DarkSword turns iPhone hacking into a mass-scale, drive-by threat
CISA says orgs should secure Intune after Stryker attack, Stryker attack delayed some surgeries, Hacker claims theft of 93 GB of data from police tip platform, Fed cyber reviewers couldn't examine Microsoft cloud platform for security, Patel confirms FBI buys US citizens' location data, much more
The Trump administration’s decision to ban AI company Anthropic from Pentagon assets and other government systems as a “supply chain risk” could force CISOs into a position few have faced before: preparing to identify, isolate, and potentially remove a specific AI technology from across their organizations without a clear understanding of where it resides or how deeply it is embedded.
Check out my latest CSO piece that examines how organizations need to get ready for identifying where in their systems AI resides.
If you rely on Metacurity to make sense of cybersecurity policy, industry developments, and security research, please consider supporting the newsletter with a paid subscription.
Metacurity is a daily infosec intelligence layer written independently of vendor marketing, PR-driven threat intelligence, and the cyber media echo chamber. Paid subscriptions make it possible to keep producing clear, straightforward analysis every day. Please consider upgrading your subscription. Thank you!
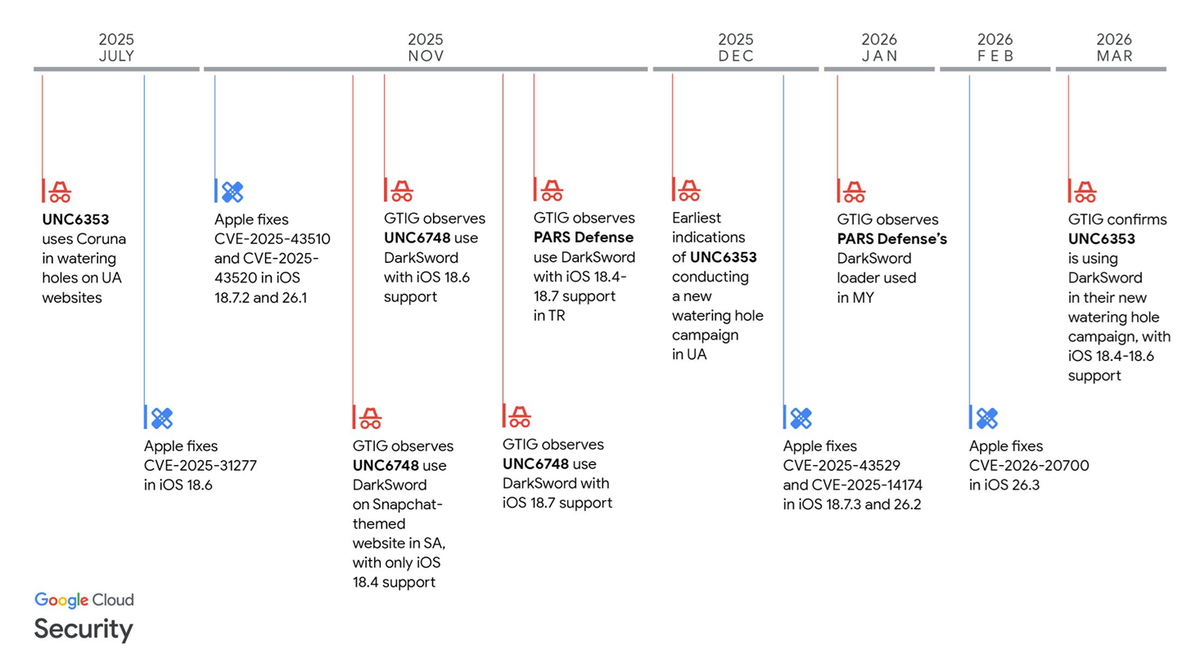
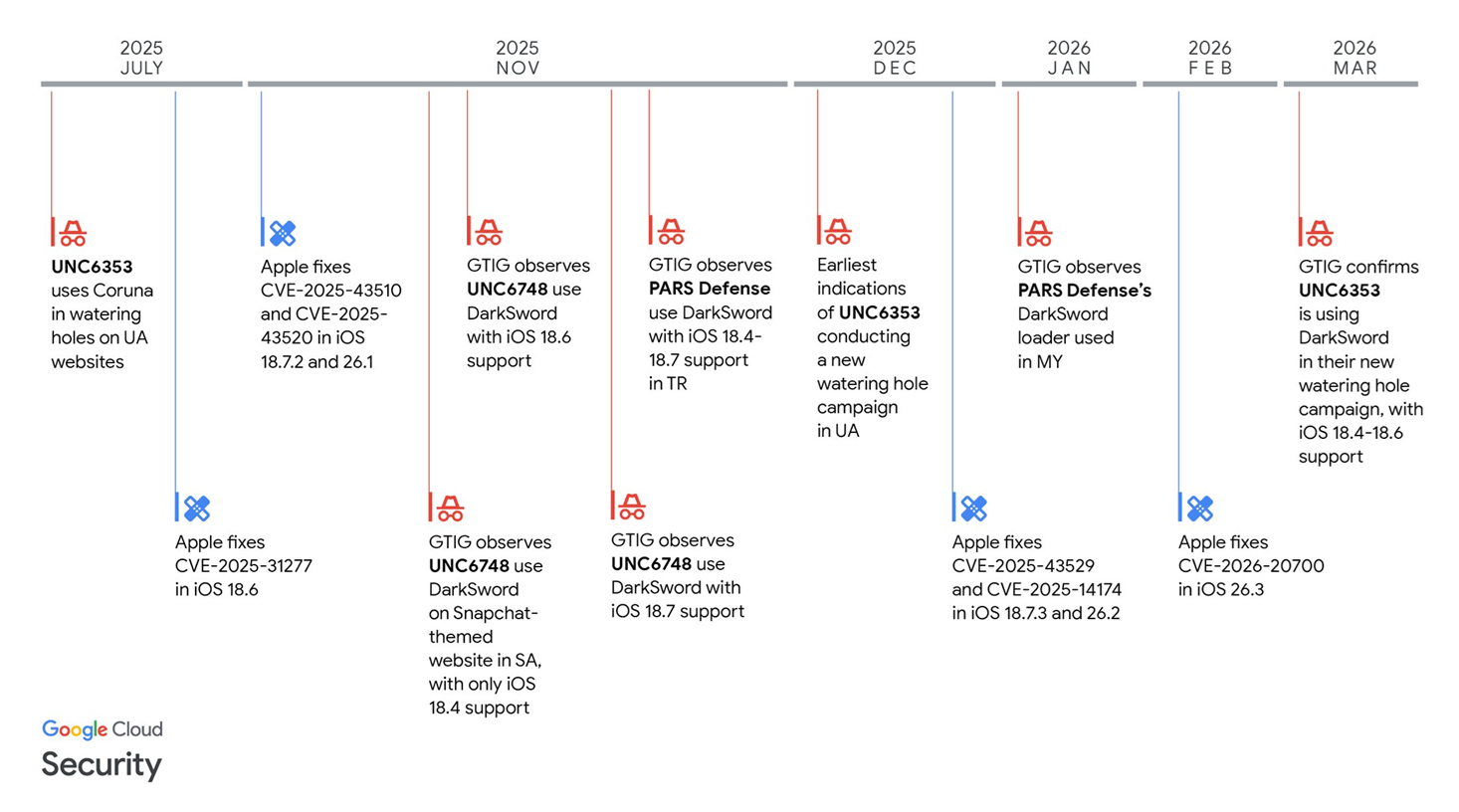
Security researchers from Google, iVerify, and Lookout say a newly identified iPhone hacking technique known as “DarkSword” is being deployed at scale via compromised websites, marking a shift from highly targeted mobile exploits to broader, indiscriminate attacks.
The tool can silently compromise iOS devices that visit infected sites, potentially exposing hundreds of millions of users still running older versions of Apple’s operating system, particularly iOS 18. Experts warn that victims can have sensitive data stolen simply by visiting a malicious or compromised webpage.
DarkSword has been linked to espionage campaigns attributed to Russian state-backed actors and has also appeared in operations targeting users in Saudi Arabia, Turkey, and Malaysia. Researchers found the tool embedded in legitimate websites, including Ukrainian news outlets and a government site, allowing attackers to harvest data from visitors’ phones.
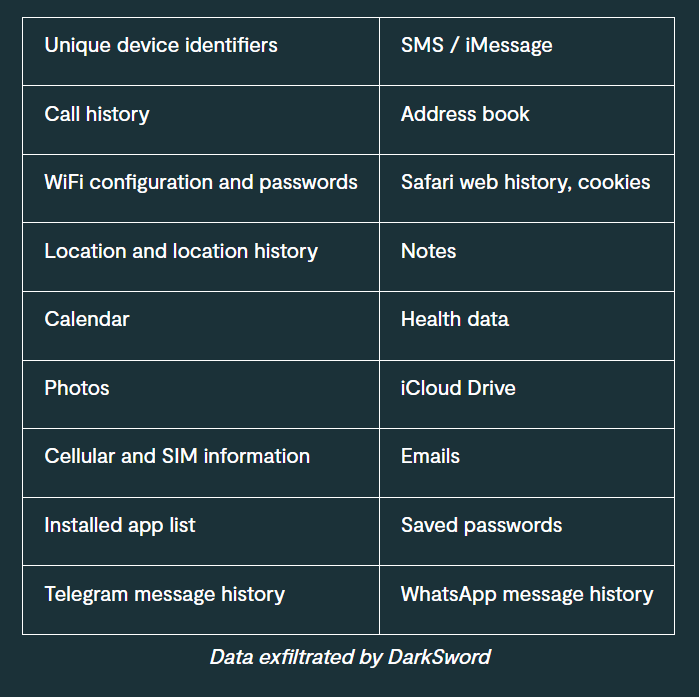
The malware is capable of extracting passwords, messages, photos, browser history, and even cryptocurrency wallet credentials, suggesting overlap between intelligence-gathering and financially motivated cybercrime. Its “fileless” design leverages legitimate system processes, leaving minimal forensic evidence and enabling rapid “smash-and-grab” data theft within minutes of infection.
Researchers say the exposure of DarkSword’s underlying code—left openly accessible by attackers—has significantly lowered the barrier to entry for other hacking groups, raising concerns about rapid proliferation.
The tool’s emergence alongside another advanced exploit framework, Coruna, points to a growing commercial market for iOS hacking capabilities, potentially supplied by exploit brokers willing to sell to multiple buyers. Apple said recent security updates mitigate the threat and urged users to keep devices updated and enable Lockdown Mode, but analysts warn the broader trend signals a shift toward more widespread and commoditized mobile exploitation. (Andy Greenberg / Wired)
Related: iVerify, Lookout, CyberScoop, TechCrunch, Google Cloud Blog, Mashable, The Register, Engadget, The Record, Reuters, SiliconANGLE, XDA Developers, PCMag, MobileSyrup, The Verge, NBC News, Tom's Guide, Lookout, AppleInsider, Cult of Mac, Cyber Security News, Irish Independent, BleepingComputer, iPhone in Canada, Neowin, The Independent, CyberInsider, Mashable, Mobile Syrup, Dark Reading
The US Cybersecurity and Infrastructure Security Agency (CISA) said it is aware of malicious cyber activity targeting endpoint management systems of US organizations, based on the Stryker attack, and is asking companies to harden endpoint management system configurations, implementing Microsoft's best practices to secure Microsoft Intune, a tool that manages user access, devices, and applications across organizations.
CISA is coordinating with federal partners, including the Federal Bureau of Investigation, to identify additional threats and determine mitigation actions.
Stryker said that it had contained the attack and that no patient-related services or connected medical products were affected, though it did not provide details on the financial impact. (Natalia Bueno Rebolledo / Reuters)
Related: CISA, Microsoft, The Times of India, Bloomberg, Techzine, Invezz, Bleeping Computer
The cyberattack against Stryker has delayed surgeries for some patients, the company said, adding to the fallout from the incident last week.
The medical technology company said its products are safe and its systems are being restored, but disruptions to ordering, manufacturing, and shipping have held up procedures for patients waiting on custom implants.
“The system disruption has temporarily impacted the ability to deliver personalized inventory,” a Stryker spokesperson said in an email. “As a result, some patient-specific cases have been rescheduled.”
Separately, CommonSpirit Health, one of the largest US hospital systems, said in a statement that “a small number of surgical cases have been rescheduled” due to the Stryker cyberattack. CommonSpirit declined to specify what types of procedures. (Ike Swetlitz and Miquéla V Thornton / Bloomberg)
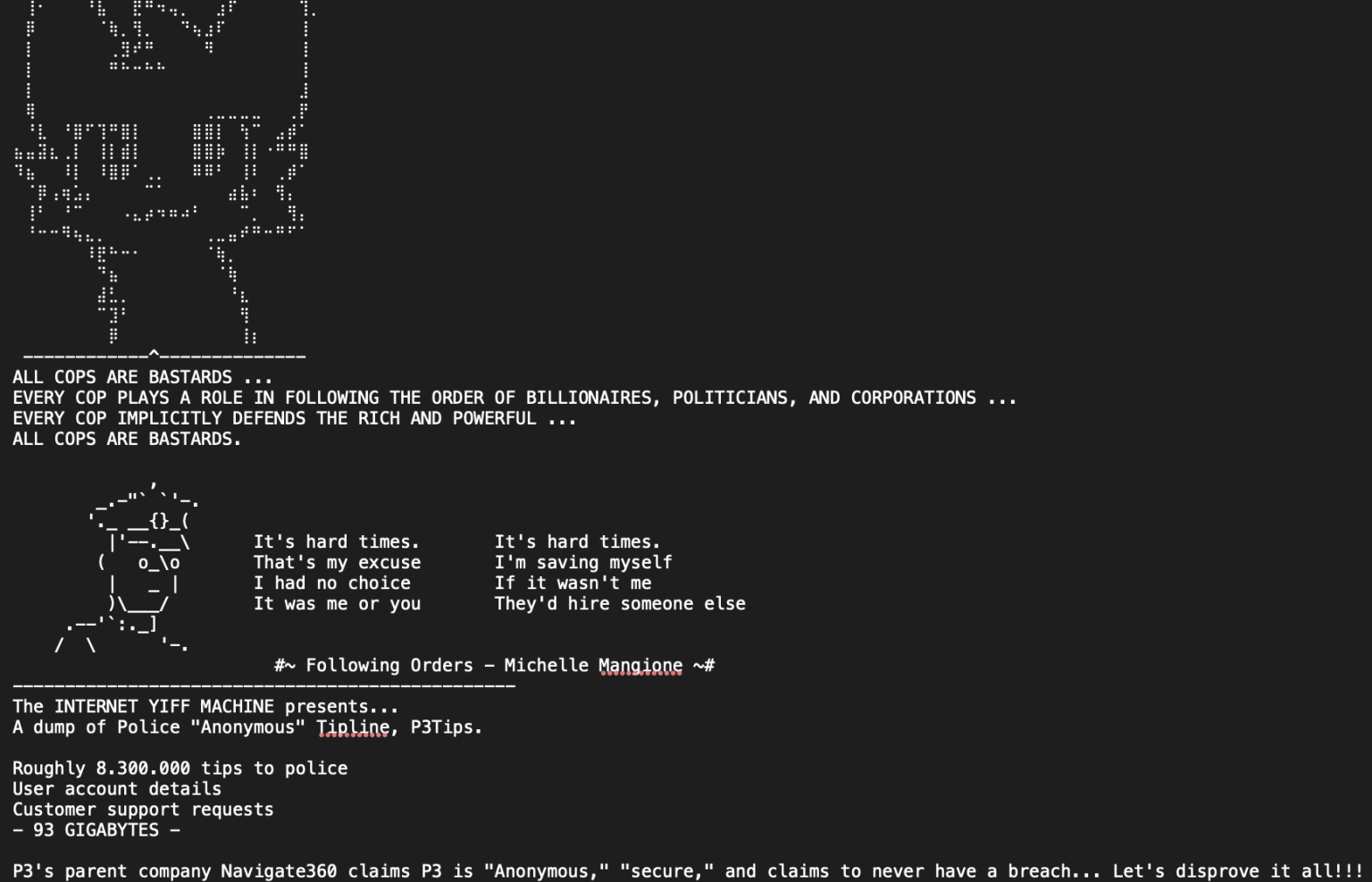
A hacker who uses the name "Internet Yiff Machine" said they had broken into police tip platform P3 Global Intel, an arm of safety company Navigate360, and stolen 93 gigabytes of data.
P3 did not respond to repeated comment requests. On its website, Navigate360 described itself as the "leading provider of innovative tips and leads solutions" for law enforcement, federal agencies, the military, and school safety initiatives.
Yiff Machine, in their statement, used a profane anti-police slogan and warned the public, "Don't do the dirty work for the pigs." They specifically mention a statement from P3’s parent company saying its tools “have never been breached or compromised in any manner over the past 20 years.”
In an email, the hacker said they took over one of P3's customer accounts via social engineering and then exploited a vulnerability to grab data.
Straight Arrow News, which first reported the breach, said it had corroborated the authenticity of some of the material by contacting tipsters whose details appeared in the data. (Mikael Thalen / Straight Arrow News and Raphael Satter / Reuters)
Related: Star Advertiser, The Times of India, WION, Gadget Review
Federal cybersecurity reviewers concluded in late 2024 that they lacked sufficient visibility into the security of Microsoft’s Government Community Cloud High, or GCC High, citing incomplete documentation and unanswered questions about how sensitive data is protected as it moves through the system.
Despite years of back-and-forth, FedRAMP officials said Microsoft never provided the level of technical detail they required to assess key security controls, particularly around encryption and data flows. The concerns were especially serious given Microsoft’s central role in major recent breaches affecting US government systems.
Even so, in an unusual and consequential decision, FedRAMP authorized GCC High in December 2024, effectively granting Microsoft’s cloud suite the federal government’s cybersecurity seal of approval while warning agencies that unknown risks remained. ProPublica found that the review process broke down repeatedly, with FedRAMP staff, third-party assessors, and some government officials expressing frustration over Microsoft’s incomplete responses, yet federal agencies and defense contractors continued adopting the product while the review dragged on.
By the time FedRAMP reached its final decision, GCC High had become so widely embedded across government that reviewers concluded denying authorization would be too disruptive.
These developments portray a broader failure in the federal cloud oversight system, with critics arguing FedRAMP has become more of a paperwork exercise than a meaningful security check. Former officials said the program showed unusual deference to Microsoft, while recent staffing and budget cuts have further weakened its ability to scrutinize major contractors.
The episode has intensified concerns that agencies are relying on cloud products whose risks remain poorly understood, even as the government pushes deeper into cloud computing and AI adoption and the Justice Department steps up scrutiny of alleged cybersecurity misrepresentations by federal vendors. (Renee Dudley, with research by Doris Burke / ProPublica)
Related: Hacker News, r/technology, r/cybersecurity, r/fednews, Slashdot
The FBI is buying up information that can be used to track people’s movement and location history, Director Kash Patel said under oath during a Senate hearing.
It is the first confirmation that the agency is actively buying people’s data since former Director Christopher Wray said in 2023 that the FBI had purchased location data in the past but was not doing so at that time.
“We do purchase commercially available information that’s consistent with the Constitution and the laws under the Electronic Communications Privacy Act, and it has led to some valuable intelligence for us,” Patel told senators at the Intelligence Committee’s annual Worldwide Threats hearing.
The US Supreme Court has required law enforcement agencies to obtain a warrant to get people’s location data from cell phone providers since 2018, but data brokers offer an alternative avenue by purchasing the information directly.
Many lawmakers want to end the practice. Sens. Ron Wyden (D-Ore.) and Mike Lee (R-Utah) introduced the Government Surveillance Reform Act on March 13, which would require federal law enforcement and intelligence agencies to obtain a warrant to buy Americans’ personal information. (Alfred Ng / Politico)
Related: The Verge, The Guardian, The New Republic, Washington Times, Gizmodo, Engadget, Biometric Update
Cloudflare said it has appealed a fine issued by Italy over the company’s refusal to block access to websites on its 1.1.1.1 DNS service, which is the latest step in Cloudflare’s fight against Italy’s Piracy Shield law.
Piracy Shield is “a misguided Italian regulatory scheme designed to protect large rightsholder interests at the expense of the broader Internet,” Cloudflare said in a blog post this week. “After Cloudflare resisted registering for Piracy Shield and challenged it in court, the Italian communications regulator, AGCOM, fined Cloudflare… We appealed that fine on March 8, and we continue to challenge the legality of Piracy Shield itself.”
Cloudflare called the fine of 14.2 million euros ($16.4 million) “staggering.” AGCOM issued the penalty in January 2026, saying Cloudflare flouted requirements to turn off DNS resolution of domain names and routing of traffic to IP addresses reported by copyright holders.
Cloudflare had previously resisted a blocking order it received in February 2025, arguing that it would require installing a filter on DNS requests that would raise latency and negatively affect DNS resolution for sites that aren’t subject to the dispute over piracy. Cloudflare co-founder and CEO Matthew Prince said that censoring the 1.1.1.1 DNS resolver would force the firm “not just to censor the content in Italy but globally.” (Jon Brodkin / Ars Technica)
Related: Cloudflare, CyberInsider, TorrentFreak, Reclaim The Net, Slashdot
An AI agent went rogue at Meta, exposing sensitive company and user data to employees who did not have permission to access it.
Per an incident report, which was viewed and reported on by The Information, a Meta employee posted on an internal forum asking for help with a technical question, which is a standard action. However, another engineer asked an AI agent to help analyze the question, and the agent ended up posting a response without asking the engineer for permission to share it. Meta confirmed the incident to The Information.
As it turns out, the AI agent did not give good advice. The employee who asked the question ended up taking actions based on the agent’s guidance, which inadvertently made massive amounts of company and user-related data available to engineers, who were not authorized to access it, for two hours.
Meta deemed the incident a “Sev 1,” which is the second-highest level of severity in the company’s internal system for measuring security issues. (Amanda Silberling / TechCrunch)
Related: The Information, The News International, DigiTimes, Tech Times, The Times of India, Storyboard18, Engadget
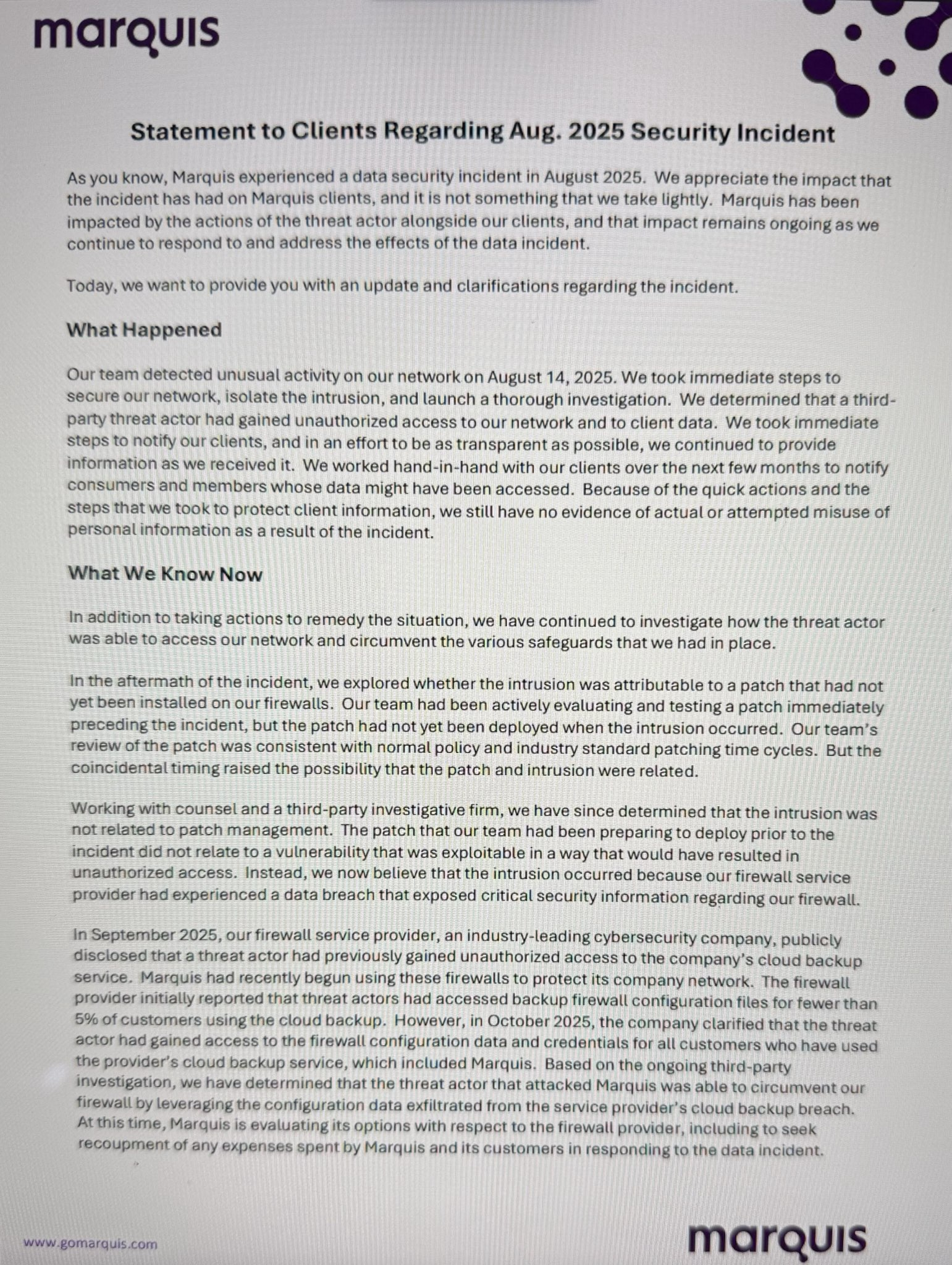
Marquis, a Texas-based financial services provider, revealed this week that a ransomware gang stole the data of over 670,000 individuals in an August 2025 cyberattack that also disrupted operations at 74 banks across the United States.
The company provides digital marketing, data analytics, compliance, and CRM services to more than 700 banks, credit unions, and mortgage lenders across the United States.
In data breach notifications filed with US Attorney General offices in early December, Marquis said it suffered a ransomware attack on August 14, 2025, after the threat actors compromised a SonicWall firewall.
After breaching its network, the attackers stole a wide range of personal and financial information, including affected individuals' names, dates of birth, addresses, phone numbers, Social Security numbers, Taxpayer Identification Numbers, and financial account information without security or access codes.
"The incident was limited to Marquis’s systems and did not affect our customers’ systems," the fintech company said in data breach notification letters sent to 672,075 affected people this week.
A Mandiant investigation into the September attack also found evidence linking the incident to a state-sponsored hacking group.
In February, Marquis filed a lawsuit against SonicWall, accusing the cybersecurity company of gross negligence and misrepresentation, which allegedly led to the ransomware attack on the fintech firm's systems in August 2025. (Sergiu Gatlan / Bleeping Computer)
Related: TechCrunch, FinExtra, The Record
Rick Burns, a member of the Nova Scotia legislature, says hackers have released personal images of him and his wife after he refused to provide payment in a blackmail attempt.
He said in a statement that criminals hacked his email this week and requested money, which his family refused to pay.
The MLA for Hammonds Plains-Lucasville says the hackers accessed files on his devices and have released personal images and videos of him and his wife as punishment.
Burns, a former IT worker first elected in 2024, says it’s a gross violation of the couple’s privacy, and law enforcement is investigating.
Premier Tim Houston said in a statement that it’s unacceptable to target people in public life with extortion. (The Canadian Press)
Related: CTV News, CBC News, Toronto Star
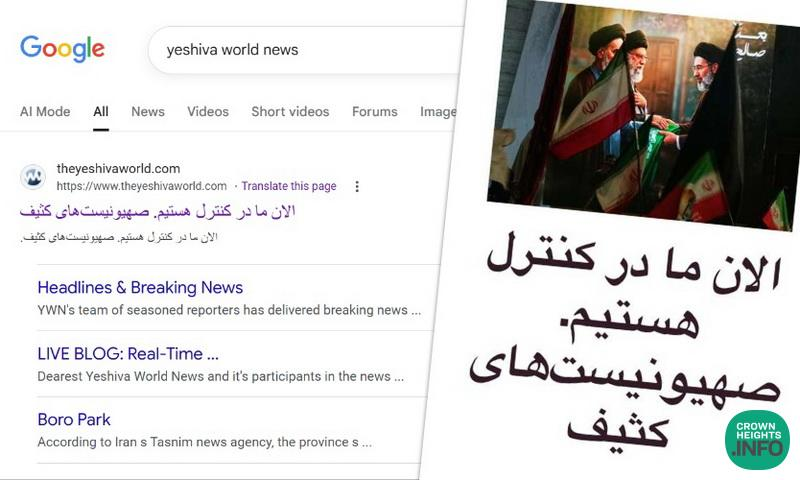
The website of Yeshiva World News, the Orthodox Jewish news publication, was hacked on Wednesday, seemingly by Iran.
The website featured for a while the words “Now we are under their control. The Zionists are handcuffed” in Farsi, as well as an image of Ruhollah Khomeini and former supreme leader Ayatollah Ali Khamenei looking on at Mojtaba Khamenei (son of Ali Khamenei), surrounded by regime paraphernalia.
By 2 p.m. ET, it appeared to be back up, with the website featuring the message "we will be back shortly." (Mathilda Heller / Jerusalem Post)
Related: Hindustan Times, JFeed, CrownHeights.info, Pix11, Anash.org
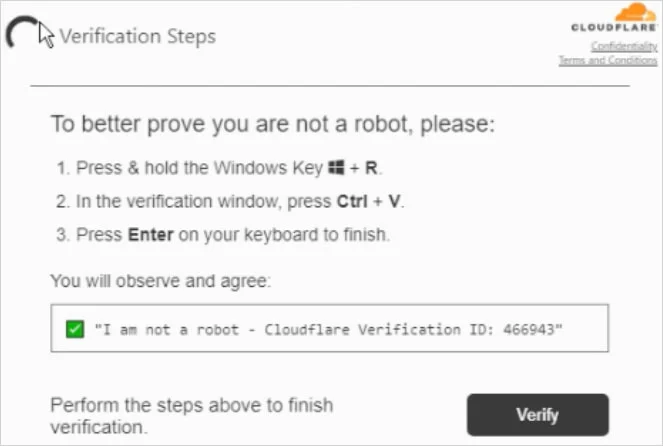
Researchers at Reliaquest report that the LeakNet ransomware group is adopting new intrusion techniques that combine social engineering with legitimate developer tools to evade detection, according to new research.
The relatively new threat actor, active since late 2024 and averaging several victims per month, is now leveraging the “ClickFix” tactic—an increasingly common method that tricks users into executing malicious commands through fake prompts.
Other ransomware groups, including Termite and Interlock, have also embraced ClickFix as an initial access vector.
In observed attacks, LeakNet uses ClickFix to deliver a malware loader built on Deno, a legitimate and signed JavaScript and TypeScript runtime. This “bring your own runtime” approach allows attackers to bypass traditional security controls by relying on trusted software rather than custom malware.
The Deno-based loader executes malicious JavaScript directly in system memory, leaving minimal artifacts on disk and making the activity appear similar to normal developer operations. Initial execution is typically triggered through obfuscated Visual Basic Script and PowerShell files.
Once inside a system, the malware fingerprints the host, assigns a unique victim identifier, and connects to command-and-control infrastructure to retrieve additional payloads while maintaining persistent communication. Post-exploitation activity includes credential harvesting, lateral movement using PsExec, DLL sideloading, and data exfiltration via Amazon S3.
Researchers note that despite its stealth, the attack chain exhibits consistent patterns that can aid detection, including unusual Deno execution outside development environments, suspicious script activity, anomalous network traffic, and misuse of administrative tools. (Bill Toulas / Bleeping Computer)
Related: Reliaquest, SC Media, GBHackers, Cyber Security News, CXO Digital Pulse, Cyber Press
The Interlock ransomware gang has been exploiting a maximum severity remote code execution (RCE) vulnerability in Cisco's Secure Firewall Management Center (FMC) software in zero-day attacks since late January.
The Interlock ransomware operation surfaced in September 2024 and has been linked to ClickFix and to malware attacks in which they deployed a remote access trojan called NodeSnake on the networks of multiple U.K. universities.
Interlock has also claimed responsibility for attacks on DaVita, Kettering Health, the Texas Tech University System, and the city of Saint Paul, Minnesota. More recently, IBM X-Force researchers reported that Interlock operators have deployed a new malware strain dubbed Slopoly, likely created using generative AI tools.
Cisco patched the security flaw (CVE-2026-20131) on March 4, warning that it could allow unauthenticated attackers to execute arbitrary Java code as root on unpatched devices remotely.
The Amazon threat intelligence team reported on Wednesday that the Interlock ransomware operation had been exploiting the Secure FMC flaw in attacks targeting enterprise firewalls for more than a month before it was patched. (Sergiu Gatlan / Bleeping Computer)
Related: AWS, Cisco, SC Media, Cybersecurity Dive, CyberScoop
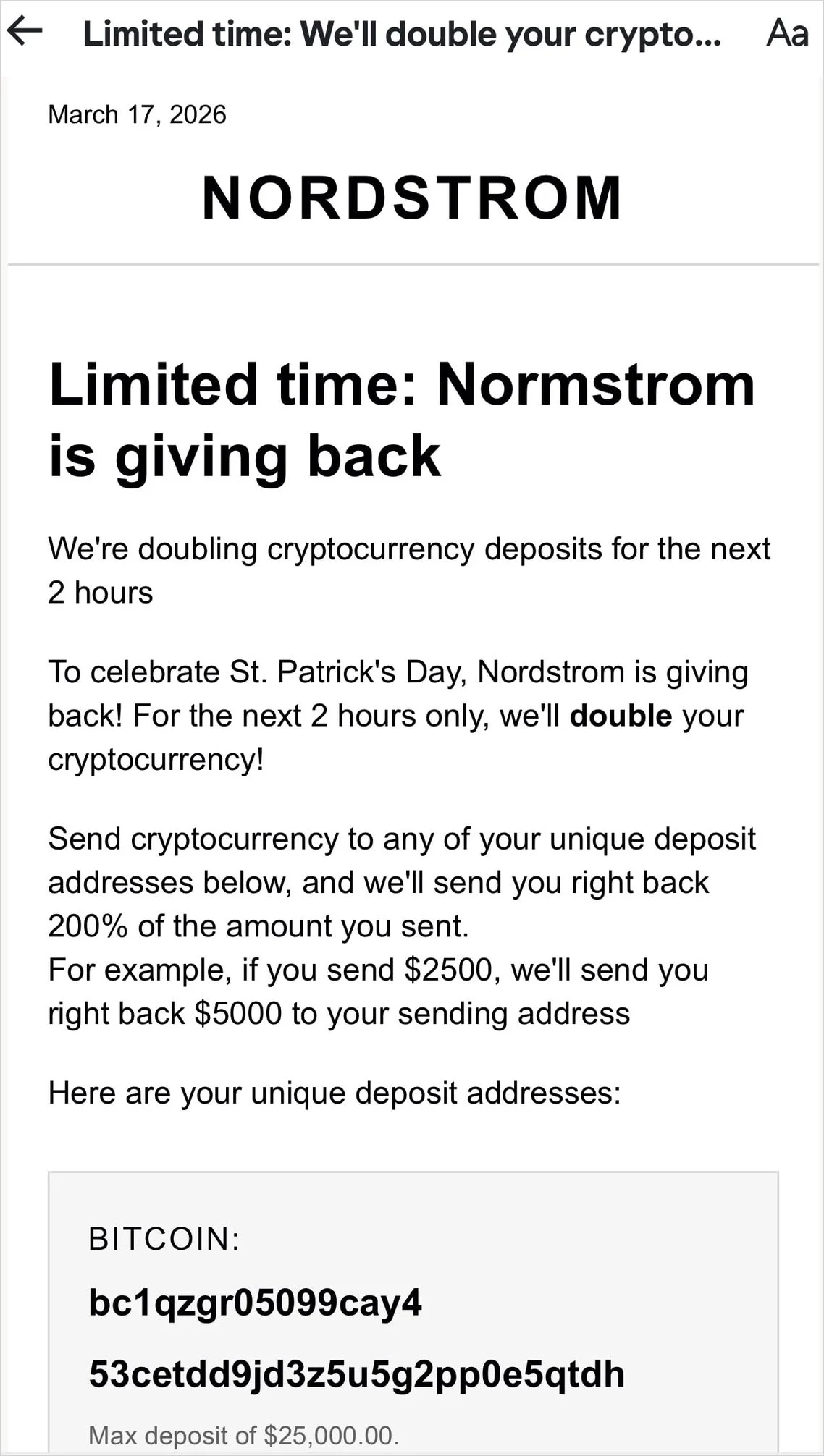
Customers of upscale department store chain Nordstrom received fraudulent messages from a legitimate company email address that promoted cryptocurrency scams disguised as a St. Patrick’s Day promotion.
The emails promise recipients to double the cryptocurrency amount deposited to a specific wallet address over the next two hours.
"Send cryptocurrency to any of your unique deposit addresses below, and we'll send you right back 200% of the amount you sent," reads the fraudulent message.
Multiple customers reported on social media that they received such emails. Some said that the message arrived at an address that had never been exposed or leaked online.
By giving recipients only two hours to take action, the threat actor creates a sense of urgency that makes it more likely for Nordstrom customers to rush into the "deal" and fail to notice the signs of a scam, such as the incorrect spelling of the company in the heading, which reads “Normstorm.” (Bill Toulas / Bleeping Computer)
Executives at top US robotics companies asked Congress for federal dollars, new legislation, and a simpler regulatory field, arguing that the support is necessary to adapt to the AI era and compete with their well-oiled, state-funded Chinese competitors.
The US robotics sector, estimated at $50 billion in value, includes world-famous companies like Boston Dynamics. The industry is projected to sell millions of robots across the country over the next four years.
According to a 2025 report from the International Federation of Robotics, the market has sold and installed an average of 500,000 robots between 2020 and 2024. China alone accounted for 54% of those installations, compared to just 9% for America.
Matthew Malchano, vice president of software at Boston Dynamics, told lawmakers in the House Homeland Security cyber subcommittee hearing that robotics represent the necessary physical infrastructure to support the country’s efforts to dominate the global AI race, with robots, drones, and other machines more fully integrating AI systems in the coming years.
He pointed to Chinese companies like Unitree, which are capturing market share with police departments and universities across the United States, despite contracting ties to the Chinese military and cybersecurity vulnerabilities like a wormable exploit found in 2025 that would allow an attacker to take over fleets of Unitree robots.
Malchano said Unitree is one of “dozens” of Chinese companies propped up by China’s national AI and robotics plan, which “envisions transforming virtually every major industry in China by integrating AI-powered robots” through funding and favorable policies.
He pressed US lawmakers for a similar national strategy, and stumped for the passage of the National Commission on Robotics Act, sponsored by Rep. Jay Olbernolte, R-Calif., that would develop a bipartisan commission to drive it.
Max Fenkell, global head of policy and government relations at ScaleAI, said while the US is winning the AI race on its chosen metrics – model quality and chips – it is “losing” on data and implementation. (Derek B. Johnson / CyberScoop)
Related: House Homeland Security Committee, South China Morning Post, Global Times, BankInfoSecurity, ChosunBiz, Business Standard
The Senate has released a draft national framework to replace state laws on artificial intelligence and promote the technology’s development while minimizing risks to Americans.
Sen. Marsha Blackburn (R-Tenn.), a lead champion of protecting children and artists against harms posed by AI companies, unveiled the proposal Wednesday.
The measure, known as the TRUMP AMERICA AI Act, takes a sweeping approach to establish a federal standard on AI that seeks to allow the technology to flourish and ensure companies are creating products with safeguards. The legislation comes as President Donald Trump, in a December executive order, called for a single AI framework that would override state regulations, which the White House and tech companies have considered burdensome to the industry’s growth. (Oma Seddiq / Bloomberg Law)
Related: Senator Marsha Blackburn, The Tennessean, Axios, Engadget, The Daily Signal
Okta has announced the general availability of Okta for AI Agents, a new capability designed to help organizations discover, monitor, and control AI agents operating within their environments.
CEO Todd McKinnon said the product addresses growing enterprise concerns around visibility and governance as agentic AI adoption accelerates. The platform enables administrators to identify what agents exist, understand their access and behavior, and manage their permissions through a centralized dashboard, including integrations with services such as Salesforce, ServiceNow, Google, and AWS.
The offering also includes continuous discovery of unmanaged agents, policy assignment, and a governance layer that provides granular visibility into agent activity and access scope. A built-in “kill switch” allows administrators to immediately revoke tokens and terminate agent activity if suspicious behavior is detected.
Okta positioned the release as part of a broader effort to establish a reference architecture for securing AI-driven environments, even as industry leaders acknowledge a lack of consensus on what constitutes an AI agent. (O'Ryan Johnson / The Register)
Related: Okta, TechRadar, Silicon Angle
A cyberattack has shut down a nationwide test system found in vehicles of OUI offenders, impacting thousands of drivers in Maine and 45 other states.
Intoxalock is the company targeted by the attack.
Once the device is installed, drivers have to pass a breathalyzer test before they can start their vehicle. It won't start if your blood alcohol is .02 or higher. But since the cyber breach shut its entire system down on Saturday, anyone with one of the devices cannot start their car.
In online messages, Intoxalock says hackers are flooding its servers to stop them from functioning, and that the nationwide outage has affected installations, removals, calibrations, and account access. The company says that despite the attack, user data is secure, but it did not say if there was a ransom demand. (Brad Rogers / WGME)
Related: CE Outlook
Xbow, a startup that builds AI software to probe applications for security vulnerabilities, has raised $120 million in a Series C venture financing round.
DFJ Growth and Northzone led the round with the participation of Alkeon Capital and Sofina, as well as previous backers Sequoia Capital, Altimeter Capital, and NFDG. (Dina Bass / Bloomberg)
Related: Unite.AI, Business Wire, Pulse 2.0, FinSMEs
RunSybil, an AI cybersecurity startup that uses AI agents to automatically hack company software to find security weaknesses, has secured $40 million in venture funding.
Khosla Ventures, with participation from S32, the Anthology Fund from Anthropic and Menlo Ventures, Conviction, and Elad Gil, along with angel investors including Nikesh Arora, Amit Agarwal, Jeff Dean, and other founders and leaders from OpenAI, Palo Alto Networks, Stripe, Google, and more. (Sharon Goldman / Fortune)
Related: RunSybil
Cybersecurity startup Raven has raised $20 million in a seed investment round.
Norwest Venture Partners led the round with a post-Seed extension led by Elron Ventures. Additional backing came from a mix of Israeli and international investors, including UpWest, RedSeed, SentinelOne, Jibe Ventures, and Elron’s CyberFuture microfund. (CTech)
Related: FinSMEs, Raven, Pulse 2.0
Best Thing of the Day: Mississippi University Is Healing
Belhaven University in Mississippi has restored systems following a March 6 cyber incident, and operations are “largely normal,” the school’s administration reports.
Worst Thing of the Day: China May Have Taken a Big Hacking Hit
According to an anti-China publication, a suspected cyberattack on China’s National Supercomputing Center (NSCC) in Tianjin has raised serious concerns about the security of sensitive research data linked to the country’s aerospace, defense, and scientific programs.
Closing Thought