology systems on Friday afternoon.
A team of third-party forensic specialists working with the district's information technology team informed AHISD that the incident was contained. But the investigation into the scope of the issue remains ongoing, according to a message Superintendent Dana Bashara sent to district staff and families Friday. (Sophia Veneziano / San Antonio Express News)
Related: HackNotice
Google announced that its ransomware detection and file restoration are now rolling out to all users, bringing a new level of protection to Google Drive.
The company says it has significantly improved the AI system’s ability to spot malicious encryption in that time, even claiming its latest model can detect 14 times more infections than before. (Matt Horne / Android Authority)
Related: Tech Times, WPTF, Android Police
Google Research published updated estimates warning that future quantum computers could break cryptocurrencies sooner than previously thought, though such an event is still several years away.
In a blog post, Google explained that most blockchain technologies and cryptocurrencies rely on the 256-bit elliptic curve discrete logarithm problem (ECDLP-256) to secure wallets and transactions.
Citing the latest whitepaper from Google Research, the blog post said that the necessary quantum computing resources to break the ECDLP-256 have decreased significantly. The team compiled two of the latest quantum circuits: one with 1,200 logical qubits and 90 million Toffoli gates, and one with 1,450 logical qubits and 70 million Toffoli gates.
"We estimate that these circuits can be executed on a superconducting qubit CRQC (cryptographically relevant quantum computers) with fewer than 500,000 physical qubits in a few minutes," the blog post said. "This is an approximately 20-fold reduction in the number of physical qubits required to solve ECDLP-256."
Google's white paper added that the reduced execution time allows quantum computers to conduct real-time attacks within Bitcoin's average block time of 10 minutes. This enables "on-spend" attacks, which are quantum computing attacks that target active cryptocurrency transactions while they are still in the mempool. (Danny Park / The Block)
Related: Google AI Blog, Google AI Blog, The Quantum Insider, CoinDesk, CCN
Best Thing of the Day: Korea To Move Up the Ransomware Defense Curve
Korea's Internet & Security Agency (KISA) has launched a "ransomware lifecycle response task force" to respond systematically to increasingly sophisticated ransomware attacks.
Worst Thing of the Day: Europe Is Preparing to Kiss Biometric Privacy Goodbye
The US and European Union are in formal talks over a biometric data-sharing arrangement that could give the Department of Homeland Security (DHS) access to fingerprint and other biometric records held by EU member states.
Bonus Worst Thing of the Day: Data Brokers Who Help ICE
Thomson Reuters, the media company that is also a data broker, has long provided underlying personal data for Immigration and Customs Enforcement (ICE) tools, and its data is now possibly part of the Palantir system ICE uses to find which neighborhoods to target.
Closing Thought