Iran-linked hackers target critical infrastructure controls, risking disruption and sabotage
Anthropic's Glasswing could upend bug discovery and fixes, GRU-linked hackers infiltrate routers to steal email account passwords, Pro-Iranian group claims Chime and Pinterest cyberattacks, ICE confirms use of Paragon spyware, Hacking and spying services sold on Telegram to harass women, much more
Don't miss my latest CSO piece on how Anthropic's Glasswing announcement is about to change the future of vulnerability discovery.
Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
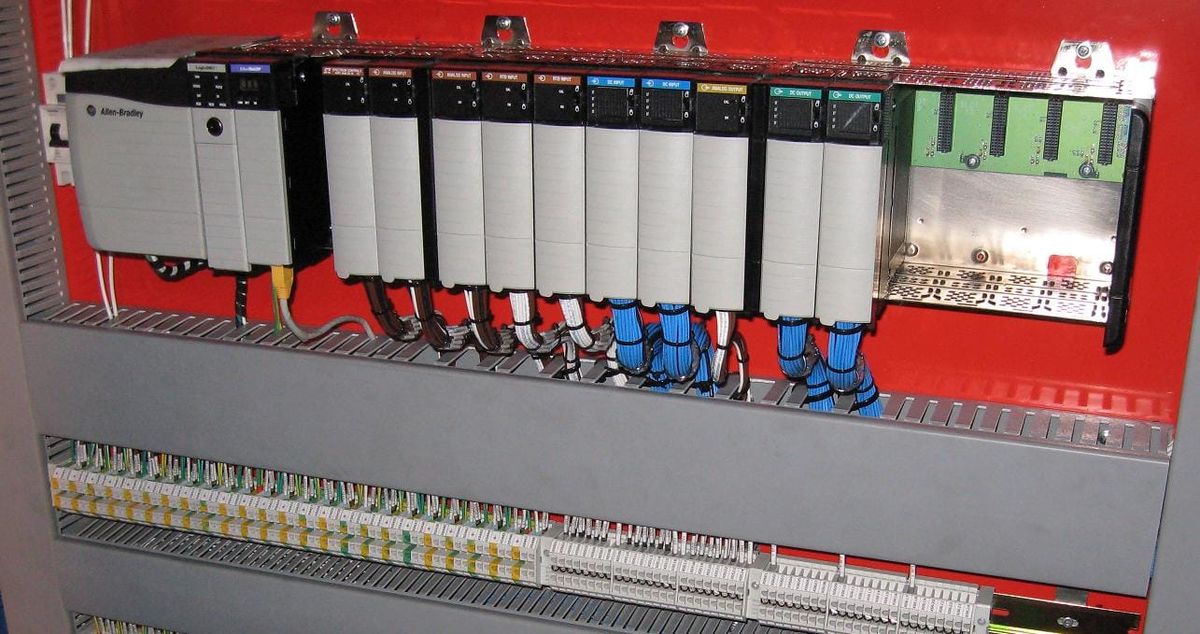
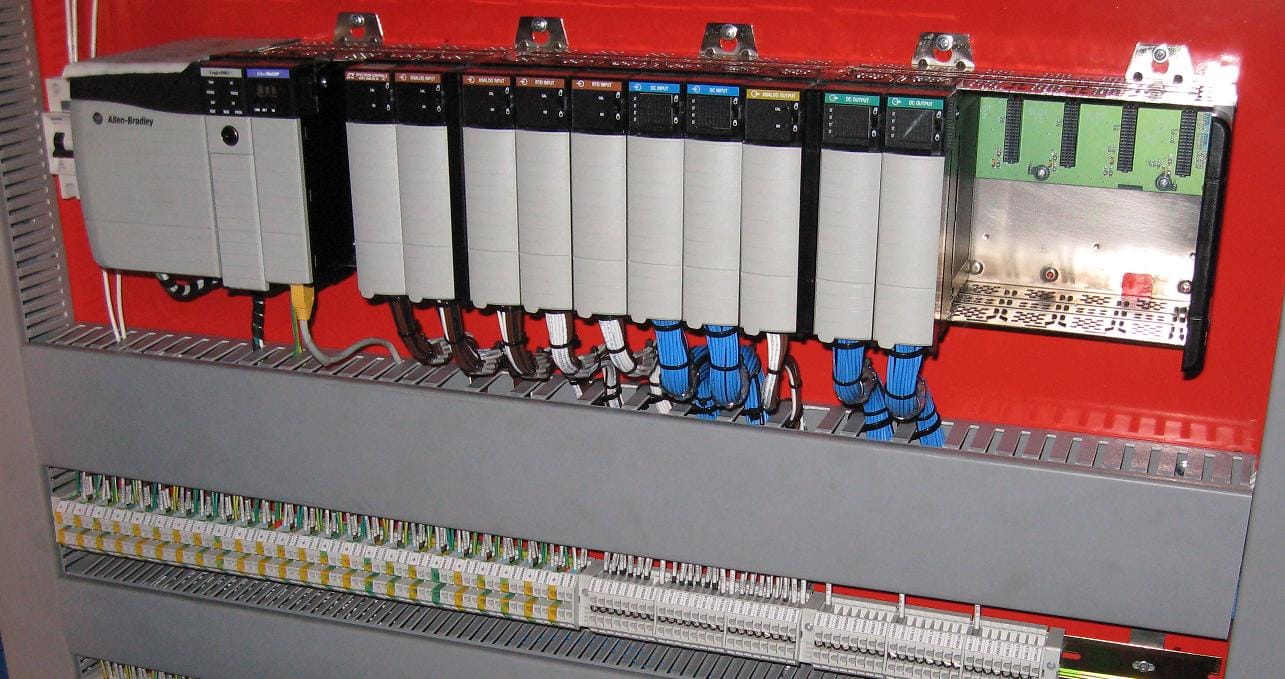
In a joint advisory, a group of US agencies including the FBI, the National Security Agency, the Department of Energy, and the Cybersecurity and Infrastructure Security Agency warned that a group of hackers affiliated with the Iranian government has targeted industrial control devices used in a series of critical infrastructure targets including in the energy sector, water and wastewater utilities, and unspecified “government facilities.”
According to the agencies, the hackers have targeted programmable logic controllers (PLCs)—a type of device designed to allow digital control of physical machinery—in those facilities, including those sold by industrial tech firm Rockwell Automation, with the apparent intention of sabotaging their systems.
By compromising those PLCs, the advisory warns, the hackers sought to change information on the displays of industrial control systems, which can in some scenarios cause system downtime, damage, or even dangerous conditions. “In a few cases, this activity has resulted in operational disruption and financial loss,” it reads, though it offers no details about the severity of those effects.
The advisory doesn’t specify a particular group responsible for the hacking campaign; it notes that the attacks are similar to those carried out by the Iran-linked group known as CyberAv3ngers, or the Shahid Kaveh Group, starting in late 2023. That team of hackers, believed to work in the service of the Iranian Revolutionary Guard Corps, inflicted several waves of attacks against Israeli and US targets in recent years, including gaining access to more than a hundred devices sold by industrial control system technology firm Unitronics, which are most commonly used in water and wastewater utilities.
In that hacking campaign, CyberAv3ngers set the names of the Unitronics devices to read “Gaza”—in a reference to Israel’s invasion of the territory in retaliation for Hamas’s October 7 attacks—and changed the devices’ displays to show an image of the CyberAv3ngers logo.
Despite the initial appearance of mere vandalism, industrial cybersecurity firms that tracked the attacks say that the hackers corrupted the Unitronics’ devices’ code deeply enough to disrupt services in water utility networks from Israel to Ireland to a Pittsburgh, Pennsylvania, facility in the US. (Andy Greenberg / Wired)
Related: CISA, CyberScoop, NextGov/FCW, Bleeping Computer, NBC News, New York Times, The Register, CNET, Newser, Security Affairs, Defense One, CRN, TechCrunch, Nextgov/FCW, Reuters, Los Angeles Times, CyberScoop, NBC Los Angeles, Security Week, Cyber Daily, The Guardian, CNN, Hoodline, Gizmodo, Biz Journals
Anthropic is taking steps to arm some of the world’s biggest technology companies with tools to find and patch bugs in their hardware and software in something it calls Project Glasswing.
The company is making a preview model of its new AI model, called Mythos, available to about 50 companies and organizations that maintain critical infrastructure, including Amazon, Microsoft, Alphabet-owned Google, and the Linux Foundation, along with a handful of cybersecurity firms, including CrowdStrike, Palo Alto Networks, and Cisco.
Mythos is a general-purpose AI model and was not specifically developed for cybersecurity purposes, Anthropic said. Yet, Mythos has already discovered several security issues, Cheng said, including a 27-year-old bug used in critical internet software. The AI system also found a 16-year-old vulnerability in a line of code for popular video game software that automated testing tools had scanned five million times but never detected, Anthropic said.
Dianne Penn, head of product management for research at Anthropic, said there are protections in place to ensure that members of Project Glasswing keep a tight grip on access to the Mythos model, but declined to share more details for security reasons. (Robert McMillan / The Wall Street Journal and Margi Murphy / Bloomberg)
Related: Anthropic, CSO Online, CyberScoop, Cisco, CNN, Axios, Fortune, Hacker News, r/singularity, The New Stack, The Verge, TechCrunch, 9to5Mac, Inc, Washington Examiner, Bloomberg, Fortune, Yahoo Finance, New York Times, Reuters, VentureBeat, CNBC, ZDNet, Wired
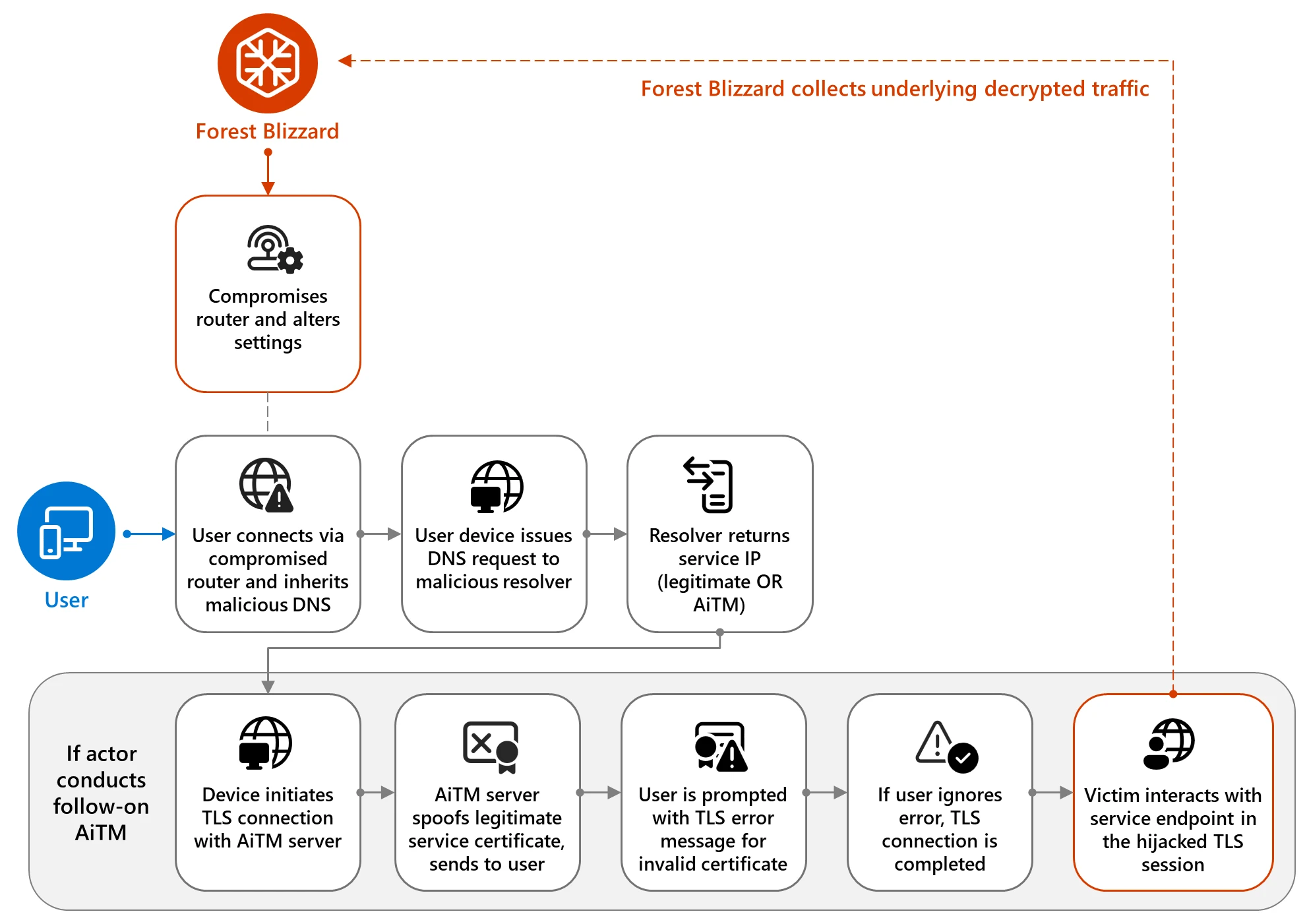
Russian government-linked hackers are compromising popular internet routers to steal passwords for email accounts and other online services, the UK’s National Cyber Security Center warned.
The hackers, a group known as APT28 or Fancy Bear or Forest Blizzard, are associated with Russia’s GRU military intelligence agency, according to research published by the UK.
British cyber officials said they have observed the alleged Russian intruders targeting routers manufactured by companies such as MikroTik and TP-Link. Attackers obtain access to the routers and modify their settings so that they redirect outgoing internet traffic through DNS servers that they control.
Such attacks put victims at risk of credential theft, data manipulation, and broader compromise, according to the alert, which also published guidance on how to mitigate the risks of an intrusion.
Paul Chichester, the center’s director of operations, said the malicious activity demonstrated that sophisticated hostile actors could leverage vulnerabilities in commonly used routers.
Lumen Technologies’ Black Lotus Labs published research on APT28’s router-hijacking campaign.
The researchers said they had identified thousands of potential victims from at least 120 countries communicating with the hackers’ infrastructure. “These operations primarily targeted government agencies — including ministries of foreign affairs, law enforcement, and third-party email providers,” the researchers said in a report.
Microsoft, which also released details of the campaign, said in a blog post that its researchers identified over 200 organizations and 5,000 consumer devices affected by these hacking operations, including at least three government organizations in Africa.
Finally, the US Justice Department announced it carried out a court-authorized disruption of the DNS hijacking network, which it said was operated by Russia's Main Intelligence Directorate of the General Staff (GRU) Military Unit 26165. The FBI called the effort Operation Masquerade.
The Justice Department said the GRU used routers to facilitate hijacking operations against worldwide targets, including individuals in military, government, and critical infrastructure sectors.
The FBI identified compromised routers in the U.S., collected evidence of Russian targeting, cut off GRU access, and reset them to normal functionality, the Justice Department said in its statement. (Ryan Gallagher / Bloomberg, Lorenzo Franceschi-Bicchierai / TechCrunch, Jaspar Ward and AJ Vicens / Reuters)
Related: Microsoft, NCSC.GOV.UK, Joint Advisory, Justice Department, IC3, Lumen, PCMag, Financial Times, Krebs on Security, The Register, The Record, Help Net Security, BleepingComputer, Mirror, Infosecurity, CyberScoop, Cybersecurity Insiders, Euractiv, Benzinga, Boston Globe, TechRadar, Bleeping Computer, Ars Technica
A pro-Iranian cybercrime group has claimed responsibility for cyberattacks on Chime Financial and Pinterest that knocked the websites of both companies offline.
Chime, a San Francisco-based fintech company, was hit with a distributed-denial-of-service attack on April 1, according to a person familiar with the matter who asked not to be named to discuss internal information.
Customers expressed frustration on social media that they were unable to access services at the time. Chime disclosed the outage on its website but didn’t share the reason why.
A pro-Iranian hacking group later claimed responsibility for the attack.
Pinterest, a San Francisco-based social networking company, was also knocked briefly offline in a similar attack. Once again, the pro-Iranian group claimed credit. (Margi Murphy and Paige Smith / Bloomberg)
Related: Giga Law
Immigration and Customs Enforcement is using Graphite spyware tools made by Israel's Paragon that can intercept encrypted messages as part of the agency's efforts to disrupt fentanyl traffickers, according to a letter sent last week by the agency's acting director, Todd Lyons.
Lyons' letter said ICE's Homeland Security Investigations (HSI) is using various tools as part of its mission to disrupt and dismantle foreign terrorist organizations, "particularly those involved in the trafficking of fentanyl."
His letter, dated April 1, was a belated response to an October inquiry from three Democratic members of the House Committee on Oversight and Government Reform expressing concern about the agency's potential use of the spyware Graphite, which was created by an Israeli company, Paragon Solutions.
The letter is the first time ICE has indicated it is using Graphite. The agency initially signed a $2 million contract with Paragon Solutions for an unspecified software product at the end of the Biden administration. But the contract was swiftly paused until it was revived by the Trump administration last fall. (Jude Joffe-Block / NPR)
Related: Gizmodo, CyberScoop, r/technology, r/politics
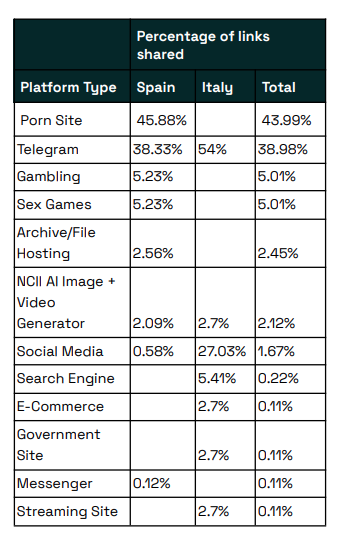
According to European nonprofit AI Forensics, thousands of men are members of Telegram groups and channels that advertise and sell hacking and surveillance services that can be used to harass friends, wives and girlfriends, and former partners, new research has uncovered.
AI Forensics also says that the communities are involved in extensive trading, selling, and promotion of a huge variety of abusive content, including nonconsensual intimate images of women, so-called nudifying services, plus folders of images that sellers claim include child sexual abuse material and depictions of incest and rape.
The group analyzed nearly 2.8 million messages sent across 16 Italian and Spanish Telegram communities that are regularly posting abusive content targeting women and girls. More than 24,000 members of the Telegram groups and channels took part in posting 82,723 images, videos, and audio files over the course of the study, the analysis says. Many posts target celebrities and influencers, but men in the groups also frequently victimize women they know.
Among the extensive types of abusive content and services observed by the AI Forensics researchers were frequent references to the access, publishing, and doxing of women’s private information, sharing their Instagram or TikTok content, as well as references to spying or hacking. “Victims are often named, tagged, and locatable via shared profile links,” the group’s report says. (Matt Burgess / Wired)
Related: AI Forensics
Dutch healthcare provider ChipSoft, which provides healthcare to about 70% of Dutch hospitals, has been hit by a ransomware attack, according to Z-Cert, the center of expertise for digital security in healthcare.
The company said that there has been a "data incident" involving "possible unauthorized access."
The healthcare provider says it is taking all measures to "limit the adverse consequences as much as possible." According to the company, immediately after the discovery of the hack, attempts were made to deny criminals access to the systems. (NOS News)
Related: NL Times, Dutch News
Minnesota Governor Tim Walz issued an emergency executive order lending the assistance of the state’s National Guard to Winona County, which is facing a cyberattack disrupting its “critical systems and digital services.”
According to the order, the county has been “working around the clock” since discovering the cyberattack on Monday. According to a press release from the governor’s office, the cyberattack is “significantly impairing the county’s ability to deliver vital emergency and municipal services.”
Walz’s order notes that the county, a region of some 50,000 residents at the southeastern edge of the state, is working with the FBI, a cybersecurity vendor, the state’s IT agency, the Minnesota Bureau of Criminal Apprehension, and the League of Minnesota Cities, a membership association that promotes “excellence in local government.” (Colin Wood / StateScoop)
Related: Minnesota Governor, Winona Daily News, Northern News Now, Post Bulletin, The Cyber Express, MPR News, KSTP, News8000, DL-Online, KAAL, KTTC
A trove of sensitive LAPD records, including officer personnel files and documents from Internal Affairs investigations, is among the materials believed to have been seized by hackers in a breach last month involving the LA city attorney’s office.
The Los Angeles Police Department said that unauthorized individuals had gained access to a digital storage system containing discovery documents from previously adjudicated or settled LAPD civil litigation.
“We take this incident very seriously and are working with the LA City Attorney’s Office to gain access to the impacted files to understand the full scope of the data breach,” the department stated.
Some of the records have started surfacing on social media platforms, including X. Among the first to post a file from the hack was the account @WhosTheCop, which regularly posts about information related to police accountability. (Libor Jany and Richard Winton / Los Angeles Times)
Related: National Today
Over a dozen companies have suffered data theft attacks after a SaaS integration provider was breached and authentication tokens stolen, with the majority of the data theft attacks targeting the cloud data platform Snowflake.
Snowflake confirmed "unusual activity," stating that a small number of its customers were impacted. Numerous sources have reported that the attacks stem from a security incident at data anomaly detection company Anodot.
Anodot is an AI-based analytics company that provides real-time anomaly detection for business and operational data, helping organizations automatically spot unusual changes in revenue, transactions, and system performance using machine learning. Data analytics company Glassbox acquired the company in November 2025.
Numerous companies are now being extorted by the ShinyHunters extortion gang, which is demanding ransom payments to prevent the release of stolen data.
After learning of the attacks, the ShinyHunters group confirmed that they were behind them, claiming to have stolen data from dozens of companies this past Friday. They also confirmed their attempts to steal data from Salesforce, but said they were blocked by AI detection. (Lawrence Abrams / Bleeping Computer)
Hackers are exploiting a maximum-severity vulnerability, tracked as CVE-2025-59528, in the open-source platform Flowise for building custom LLM apps and agentic systems to execute arbitrary code.
The flaw allows injecting JavaScript code without any security checks and was publicly disclosed last September, with the warning that successful exploitation leads to command execution and file system access.
The problem is with the Flowise CustomMCP node allowing configuration settings to connect to an external Model Context Protocol (MCP) server and unsafely evaluating the mcpServerConfig input from the user. During this process, it can execute JavaScript without first validating its safety.
Caitlin Condon, security researcher at vulnerability intelligence company VulnCheck, announced on LinkedIn that their Canary network has detected exploitation of CVE-2025-59528.
“Early this morning, VulnCheck's Canary network began detecting first-time exploitation of CVE-2025-59528, a CVSS-10 arbitrary JavaScript code injection vulnerability in Flowise, an open-source AI development platform,” Condon warned.
Related: Flowise, Security Week, SC Media, CSO Online, Security Affairs, Caitlin Condon on LinkedIn
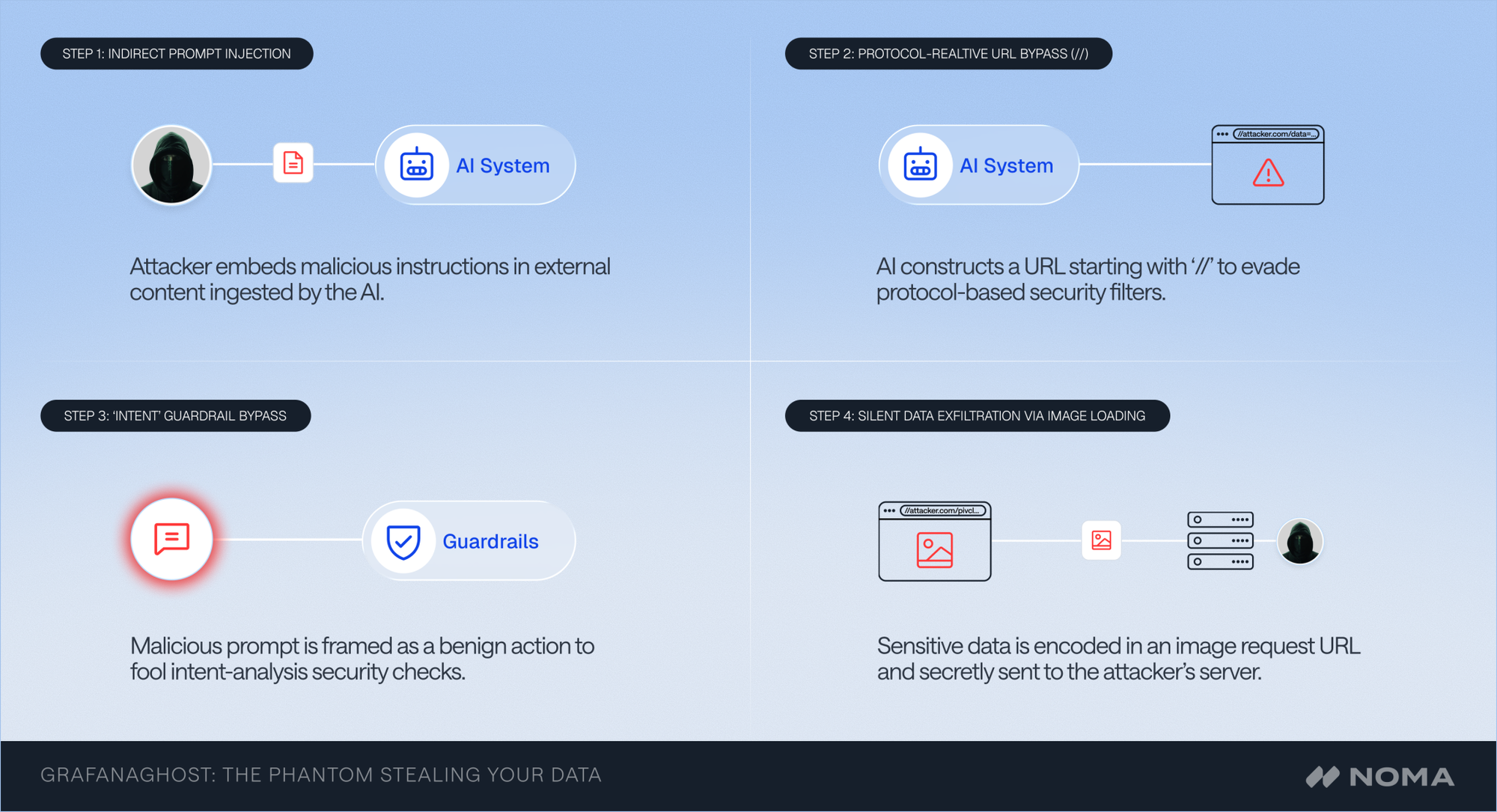
Researchers at Noma Security disclosed a new vulnerability they are calling GrafanaGhost, an exploit capable of silently stealing sensitive data from Grafana environments by chaining multiple security bypasses, including a method that circumvents the platform’s AI model guardrails without requiring any user interaction.
Grafana is widely deployed across enterprise organizations as a central hub for observability and data monitoring, typically housing real-time financial metrics, infrastructure health data, private customer records, and operational telemetry, among other uses.
The attack requires no login credentials and does not depend on a user clicking a malicious link. It begins when an attacker crafts a specific URL path using query parameters originating outside the victim organization’s environment. Because Grafana handles entry logs, an attacker can gain access to an enterprise environment to which they have no legitimate connection. The attacker then injects hidden instructions that Grafana’s AI processes — a tactic known as prompt injection — using specific keywords to cause the model to ignore its own guardrails.
Grafana has built-in protections designed to prevent prompt injection, but Noma’s researchers found a flaw in the logic underlying that protection — one that could be exploited by formatting a web address in a way that Grafana’s security check misread as safe, while the browser treated it as a request to an external server the attacker controlled.
The gap between what the security check believed it was allowing and what actually happened was enough to open the door for the attack. (Greg Otto / CyberScoop)
Related: Noma Security, HackRead, CSO Online, Dark Reading
Five public officials in Evangeline Parish in Louisiana have been arrested following an investigation into allegations of malfeasance involving the unauthorized access and dissemination of protected information.
The investigation, prompted by the Evangeline Parish Sheriff’s Office (EPSO) and conducted by the Louisiana State Police Criminal Investigations Division (LSP-CID), uncovered a breach of trust within the community.
The investigation revealed that these officials allegedly accessed state and government computer databases and shared sensitive information regarding ongoing criminal cases with an arrested defendant.
The compromised data included information about alleged victims in active investigations, raising serious concerns about the integrity of local law enforcement. (Khalale Smith / NewsNationNow)
Related: Louisiana State Police, WDSU, KTAL
Best Thing of the Day: Making Lemonade Out of Malware
Reddit user SD483 was targeted by a fake job interview on Wellfound that aimed to deliver malware, but instead SD483 spent the next several hours reverse-engineering the malware in an air-gapped Docker lab and reported it to the FBI.
Worst Thing of the Day: Don't Believe Everything You Read
The New York Times fell for the false story behind an “AI-powered” telehealth startup worth $1.8 billion and run by two brothers, which is in reality a scam outfit facing a class-action lawsuit by the FDA.
Closing Thought