Feds summon Wall Street CEOs over fears Anthropic AI could supercharge cyberattacks
The FBI has accessed incoming Signal messages from a defendant’s iPhone after Signal app removal, Viktor Orbán secretly uses Webloc spyware in violation of GDPR, US Treasury launches cyber threat intel program for digital asset firms, Storm-2755 is stealing Canadians' paychecks, much more

Don't miss my latest CSO piece, which breaks down which US federal agencies are cyber winners and losers under Donald Trump's fiscal 2027 budget.
Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.

Treasury Secretary Scott Bessent and Federal Reserve Chair Jerome Powell summoned Wall Street leaders to an urgent meeting on concerns that the latest artificial intelligence model from Anthropic PBC will usher in an era of greater cyber risk.
Bessent and Powell assembled the group at Treasury’s headquarters in Washington on Tuesday to make sure banks are aware of possible future risks raised by Anthropic’s Mythos and potential similar models, and are taking precautions to defend their systems, according to people familiar with the matter who asked not to be identified, citing the private discussions.
The previously unreported meeting, arranged on short notice, is another sign that regulators consider the possibility of a new breed of cyber attacks as one of the biggest risks facing the financial industry. All the banks summoned to the meeting are classified as systemically important by top regulators, meaning their stability is a priority for the global financial system.
Anthropic’s Mythos is a more powerful system that the AI firm has said is capable of identifying and then exploiting vulnerabilities in every major operating system and web browser when directed by a user to do so.
Regulators’ caution about the power of the model in hackers’ hands echoes Anthropic’s own prudence. Anthropic has limited the release of it to just a few major technology and finance firms at first. Those companies, which include Amazon.com Inc. and Apple Inc. as well as JPMorgan Chase & Co., are part of “Project Glasswing,” which will work to secure the most important systems before other similar AI models become available.
Chief executive officers summoned to the meeting with the Fed and Treasury include Citigroup Inc.’s Jane Fraser, Morgan Stanley’s Ted Pick, Bank of America’s Brian Moynihan, Wells Fargo’s Charlie Scharf, and Goldman Sachs Group’s David Solomon, said the people. JPMorgan’s Jamie Dimon was unable to attend, the people said. (Todd Gillespie, Katanga Johnson, Hannah Levitt, and Sridhar Natarajan / Bloomberg)
Related: RTÉ, Capital Brief, The Information, Financial Times, Blockonomi, CoinDesk, r/politics, The Guardian, Financial Review
According to 404 Media, testimony in a recent trial involving “a group of people setting off fireworks and vandalizing property at the ICE Prairieland Detention Facility in Alvarado, Texas,” showed that the FBI was able to recover content of incoming Signal messages from a defendant’s iPhone, even though Signal had been removed from the device.
As 404 Media notes, Signal’s settings include an option that prevents the actual message content from being previewed in notifications. However, it appears the defendant did not have that setting enabled, which, in turn, seemingly allowed the system to store the content in the database.
404 Media reached out to Signal and Apple, but neither company provided any statements on how notifications are handled or stored. (Marcus Mendes / 9to5Mac)
Related: 9to5Mac, r/apple, Tech Times, The Mac Observer, Digital Trends, NewsBytes, CyberInsider, 404 Media
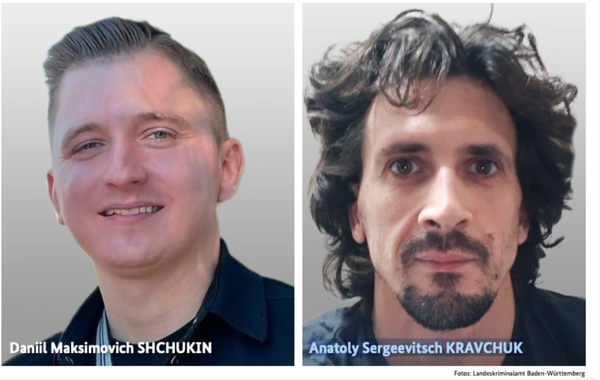
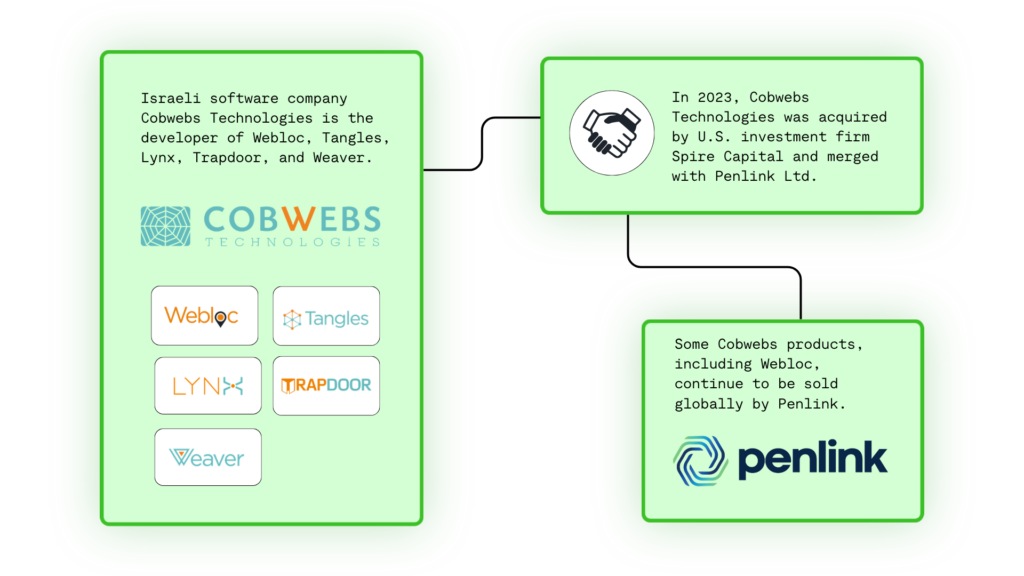
Intelligence agencies of Viktor Orbán’s government have been secretly using Webloc — a mass surveillance tool that tracks hundreds of millions of people via smartphone advertising data — making Hungary the first confirmed EU country to deploy it, in likely violation of GDPR.
Hungarian intelligence and law enforcement agencies have been operating AI-powered, open-source intelligence tools developed by Israel’s Cobwebs Technologies for at least five years, an investigation by VSquare, in collaboration with Citizen Lab, reveals.
Foreign technologies are used alongside tools allegedly developed in Hungary. Such tools include an OSINT software and a mysterious spyware tied to SCI-Network Ltd., the same Hungarian firm that purchased Cobwebs’ licenses for the Orbán government.
The most powerful previously unknown Cobwebs product used by Hungarian authorities is called Weblock, also known as WebLoc or Webloc.
According to Citizen Lab, “Webloc is a global geolocation surveillance system that monitors hundreds of millions of people based on data purchased from consumer apps and digital advertising.” In short, Webloc uses smartphone apps’ advertising data for mass surveillance without the knowledge or consent of users.
Hungary is the first confirmed country to deploy Webloc within the European Union, where data protection and privacy rules under the General Data Protection Regulation (GDPR) effectively prohibit such use of personal and advertising data.
Documents on Cobwebs licenses reviewed by VSquare, as well as multiple sources with ties to Hungary’s intelligence community, confirm that Hungarian authorities have been using tools from Cobwebs Technologies, including Webloc, since at least early 2022. (Szabolcs Panyi / VSquare)
Related: Citizen Lab, United24
The US Treasury’s Office of Cybersecurity and Critical Infrastructure Protection (OCCIP) launched a program to share real-time cyber threat intelligence with eligible digital asset firms at no cost.
The initiative gives qualifying crypto companies access to the same security briefings that traditional banks and financial institutions have received for years.
Treasury officials cited the growing frequency and sophistication of attacks as the primary driver behind the program.
The effort also advances a recommendation from the President’s Working Group on Digital Asset Markets.
Tyler Williams, Counselor to the Secretary for Digital Assets, linked the program to the Guiding and Establishing National Innovation for US Stablecoins (GENIUS) Act, signed into law in July 2025.
The FDIC approved a separate GENIUS Act implementation framework on April 7, covering cybersecurity standards for stablecoin issuers. (Lockridge Okoth / BeInCrypto)
Related: Treasury Department, Crypto Times, BitGet, CryptoRank, The Cyber Express, crypto.news, Finextra, CryptoRank, BeInCrypto, The Street, The Record, Cryptopolitan, PYMNTS
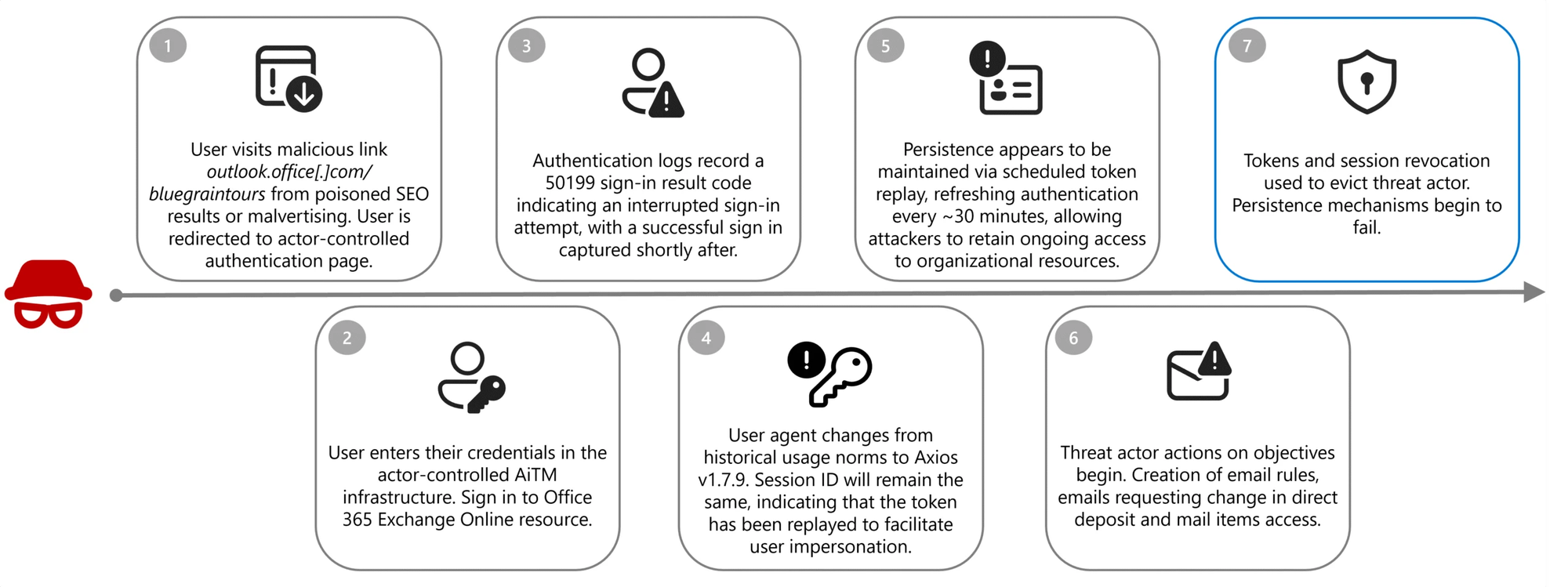
Researchers at Microsoft report that a financially motivated threat actor tracked as Storm-2755 is stealing Canadian employees' salary payments after hijacking their accounts in payroll pirate attacks.
The attackers used malicious Microsoft 365 sign-in pages to steal victims' authentication tokens and session cookies by redirecting them to domains (e.g., bluegraintours[.]com) hosting malicious web pages (pushed to the top of search engine results through malvertising or SEO poisoning) that masqueraded as Microsoft 365 sign-in forms.
This masquerade allowed Storm-2755 to bypass multifactor authentication (MFA) in adversary‑in‑the‑middle (AiTM) attacks by replaying stolen session tokens rather than re-authenticating.
To harden defenses against AiTM and payroll pirate attacks, Microsoft advises defenders to block legacy authentication protocols and implement phishing-resistant MFA. (Sergiu Gatlan / Bleeping Computer)
Related: Microsoft, Help Net Security
Blockchain investigator ZachXBT uncovered what he claims is a North Korean-linked IT worker network generating roughly $1 million per month through crypto-linked payments and fraudulent employment schemes.
In a detailed thread on X, the onchain sleuth said the findings stem from data exfiltrated from an internal payment server tied to 390 accounts.
The data cache also includes chat logs, wallet activity, and identity records that had not previously been made public, the crypto detective said.
According to ZachXBT’s analysis, what appears to be a structured operation that relies on forged personas, fake documents, and a well-coordinated payment flow has pulled in north of $3.5 million since last November.
An internal remittance platform resembling a messaging service is at the center of the system, he said. Workers use the tool to report earnings and receive payment instructions from a central administrator account.
Then, funds were usually routed through cryptocurrency transactions before being converted to fiat using Chinese bank accounts or platforms like Payoneer.
ZachXBT linked several payment addresses to known clusters associated with North Korean IT worker activity. Tether froze one Tron address connected to the network in December, he said. (Naga Avan-Nomayo / The Block)
Related: CoinCentral, Blockonomi, Incrypted, CoinGape, Futubull, ForkLog, Bitcoin.com, CryptoRank, CryptoPotato, Bitget
Hong Kong police arrested a man suspected of stealing the personal data of more than 56,000 patients from a Hospital Authority (HA) computer system.
They identified the 30-year-old suspect as an employee of a systems maintenance contractor hired by the HA. He is accused of downloading patient data without authorization.
Officers from the Cyber Security and Technology Crime Bureau said the leak originated from two of the contractor’s offices in the New Territories.
Police raided the offices, seizing more than 60 digital devices, including servers and mobile phones. The suspect was arrested Tuesday in Tin Shui Wai on suspicion of “access to a computer with criminal or dishonest intent.”
Superintendent Ferris Cheung said investigators are still probing the suspect’s motive and possible accomplices. (Hans Tse/ Hong Kong Free Press)
Related: Healthcare IT News, South China Morning Post
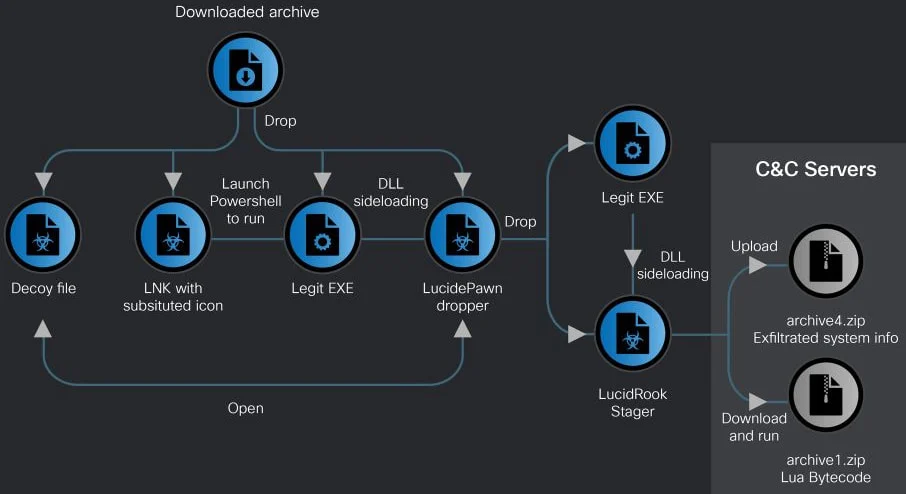
Researchers at Cisco Talos report that a new Lua-based malware, called LucidRook, is being used in spear-phishing campaigns targeting non-governmental organizations and universities in Taiwan.
They attribute the malware to a threat group tracked internally as UAT-10362, who they describe as a capable adversary "with mature operational tradecraft."
LucidRook was observed in attacks in October 2025 that relied on phishing emails carrying password-protected archives.
The researchers identified two infection chains, one using an LNK shortcut file that ultimately delivered a malware dropper called LucidPawn, and an EXE-based chain that leveraged a fake antivirus executable impersonating Trend Micro Worry-Free Business Security Services.
The LNK-based attack employs decoy documents, such as government letters crafted to appear as if they originate from the Taiwanese government, to divert the user's attention. (Bill Toulas / Bleeping Computer)
Related: Cisco Talos, CyberPress, CyberSecurityNews
Hackers hijacked the update system for the Smart Slider 3 Pro plugin for WordPress and Joomla, and pushed a malicious version with multiple backdoors.
The developer says that only the Pro version 3.5.1.35 of the plugin is affected and recommends switching immediately to the latest version, currently 3.5.1.36, or 3.5.1.34 and earlier.
Apart from installing backdoors in multiple locations, the malicious update created a hidden user with administrator permissions and stole sensitive data.
According to the vendor, the threat actor distributed the malicious update on April 7, and some websites may have installed it.
An analysis from PatchStack, a company focusing on securing WordPress and open-source software, notes that the malware is a fully featured, multi-layered toolkit embedded in the plugin’s main file while preserving Smart Slider's normal functionality. (Bill Toulas / Bleeping Computer)
Related: PatchStack, TechRadar
Security researcher Haifei Li (the founder of the sandbox-based exploit-detection platform EXPMON) says that attackers have been exploiting a zero-day vulnerability in Adobe Reader using maliciously crafted PDF documents since at least December.
Li warned that the attackers are using what he described as a "highly sophisticated, fingerprinting-style PDF exploit" to target an undisclosed Adobe Reader security flaw.
Li also said that these attacks have been targeting Adobe users for at least 4 months, stealing data from compromised systems using privileged util.readFileIntoStream and RSS.addFeed Acrobat APIs, and deploying additional exploits.
Threat intelligence analyst Gi7w0rm, who also analyzed this Adobe Reader exploit, found that PDF documents pushed in these attacks contain Russian-language lures referencing ongoing events in the Russian oil and gas industry.
Li has notified Adobe about these findings and, until the company releases security updates to address this actively exploited vulnerability, advised Adobe Reader users not to open PDF documents received from untrusted contacts until a patch is released. (Sergiu Gatlan / Bleeping Computer)
Related: Haifei Li, eSecurity Planet, Sophos, The Register, The Stack, Security Week, Haifei's random thoughts, DeviceSecurity.io, Hackread, Help Net Security, Forbes, Cyber Security News, r/cybersecurity, CSO Online
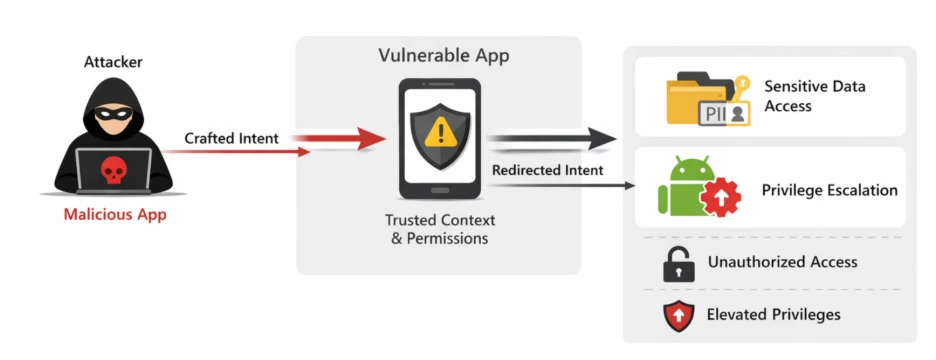
Microsoft researchers discovered a vulnerability in EngageLab’s EngageSDK, which is designed for managing messaging and push notifications in mobile applications, that could expose highly sensitive information.
According to Microsoft, the SDK, which is integrated by developers into Android apps as a dependency, is used by crypto wallet apps that have a total of more than 30 million installations.
Unpatched versions of EngageSDK are affected by a vulnerability related to Android intents, which enable interaction between different applications and data sharing between the components of the same application.
Microsoft researchers identified an intent redirection flaw that enables an attacker to manipulate the contents of an intent sent by vulnerable applications.
An attacker can use a malicious app running on the targeted device to send specially crafted intents that leverage the vulnerable app to bypass the Android security sandbox and gain access to sensitive data, including personal information, user credentials, and financial information.
Microsoft notified EngageLab developers in April 2025. The Android Security Team was also informed the next month due to the vulnerability affecting apps distributed through Google Play. (Eduard Kovacs / Security Week)
Related: Microsoft, Security Affairs
Users attempting to download HWMonitor and CPU-Z from the official CPUID website are reportedly being served malware-laced installers, in what appears to be an active compromise of the vendor’s distribution infrastructure.
CPUID, the developer behind HWMonitor and CPU-Z, is a French software company known for producing lightweight system profiling and monitoring tools widely used by enthusiasts, IT professionals, and OEMs. CPU-Z alone has tens of millions of users globally.
The issue first surfaced through user reports on Reddit, where a user attempting to update HWMonitor to version 1.63 was redirected from the official CPUID website to a suspicious download hosting a file named HWiNFO_Monitor_Setup.exe. The anomaly was immediately notable, as HWiNFO is an entirely separate hardware monitoring tool developed by a different vendor. Upon execution, the installer reportedly launched a Russian-language setup interface, prompting the user to abort the installation.
Further investigation by community members revealed that the download link embedded on CPUID’s official HWMonitor page redirected to an external domain hosted on Cloudflare R2 storage, rather than CPUID’s standard infrastructure. This domain served a trojanized installer wrapped in a modified Inno Setup package, a technique frequently used to obfuscate malicious payloads and hinder static analysis.
In contrast, legitimate HWMonitor installers use standard, easily extractable Inno Setup configurations.
It remains unclear how the attackers gained access to CPUID’s infrastructure or whether the breach has been fully contained. The software publisher has not issued an official statement about the incident yet, and the website is currently offline. (Amar Ćemanović / Cyber Insider)
Related: Hybrid Analysis, r/pcmasterrace, igor'slab, PC Guide, dev.ua, PC Gamer, VideoCardz
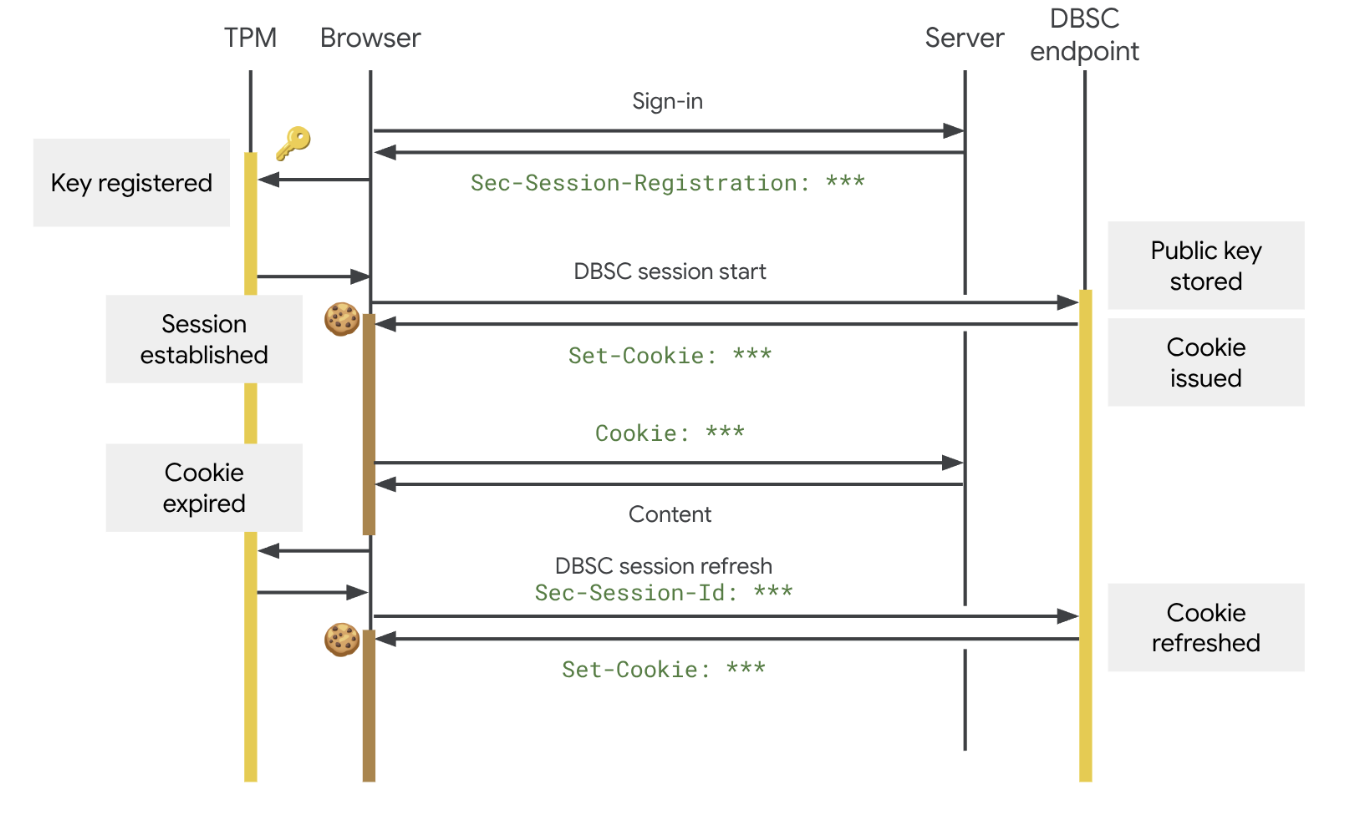
Google has announced the rollout of new session cookie protections in Chrome to prevent account compromise via stolen authentication cookies.
The feature, called Device Bound Session Credentials (DBSC), was announced in April 2024 and has become available in Chrome 146 for Windows. macOS users will receive it as well, in a future browser release.
DBSC fights session cookie theft by cryptographically binding authentication sessions to the user’s device, thus rendering stolen cookies useless.
Typically stolen using information-stealing malware and often shared or sold on cybercrime platforms, these tokens may provide attackers with access to users’ accounts without a password. (Ionut Arghire / Security Week)
Related: Google Security Blog, Android Headlines, Bleeping Computer, gHacks, Help Net Security
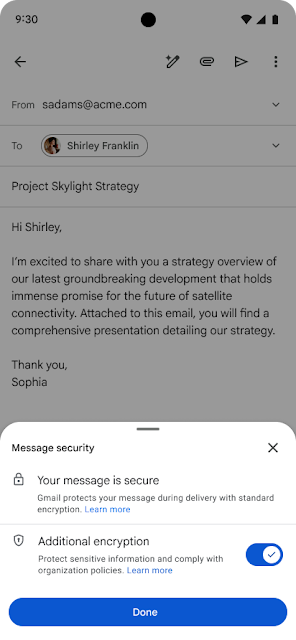
Google says Gmail end-to-end encryption (E2EE) is now available on all Android and iOS devices, allowing enterprise users to read and compose emails without additional tools.
Starting this week, encrypted messages will be delivered as regular emails to Gmail recipients' inboxes if they use the Gmail app.
Recipients who don't have the Gmail mobile app and use other email services can read them in a web browser, regardless of the device and service they're using.
"For the first time, users can compose and read these E2EE messages natively within the Gmail app on Android and iOS. No need to download extra apps or use mail portals. Users with a Gmail E2EE license can send an encrypted message to any recipient, regardless of what email address the recipient has," Google said. (Sergiu Gatlan / Bleeping Computer)
Related: Google Workspace Updates, How-to-Geek, Help Net Security, gHacks
Stephen Kamnik, a corporal in the Pennsylvania state police, pleaded guilty to a mind-boggling set of crimes that include going through his co-workers’ underwear, possessing a stolen gun, having child sexual abuse material on his hard drives, and using AI tools to create over 3,000 pornographic “deepfakes.”
One of the deepfakes involved a district court judge, while many of the others were created based on photos downloaded illicitly from state databases, including driver’s license photos.
Some of the imagery was even created at police barracks, using state-owned devices. (Nate Anderson / Ars Technica)
Related: Pennsylvania Attorney General, KYW News Radio, Hoodline, Philadelphia Inquirer
OpenAI is throwing its support behind an Illinois state bill that would shield AI labs from liability in cases where AI models are used to cause serious societal harms, such as death or serious injury of 100 or more people or at least $1 billion in property damage.
The effort seems to mark a shift in OpenAI’s legislative strategy. Until now, OpenAI has largely played defense, opposing bills that could have made AI labs liable for their technology’s harms. Several AI policy experts say that SB 3444—which could set a new standard for the industry—is a more extreme measure than bills OpenAI has supported in the past. (Maxwell Zeff / Wired)
Related: r/technology, Transparency Coalition
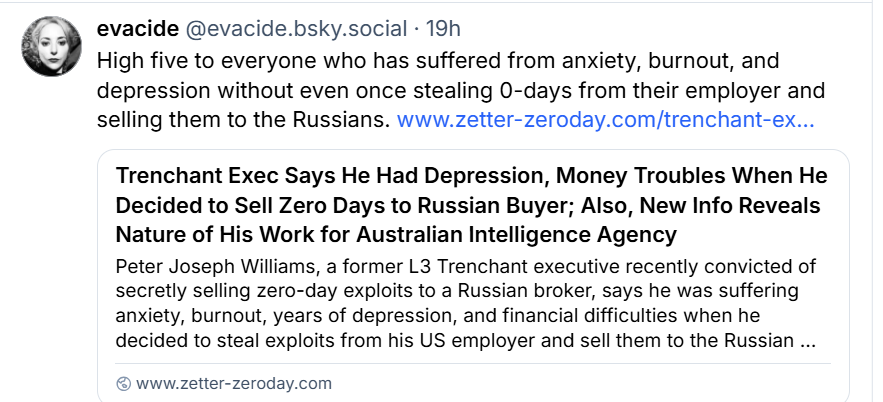
Peter Joseph Williams, a former L3 Trenchant executive convicted of secretly selling zero-day exploits to a Russian broker, says he was suffering anxiety, burnout, years of depression, and financial difficulties when he decided to steal exploits from his US employer and sell them to the Russian buyer.
Williams, who was promoted to general manager of Trenchant during the three years he was stealing from his company, explained the circumstances around his fateful decision in a letter submitted to the DC District Court before his recent sentencing. His attorney also described his crime spree as "an unfortunate period of extraordinarily poor judgment exacerbated by severe job stress and exhaustion."
An Australian national who has lived in the US since July 2023 while working out of Trenchant's DC offices on a visa, Williams wrote that at the time he committed the offenses, he was "experiencing significant professional pressure and personal anxiety." But instead of seeking help or "removing" himself from circumstances he said he was not handling well, he signed contracts worth $4 million to sell eight of his company's hacking tools to a Russian company called Operation Zero – a firm known to sell exploits to the Russian government and other non-NATO countries.
Williams, who is 39 years old and the father of two young children, acknowledged that his depression and burnout were not the causes of his crimes, but offered the court details about his mental state as an explanation for why his judgment was impaired at the time and why his actions deviated so far from a lifetime spent in service to the Australian government and military.
Williams' wife and older brother wrote similar letters to the court about the strain he was under between 2022 and 2025 when he committed his crimes – Williams was the sole breadwinner for his family and handled all financial and administrative aspects of their lives, in addition to his stressful job, his wife wrote; and his criminal actions were completely out of character for someone who had devoted his life to protecting his country and its ideals. (Kim Zetter / Zero Day)
Best Thing of the Day: Everyone Should Emulate EFF
Digital civil liberties organization EFF has decided to leave the rotting hole of disinformation, racism, anti-semitism, and right-wing propaganda known as X.
Bonus Best Thing of the Day: This Took Forever, But All's Well That Ends Well
US agriculture equipment maker Deere agreed to pay $99 million into a settlement fund for farms and farmers that are part of a class action over costs and their right to repair their own highly digitized equipment.
Worst Thing of the Day: Of Course Musk Would Oppose This Law
Elon Musk’s artificial intelligence company, xAI, has filed a lawsuit against the state of Colorado for its law that protects citizens against “algorithmic discrimination” in sectors such as education, employment, healthcare, housing, and financial services.