China’s hackers hide in plain sight through hijacked home routers, allies warn
US charges two accused of running major scam compound, White House accuses China of stealing AI property on 'industrial scale,' Stuxnet-like code was used in mid-2000s, Health info from UK Biobank was posted for sale in China, Indian media giant was hacked by an alleged Afghan group, much more
Don't miss my latest CSO piece, which examines Sean Plankey's derailed CISA director nomination and the unexplained resistance, disputed allegations, and a cybersecurity agency drifting without confirmed leadership during the Iran war.
Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
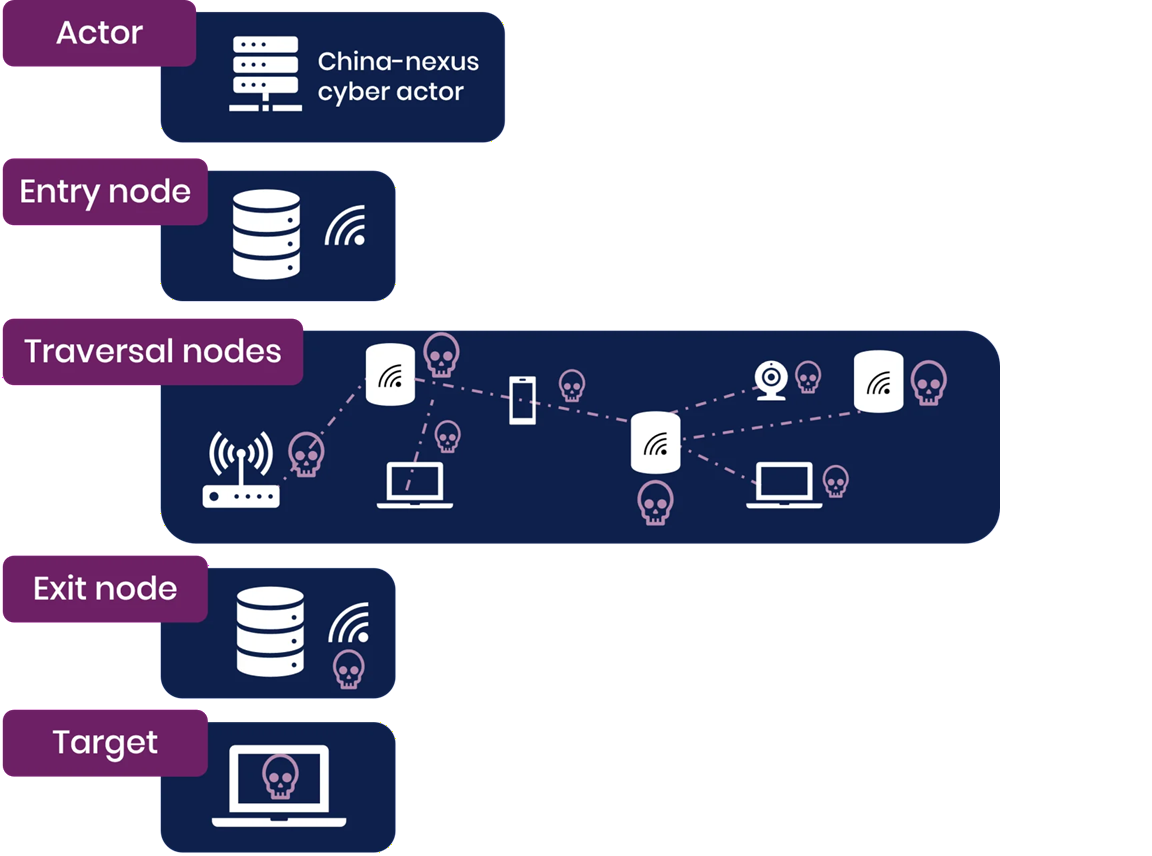
The UK's National Cyber Security Centre (NCSC-UK) and international partners, including the US Cybersecurity and Infrastructure Security Agency, warned that China-nexus hackers are increasingly using large-scale proxy networks of hijacked consumer devices to evade detection and disguise their malicious activity.
This joint advisory, co-signed by agencies from the United States, Australia, Canada, Germany, Japan, the Netherlands, New Zealand, Spain, and Sweden, says the majority of Chinese hacking groups have switched from individually procured infrastructure toward vast bonets of compromised devices, primarily small office and home office routers, along with internet-connected cameras, video recorders, and network-attached storage (NAS) equipment.
These massive botnets allow them to route traffic through chains of compromised devices, entering the network at one point, passing through multiple intermediate nodes, and exiting near the intended target to avoid geographic detection.
One such massive Chinese botnet, known as Raptor Train, infected more than 260,000 devices worldwide in 2024 and was linked by the FBI to malicious activity attributed to the Chinese state-sponsored Flax Typhoon hacking group and Chinese company Integrity Technology Group (sanctioned in January 2025).
The FBI disrupted Raptor Train in September 2024 with help from researchers at Black Lotus Labs after linking it to campaigns targeting entities in the military, government, higher education, telecommunications, defense industrial base (DIB), and IT sectors, primarily in the US and Taiwan.
A separate network (KV-Botnet) was used by the Chinese state-backed Volt Typhoon threat group and consisted primarily of vulnerable Cisco and Netgear routers that were out of date and no longer received security patches. The FBI also disrupted KV-Botnet by wiping malware from infected routers in January 2024, but Volt Typhoon slowly started reviving it in November 2024 after an initial failed attempt in February.
Western intelligence agencies that signed the advisory warned that traditional defenses based on blocking static lists of malicious IP addresses are becoming less effective as these botnets continuously add new compromised nodes.
Instead, network defenders at small, medium, and large organizations are advised to implement multifactor authentication, map network edge devices, leverage dynamic threat feeds that include known covert network indicators, and, where possible, apply IP allowlists, zero-trust controls, and machine certificate verification. (Sergiu Gatlan / Bleeping Computer)
Related: NCSC, NCSC, The Cyber Express, Dark Reading, Security Affairs, Help Net Security, GBHackers, CyberScoop, CISA, Industrial Cyber, The Cyber Express, Meritalk

The US Justice Department said it has charged two Chinese nationals accused of running a major scam compound in Myanmar that targeted Americans in cryptocurrency fraud schemes, as Attorney Jeanine Pirro warned the US would continue to crack down on cyber crimes.
Prosecutors allege Huang Xingshan and Jiang Wen Jie oversaw operations at a site known as Shunda Park, where trafficked workers were forced to carry out so-called “pig butchering” scams — building online relationships with victims before steering them into fake crypto investments that siphoned large sums of money.
“We have seized the sites and we are coming for the rest,” Pirro told reporters following the announcement. “These criminals thought they were untouchable because they are overseas. Today we have proved them wrong and we’re just getting started.”
The charges are part of the Justice Department’s Scam Center Strike Force targeting syndicates, including those linked to Chinese organized crime operating across Myanmar, Cambodia, and Laos, that have siphoned billions of dollars from victims all over the world. Such operations often rely on human trafficking networks, with workers lured abroad and forced to conduct scams under threats of violence.
The Justice Department said the latest effort included a “first-of-its-kind” seizure of a Telegram channel used to recruit workers to Cambodia under false job offers, while authorities have restrained more than $700 million in cryptocurrency tied to the schemes and taken down over 500 fraudulent websites.
Huang and Jiang were arrested on immigration charges by Thai authorities in early 2026 and remain in custody in Thailand. The case is being investigated by the FBI’s New York Field Office, with assistance from the FBI’s legal attaché in Bangkok and Thai authorities. It was not immediately clear if Huang and Jiang are contesting the allegations. (Rosalind Mathieson and Philip Heijmans / Bloomberg)
Related: Justice.gov, GovInfoSecurity, Boston Globe, BeInCrypto, The Record, CryptoNews
The White House accused China of stealing US artificial intelligence labs' intellectual property on an industrial scale in a memo that threatens to strain relations ahead of a summit between US and Chinese leaders next month.
"The US government has information indicating that foreign entities, principally based in China, are engaged in deliberate, industrial-scale campaigns to distill US frontier AI systems," Michael Kratsios, director of the White House Office of Science and Technology Policy, wrote in a memo first reported by the Financial Times.
"Leveraging tens of thousands of proxy accounts to evade detection and using jailbreaking techniques to expose proprietary information, these coordinated campaigns systematically extract capabilities from American AI models, exploiting American expertise and innovation," he added. (Alexandra Alper and Ruchika Khanna / Reuters)
Related: White House, BBC News, NextGov/FCW, CNN, Meritalk, Financial Times, The Hill, Axios, PYMNTS, The Independent, Crypto Briefing, Decrypt
Vitaly Kamluk and Juan Andrés Guerrero-Saade, two researchers from the cybersecurity firm SentinelOne, revealed a breakthrough in the mystery of a piece of malware known as Fast16, a piece of code whose purpose has eluded the cybersecurity world since its existence was first revealed in an NSA leak in 2017.
The SentinelOne researchers have now reverse-engineered the Fast16 code, which they say dates back to 2005 and was likely created by either the US government or one of its allies.
It is a 21-year-old specimen of malware capable of tampering with research and engineering software to undetectably sow mayhem—one that may have been used in Iran, even before Stuxnet.
Kamluk and Guerrero-Saade have determined that the Fast16 malware was designed to carry out the most subtle form of sabotage ever seen in an in-the-wild malware tool: By automatically spreading across networks and then silently manipulating computation processes in certain software applications that perform high-precision mathematical calculations and simulate physical phenomena, Fast16 can alter the results of those programs to cause failures that range from faulty research results to catastrophic damage to real-world equipment.
Fast16 might have been used in the mid-2000s specifically to subvert Iran's attempt to gain nuclear weapons, perhaps even years before Stuxnet was deployed to achieve the same result through a more direct form of sabotage, as part of a joint program carried out by the NSA and Israel's Unit 8200 hackers known as Olympic Games. (Andy Greenberg / Wired)
Related: SentinelOne, The Register
The health information of 500,000 members of the UK's health data project, UK Biobank, was offered for sale online in China, the government has confirmed.
Technology minister Ian Murray said information of all members of the database was found listed for sale on the website Alibaba.
Murray told MPs the charity that runs UK Biobank had told the government about the data breach on Monday. He said the information did not include names, addresses, contact details, or telephone numbers.
The Biobank is a collection of data that has been used to help improve the detection and treatment of dementia, some cancers, and Parkinson's.
UK Biobank said it was investigating the incident and thanked the UK and Chinese governments, as well as Alibaba, for support and cooperation. (James Kelly / BBC News)
Related: Biobank, International Business Times, Insurance Business, Identity Week, The Times, The Guardian, DW, The Independent, BBC News, Sky News, Financial Times, Associated Press, Digital Health, The Telegraph, The Register, Public Technology, European Interest
Indian media giant OneIndia was successfully compromised by a group identifying itself as "True Muslim Afghans."
The hackers successfully infiltrated the network's digital platforms, which boast a massive reach of over 30 million followers, to broadcast a defiant political message.
The incident is being viewed by regional observers not merely as a technical breach, but as a calculated geopolitical strike.
The hackers, believed to be potentially aligned with the Northern Alliance and other resistance factions, used the compromised broadcast channels to publicly denounce the current Interim Afghan Government (IAG) and the Taliban's (TTA) shifting policies.
The group utilized the hijacked platform to display the Afghan flag, symbolizing their rejection of the current regime in Kabul.
The hackers vehemently condemned the growing proximity between the Taliban and the Indian establishment. (The Express Tribune)
Related: 24 Digital
When Coupang, South Korea’s biggest online retailer, revealed last year that a data breach had compromised tens of millions of customer accounts, it appeared to be a corporate crisis.
Coupang is nominally a Korean company but operates from Seattle, is listed on the New York Stock Exchange, and is run by Korean-American billionaire Bom Kim. In November last year, the company disclosed that a former employee had stolen an internal security key, enabling unauthorized access to data from 33.7 million users.
The breach triggered a widespread movement to abandon the service and a sweeping government response. Police raided the company’s Seoul headquarters, tax authorities launched a special audit, and parliament summoned executives for questioning. Kim refused to travel to Korea for hearings, citing his role as a global chief executive, and the Korean police have requested that immigration authorities notify them if he enters the country.
Reports suggest that the strength of Seoul’s response may have jeopardized relations with the US, adding to tensions in an alliance that is vital to South Korea’s national security.
Korean broadcaster SBS reported this week that Washington had signaled it would not proceed with high-level diplomatic and defense consultations unless South Korea guaranteed Kim would face no legal consequences in connection with the data breach.
South Korea’s foreign ministry has not denied the report but said in a statement that “security discussions should proceed separately from the Coupang matter” and that investigations of the data breach would continue under Korean law. (Raphael Rashid / The Guardian)
Related: Investing.com, South China Morning Post, Korea Herald, Maeil Business
Insurance provider Canada Life says it’s aware of a cybersecurity incident that may have compromised the personal data of some of its customers, though the full scope of the incident remains under investigation.
“Canada Life recently identified a cyber incident involving unauthorized access to certain applications through an employee account,” the Canadian life and health insurance giant said in a statement posted to its website on Monday.
“The incident has been contained, and regular operations and services continue. We launched an immediate investigation with support from leading third-party cybersecurity experts and notified authorities.”
They said their current assessment was that “a small proportion” of customers may have been affected. Some media reports suggest that tens of thousands of people’s personal information was accessed in the breach.
The company says that individuals whose personal information was accessed will be contacted directly soon. For those people, Canada Life says it will offer free-of-charge credit monitoring for an unspecified amount of time. (Jordan Fleguel / CTV News)
Related: Canada Life, Insurance Business, r/CanadianForces, Globe and Mail, HR Reporter
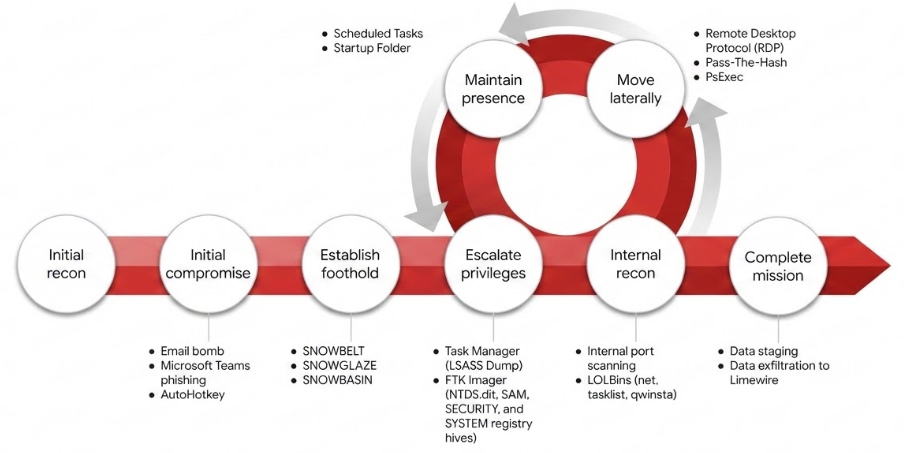
Google Threat Intelligence Group (GTIG) and Mandiant researchers say they have caught a newly identified threat group, UNC6692, running a sophisticated multistage intrusion campaign that uses Microsoft Teams impersonation, a custom modular malware suite, and cloud infrastructure abuse to deeply penetrate enterprise networks, all without exploiting a single software vulnerability.
In late December 2025, UNC6692 launched a mass email bombing campaign against its targets, deliberately flooding inboxes to create a sense of urgency and confusion.
With victims overwhelmed and distracted, the threat actor delivered the critical blow by sending a phishing message directly over Microsoft Teams, with the attacker posing as an IT helpdesk employee offering assistance with the email volume.
This technique is not a zero-day exploit or a software flaw. As Microsoft noted in its own April 2026 advisory, the campaign abuses legitimate external collaboration features in Teams, with attackers convincing users to override multiple, clearly presented security warnings.
Google recommends that organizations restrict or closely monitor Microsoft Teams external access settings to prevent unknown tenants from initiating chat sessions with employees. (Guru Baran / Cyber Security News)
Related: Google Cloud, Notebookcheck
The Cybersecurity and Infrastructure Security Agency and the United Kingdom’s National Cyber Security Centre jointly published a malware analysis report identifying a backdoor, code-named Firestarter, on Cisco network security devices that can survive firmware updates and standard reboots.
Cisco’s threat intelligence division, Talos, attributed the malware to a threat actor it tracks as UAT-4356. The company attributed the same group to a 2024 espionage campaign called ArcaneDoor, which focused on compromising network perimeter devices.
The central concern driving the updated directive is the attack group’s ability to persist on compromised devices, even after enterprises applied the security patches Cisco released in September 2025. Those patches addressed two vulnerabilities — CVE-2025-20333, a remote code execution flaw in the VPN web server component, and CVE-2025-20362, an unauthorized access vulnerability — that UAT-4356 exploited to gain initial entry. According to CISA, devices compromised before patching may still harbor the implant.
CISA confirmed it discovered Firestarter on a US federal civilian agency’s Cisco Firepower device after identifying suspicious connections through continuous network monitoring. The finding prompted an updated emergency directive requiring all federal civilian agencies to audit their Cisco firewall infrastructure and submit device memory snapshots for analysis by Friday. (Greg Otto / CyberScoop)
Related: Arcane Door, CISA
Best Thing of the Day: One Can Only Hope
The multiple investigations into xAI’s creation and dissemination of sexually abusive imagery may lead the company to lose access to certain markets, parent company SpaceX warned.
Worst Thing of the Day: Here Come the More Malware-Adept Scam Compounds
Some Cambodia-based scam operations are buying and using easier-to-operate malware to steal data from unsuspecting victims, according to Infoblox and Vietnamese cybersecurity nonprofit Chong Lua Dao.
Closing Thought





