EU sanctions Iranian, Chinese companies for cyberattacks
Stryker denies report of data exfiltration in "Handala" attack, Teens sue xAI for sexually explicit images, Man charged with scam schemes while impersonating adult film star, Canadian bill expands cops' lawful access to telecom data, MedTech firm Intuitive hit by phishing incident, much more


Check out my latest CSO piece that examines how runtime security could be a key security solution for the growing multitude of AI agents roaming around organizations.
If you rely on Metacurity to make sense of cybersecurity policy, industry developments, and security research, please consider supporting the newsletter with a paid subscription.
Metacurity is a daily infosec intelligence layer written independently of vendor marketing, PR-driven threat intelligence, and the cyber media echo chamber. Paid subscriptions make it possible to keep producing clear, straightforward analysis every day. Please consider upgrading your subscription. Thank you!
The European Union imposed sanctions against two China-based and one Iranian company for cyberattacks against EU member states.
Integrity Technology is seen to have enabled hacks of over 65,000 devices across six member states, according to an EU statement. Anxun is seen to have provided hacking services aimed at critical infrastructure, according to the EU.
The EU has individually listed two co-founders of Anxun for their involvement in cyberattacks.
Emennet is seen to have compromised advertising billboards to spread disinformation during the 2024 Paris Olympics.
Sanctions include an asset freeze and a travel ban for the individuals. EU citizens and companies are also prohibited from making funds available for the companies involved. (Bart Meijer and Laurie Chen / Reuters)
Related: European Council, Cyber Daily, DigWatch, Politico
Medical supply giant Stryker, which disclosed that last week’s cyberattack was confined to its internal Microsoft environment and did not affect its medical devices, which remain safe to use, has confirmed that the incident disrupted key business systems, including electronic ordering, forcing customers to place orders manually through sales representatives while restoration efforts continue.
The company stressed that the attack was not ransomware and that no malware was deployed on its systems.
The attack has been attributed to the hacktivist group Handala, believed to have links to Iran, which claimed it wiped more than 200,000 systems and stole 50 terabytes of data. Stryker and its investigators have disputed those claims, saying there is no evidence of data exfiltration.
Still, the disruption was significant: employees across multiple countries reported that tens of thousands of managed devices—and in some cases personal devices enrolled in the corporate network—were remotely wiped.
According to sources, the attackers gained access by compromising an administrator account and escalating privileges to create a new Global Administrator account. They then used Microsoft Intune to issue remote wipe commands to roughly 80,000 devices within a three-hour window.
The investigation, led by Microsoft’s Detection and Response Team alongside Palo Alto Networks’ Unit 42, is ongoing, while Stryker focuses on restoring supply chain operations, resuming order processing, and stabilizing its internal systems. (Ionut Ilascu / Bleeping Computer)
Related: The Record, Cyber Daily
A group of Tennessee teenagers has filed a lawsuit against xAI, the artificial intelligence company founded by Elon Musk, alleging its Grok chatbot was used to generate sexually explicit images of them by digitally “undressing” photos in which they were clothed.
The complaint, filed in federal court in California, stems from a criminal case in which a suspect allegedly used AI tools to alter images of at least 18 underage girls, many from the same school, and distribute the content on platforms such as Discord and Telegram.
Some of the images were reportedly traded for other child sexual abuse material, amplifying their spread.
The plaintiffs, including two minors, argue that xAI’s tools enabled the creation of illegal content by design, alleging the company fostered an environment where such misuse was foreseeable. Attorneys claim the technology—particularly features tied to Grok’s image-generation and editing capabilities—allowed users to create sexualized depictions of real people, including minors, and that the resulting images constitute child pornography under US law.
The suit seeks damages and calls for restrictions on such editing features, with lawyers warning the victims may face lifelong consequences as the images continue to circulate online.
xAI and Musk have denied knowledge of any generation of explicit images involving minors, with Musk stating earlier this year that Grok is designed to refuse illegal requests and that any misuse would be addressed as a bug. The controversy follows broader scrutiny of the company’s tools, which had allowed users to create sexualized imagery of real individuals, prompting investigations by regulators in the United States and Europe.
The lawsuit marks one of the first legal actions brought by alleged minor victims tied to AI-generated “undressing” technology, raising new questions about platform liability and safeguards in generative AI systems. (Faiz Siddiqui / Washington Post)
Related: BBC News, The Guardian, USA Today
A Georgia man, Kwamaine Jerell Ford, has been charged in a wide-ranging scheme that allegedly targeted professional NBA and NFL athletes through social engineering while impersonating a well-known adult film star.
Prosecutors say Ford, 34, used fake social media personas and spoofed Apple customer service messages to trick victims into sharing iCloud login credentials and multifactor authentication codes, giving him access to sensitive personal and financial data. He is accused of carrying out more than 2,000 unauthorized transactions between 2020 and 2024.
Authorities allege Ford conducted part of the scheme while serving a federal prison sentence for a similar earlier fraud case, and continued after his release on probation in 2022. Once inside victims’ accounts, he allegedly stole credit card information, identification documents, and other personal data to fund his lifestyle.
Ford has pleaded not guilty to 22 charges, including wire fraud, identity theft, and access device fraud, and is being held without bail pending trial.
Prosecutors also accuse Ford of escalating his conduct by coercing an OnlyFans model into participating in recorded sex acts with athletes without their knowledge, which he allegedly arranged and monetized. Officials say he used the videos to lure victims further and extract money, adding potential sex trafficking charges to the case. (Matt Kapko / CyberScoop)
Related: Justice Department, Fox5 Atlanta, Atlanta News First, WSB
Canada’s Liberal government has introduced Bill C-22 to update lawful access rules, which officials say will help police identify people using social media or AI for crime or national security threats.
The government says it balances safety with privacy after backlash to earlier proposals.
The bill lets authorities ask telecom companies to confirm whether a suspect is a customer. More detailed data, like phone numbers or addresses, would still require a warrant. It also creates a framework for requesting information from foreign tech and AI firms, without forcing them to comply.
The legislation would require providers to enable location tracking capabilities for investigations. Officials say this could improve both policing and emergency response. The bill follows earlier failed efforts that raised concerns about expanded surveillance powers. (Peter Zimonjic / CBC News)
Related: Michael Geist, The Globe and Mail, Canadian Chamber of Commerce, Global News, CTV News
MedTech firm Intuitive disclosed a targeted phishing incident hit it but said the attack did not disrupt operations or customer support.
The company said it quickly activated its incident response and secured affected systems after discovering the breach.
The company emphasized that its core products—including the da Vinci surgical system and Ion platform—were not impacted. It said its network architecture is segmented, keeping internal IT systems separate from manufacturing and clinical platforms, as well as from hospital customer networks.
According to Intuitive, the breach stemmed from a compromised employee account within its internal administrative network. Some customer contact information and corporate data were accessed, though details remain limited. The company said the investigation is ongoing and regulators have been notified. (Ross Law / Medical Device Network)
Related: The Register, Medical Device and Diagnostic Industry, MedTech Dive
Security researcher Jeremiah Fowler was surprised and alarmed last month when he found three publicly exposed Sears databases containing massive troves of chat logs, audio files, and text transcriptions of audio that contained personal details about Sears Home Services customers, which apparently leaked from the company's AI chatbot and phone assistant named Samantha.
The exposed Sears databases uncovered by Fowler, which have since been secured, contained 3.7 million chat logs, plus 1.4 million audio files and plain text transcripts from 2024 to this year. Fowler found that one CSV file about the incident contained 54,359 complete chat logs. Conversations Fowler saw included the chatbot introducing itself as “Samantha, an AI virtual voice agent for Sears Home Services,” with the logs also including the name of the company’s AI technology “kAIros.”
The cache of data contained chats in both English and Spanish and included personal information about Sears customers, such as names, phone numbers, home addresses, appliances owned, and information on delivery appointments and repairs. (Lily Hay Newman and Matt Burgess / Wired)
Related: Express VPN
In an analysis of publicly available contract forecasts, the Department of Homeland Security outlines its plan to award hundreds of millions of dollars in contracts in 2026 that expand detection and tracking capabilities.
These contracts are in addition to the agency putting a $1 billion ceiling on a single award blanket purchase agreement with Palantir, a software company that helps customers, like Immigration and Customs Enforcement, analyze vast datasets. That contract went into effect in February.
The ramp-up comes as questions and concerns circulate about the effectiveness of oversight of the department by lawmakers, the DHS inspector general, and others. (Lindsey Wilkinson / FedScoop)
Qihoo 360, one of the biggest cybersecurity companies from China, accidentally shipped a highly sensitive wildcard SSL private certificate inside the public installer for its 360 Security Claw AI assistant.
The assistant is the company"s wrapper on OpenClaw, the viral open-source AI agent, and the godfather of all the new AI agentic tools with the “Claw” suffix. This oversight gives anyone who downloaded the software the exact master key needed to authenticate traffic on the company"s backend infrastructure.
Security researcher Lukasz Olejnik discovered the valid SSL certificate for the platform's myclaw.360.cn domain sitting completely unprotected inside an uncompressed archive. Anytone only needs a basic extraction tool to unpack the installer and pull the private key right out of it.
The certificate is valid until April 2027 and covers every subdomain on the platform. To add insult to injury, Qihoo"s founder Zhou Hongyi launched the product with a public promise that it would "never leak passwords." The company currently serves around 461 million users and is valued at $10 billion.
Having a wildcard private key floating around the internet opens the door to serious infrastructure attacks. Malicious actors could use this leaked file to impersonate 360's servers, intercept user traffic, or build incredibly convincing phishing pages that browsers will treat as completely legitimate. (Ivan Jenic / Neowin)
Related: Barrack, r/sysadmin, Cyber Security News
According to researchers at Step Security, threat actors have been abusing credentials stolen in the VS Code GlassWorm campaign to hack GitHub accounts and inject malware into Python repositories.
The campaign likely started on March 8, targeting Python projects such as Django apps, ML research code, PyPI packages, and Streamlit dashboards. The purpose of the attacks is likely the theft of cryptocurrency and sensitive information.
Using compromised developer credentials, the threat actors have been rebasing the latest legitimate commits on the default branch of repositories, adding obfuscated malicious code, and then force-pushing the commits.
The malware injection method used in this campaign, which StepSecurity dubbed ForceMemo, leaves fewer traces of compromise, as both the commit message and author date remain unchanged from the original commit, and only the committer date is modified. (Ionut Arghire / Security Week)
Related: SC Media, WinBuzzer, Aikido, Dark Reading, Step Security
Spain’s data protection authority has fined UK-based digital identity firm Yoti €950,000 for violations tied to its biometric age verification services.
Regulators found the company breached multiple provisions of the GDPR, including unlawful processing of biometric data, invalid user consent, and excessive retention of personal information.
The fine includes penalties for improper handling of biometric information, flawed consent mechanisms, and retaining personal data longer than allowed under GDPR rules. Authorities found that Yoti’s facial age estimation and digital ID systems did not meet strict legal requirements for processing such data.
Regulators have ordered Yoti to implement corrective measures within six months. The case highlights growing scrutiny of biometric technologies and the compliance risks companies face when handling sensitive personal data. (Luis Espada / PPC Land)
Related: Biometric Update, ID Tech Wire, Data Guidance
According to a source, the Japanese government has warned domestic companies willing to assist in Ukraine's reconstruction about the potential for technology and sensitive information to be leaked through 5G high-speed networks supplied by Huawei Technologies.
The Japanese government opted to take the rare move from an economic security standpoint to address concerns over the use of equipment provided by the Chinese telecom giant, which the United States has blacklisted amid spying concerns.
A major Ukrainian telecoms operator, which conducted 5G trials with Huawei in some cities last year, has been granted 5G radio spectrum by the Ukrainian government.
Japanese e-commerce and mobile communications company Rakuten Group Inc. bid for 5G business in Ukraine but was unsuccessful.
Related Japanese government documents obtained by Kyodo News said that if Huawei's 5G network expands to Kyiv and other major cities, it would pose a "big risk" for Japan, Europe, and the United States to invest in critical infrastructure such as energy.
The document also warned of the possibility of Chinese products "finding their way into markets" via Turkish companies.
The Japanese government is reportedly concerned about allegations that Huawei technology is embedded with secret "back doors" that could be used to extract information. (Kyodo News)
Related: Militarnyi
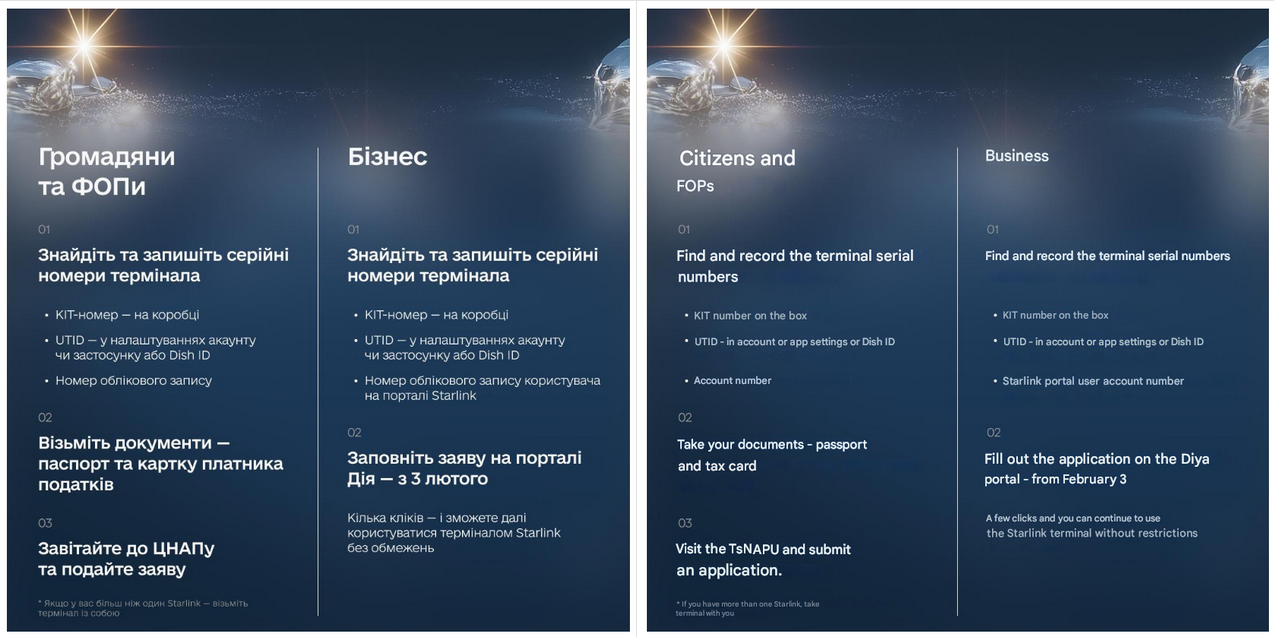
According to cybersecurity firm Lab52, a relatively new Russia-linked hacker group has launched a cyber-espionage campaign targeting Ukrainian organizations using spyware disguised within documents about Starlink satellite internet terminals and a well-known Ukrainian charity.
The campaign, observed in February, deployed a backdoor dubbed DrillApp that allows attackers to upload and download files from infected computers, record audio through a microphone, and capture images from a webcam.
Researchers attributed the campaign to the Russian-linked hacker group Laundry Bear, also tracked as Void Blizzard, which has been active since at least 2024 and has previously targeted NATO member states and Ukrainian institutions. (Daryna Antoniuk / The Record)
Related: Lab52, Security Affairs
Denver pedestrians got a surprise this weekend when the audio messages from push-button speakers on some crosswalks were mysteriously replaced with anti-President Donald Trump messages.
“The walk signal is on, Trump … (reference to the Iran school that was bombed),” a robotic voice said, according to a video on the social media platforms TikTok and Instagram.
Other messages included profanity directed at Trump, social media users reported.
Audio signals at crosswalks, known as Accessible Pedestrian Signals, are designed to assist those who are blind or have low vision navigate intersections safely.
A spokesperson for Denver’s Department of Transportation and Infrastructure told The Denver Gazette on Monday that the agency was aware of only two hacked locations — Pearl Street and Colfax Avenue, and at Colfax and Washington Street. (Deborah Grigsby / Colorado Politics)
Related: The Denver Post, Instagram, Denverite, 9News, Colorado Politics, CBS News
Google featured a Chrome extension called Save Image As for months, which was later found to contain malicious code, raising questions about oversight in the Chrome Web Store.
The extension initially appeared legitimate but was later modified to include harmful functionality without triggering detection.
Researchers said the malicious update allowed the extension to retain its trusted appearance while quietly introducing hidden code, potentially exposing users to data theft or other exploitation. The case highlights how attackers can weaponize legitimate extensions after approval. (Adam Conway / XDA Developers)
Related: Android Police, Mashable
Best Thing of the Day: The Mark of True Professionals
A Mississippi man who had been awaiting a donor for three months so he could receive a liver transplant finally got word his time had come, and in the middle of his surgery, a cyberattack hit the hospital, but the doctors carried on like champs.
Bonus Best Thing of the Day: No to Musk Rummaging Around In Classified Data
Sen. Elizabeth Warren (D-MA) sent a letter to Defense Secretary Pete Hegseth expressing concern over the Pentagon’s decision to give Elon Musk’s company xAI access to classified networks.
Extra Bonus Best Thing of the Day: Very Useful Pub Drinking
Evening gatherings in London between journalists and tech workers called Hacks/Hackers LDN, which were disbanded during the pandemic, have been relaunched as Source Code.
Worst Thing of the Day: Anyone Surprised?
According to a declassified September 2021 federal watchdog report obtained by POGO Investigates, years after Edward Snowden’s disclosures of sweeping domestic surveillance, the National Security Agency (NSA) continued to violate key rules limiting the government’s ability to conduct warrantless searches of Americans’ electronic communications.
Closing Thought