Germany names alleged ‘UNKN’ kingpin behind GandCrab and REvil ransomware empire
Meta pauses work with Mercor indefinitely following breach, N. Ireland education IT system contractor hit by breach, First convicted spyware maker dodges jail time, N. Korea carried out six-month op to steal $270m from Drift, Y Combinator dumps Delve over compliance fabrications, much more
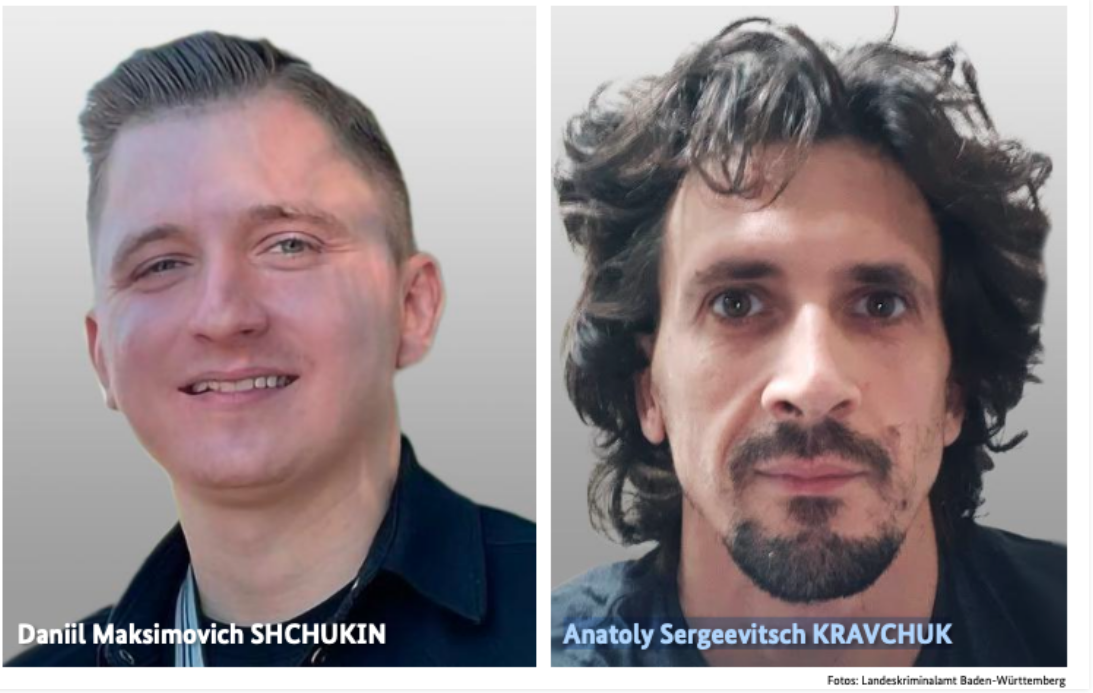
Authorities in Germany say 31-year-old Russian Daniil Maksimovich Shchukin went by the handle “UNKN” and ran the early Russian ransomware groups GandCrab and REvi and helped carry out at least 130 acts of computer sabotage and extortion against victims across the country between 2019 and 2021.
Shchukin was named as UNKN (a.k.a. UNKNOWN) in an advisory published by the German Federal Criminal Police or BKA. The BKA said Shchukin and another Russian — 43-year-old Anatoly Sergeevitsch Kravchuk — extorted nearly 2 million euros across two dozen cyberattacks that caused more than 35 million euros in total economic damage.
Germany’s BKA said Shchukin acted as the head of one of the largest worldwide operating ransomware groups, GandCrab and REvil, which pioneered the practice of double extortion — charging victims once for a key needed to unlock hacked systems, and a separate payment in exchange for a promise not to publish stolen data.
Germany’s BKA said Shchukin acted as the head of one of the largest worldwide operating ransomware groups, GandCrab and REvil, which pioneered the practice of double extortion — charging victims once for a key needed to unlock hacked systems, and a separate payment in exchange for a promise not to publish stolen data. (Brian Krebs / Krebs on Security)
Meta has paused all its work with the data contracting firm Mercor while it investigates a major security breach that impacted the startup, two sources confirmed.
The pause is indefinite, the sources said. Other major AI labs are also reevaluating their work with Mercor as they assess the scope of the incident, according to people familiar with the matter.
Mercor is one of a few firms that OpenAI, Anthropic, and other AI labs rely on to generate training data for their models. The company hires massive networks of human contractors to generate bespoke, proprietary datasets for these labs, which are typically kept highly secret as they’re a core ingredient in the recipe to generate valuable AI models that power products like ChatGPT and Claude Code. (Maxwell Zeff, Zoë Schiffer, and Lily Hay Newman / Wired)
Related: The Economic Times, The Verge, Business Insider. Moneycontrol, Livemint
The Education Authority in Northern Ireland has said it is making "good progress" to restore access to a school IT system following a cyber attack last Thursday.
The C2K school system, provided by Capita, is used as a curriculum support, and the Education Authority had apologized to those preparing for exams over the Easter break.
In a statement yesterday, the Authority said: "We are continuing to make good progress to restore access to the C2K system following the recent cyber attack.
"Our teams have been working hard through the weekend to restore access to the system safely and securely, starting with post primary schools."
It added: "This work will continue over the coming days, as we move to stand the system back up in all schools as soon as possible. (RTE)
Related: BBC News, The Independent, Belfast Telegraph, Derry Journal, The Impartial Reporter, The Irish News
Bryan Fleming, the first convicted spyware maker in over a decade, has avoided jail time after earlier pleading guilty to US federal charges associated with running his surveillance company.
He was sentenced in a San Diego federal court to time served and a $5,000 fine, confirmed a spokesperson for the US Attorney for the Southern District of California, whose office brought the charges against Fleming.
During a plea hearing in January following a years-long federal investigation into his spyware company, pcTattletale, Fleming admitted to making, selling, and advertising spyware for unlawful uses.
Prosecutors had previously asked the judge for Fleming to receive no custodial sentence or fine. (Zack Whittaker / TechCrunch)
A six-month intelligence operation preceded the $270 million exploit of Drift Protocol and was carried out by a North Korean state-affiliated group, according to a detailed incident update published by the team on X.
The attackers first made contact around fall 2025 at a major crypto conference, presenting themselves as a quantitative trading firm looking to integrate with Drift.
They were technically fluent, had verifiable professional backgrounds, and understood how the protocol operated, Drift said. A Telegram group was established, and what followed were months of substantive conversations around trading strategies and vault integrations, interactions that are standard for how trading firms onboard with DeFi protocols.
Between December 2025 and January 2026, the group onboarded an Ecosystem Vault on Drift, held multiple working sessions with contributors, deposited over $1 million of their own capital, and built a functioning operational presence inside the ecosystem.
Drift contributors met individuals from the group face-to-face at multiple major industry conferences across several countries through February and March. By the time the attack was launched on April 1, the relationship was nearly half a year old.
The compromise appears to have come through two vectors.
A second person downloaded a TestFlight application, Apple's platform for distributing pre-release apps that bypasses App Store security review, which the group presented as their wallet product.
For the repository vector, Drift pointed to a known vulnerability in VSCode and Cursor, two of the most widely used code editors in software development, that the security community had been flagging since late 2025, where simply opening a file or folder in the editor was sufficient to silently execute arbitrary code with no prompt or warning of any kind.
Once devices were compromised, the attackers had what they needed to obtain the two multisig approvals that enabled the durable nonce attack CoinDesk detailed earlier this week. Those pre-signed transactions sat dormant for more than a week before being executed on April 1, draining $270 million from the protocol's vaults in under a minute.
The attribution points to UNC4736, a North Korean state-affiliated group also tracked as AppleJeus or Citrine Sleet, based on both on-chain fund flows tracing back to the Radiant Capital attackers and operational overlap with known DPRK-linked personas. (Shaurya Malwa / CoinDesk)
Related: Cointelegraph. Cointelegraph, The Block, Blockonomi, Yahoo Finance, Hacker News (ycombinator), crypto.news, Decrypt, CoinGape
Compliance startup Delve has parted ways with its backer Y Combinator (YC), according to COO Selin Kocalar, with the accelerator also removing the company’s profile from its startup directory.
The development follows allegations that compliance certifications for hundreds of Delve’s clients were fabricated.
In addition, an alleged screenshot of a message from Y Combinator CEO Garry Tan on Bookface (a platform used by YC founders to connect) is also circulating, suggesting the firm was asked to leave, even as Kocalar’s post struck a more positive tone about the split.
CEO Karun Kaushik and Kocalar shared their side on the social media platform X, with Kaushik saying they want to “set the record straight” on the anonymous attacks. He said that the evidence points to a “targeted cyberattack” rather than a whistleblower.
Kaushik wrote, “We believe the attacker purchased Delve under false pretenses, exfiltrated internal company data, and used it to launch a coordinated smear campaign. The posts rely on a mix of fabricated claims, cherry-picked screenshots, and stolen data taken out of context. (Economic Times)
Related: DeepDelver, Delve, Tech in Asia, Inc.com, The Economic Times
Donald Trump's proposed budget for civilian agencies for fiscal year 2027 sheds around $707 million from the Cybersecurity and Infrastructure Security Agency, according to a White House summary.
The move mirrors efforts last year to draw down resources from the nation’s main civilian cyberdefense bureau, which is located in the Department of Homeland Security. CISA has drawn the ire of the president and many of his allies over past activities tied to election security.
A cut of this size would mark a sharp escalation from the prior year’s budget fight, when the White House sought roughly $490 million in reductions — about 16% of the agency’s initial $3 billion budget — but ultimately faced congressional resistance that brought proposed cuts closer to a range of $130 million to $300 million.
If enacted, the FY27 proposal would deepen the reductions by more than $200 million compared to the administration’s earlier request, signaling a continued push to scale back the agency’s footprint significantly.
“CISA was more focused on censorship than on protecting the nation’s critical systems, and put them at risk due to poor management and inefficiency, as well as a focus on self-promotion,” the FY27 document says.
It adds that the budget would remove “duplicative” programs focused on state and local cyber funding. Notably, it proposes eliminating programs “focused on so-called misinformation and propaganda as well as external engagement offices such as council management, stakeholder engagement, and international affairs.” (Edward Graham, David DiMolfetta, and Alexandra Kelley / NextGov/FCW)
Related: Gadgets Now, The Register, Politico Pro, Vital Law
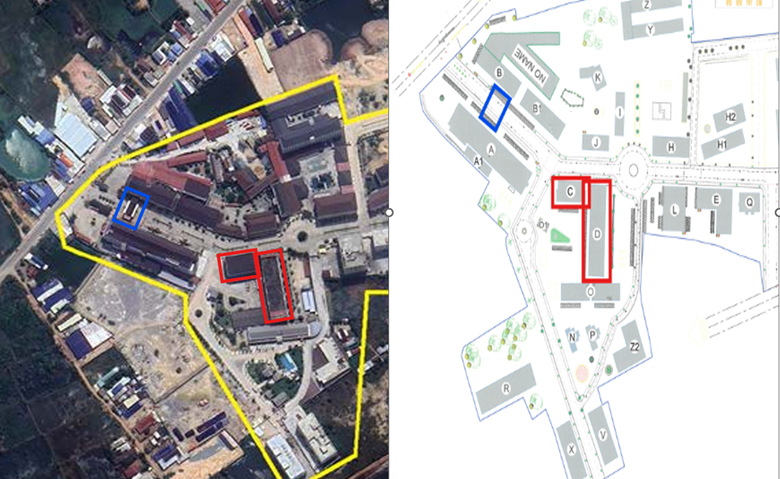
Cambodia's parliament passed the first law dedicated to targeting scam centers accused of bilking international victims out of billions of dollars, as pressure mounts on governments to tackle the illicit businesses.
Justice Minister Keut Rith said the law aimed to enhance the "cleaning operation" taking place across the country, as well as to ensure the centers do not return after the crackdown.
This law is strict like the fishing net, strict to ensure we don’t have the online scams anymore in Cambodia, strict to serve the interest of the Cambodian nation and people," he told reporters, adding the problem had also impacted the economy, tourism, and investment.
The new law will eventually go to Cambodia's king for final signature.
It lays out punishments of two to five years in prison and fines of up to $125,000 for those convicted of online scams.
Sentences for those convicted of scams conducted by gangs or against many victims can be up to 10 years in prison and as much as $250,000 in fines. It also outlines penalties for those convicted of money laundering, gathering victims' data, or recruiting scammers.
The law was passed days after Amnesty International released an analysis of official licensing documents issued by Cambodia’s Commercial Gambling Management Commission (CGMC) showing that casino owners are in direct control of buildings and sites where human rights abuses have been documented in at least 12 separate locations.
The findings corroborate testimony from compound survivors who described being on the casino property while they were confined and abused. (Chantha Lach / Reuters and Amnesty International)
Related: Al Jazeera, iGaming Business, AFP, The Australian, myRepublica
In early March, several official Syrian government accounts on X—including those linked to the presidency’s General Secretariat, the Central Bank, and multiple ministries—were hacked, raising a host of questions regarding how adequate the country's cybersecurity is.
The compromised profiles posted “Glory to Israel,” retweeted explicit material, and briefly renamed themselves after Israeli leaders.
Authorities moved to restore control within days, with the Ministry of Communications and Information Technology announcing “urgent steps” to recover the accounts and prevent further breaches. Yet what remained unsettled was the deeper question: How secure is the state’s digital front door?
In a government now dependent on commercial platforms for communication, losing a verified account doesn’t just disrupt messaging—it silences the state’s voice.
At first glance, the breach appeared politically charged. Pro‑Israel messages circulating on verified government accounts during a tense regional moment fueled speculation over motive and attribution. No group claimed responsibility, and officials did not clarify whether internal systems were compromised.
To analysts, the episode pointed less to a geopolitically driven hack and more to a familiar, systemic weakness.
“We still do not know exactly what happened. Whether the accounts were directly hacked or accessed through weak or reused credentials, the conclusion is much the same: very poor digital security practices,” says Noura Aljizawi, a senior researcher at the Citizen Lab, a research organization that monitors threats to civil society in the digital age. (Danni Maki / Wired)
Related: Space Daily
Florence's Uffizi Galleries said it was hit by a cyberattack earlier this year, but denied a newspaper report that the incident caused a major security breach or theft of data.
The statement came after Corriere della Sera daily reported that the attack had emptied the Uffizi's servers and prompted the emergency transfer of valuable jewels to the Bank of Italy.
The Uffizi said a cyberattack had targeted it on February 1, but added that nothing had been stolen and no information had been lost. It also denied that the hackers had obtained security maps or that employees' phones had been infiltrated.
The museum said the only disruption caused by the attack was linked to the time needed to restore backups, adding that it had released a statement about the incident after it had happened. Corriere reported that hackers had infiltrated the network of the Uffizi, Palazzo Pitti, and the Boboli Gardens, had taken control of the photographic server, and sent a ransom demand to the personal phone of Uffizi director Simone Verde.
It also said the closure of a section of the Palazzo Pitti and subsequent removal of valuables to the Bank of Italy was tied to renovation work planned last autumn and had nothing to do with the cyberattack. (Crispian Balmer and Silvia Ognibene / Reuters)
Related: Reuters, ANSA, BBC News, UPI, Art Forum, Tech Radar, Politico EU
The Qilin ransomware group has stolen data from Die Linke (The Left), a German democratic socialist political party, and is threatening to leak it.
On March 27, a day after the threat actor compromised its network, the party disclosed a cyber incident but stopped short of confirming a data breach.
“According to current findings, the attackers aim to publish sensitive data from the internal areas of the party organization as well as personal information of employees at the party headquarters,” Die Linke says.
“It is currently unclear whether and to what extent this has succeeded or has already occurred. However, such a risk exists.”
The party clarified that its membership database wasn’t impacted, specifically stating that the attackers failed in their effort to obtain member data.
Die Linke said that it received information that behind the attack is the Qilin ransomware group, describing the threat actor as Russian-speaking cybercriminals that are both financially and politically motivated. The German party also said that the attack on its systems “does not appear to be coincidental in this context.” (Bill Toulas / Bleeping Computer)
Related: Die Linke, Security Affairs, Cloaked
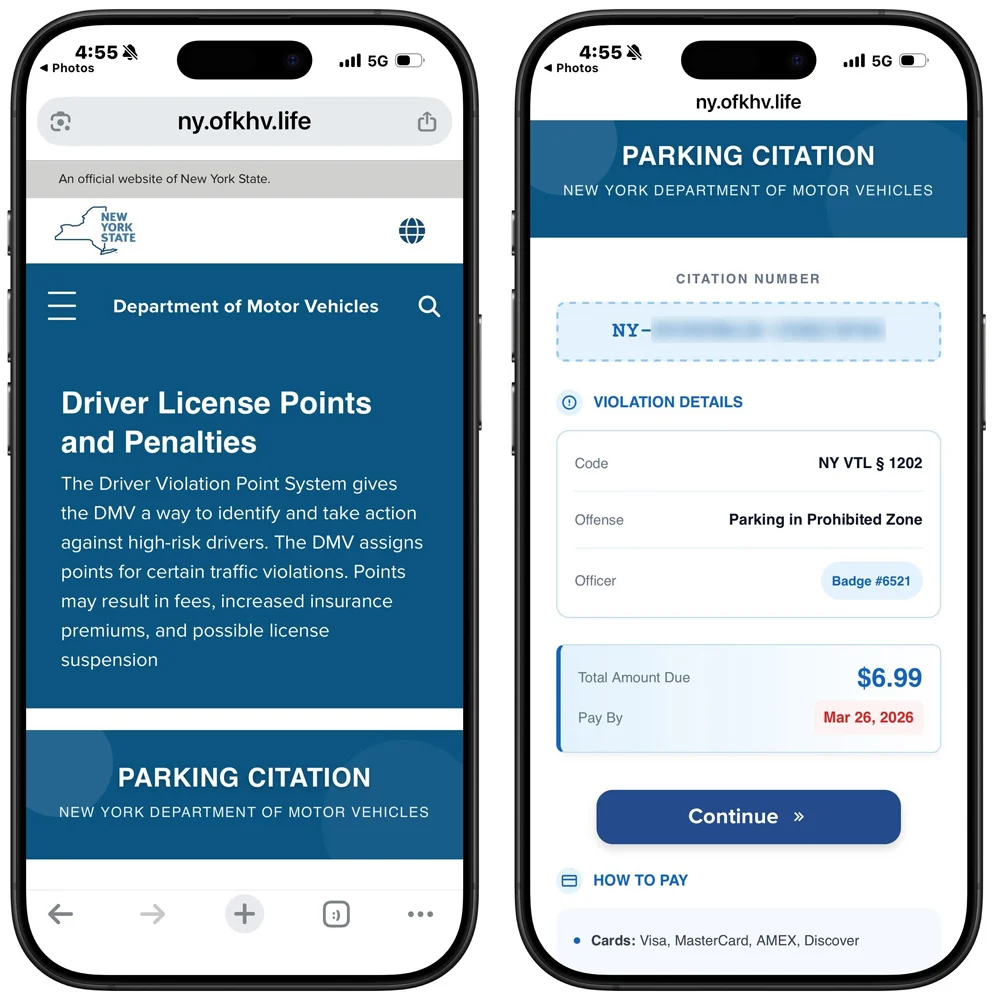
Scammers are sending fake "Notice of Default" traffic violation text messages impersonating state courts across the US, pressuring recipients to scan a QR code that leads to a phishing site demanding a $6.99 payment while stealing personal and financial information.
This tactic is a new variation of the widely sent toll violation and unpaid parking ticket scams that users received in 2025, which claimed to be from state toll agencies.
Scammers are sending fake "Notice of Default" traffic violation text messages impersonating state courts across the US, pressuring recipients to scan a QR code that leads to a phishing site demanding a $6.99 payment while stealing personal and financial information. (Lawrence Abrams / Bleeping Computer)
Related: KTTN, Missourinet, KOLN, NBC6, KOLO, WNYT
Harvard is monitoring an ongoing cybersecurity threat involving individuals impersonating University information technology staff to gain access to accounts and sensitive data, according to a Friday afternoon message to affiliates.
The attackers are contacting affiliates directly — often urging them to join live phone calls or directing them to fraudulent websites designed to mimic official Harvard pages — in an attempt to steal login credentials, according to the email.
Harvard Chief Information Security and Data Privacy Officer Michael Tran Duff wrote that the scam represents “an active and specific cybersecurity threat,” urging affiliates to remain on “high alert.”
Duff cautioned recipients not to engage with unsolicited communications claiming to be from “Harvard IT,” and warned against logging into unfamiliar websites, installing software, or executing commands at a caller’s direction. Legitimate Harvard websites, he noted, will always end in “.edu.”
The alert comes amid a broader wave of similar attacks at peer institutions. On Thursday, officials at the University of Pennsylvania’s Annenberg School warned affiliates of nearly identical “advanced social engineering attacks” involving impersonation and fake university websites. (Sebastian B. Connolly and Summer E. Rose / The Harvard Crimson)
Related: Hoodline
A new report dubbed "BrowserGate" warns that Microsoft's LinkedIn is using hidden JavaScript scripts on its website to scan visitors' browsers for installed extensions and collect device data.
According to a report by Fairlinked e.V., which claims to be an association of commercial LinkedIn users, Microsoft's platform injects JavaScript into user sessions that checks for thousands of browser extensions and links the results to identifiable user profiles.
The author claims that this behavior is used to collect sensitive personal and corporate information, as LinkedIn accounts are tied to real identities, employers, and job roles.
LinkedIn scans for over 200 products that directly compete with its own sales tools, including Apollo, Lusha, and ZoomInfo. Because LinkedIn knows each user's employer, it can map which companies use which competitor products. It is extracting the customer lists of thousands of software companies from their users' browsers without anyone's knowledge,' the report says.
"Then it uses what it finds. LinkedIn has already sent enforcement threats to users of third-party tools, using data obtained through this covert scanning to identify its targets." (Lawrence Abrams / Bleeping Computer)
Related: Browsergate.eu, The Next Web, Tom's Hardware, HackRead, Tech Times, Mezha, PPC Land, Gigazine
Fortinet released an emergency weekend security update for a new critical FortiClient Enterprise Management Server (EMS) vulnerability that is actively exploited in attacks.
Tracked as CVE-2026-35616, the flaw is an improper access control vulnerability that allows unauthenticated attackers to execute code or commands via specially crafted requests.
The issue was patched Saturday, with Fortinet confirming it has been exploited in the wild.
"Fortinet has observed this to be exploited in the wild and urges vulnerable customers to install the hotfix for FortiClient EMS 7.4.5 and 7.4.6," warns Fortinet.
Fortinet says the vulnerability impacts FortiClient EMS versions 7.4.5 and 7.4.6 and can be mitigated by installing one of a number of hotfixes. (Lawrence Abrams / Bleeping Computer)
Related: Security Affairs, Security Week, GBHackers, Cyber Press, Heise Online
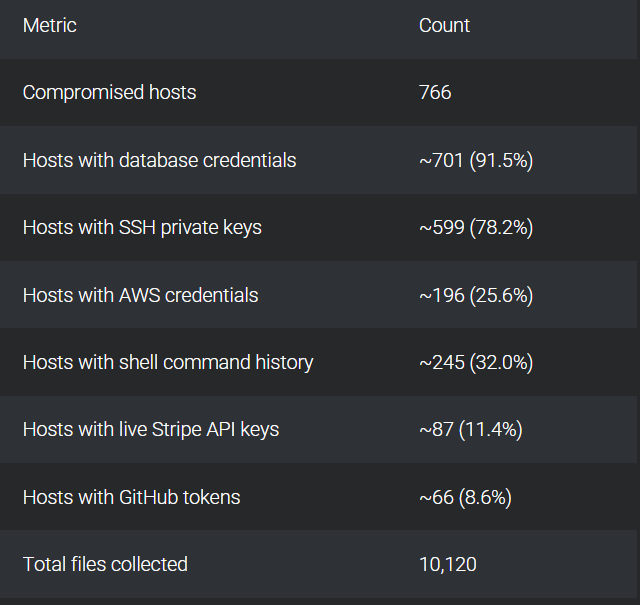
Researchers at Cisco Talos report that a threat actor has been exploiting vulnerable Next.js applications to compromise systems and exfiltrate credentials at scale.
Tracked as UAT-10608, the threat actor relies on automated scanning to identify applications impacted by CVE-2025-55182 (CVSS score of 10), a critical React vulnerability that allows remote, unauthenticated attackers to execute arbitrary code, and which is tracked as React2Shell by the cybersecurity community.
Following initial access, the attackers leverage automated scripts and the Nexus Listener framework to harvest credentials, cloud tokens, SSH keys, and environment secrets at scale.
According to Talos, at least 766 systems have been compromised, and more than 10,000 files have been collected as part of the campaign. (Ionut Arghire / Security Week)
Related: Cisco Talos, Bleeping Computer, CSO Online, SC Media
An EU law allowing tech companies to scan online messages for child abuse material expired on Saturday, although the firms aren't likely to stop the practice just yet.
A temporary European Union legislation had allowed companies — including Meta, Google, Microsoft, and Snapchat — to voluntarily scan their services for child sexual abuse material (CSAM). Law enforcement officials have described the process as “vital" to crack down on child abuse.
But the regime ran out on April 3, and EU legislators last month failed to agree on the terms to extend it.
Google, Meta, Microsoft, and Snapchat's parent company Snap said in a joint statement late on Friday that they "will continue to take voluntary action" to scan messages. "We call on EU institutions to conclude negotiations on a regulatory framework as a matter of urgency," the tech companies said. (Sam Clark / Politico EU)
Related: The Keyword, Social Media Today, CDT, digwatch, Snap, PPC Land
Keir Starmer’s government is trying to tempt Anthropic to expand its presence in the UK, looking to capitalize on the $380bn start-up’s fight with the US defense department to woo one of America’s top AI groups.
Staff at the Department for Science, Innovation and Technology have sketched out proposals for the San Francisco-headquartered company, spanning from an office expansion in London to a dual listing, according to multiple people with knowledge of the plans.
Downing Street has been supportive of the work, which will be put to Anthropic chief executive Dario Amodei when he visits the UK in late May as part of a trip to meet European customers and policymakers, they added.
Efforts to persuade the start-up to expand its presence in the UK beyond an existing office in London have stepped up in recent weeks after the US defense department labeled the start-up a supply-chain risk, said two of the people. (George Hammond and Jim Pickard / Financial Times)
Related: Engadget, Reuters, Taipei Times, Business Standard, Tech in Asia, Blockonomi, Benzinga, Washington Examiner
Best Thing of the Day: Leave It to the Professionals
Professional ransom negotiators have become a booming part of the cybersecurity industry as businesses seek help for high-stakes talks with criminal gangs.
Bonus Best Thing of the Day: A Cybercriminal By Any Other Name Would Sound Like a Loser
Cybersecurity folks continue to be fed up with the strangely sexy and powerful names that threat intel firms apply to cybercriminals, such as Wizard Spider and Velvet Tempest.
Worst Thing of the Day: If Everyone Likes It, Time to Destroy It
Donald Trump defunded the CIA World Factbook, a map and reference manual of Planet Earth and its inhabitants upon which nearly everyone could agree.
Closing Thought