FBI probes crypto theft linked to malware-infected Steam games
Operation Synergia III busts 94 alleged cybercriminals, DPRK's Konni Group used KakaoTalk to spread info-stealing malware, Japan was hit by 226 ransomware attacks in 2025, Chinese attack on Costa Rica electricity institute sparks diplomatic row, Intellexa sold spyware to the Greek gov't, much more
If you rely on Metacurity to make sense of cybersecurity policy, industry developments, and security research, please consider supporting the newsletter with a paid subscription.
Metacurity is a daily infosec intelligence layer written independently of vendor marketing, PR-driven threat intelligence, and the cyber media echo chamber. Paid subscriptions make it possible to keep producing clear, straightforward analysis every day. Please consider upgrading your subscription. Thank you!
The FBI is seeking information from gamers who may have installed malware-infected games on the Steam platform as part of an ongoing investigation into malicious software distributed through the service.
In a notice issued by the FBI’s Seattle field office, authorities said they are attempting to identify victims who downloaded compromised titles between May 2024 and January 2026. The agency identified several affected games, including BlockBlasters, Chemia, Dashverse (also known as DashFPS), Lampy, Lunara, PirateFi, and Tokenova.
Investigators believe the malware embedded in the games was used to steal cryptocurrency and hijack user accounts. The FBI has asked potential victims to complete a questionnaire describing any stolen funds, compromised accounts, or suspicious cryptocurrency transactions.
The form also requests screenshots or other records of communications with individuals who promoted the games, which could help investigators trace the stolen assets and identify those responsible for distributing the malware.
Several of the malicious titles were discovered over the past two years after distributing information-stealing malware capable of harvesting credentials, cryptocurrency wallets, and other sensitive data from infected systems. One prominent case involved the free-to-play platformer BlockBlasters, which was initially uploaded to Steam as a legitimate game before attackers later inserted cryptodrainer malware.
The threat surfaced publicly when a streamer who installed the game reported losing more than $32,000 in cryptocurrency during a charity livestream. (Lawrence Abrams / Bleeping Computer)
Related: FBI, Polygon, Mashable, Kotaku, Decrypt, PCMag, GameSpot, TechCrunch, Cryptonews
Interpol announced the arrest of 94 people as part of a global cybercrime crackdown known as Operation Synergia III, the third phase of an international initiative launched in 2023.
The operation ran from July 18, 2025, through January 31, 2026, and targeted cyber-enabled crimes, including phishing, romance scams, and credit card fraud. Authorities also reported that 110 additional suspects remain under investigation.
During the multi-month effort, law enforcement agencies seized 212 electronic devices and sinkholed more than 45,000 malicious IP addresses linked to suspected criminal infrastructure. Neal Jetton, director of Interpol’s cybercrime directorate, said the operation demonstrates the importance of international collaboration as cybercrime grows increasingly sophisticated and destructive.
Bangladesh accounted for the largest share of arrests and seizures. Authorities there detained 40 suspects and confiscated 134 devices tied to a range of schemes, including loan and employment scams, identity theft, and credit card fraud. In Togo, police arrested ten individuals believed to have played leadership roles in a fraud ring operating from a residential neighborhood.
Interpol said members of the Togo-based group specialized in different aspects of cybercrime, with some focusing on technical activities such as compromising social media accounts, while others conducted social engineering operations, including romance and sextortion scams.
Meanwhile, police in Macau identified more than 33,000 phishing and fraud websites—many impersonating banks, government agencies, and payment services, or operating as fake online casinos designed to lure victims into depositing money they could not withdraw. (Connor Jones / The Register)
Related: Interpol, Security Affairs, GBHackers, Eurasia Review, Help Net Security, Infosecurity Magazine, HackRead, IT Pro, Bleeping Computer
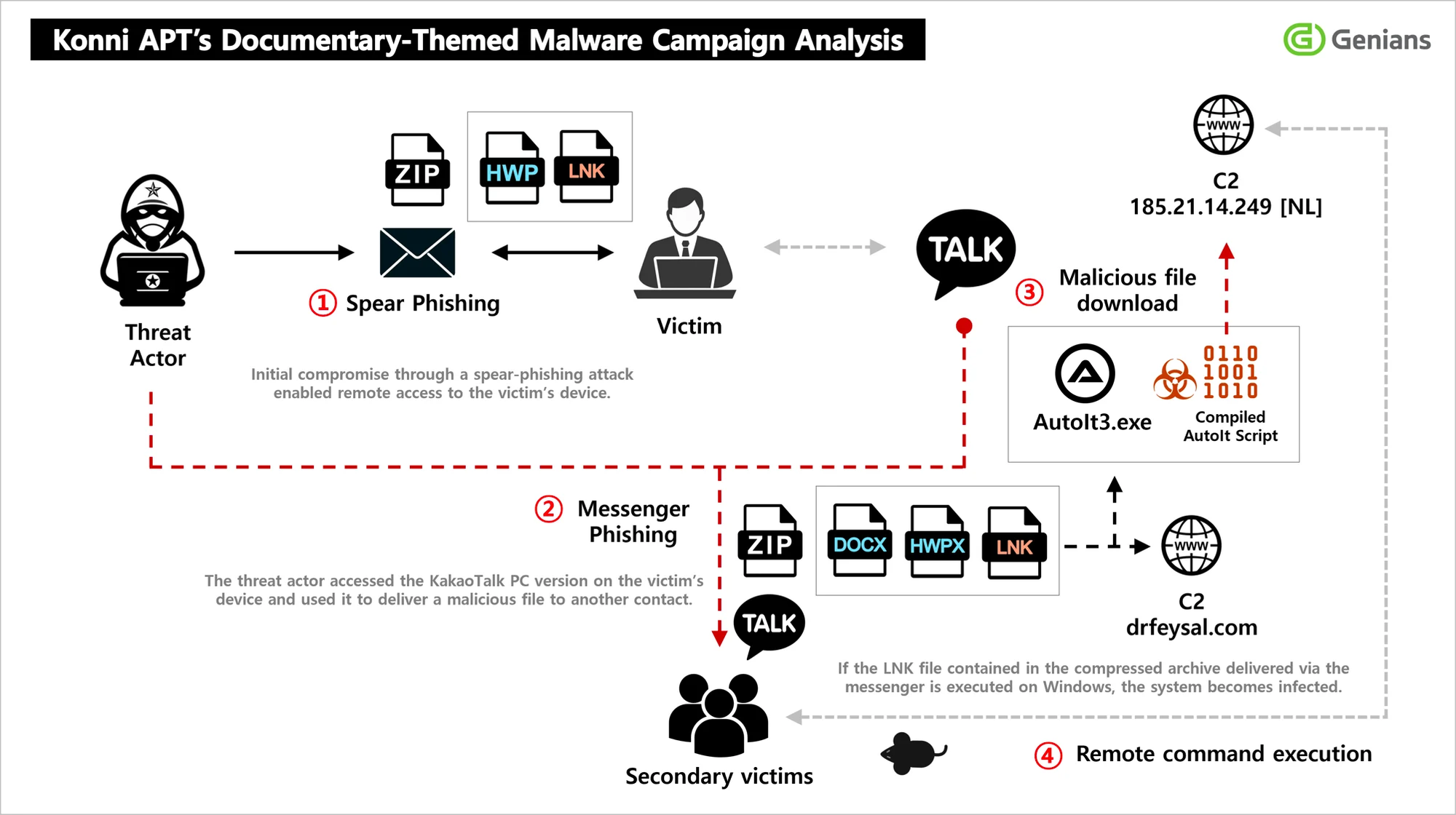
North Korea-linked hackers known as the Konni Group carried out a spear-phishing campaign that used the South Korean messaging platform KakaoTalk to distribute malware and steal sensitive information, according to the Genians Security Center.
Researchers said the attackers initially targeted victims with emails offering what appeared to be appointments as lecturers on North Korean human rights issues. The messages contained malicious shortcut files that installed remote-access malware when opened.
Once inside a victim’s system, the attackers collected internal documents and maintained persistent access while expanding the operation through compromised accounts. Investigators said the hackers took control of victims’ KakaoTalk desktop sessions and used contacts from their friend lists to send additional malicious files, creating what researchers described as a trust-based propagation chain that used existing victims as intermediaries for further attacks.
Messages were often framed as discussions about North Korea-related video content to entice recipients to open the files.
Researchers said the Konni group shares overlapping infrastructure and targets with other North Korea-linked threat actors such as Kimsuky and APT37, which have been tied to espionage and influence operations targeting South Korean institutions and civil society groups. (Thomas Maresca / UPI)
Related: Genians, Maeil Business Newspaper, GBHackers, The Korea Bizwire, The Chosun Daily, The Cyber Press, Yonhap News
Ransomware attacks reported in Japan reached 226 confirmed cases in 2025, the second-highest annual total on record, according to the country’s National Police Agency.
Authorities said the figure reflects continuing pressure from cybercriminal groups targeting Japanese organizations, particularly through data-extortion schemes that disrupt business operations.
Police said small and midsize businesses accounted for roughly 60% of victims.
The report also noted the increasingly organized nature of cybercrime targeting Japan, with attackers using phishing campaigns, malware, and other intrusion techniques to gain initial access to corporate networks before deploying ransomware.
Authorities warned that the attacks are becoming more sophisticated and urged businesses to strengthen defenses, including better monitoring and employee training to detect phishing attempts. (The Japan Times)
Related: Nippon.com, The Mainichi, Asia News Network
China asked Costa Rica to provide evidence supporting allegations that Chinese-linked actors were responsible for a cyberespionage attack on the Costa Rican Electricity Institute (ICE), escalating tensions between the two countries.
The request was made publicly by Chinese Ambassador Wang Xiaoyao after Costa Rican officials linked a January breach at the state utility to the group UNC2814, which Google has described as a suspected cyberespionage actor tied to China.
Chinese officials said the evidence is needed to verify the claims and pursue legal action if warranted. Beijing also said it has attempted since 2024 to engage Costa Rica in cybersecurity cooperation through consultations, professional exchanges, and mechanisms tied to the United Nations cybercrime framework, but had received no response from Costa Rican authorities.
Costa Rican officials said the breach was detected in late January in ICE administrative email systems and involved the extraction of about nine gigabytes of internal data. Authorities said the incident did not disrupt electricity or telecommunications services and did not compromise customer information, but the attribution to a China-linked group has turned the cyber incident into a broader diplomatic dispute between the two countries. (Tico Times)
Related: Convergencia Latina, The Cyber Express, Tico Times
A convicted spyware dealer has linked the Greek government to a major surveillance scandal, alleging that authorities were connected to the deployment of Predator spyware used to monitor journalists, politicians, and other figures.
The claims were made by Tal Dilian, the founder of the spyware company Intellexa, after he and several associates were convicted in Greece for illegally accessing private communications.
Dilian said that Intellexa sells its surveillance technology only to governments, suggesting that state authorities must have been behind the use of Predator spyware in Greece. The case centers on a broader wiretapping scandal that has drawn intense scrutiny over how the spyware was used and who authorized its deployment against domestic targets.
Greek officials have denied involvement in the surveillance campaign, while critics say Dilian’s comments reinforce longstanding suspicions that the government played a role. The controversy has fueled political tensions in Greece and raised broader concerns across Europe about the use of commercial spyware and the oversight of surveillance technologies. (Eliza Triantafillou / OCCRP)
Related: Mega Stories, Greek City Times, Tovima.com
A technical flaw in the UK Companies House website exposed sensitive personal and corporate data and allowed unauthorized users to access or potentially modify company filings, raising concerns about fraud and data security.
The vulnerability affected the government’s official corporate registry, which holds records for millions of companies, and was discovered after users found they could bypass authorization controls within the WebFiling system.
The glitch enabled individuals to view private information such as directors’ home addresses, email addresses, and full dates of birth—data that is normally restricted from public view. In some cases, the flaw could also have allowed attackers to alter company records by manipulating the website’s navigation process, potentially enabling fraudulent changes to corporate filings.
After being alerted to the issue, Companies House suspended its online filing service while investigators worked to fix the vulnerability and assess the impact. Officials apologized for the incident and launched an investigation, while experts warned that exposed data could be exploited for fraud if malicious actors had discovered the flaw before it was reported. (Ashley Armstrong / Financial Times and Phil Muncaster / Infosecurity Magazine)
Related: Tax Policy Associates, The Times, Daily Mail
Eight major technology companies, including Google, Amazon, Microsoft, and OpenAI, have signed a new pledge to share threat intelligence about how scammers exploit their platforms, in an effort to strengthen industry coordination against online fraud.
The agreement, called the “Online Services Accord Against Scams,” was announced ahead of the U.N. Global Fraud Summit in Austria and aims to establish expectations for how companies cooperate with one another, law enforcement, and governments to disrupt scam networks.
The companies — which also include LinkedIn, Meta, Adobe, and Match Group — said they will expand information sharing about transnational criminal groups, collaborate on best practices for detecting fraud, and deploy new defensive tools such as artificial intelligence systems to identify scams more quickly. The accord also calls for stronger verification requirements for financial transactions on their services and clearer reporting channels for users who encounter scams.
The agreement is voluntary and carries no enforcement penalties, but companies said it will allow faster information exchange and more coordinated efforts to disrupt global scam infrastructure. (Sam Sabin / Axios)
Related: DigWatch
The European Union is preparing to ban artificial intelligence systems that can generate non-consensual sexualized deepfakes of real people under new proposals expected to be approved by EU ambassadors.
The measure would make it illegal to market AI tools in Europe that can create sexually explicit images, videos, or audio involving identifiable individuals without their consent. Lawmakers accelerated the push after users of the Grok AI system on X generated millions of sexualized images of real people, including children, before the platform implemented restrictions.
The proposed ban would amend the EU’s existing AI regulatory framework and could take effect as early as this summer if negotiations between EU countries and the European Parliament conclude successfully. The proposal would target so-called “AI nudification” tools that generate explicit content from real photographs, though companies that implement effective safeguards to prevent such misuse could potentially avoid the prohibition.
EU officials are also examining whether X adequately mitigated the risks associated with integrating Grok into its platform, rm as concerns grow about the harm caused by non-consensual deepfake content. (Pieter Haeck / Politico EU)
Related: The Record, Brussels Times, The Next Web, Belga News Agency, Firstpost
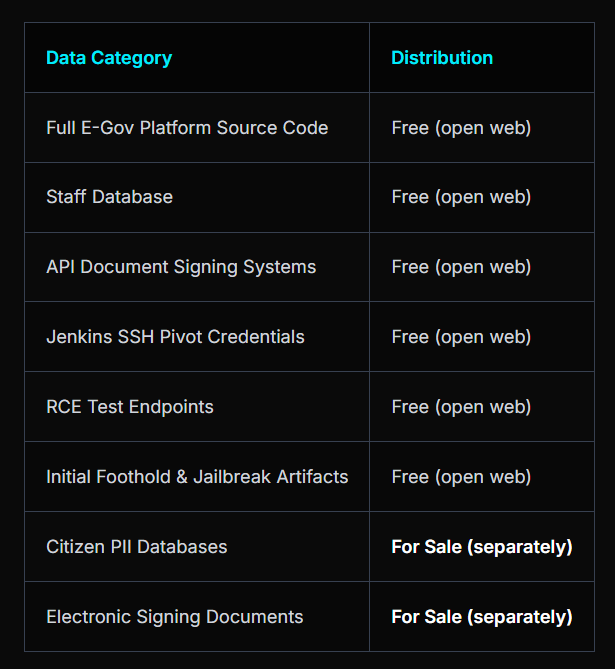
Swedish authorities are investigating a suspected breach involving the country’s e-government platform after hackers claimed to have stolen internal files linked to the system.
The hacking group ByteToBreach posted on the dark web that it had obtained data from the Swedish subsidiary of IT consulting firm CGI Group, including portions of the platform’s source code, staff databases, configuration files, and documents described as citizen databases and electronic-signing materials.
Officials said they are reviewing the incident and assessing the potential impact. Sweden’s national cyber incident center, CERT-SE, is analyzing the leaked material while other agencies evaluate whether sensitive government systems or personal data were exposed.
The platform is widely used across Swedish public services, including by the country’s tax authorities, though BankID — Sweden’s electronic identification system used for online authentication — said its services were not affected.
CGI said the breach involved two internal test servers and an older version of the application source code rather than active systems. However, security analysts warned that even outdated code could reveal vulnerabilities that attackers might exploit in future attacks on Sweden’s digital infrastructure.
The group ByteToBreach has also claimed responsibility for a recent breach involving the Finnish ferry operator Viking Line, where passenger and payment data were allegedly exposed online. (The European Conservative)
Related: SVT.se, Irish Sun, r/programming, Dagens Nyheter, Threat Landscape
Small and midsize businesses are overlooking printer security as a cybersecurity risk, even as connected devices become increasingly integrated into office networks, according to a new global study by HP.
The survey of 800 IT decision-makers and 2,400 knowledge workers found that 57 percent of SMBs consider print security a low priority in their cybersecurity strategies, despite concerns that document processes could expose sensitive data or create privacy risks.
The report found that many organizations lack basic visibility and controls over printing activity, with half of SMBs unable to track who prints documents or where they are printed. At the same time, employees often underestimate the risks: two-thirds assume office printers are secure, re and half do not view them as a potential threat.
While most companies acknowledge that printer security needs improvement, experts warn that uncollected print jobs, misdirected scans, and unauthorized access to print queues could expose sensitive information such as payroll data, customer records, or contract details. (Ian Barker / BetaNews)
Related: HP, SC Media, Computer Weekly
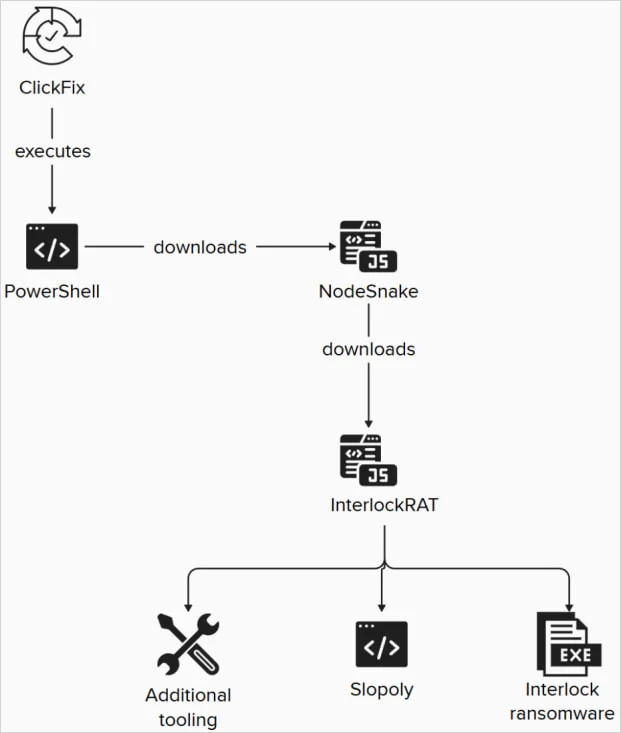
IBM X-Force researchers have identified a new malware strain dubbed Slopoly that was used in an Interlock ransomware attack and likely created with the help of generative AI tools.
The malware functioned as a PowerShell-based backdoor that allowed attackers to maintain access to a compromised server for more than a week while stealing data. Investigators attributed the attack to a financially motivated threat group tracked as Hive0163, which focuses on extortion through large-scale data exfiltration and ransomware deployment.
Researchers found several indicators suggesting AI-assisted development, including extensive code comments, structured logging, detailed error handling, ng, and clearly named variables—features that are uncommon in most human-written malware.
Despite this, Slopoly itself is relatively simple and does not actually exhibit the polymorphic capabilities described in its own code comments. Instead, researchers believe the malware was likely generated using a builder that inserts randomized configuration values such as command-and-control servers, beacon intervals, and function names.
In the attack observed by IBM, the intrusion began with a ClickFix social engineering technique and later involved multiple malware components, including the NodeSnake and InterlockRAT backdoors, before Slopoly was deployed. The operation ultimately delivered the Interlock ransomware payload, which encrypts files and appends distinctive extensions after terminating processes that might lock files.
The Interlock group, which emerged in 2024, has previously claimed attacks against several organizations, including the Texas Tech University System, DaVita, Kettering Health, and the city of Saint Paul, Minnesota. (Bill Toulas / Bleeping Computer)
Related: IBM, SC Media, Security Week, The Cyber Express, Security Affairs, The Cyber Press
Meta announced new measures to combat impersonation and low-quality AI-generated posts on Facebook following growing complaints that the platform has been overwhelmed by spam and “AI slop.”
The company said it is introducing improved tools to help creators detect when their content is reposted by impersonators and making it easier to report violations through a centralized dashboard. Meta said it removed about 20 million impersonation accounts last year and saw reports targeting large creators drop by roughly one-third.
The company is also updating Facebook’s creator guidelines to more clearly define what counts as original content. Posts filmed or produced directly by creators — including reels that remix material with added commentary, analysis, or new information — will be prioritized, while duplicated or minimally altered content such as simple re-uploads or videos with only added captions or borders will be deprioritized.
Meta said earlier efforts to curb spam and promote original work helped double both views of and time spent watching original content on Facebook during the second half of 2025 compared with the same period a year earlier. (Sarah Perez / TechCrunch)
Related: Meta Newsroom, Neowin
Hacked data from the Department of Homeland Security’s technology incubator shows it is funding a variety of companies that would expand its surveillance capabilities with artificial intelligence.
The projects at the Office of Industry Partnership (OIP) include automated surveillance in airports; adapters allowing agents to use phones for biometric scanning; and an AI platform that ingests all 911 call data nationally and builds “geospatial heat maps” to “predict incident trends”, which appears to be a form of predictive policing.
The data throws new light on the department’s surveillance ambitions in the wake of the agency’s unprecedented $165bn funding boost in last year’s tax and spending bill, and controversies over agents’ apparent gathering of visual and biometric data on protesters in Minneapolis. (Jason Wilson / The Guardian)
Related: The420
Romania’s Ministry of Foreign Affairs said two of its online platforms were hit by distributed denial-of-service (DDoS) attacks on March 13 and early March 14, temporarily disrupting access to digital services.
The attacks targeted the eviza.mae.ro and econsulat.ro websites, causing slow performance and short periods when the sites became unavailable before mitigation measures restored normal operations.
Officials said the ministry’s security systems and technical staff acted quickly to reduce the impact of the attacks and confirmed that all digital systems are now functioning normally.
The ministry emphasized that DDoS attacks overload websites with traffic but do not involve unauthorized access to data, adding that no sensitive information was compromised even though the disruption temporarily prevented citizens from using the affected online services. (Digi24)
Related: NineoClock, Agerpress, Informat, Odessa Journal
Meta plans to discontinue end-to-end encryption for Instagram direct messages, with the opt-in feature scheduled to be removed on May 8, 2026.
The company said the decision was driven by low adoption, noting that only a small number of users enabled encrypted messaging in Instagram chats. Unlike WhatsApp, where encryption is enabled by default, Instagram’s encrypted DMs were available only in some regions and had to be activated manually for individual conversations.
Meta said users who want end-to-end encrypted messaging can continue using WhatsApp, where the feature has been standard since 2016. (Karissa Bell / Engadget)
Related: Mashable, Cyber Press, Igor's Lab, The Verge, 9to5Google
Samsung’s Galaxy S26 Ultra introduces a built-in “Privacy Display” designed to prevent people nearby from easily viewing what’s on a user’s screen.
The hardware feature mimics the effect of a privacy screen protector but is integrated directly into the display, allowing the phone to dim and obscure content when viewed from the side while maintaining normal brightness and clarity when viewed head-on. Users can also configure the feature to activate automatically when certain apps—such as messaging or banking apps—are opened.
A stronger “Max Privacy Protection” mode can be manually enabled to make the screen nearly unreadable from side angles, offering additional protection in public settings like transit or cafés.
Unlike physical privacy screen protectors, the system can be turned on or off through software, allowing users to maintain privacy when needed without permanently reducing display quality or limiting shared viewing when showing content to others. (Julian Chokkattu / Wired)
Related: Samsung, Android Police, Tom's Guide, TechRadar, The Guardian

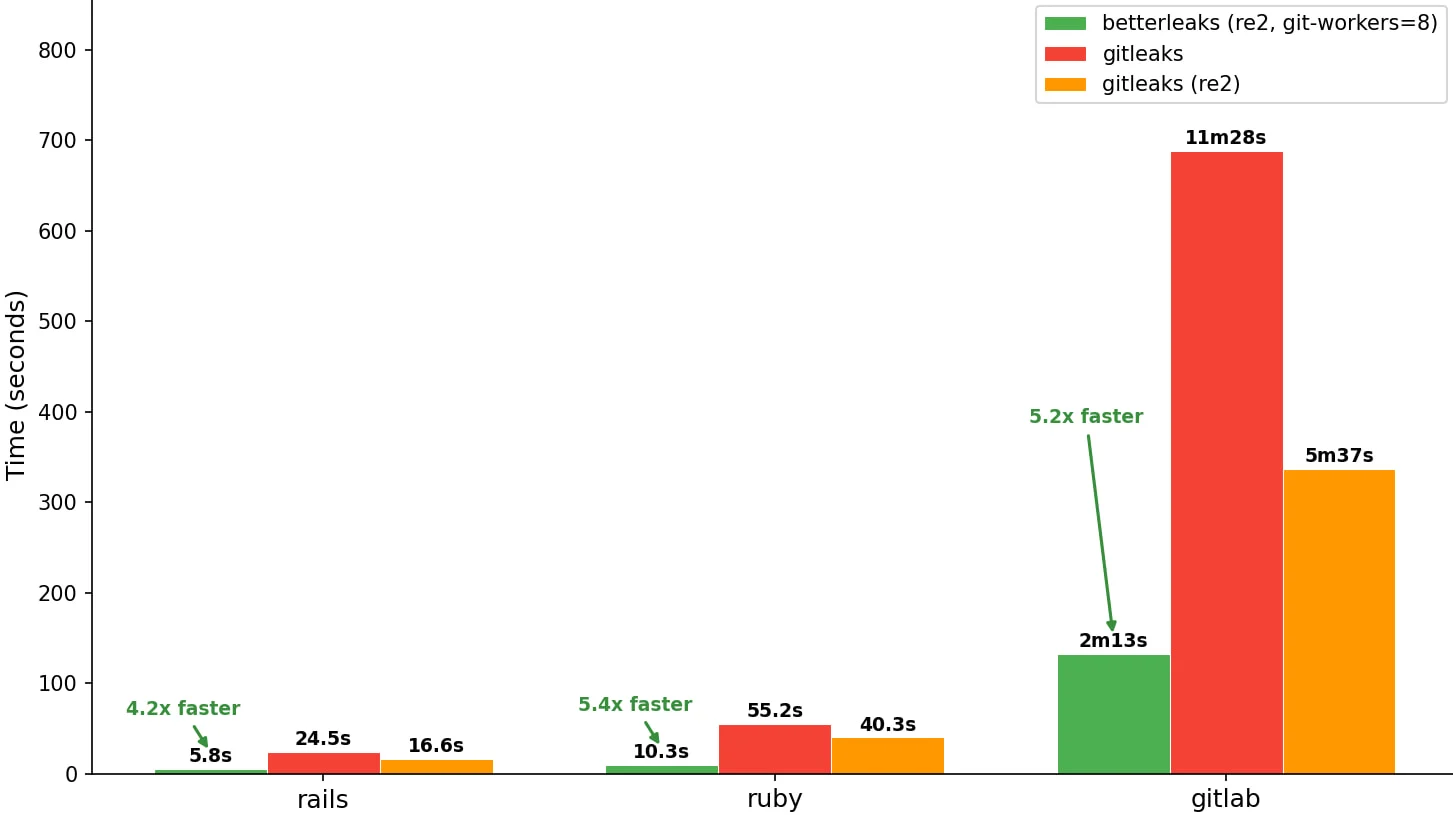
A new open-source security tool called Betterleaks has been released to help developers detect exposed credentials and other sensitive information in directories, files, and Git repositories.
The tool scans codebases for secrets such as API keys, tokens, and private keys that may have been accidentally committed to source code, allowing organizations to identify and remove them before attackers discover them. Betterleaks was created as a successor to the widely used Gitleaks tool and is maintained by the same developer with support from security firm Aikido.
Betterleaks introduces several technical improvements, including rule-based validation using Common Expression Language, faster scanning through parallelized repository analysis, and a new token efficiency scanning method that improves detection accuracy compared with traditional entropy-based techniques.
Developed primarily in the Go programming language, the tool also supports expanded detection rules and automated handling of encoded secrets, with future versions planned to include features such as LLM-assisted analysis, additional data source scanning, and automated secret revocation through provider APIs. (Bill Toulas / Bleeping Computer)
Related: Betterleaks, Aikido Security
Cybersecurity startup Scanner announced it had raised $22 million in a Series A funding round.
Sequoia Capital led the round with additional support from CRV, Mantis VC, and angel investors. (Ionut Arghire / Security Week)
Related: scanner.dev, Sequoia Capital, FinTech Global, Ventureburn
Best Thing of the Day: The Pitt Gets Better and Better
HBO’s popular medical drama “The Pitt” is raising the profile of the deadly consequences of ransomware attacks on healthcare facilities.
Worst Thing of the Day: As If There Weren't Enough Iran War Misinformation Out There
A torrent of fake videos and images generated by artificial intelligence has overrun social networks during the first weeks of the war in Iran.
Bonus Worst Thing of the Day: The World Will Curse the Day These Things Were Created
A man has been accused in the UK of wearing smart glasses to receive "coaching" while giving evidence.
Closing Thought