DOGE engineer stole hundreds of millions of US taxpayers' data, whistleblower
Meta unveils new fraud protections as an international operation disrupts scam compound activity, China bans OpenClaw apps on security grounds, Foreign hacker accessed Epstein files in 2023, Rudd confirmed as Cybercom/NSA chief, Quittr app exposes (ahem) sensitive data, much more


Metacurity is the only daily cybersecurity newsletter that is written outside the usual cyber press echo chamber and is a straightforward and accurate alternative to vendor-driven content and PR-flavored threat intelligence.
Please consider supporting my work on Metacurity by upgrading your subscription. Thank you.
The Social Security Administration’s inspector general is investigating a whistleblower complaint alleging that a former DOGE Service software engineer claimed to possess highly sensitive agency databases containing personal information on hundreds of millions of Americans and intended to share the data with a private employer.
According to a letter sent to congressional committees, the watchdog has opened an inquiry and shared the disclosure with the Government Accountability Office, which is separately auditing DOGE’s access to government data.
The complaint alleges the engineer, who worked at the agency last year and later joined a government contractor, told colleagues he had copies of two tightly restricted databases — the Numident file and the Master Death File — which together contain records for more than 500 million living and deceased Americans. The files include Social Security numbers, birth details, citizenship status, race and ethnicity, and parents’ names.
The whistleblower claims the engineer said he had at least one database on a thumb drive and sought help transferring the data to a personal computer so he could “sanitize” it before uploading it to his company’s systems.
According to the disclosure, the engineer also told colleagues he believed he would receive a presidential pardon if his actions were deemed illegal. The complaint does not allege that any data was successfully transferred to the company’s systems. The engineer’s attorney denied the allegations, and both the Social Security Administration and the company said earlier internal reviews did not substantiate the claims.
The allegations add to broader concerns about the role of the Trump administration’s DOGE cost-cutting initiative, led by Elon Musk, which embedded engineers inside federal agencies to examine government databases for fraud and inefficiencies. Earlier whistleblower complaints and court filings have already alleged that DOGE staff accessed or shared sensitive Social Security data through unapproved channels, prompting ongoing audits and congressional scrutiny over whether privacy protections for millions of Americans were compromised. (Meryl Kornfield, Elizabeth Dwoskin, and Lisa Rein / Washington Post)
Related: TechCrunch, r/politics, WION, Common Dreams, MarketWatch, New Republic
Meta unveiled new protections across its platforms designed to detect and disrupt online scams earlier in user interactions, as organized fraud operations continue to generate billions of dollars in global losses.
The company said it is expanding Messenger scam-detection tools, introducing warnings when users link new devices to WhatsApp accounts, and testing alerts on Facebook to flag potentially suspicious friend requests.
The announcement coincided with a multinational law enforcement operation targeting scam syndicates linked to Southeast Asian “pig butchering” investment schemes. Authorities, including the Royal Thai Police, FBI, UK National Crime Agency, and Australian Federal Police, arrested 21 suspects and helped Meta identify and deactivate more than 150,000 accounts tied to scam compounds that targeted victims across the United States, United Kingdom, and Asia-Pacific region.
Meta said it has intensified enforcement against scam networks, removing 10.9 million Facebook and Instagram accounts associated with scam centers in 2025 and taking down more than 159 million scam advertisements. The company also said it plans to expand advertiser verification so that 90 percent of advertising revenue comes from verified advertisers by 2026 and is deploying AI systems to detect impersonation scams and malicious links, while emphasizing that cooperation between technology firms and global law enforcement remains critical to combating large-scale fraud networks. (Lily Hay Newman / Wired)
Related: Meta, Meta, Engadget, The Verge, Axios, Channel News Asia, Bleeping Computer
Chinese authorities have moved to restrict the use of OpenClaw AI applications on government and state-owned enterprise devices, citing potential security risks as the agentic AI platform rapidly gains popularity across the country.
According to people familiar with internal notices, government agencies and major state-run institutions — including large banks — were warned against installing OpenClaw software on office computers and instructed to report any existing installations for review and possible removal.
Some organizations imposed broader restrictions, banning employees from installing OpenClaw on both work computers and personal phones connected to corporate networks, with one person saying the prohibition extended to family members of military personnel.
Other notices required prior approval before the software could be used. The warnings reflect growing concern in Beijing about the platform’s broad access to user data and its ability to communicate externally, which officials fear could expose sensitive systems to outside attacks.
OpenClaw, developed by Austrian software engineer Peter Steinberger, has gained a cult following since its launch in November for its ability to autonomously complete tasks such as managing inboxes, booking reservations, and interacting through messaging apps like WhatsApp and Slack.
Despite rising security concerns, Chinese technology companies, including Tencent and Alibaba, have launched their own OpenClaw-based tools amid surging interest in AI agents, even as regulators signal increasing scrutiny over the technology’s potential risks to data security and government control. (Bloomberg)
Related: Reuters, The Information, Tech in Asia, Nikkei Asia, Bloomberg, South China Morning Post
A foreign hacker breached a server at the FBI’s New York Field Office in February 2023 and accessed files related to the bureau’s investigation of financier and convicted sex offender Jeffrey Epstein, according to a source familiar with the matter and Justice Department documents.
The FBI described the incident as an isolated “cyber incident,” saying it quickly restricted the attacker’s access and secured the network while the investigation continues.
The intrusion occurred at the Child Exploitation Forensic Lab after a server was inadvertently left exposed while an FBI agent was navigating procedures for handling digital evidence. According to internal documents, the breach was discovered the day after it occurred when the agent found a text file on the system warning that the network had been compromised.
Investigators later detected unusual activity on the server, including searches through files connected to the Epstein case, though it remains unclear which specific materials were accessed or whether any data was downloaded.
A person familiar with the incident said the attacker appeared to be a cybercriminal rather than a state-backed operative and may not have realized the system belonged to the FBI. The hacker reportedly left a message expressing disgust at the presence of child exploitation material on the server and threatened to report it to authorities.
FBI officials ultimately convinced the intruder that the system belonged to law enforcement by showing credentials during a video call, though the hacker’s identity, location, and whether any data was taken remain unknown. (Raphael Satter / Reuters)
Related: Modern Diplomacy, r/news
The Senate confirmed Donald Trump’s pick to lead Cyber Command and the National Security Agency in a dual-hatted capacity, giving the signals intelligence and hacking titans their first permanent leader in almost a year.
Gen. Joshua Rudd was confirmed in a 71-29 vote some three months after he was nominated to the position. NSA and Cyber Command have been without a permanent leader since far-right activist Laura Loomer pushed for the firing of the post’s previous occupant, Gen. Timothy Haugh, last April. Since then, Lt. Gen. William Hartman has led the agency in an acting capacity.
On Monday, the first procedural hurdle to Rudd’s confirmation cleared in a 68-28 vote. The nominee to lead Cyber Command and the NSA usually moves through the Senate without such a vote, but Senate Majority Leader John Thune (R-SD), bypassed a hold from Sen. Ron Wyden (D-OR), to confirm Rudd after Wyden pledged to block the nominee over concerns about his experience. (David DiMolfetta / NextGov/FCW)
Related: The Record, Politico, Axios, Breaking Defense, DefenseScoop
Quittr, an app designed to help men stop watching pornography, exposed highly sensitive data belonging to hundreds of thousands of users due to a long-standing security flaw.
The app leaked personal information, including users’ ages, masturbation habits, emotional responses to pornography, and written confessions. Data from more than 600,000 users was reportedly accessible through a misconfigured database, including about 100,000 accounts belonging to minors.
An independent security researcher discovered the vulnerability in September 2025 while scanning popular mobile apps for common Google Firebase configuration errors.
The researcher alerted Quittr cofounder Alex Slater, who initially acknowledged the issue and promised to fix it quickly, according to WhatsApp messages reviewed by 404 Media. However, the flaw reportedly remained unresolved for months, leaving user data exposed despite repeated warnings from the researcher and inquiries from journalists.
Quittr, founded by Slater and Connor McLaren—members of a group of young developers known as the “App Mafia”—has claimed more than 1.5 million downloads and roughly $500,000 in monthly revenue.
The developers previously denied that sensitive user information had been exposed, but the vulnerability was ultimately fixed after media scrutiny intensified. The case highlights growing concerns over security practices in consumer apps that collect deeply personal behavioral data. (Emanuel Maiberg / 404 Media)
Related: Techlicious
Microsoft released its March 2026 Patch Tuesday security updates, addressing 79 vulnerabilities across its products, including two publicly disclosed zero-day flaws, covering a wide range of Microsoft software and services, including Windows, Microsoft Office, Azure, and other core components, with several vulnerabilities rated critical because they could allow remote code execution.
The two zero-day vulnerabilities had already been publicly disclosed before patches were available, increasing the risk that attackers could attempt to exploit them. In addition to the zero-days, the update includes fixes for multiple categories of security weaknesses, including privilege-escalation bugs, information-disclosure issues, spoofing vulnerabilities, and remote-code-execution flaws affecting Windows systems.
Security experts are urging organizations and users to apply the updates as soon as possible, noting that attackers frequently target unpatched vulnerabilities and can sometimes combine them to gain deeper access to compromised systems. Microsoft releases its Patch Tuesday updates on the second Tuesday of each month as part of its regular security update cycle. (Lawrence Abrams / Bleeping Computer)
Related: Cyber Security News, Qualys Blog, SANS Internet Storm Center, Reddit cybersecurity, Reddit cybersecurity, CSO Online, Windows Central, Neowin, The Register, HackRead, Security Week, Krebs on Security, Help Net Security, CyberScoop, Infosecurity Magazine, Ask Woody
Giant Canadian grocery, apparel, and banking giant Loblaw is investigating a data breach after identifying suspicious activity on a contained, non-critical part of its IT network.
The retailer said a criminal third party accessed some basic customer information, such as names, phone numbers, and email addresses, but its probe indicates that passwords, health data, and credit card information were not compromised.
Loblaw said it has notified customers of the breach. They will be automatically logged out of their accounts and will have to sign back in to access their digital services.
The company said its financial services subsidiary, PC Financial, was not impacted and the incident was not expected to affect its financial performance. (Sanskriti Shekhar / Reuters)
Related: Toronto City News, The Star, Reuters, The Canadian Press
The US cybersecurity agency CISA expanded its Known Exploited Vulnerabilities (KEV) catalog with another Ivanti bug, urging its immediate patching.
The issue, tracked as CVE-2026-1603 (CVSS score of 8.6), is a high-severity authentication bypass vulnerability in Ivanti Endpoint Manager that could be exploited to leak credential data.
Impacting all Endpoint Manager iterations before version 2024 SU5, the security defect was patched in early February, when Ivanti said it was not aware of its in-the-wild exploitation. The company has yet to update its advisory.
CISA urged federal agencies to apply patches for CVE-2026-1603 within two weeks, which is one week faster than the typical three-week patching window mandated by Binding Operational Directive (BOD) 22-01.
The same pathing window applies to another vulnerability newly added to KEV, namely CVE-2021-22054 (CVSS score of 7.5), a high-severity server-side request forgery (SSRF) issue in Omnissa Workspace One UEM (formerly VMware Workspace One UEM).
Patched in December 2021, the issue could allow an attacker with network access to UEM to send unauthenticated requests and access sensitive data in the management console. (Ionut Arghire / Security Week)
Related: The Record
Laurens County, SC, is trying to claw back more than $1.5 million in taxpayer funds a lawsuit alleges were stolen in a cyberattack that tricked the county into paying fake invoices.
The county has asked a circuit court judge for an injunction that would give it the authority to freeze the money from being spent and the ability to investigate bank records to identify the unknown parties responsible for the scheme.
In a March 10 statement to The Post and Courier, County Administrator Jerre Threatt said he couldn’t comment on a pending criminal investigation. He wanted to clarify that there is no suggestion of impropriety by anyone associated with the county.
“Laurens County is working diligently with State and Federal law enforcement officials in the course of their investigations and continues to pursue recovery options to make County taxpayers whole,” Threatt said.
The cyberattack dates back almost three months to Dec. 15, when the suit alleges unknown scammers — listed in the legal filings as John and Jane Doe — first reached out to the county posing as a contractor submitting an invoice for payment. (Eric Connor / Post and Courier)
Related: Fox Carolina
Hackers breached the website of the Academy of the Hebrew Language, replacing the homepage with a message declaring, “No need to learn Hebrew anymore. You won’t need it much longer.”
The cyberattack comes amid the ongoing U.S.-Israeli war with Iran and appears to be part of a broader wave of cyber activity targeting Israeli institutions.
The Academy of the Hebrew Language is Israel’s official body responsible for the study and cultivation of Hebrew, charged by law with guiding the development of the language.
Visitors to both the Hebrew and English versions of the academy’s website were redirected to the threatening message, accompanied by an image of “Handala,” a symbol associated with the Palestinian national movement. (Jewish News Service)
Related: Ynet News, The Times of Israel
Ukraine has said its offensive cyber operations last year inflicted $220 million worth of damage on Russia in direct losses.
In a post on Facebook, the General Staff of the Ukrainian Armed Forces said Russia’s indirect losses as a result of the operations exceeded $1.5 billion.
The post highlighted the effective cooperation between cyber warfare units and other components of the Ukrainian Defense Forces, successfully identifying and striking Russian military facilities. (Stanisław Kaleta /TVP World)
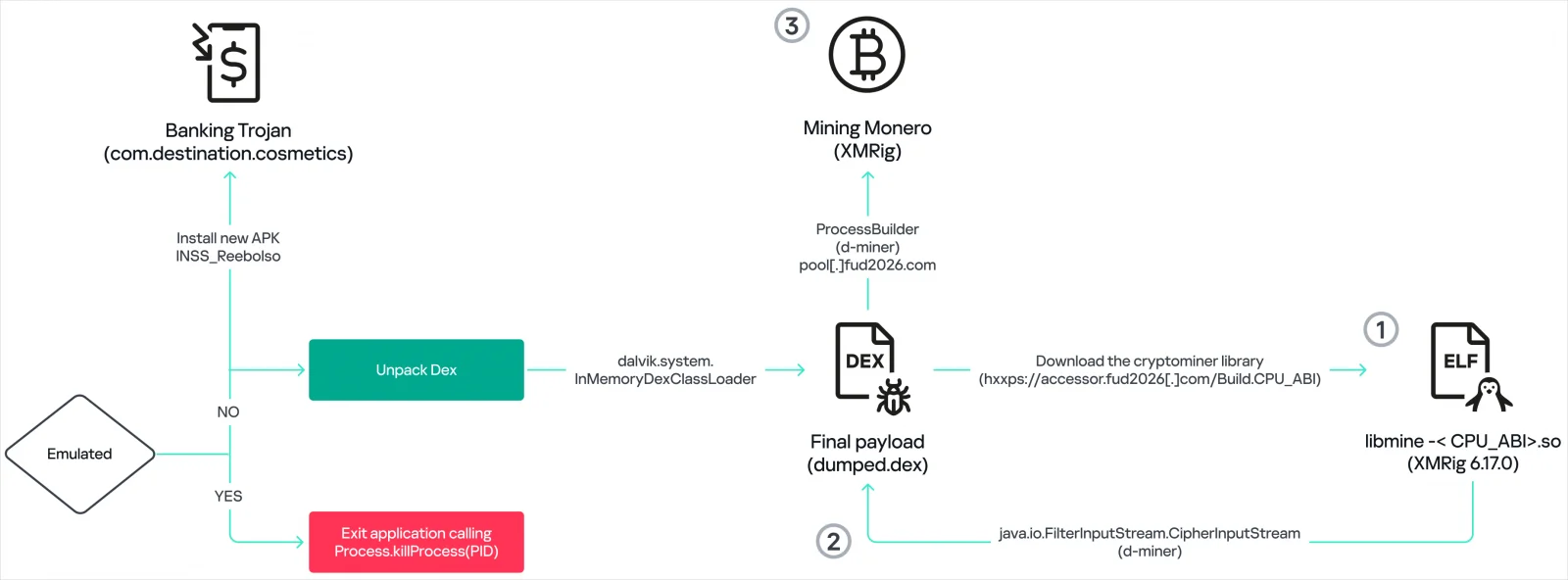
Researchers at Kaspersky report that a new Android malware named BeatBanker can hijack devices and trick users into installing it by posing as a Starlink app on websites masquerading as the official Google Play Store.
The malware combines banking trojan functions with Monero mining, and can steal credentials, as well as tamper with cryptocurrency transactions.
Kaspersky researchers discovered BeatBanker in campaigns targeting users in Brazil. They also found that the most recent version of the malware deploys the commodity Android remote access trojan called BTMOB RAT, instead of the banking module.
BTMOB RAT provides operators with full device control, keylogging, screen recording, camera access, GPS tracking, and credential-capture capabilities.
BeatBanker uses a modified XMRig miner version 6.17.0, compiled for ARM devices, to mine Monero on Android devices. XMRig connects to attacker-controlled mining pools using encrypted TLS connections, and falls back to a proxy if the primary address fails.
The miner can be dynamically started or stopped based on device conditions, which the operators closely monitor to ensure optimal operation and maintain stealth. (Bill Toulas / Bleeping Computer)
Related: Securelist
In a joint announcement, the UK Home Office and the National Crime Agency said that a new online crime center is designed to crack down on fraud and will combine expertise from government, intelligence agencies, the police, banks, mobile networks, and major technology firms.
Set to begin work in April, the Online Crime Centre is tasked with actively disrupting cyber-criminal operations, including overseas scam compounds.
In recent years, these criminal operations have scaled hugely, providing those working in the compounds, many of whom are victims in their own right who are there under duress, with scripts and procedures to help target vast numbers of people at once.
The centre will identify the accounts, websites, and phone numbers that cyber-criminal gangs rely on and shut them down. Activities that are set to be taken include blocking scam texts, freezing criminal accounts, removing scam social media accounts, and disrupting operations at source. (Danny Palmer / Infosecurity Magazine)
Related: Gov.uk, Decrypt, UKTN, Association of British Insurers, Cryptonews.net
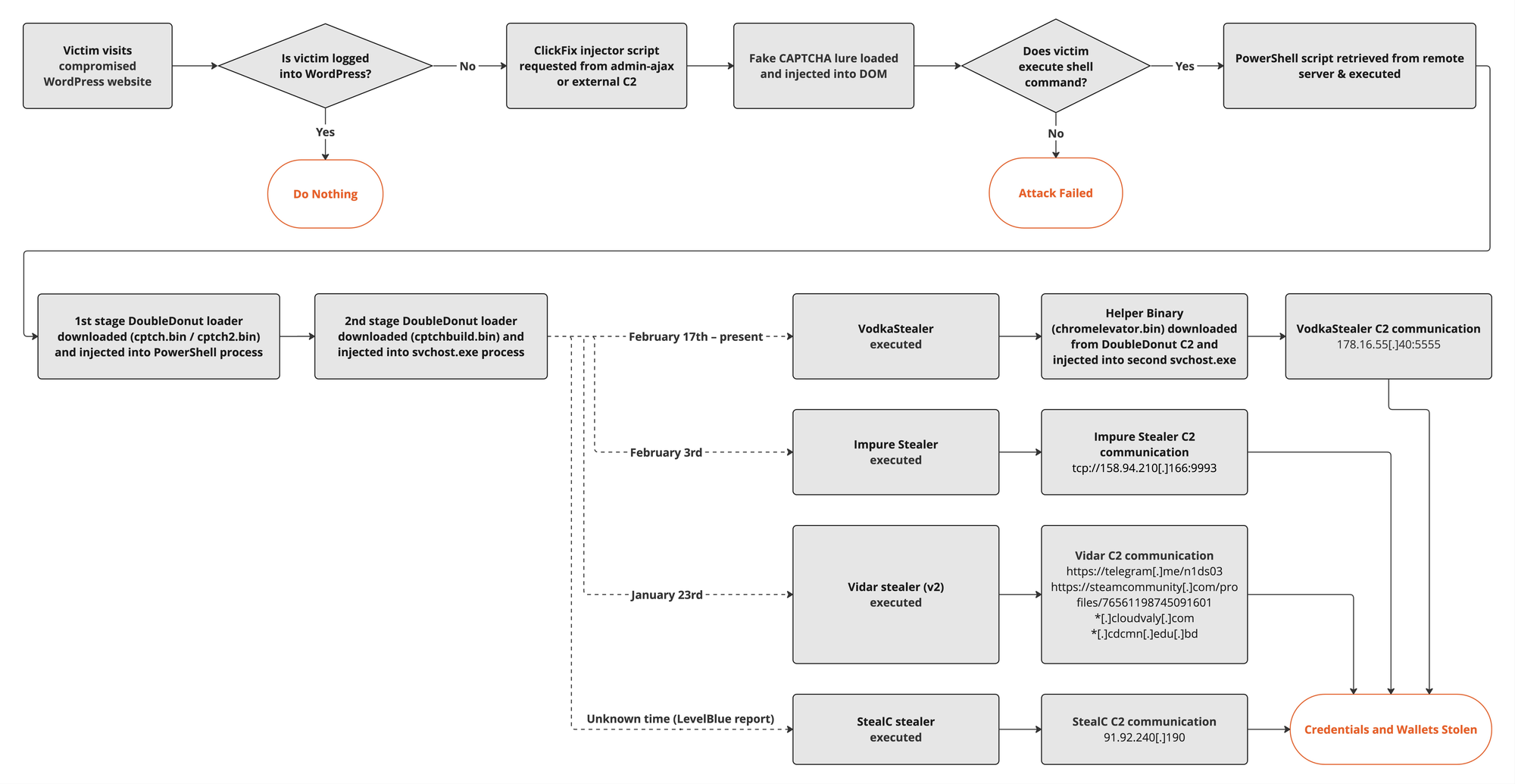
Researchers at Rapid7 report that cybercriminals quietly compromised legitimate WordPress websites in a large-scale fashion, including the campaign site of a US Senate candidate, turning them into launchpads for a global infostealer operation.
They say the scheme works by injecting malicious code into compromised sites, which then serve visitors a convincing fake Cloudflare CAPTCHA page. Instead of simply proving you're not a robot, the prompt instructs users to copy and run a command on their machine – a step that ultimately triggers the download of credential-stealing malware.
The trick works because the attack starts on websites that otherwise look legitimate. Visitors think they're just clearing yet another Cloudflare bot check – the sort that litters the modern web – when in fact they're being talked through the first step of infecting their own machine.
The technique is part of the now well-worn ClickFix social engineering playbook, in which attackers persuade victims to execute commands themselves under the guise of fixing or verifying something on their systems.
The infected sites span a broad mix of organizations. According to Rapid7, compromised pages include regional media outlets, small business websites, and "in one case even a United States Senate candidate's official webpage." The company says it notified US authorities to investigate the issue and clean it up. (Carly Page / The Register)
Related: Rapid7, Cyber Daily
Researchers at ESET report that the Russian state-sponsored APT28 threat group is using a custom variant of the open-source Covenant post-exploitation framework for long-term espionage operations.
Also tracked as Fancy Bear, Forest Blizzard, Strontium, and Sednit, the APT28 hacker group is known for developing high-end implants and breaching notable entities, such as the German Parliament, multiple French organizations, government networks in Poland, and European NATO member countries.
ESET noticed that since April 2024, the Russian group has started using in attacks two implants named BeardShell and Covenant.
"This dual-implant approach enabled long-term surveillance of Ukrainian military personnel," ESET notes in a report today.
The two pieces of malware have been used recently to target central executive bodies of Ukraine in attacks that exploited the CVE-2026-21509 vulnerability in Microsoft Office via malicious DOC files.
The researchers uncovered these malware families after discovering SlimAgent, a keylogging implant deployed in a Ukrainian government system capable of keystroke capture, clipboard collection, and screenshot capture.
BeardShell is a modern implant that leverages the legitimate cloud storage service Icedrive for command-and-control (C2) communication. It can execute PowerShell commands in a .NET runtime environment and was used together with SlimAgent, according to a report from CERT-UA in June 2025.
ESET found that BeardShell also uses a unique obfuscation technique previously seen in Xtunnel, a network-pivoting tool that APT28 used in the 2010s.
In the recent attacks, the Russian threat group paired BeardShell with a heavily modified version of the open-source Covenant .NET post-exploitation framework. (Bill Toulas / Bleeping Computer)
Related: We Live Security
US Homeland Security investigators used artificial intelligence to generate the image of a fictitious 13-year-old girl as part of an undercover operation that led to the arrest of a man accused of distributing child sexual abuse material, according to court documents.
The AI-generated persona was deployed in online chatrooms frequented by teenagers, where investigators said a male user began communicating with the profile, requesting additional images and later sending explicit material while attempting to groom the supposed minor.
Authorities identified the suspect as Marcell Meyer, a 43-year-old South African citizen living in New York. Prosecutors say Meyer sent pornographic images and child sexual abuse material during the exchanges. He has been charged with distribution of child sexual abuse material and faces up to 20 years in prison if convicted. Meyer has not yet entered a plea and is presumed innocent unless proven guilty.
The case highlights how law enforcement is beginning to use AI-generated personas in sting operations targeting online predators, expanding on earlier efforts that relied on human investigators or simpler chatbots posing as minors. Advocates say AI tools allow investigators to create unlimited realistic identities without exposing real people to risk, though the approach could raise concerns among civil liberties groups about the broader use of AI personas in surveillance and undercover investigations. (Thomas Brewster / Forbes)
Related: US Senate, NextGov/FCW, DefenseScoop
Russian cybersecurity company Kaspersky was forced to cut staff in France as it continues to pay the price for the collateral damage of the war in Ukraine.
Revenue at its French subsidiary fell by a quarter between 2021 and 2024, from nearly €30 million to €22.4 million, and the workforce was reduced by a fifth.
A plan to optimize the company's operations in the European region was launched in the second half of 2025. "The current situation in the French market necessitates laying off several employees for economic reasons," the company stated in its latest financial statements.
"The goal is to guarantee Kaspersky's continued presence in France." A sign of the intense pressure, the French entity has changed its CEO three times in three years, culminating in the appointment of Cesare D'Angelo last April. (Emmanuel Paquette / L'informe)
Israeli cybersecurity company Jazz announced it had raised $43 million in a Series A venture funding round.
Glilot Capital Partners and Team8 led the round, with participation from Ten Eleven Ventures (1011vc), MassMutual, Merlin Ventures, and leading cyber and AI entrepreneurs, including the founders of Decart, Tenzai, and Oligo Security. (Meir Orbach / Calcalist)
Related: BankInfoSecurity, Security Week, Ventureburn, Pulse 2.0, Ynet News, Bloomberg
Previously bootstrapped cybersecurity startup Quantro Security emerged from stealth mode with $2.5 million in seed funding from Google’s early-stage AI fund Gradient.
Founded in 2025 by veterans of CrowdStrike, Tenable, and Qualys, New York-based Quantro has built VM.Analyst, an AI agent that harvests data from multiple sources to provide actionable intelligence. (Ionut Arghire / Security Week)
Related: Quantro Security, Pulse 2.0, Silicon Angle, CityBiz
Google has officially acquired Israeli cybersecurity firm Wiz for $32 billion in cash, a full year after the companies announced the deal. This marks Google’s biggest acquisition in its history.
Wiz provides a security platform that protects major cloud environments by preventing and responding to cybersecurity threats. While the company will join Google Cloud, it will maintain its brand and commitment to securing customers across all cloud environments, the company said.
The deal comes after Wiz crossed $1 billion in ARR in 2025, according to a source familiar with the matter. (Rebecca Bellan / TechCrunch)
Related: Google, Google Cloud, Wiz
Best Thing of the Day: Light at the End of the Cyberattack Tunnel
Japanese alcoholic drink maker Asahi Breweries plans to resume shipments of all its products starting April 7 after a halt due to a computer system failure caused by a February cyberattack on its parent.
Worst Thing of the Day: Haven't You Heard? We Can Trust Russia
Apparent Russia-linked hacking collectives backing Iran have been observed joining the cyber activity unfolding alongside the US-Israel war against Iran.
Closing Thought