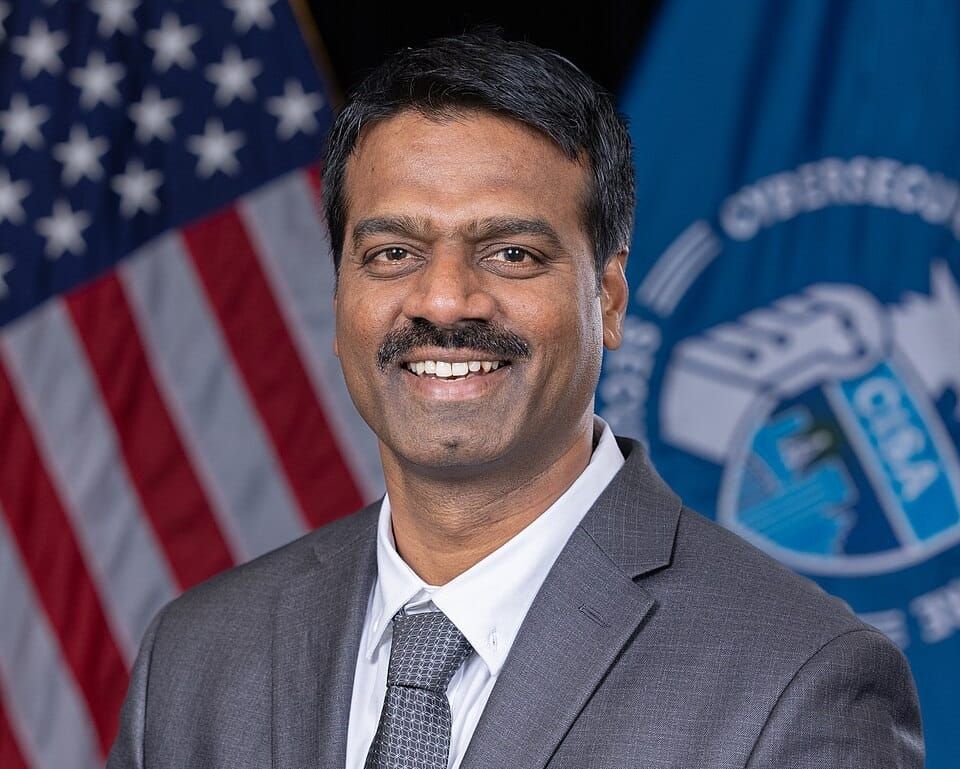
Gottumukkala is out as acting CISA director
Intellexa founder and three others sentenced to prison, Anthropic rejects Pentagon's weakened guardrails, Google employees oppose AI use in surveillance and autonomous weapons, Project Compass led to the arrest of 30 mostly young suspects, Medical device maker UFP hit by cyberattack, much more