Iran's Handela group claims control of the IT infrastructure in St. Joseph County, Indiana
Hasbro takes down systems after cyberattack, Italy’s ASIGINT accused of fake WhatsApp app, Attackers use WhatsApp to spread malicious MSI files, $250M stolen from DeFi project Drift, Anthropic knocks out GitHub repos in frantic bid to pull back exposed code, much more


Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
The Iranian Handela hacking group, allegedly responsible for the March hacking of Federal Bureau of Investigations Director Kash Patel and the major breach of American medical supply giant Stryker, has claimed an "attack" in St. Joseph County, Indiana, the fifth-most populous county in Indiana, and home to Notre Dame University.
The Handala Hack Team posted on Wednesday, April 1, online that they “have completely taken control of the centralized IT infrastructure of St. Joseph County in the state of Indiana.”
County Council member Randall Figg and County Commissioners President Carl Baxmeyer confirmed a breach of a third-party fax system. Figg said no servers were hacked.
Baxmeyer said he does not believe any sensitive information was accessed, and it is currently under investigation.
Further details will be released to the public on Thursday, April 2, according to Baxmeyer. (Juliane Balog / South Bend Tribune)
Related: NewsTalk95.3, WSBT, WNDU, Fox59, Foundation for the Defense of Democracies
In an SEC filing, American toy-making giant Hasbro confirmed a cyberattack, and the company says it may take “several weeks” before the incident is resolved.
The company said that it detected an intrusion on March 28, which prompted the company to take down some of its systems.
Hasbro said it has implemented and continues to roll out business continuity plans to allow it to “take orders, ship product and conduct other key operations while it resolves this situation.”
Parts of Hasbro’s website appeared down as of Wednesday, when checked by TechCrunch. One error message said the site was “currently undergoing maintenance.”
The company said it has called cybersecurity professionals to help, but noted that it was continuing to “implement measures to secure its business operations,” suggesting that the hackers may still be in the company’s systems. (Zack Whittaker / TechCrunch)
Related: SEC, Reuters, The Verge, Help Net Security, BBC, Cord Cutters News, WPXI-TV, CXO Digital Pulse, Cybersecurity Insiders, CBS19, Times of India, Apple Insider, Wall Street Journal, The Next Web, Guru Focus, The Record
Meta announced the adoption of formal and technical measures against the actions of ASIGINT, an Italy-based technology company accused of having created and distributed a fraudulent application designed to imitate the look and feel of WhatsApp.
The operation conducted by the Meta security team led to the identification of malicious software distributed not through official channels such as the Google Play Store or the Apple App Store, but through less-controlled third-party channels.
The method used to target users is based on so-called social engineering, a manipulation technique that tricks people into performing reckless actions, such as installing unverified software.
In this case, the perpetrators convinced a limited number of individuals to download a modified client, that is, an altered version of the official application, by presenting it as an update or a legitimate variant of WhatsApp.
Once installed on the victim's device, this software would have allowed external actors to gain access to the data on the smartphone.
Meta emphasizes that the scam did not exploit an inherent vulnerability in WhatsApp's systems. (Pier Luigi Pisa / La Repubblica)
Related: The Record, TechCrunch, Security Affairs, The Next Web, 9to5Mac, Silicon Canals, MacTech
Researchers at Microsoft report that miscreants are abusing WhatsApp messages in a multi-stage attack that delivers malicious Microsoft Installer (MSI) packages, allowing criminals to control victims' machines and access all of their data.
The campaign began in late February, and the attack chain starts with a WhatsApp message that delivers malicious Visual Basic Script (VBS) files.
Somehow, the attacker tricks the message recipient into executing the malicious file on their system. They likely do this using a compromised WhatsApp session so that the message appears to come from one of the victim's existing contacts. Or they blast users with a lure that contains a sense of urgency, prompting the recipient to open the file in a rush.
Once it's executed, the malicious script creates hidden folders in C:\ProgramData and drops renamed versions of legitimate Windows utilities - for example, curl.exe renamed as netapi.dll and bitsadmin.exe as sc.exe.
Using legitimate Windows tools for evil purposes allows attackers to blend in with normal network activity - defenders call this "living off the land" - but the miscreants did make a mistake in renaming these binaries.
"Notably, these renamed binaries retain their original PE (Portable Executable) metadata, including the OriginalFileName field, which still identifies them as curl.exe and bitsadmin.exe," Microsoft's researchers wrote. (Jessica Lyons / The Register)
Related: Microsoft, SC Media, Cyber Security News, Heise Online, Cyber Press, CSO Online, Computing
Solana-based decentralized finance (DeFi) platform Drift warned users about an "active attack" on its platform, saying it had suspended withdrawals and deposits.
Arkham data said over $250 million had moved from Drift to an interim wallet before moving to various other addresses. Less than $600,000 was in the address as of press time.
The Drift (DRIFT) token's price fell over 20% in the hours after the exploit was first reported, trading at about $0.05 as of press time. (Helene Braun / CoinDesk)
Related: The Block, Coinpedia Fintech News, The Record, Blockchain.News, CoinGape, Cryip, TechCrunch, Yahoo Finance, DL News, Bloomberg, Bitcoin News, The Daily Hodl, Cointelegraph
Anthropic is racing to contain the fallout after accidentally exposing the underlying instructions it uses to direct Claude Code, the popular artificial-intelligence agent app that has won the company an edge with developers and businesses.
By Wednesday morning, Anthropic representatives had used a copyright take-down request to force the removal of more than 8,000 copies and adaptations of the raw Claude Code instructions—known as source code—that developers had shared on programming platform GitHub. It later narrowed its take-down request to cover just 96 copies and adaptations, saying its initial ask had reached more GitHub accounts than intended.
The leak of “some internal source code” didn’t expose any customer information or data, a spokesman for Anthropic said. Nor did it divulge the valuable inner mathematics—sometimes called weights—of the company’s expensive and powerful AI models.
“This was a release packaging issue caused by human error, not a security breach. We’re rolling out measures to prevent this from happening again,” the spokesman said.
But the leak did reveal commercially sensitive information, including Anthropic’s proprietary techniques, tools, and instructions for cajoling its AI models to work as coding agents. Those techniques and tools are called a harness because they are what allow users to control and direct those models, much like a harness allows a rider to guide a horse.
In the process of its take-downs, Anthropic accidentally caused thousands of code repositories on GitHub to be taken down while trying to pull copies of its most popular product’s source code off the internet. (Sam Schechner and Robert McMillan / Wall Street Journal and Tim Fernholz / TechCrunch)
Related: PCMag, Digital Music News, Binance, Gizchina, Bitget, Slashdot
The FBI last week deemed a recent China-linked cyber intrusion into a sensitive agency surveillance system a “major incident,” meaning it poses significant risks to US national security, according to one congressional aide and two US officials with knowledge of the matter.
The bureau first told Congress on March 4 that it was investigating suspicious activity on an internal agency system that contained “law enforcement sensitive information.” The FBI did not publicly identify who was behind the activity at the time, but POLITICO previously reported that China is suspected.
The FBI determined the intrusion meets the definition of a major incident under a federal data security statute known as FISMA, said the three people. Congress was informed of the decision earlier this week, according to the aide. This person, like others in this report, was granted anonymity because they were not authorized to speak publicly on the investigation.
The determination suggests the hackers successfully compromised swathes of sensitive data stored directly on FBI systems, likely marking a major counterintelligence coup for China. FISMA requires agencies to tell lawmakers within seven days about any digital intrusion it has determined is “likely to result in demonstrable harm” to US national security.
Cynthia Kaiser, the former deputy assistant director of the FBI’s cyber division, said she is not aware of the FBI making any such determination on a hack affecting its own systems since at least 2020. (The FBI last week deemed a recent China-linked cyber intrusion into a sensitive agency surveillance system a “major incident,” meaning it poses significant risks to US national security, according to one congressional aide and two US officials with knowledge of the matter. (John Sakellariadis / Politico)
US Immigration and Customs Enforcement said it purchased spyware made by Israel's Paragon designed to hack phones and access encrypted messages as part of an effort to counter the flow of fentanyl into the US.
The immigration agency signed a $2 million deal in 2024 to acquire spyware manufactured by Paragon, which is designed to covertly access private messages and other data stored on mobile phones.
The contract was the subject of a stop-work order soon after by the Biden administration. But it was reactivated last August by the Trump administration, triggering concerns from rights groups about potential abuses of the technology to target opponents of ICE’s mass deportation campaign. (Ryan Gallagher / Bloomberg)
A cybersecurity attack is affecting several Massachusetts towns that share a regional emergency communications center.
The cyberattack affecting the Patriot Regional Emergency Communications Center and associated towns was identified early Tuesday, according to statements from affected towns.
The towns of Ashby, Dunstable, Pepperell, and Townsend also said their police and fire departments were impacted by the attack, to varying degrees. The regional communication center is located in Pepperell.
Police in Groton, which the regional communications center also serves, posted alerts on social media that business lines for those departments were unavailable, although those statements did not specifically reference a cyberattack.
According to statements from Pepperell and Townsend, leaders called upon insurance providers, cybersecurity specialists, and state and federal law enforcement for help. They are now working to determine the scope of what data may be compromised. (Phil Tenser / WCVB)
Related: GovTech, Lowell Sun, Boston Globe
Some Oklahomans are receiving letters warning that their personal information, including Social Security numbers, has been accessed in a security incident involving the Oklahoma Tax Commission’s online taxpayer portal.
The letters, dated March 27, 2026, say the Oklahoma Tax Commission discovered suspicious activity in December 2025 involving the Oklahoma Taxpayer Access Point, known as OK-TAP.
The agency said it sent the notices to individuals whose information was contained in files accessed by unauthorized users. (Emma McAndrews / Fox25)
Related: KOCO, KFOR, KJRH, OK Energy Today
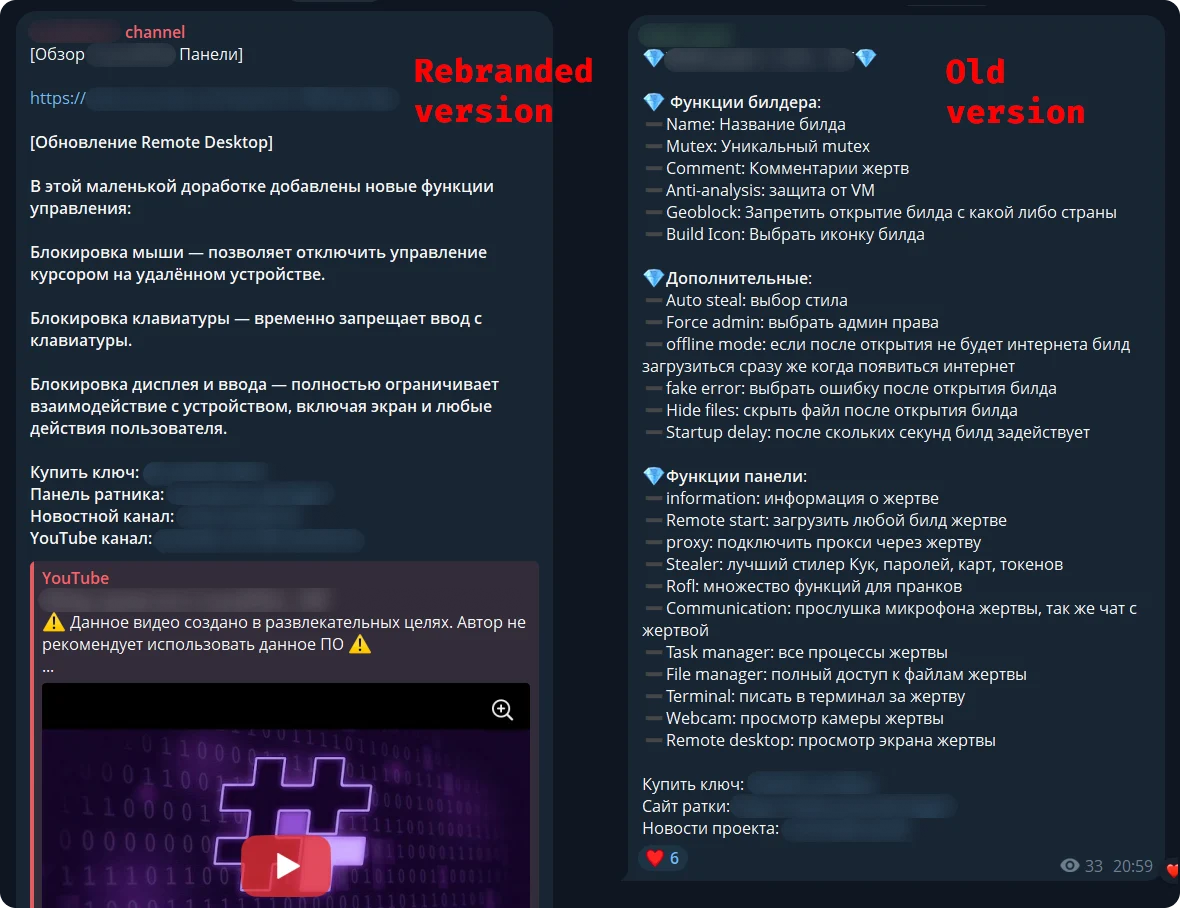
Researchers at Kaspersky report that a new malware-as-a-service called CrystalRAT is being promoted on Telegram, offering remote access, data theft, keylogging, and clipboard hijacking capabilities.
The malware emerged in January with a tiered subscription model. Apart from the Telegram channel, the MaaS was also promoted on YouTube via a dedicated marketing channel that showcased its capabilities.
Kaspersky researchers say that the malware features strong similarities to WebRAT (Salat Stealer), including the same panel design, Go-based code, and a similar bot-based sales system.
CrystalX also includes an extensive list of prankware features designed to annoy the user or disrupt their work. Despite its "fun" side, CrystalX offers a large set of data theft capabilities.
A series of prankware features in the malware do not improve the attack’s monetization potential for cybercriminals, but they make the product distinctive and could bait script kiddies and low-skilled/entry-level threat actors into getting a subscription. (Bill Toulas / Bleeping Computer)
Related: Securelist
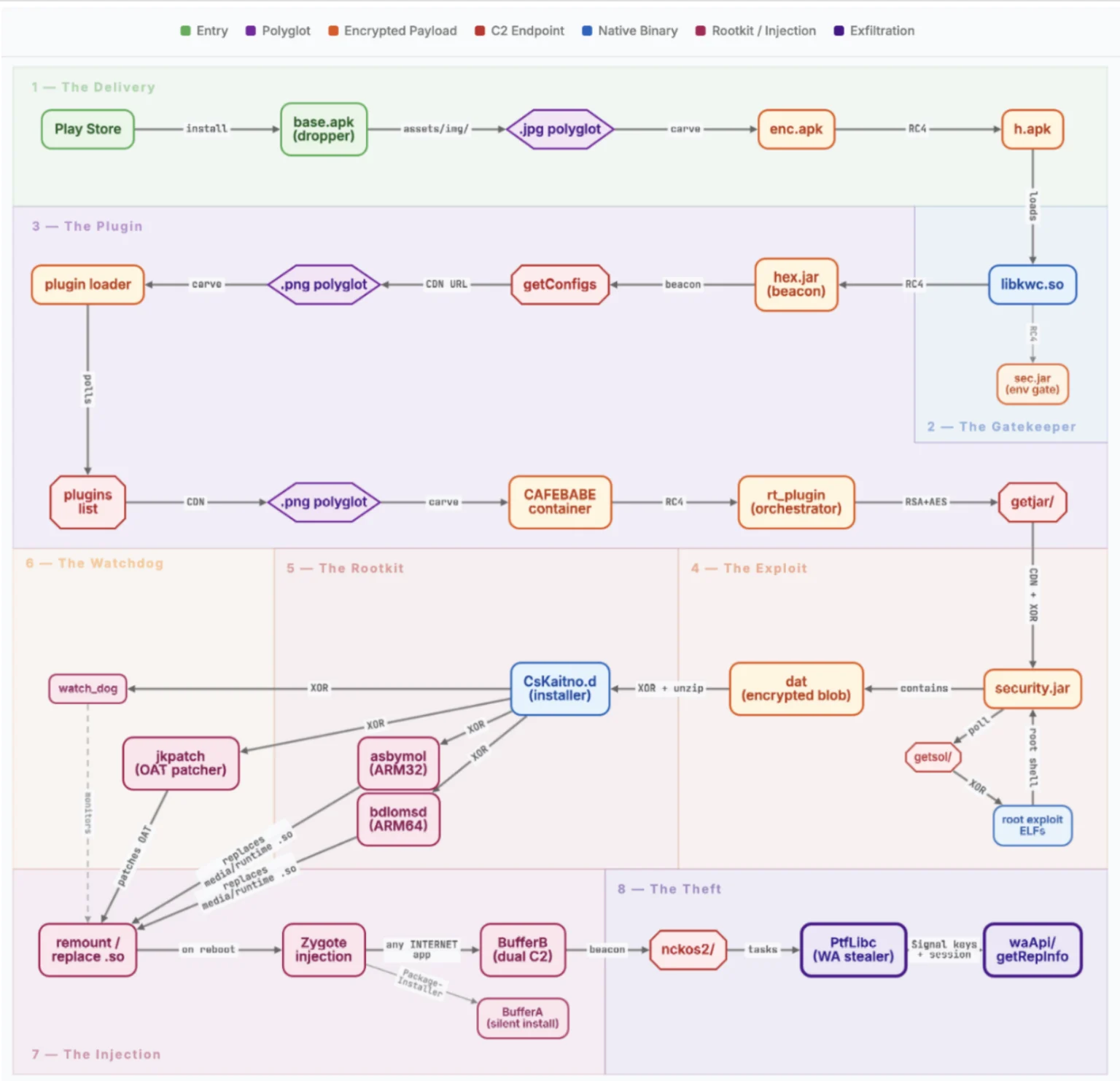
Researchers at McAfee report that a new Android malware named NoVoice was found on Google Play, hidden in more than 50 apps that were downloaded at least 2.3 million times.
The apps carrying the malicious payload included cleaners, image galleries, and games. They required no suspicious permissions and provided the promised functionality.
After launching an infected app, the malware tried to obtain root access on the device by exploiting old Android vulnerabilities that received patches between 2016 and 2021.
McAfee discovered the NoVoice operation but could not link it to a specific threat actor. However, they highlighted that the malware shared similarities with the Triada Android trojan. (Bill Toulas / Bleeping Computer)
Related: McAfee, Tom's Guide, GBHackers
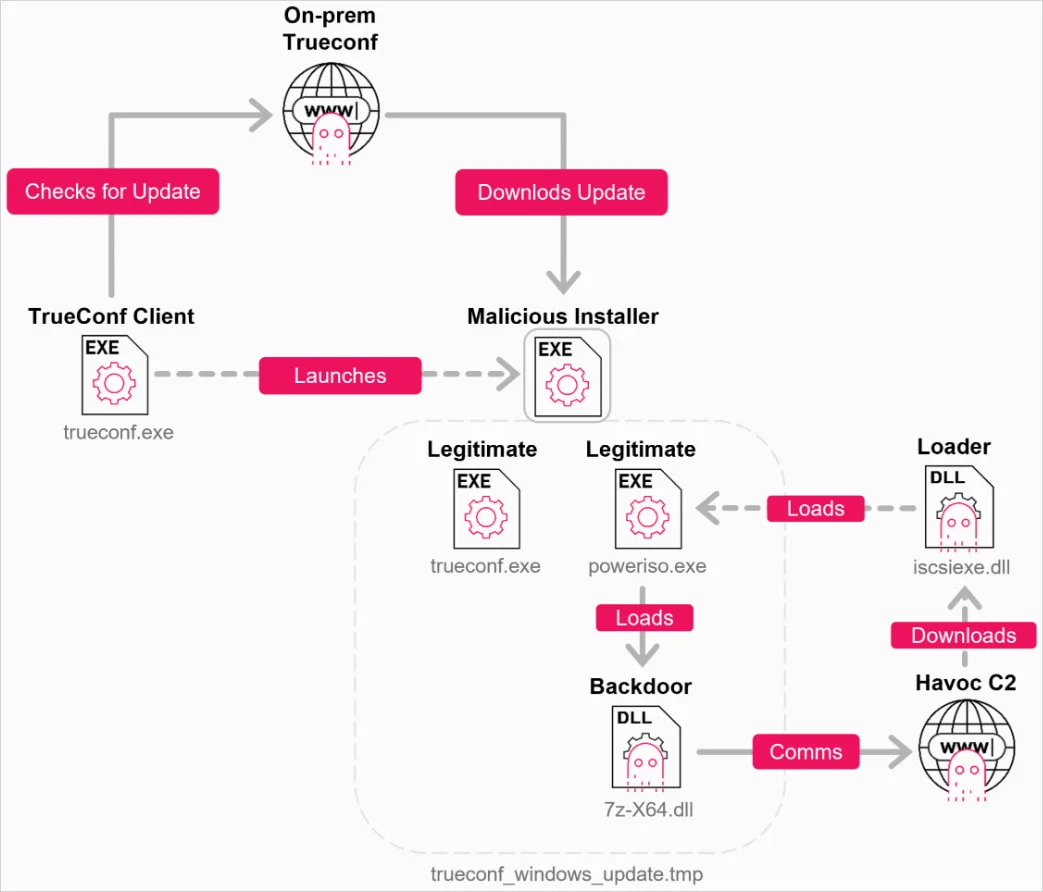
Researchers at Check Point report that hackers have targeted TrueConf conference servers in attacks that exploit a zero-day vulnerability, allowing them to execute arbitrary files on all connected endpoints.
The flaw is tracked as CVE-2026-3502 and received a medium severity score. It stems from a missing integrity check in the software’s update mechanism, which can be used to replace the legitimate update with a malicious variant.
TrueConf is a video conferencing platform that can run as a self-hosted server. Although it also supports cloud deployments, it is generally designed for closed, offline environments.
According to the vendor, more than 100,000 organizations transitioned to TrueConf during the COVID-19 pandemic for remote online business activities. Among TrueConf users are military forces, government agencies, oil and gas corporations, and air traffic management companies.
CheckPoint researchers have been tracking a campaign they track as TrueChaos that, since the beginning of the year, has exploited CVE-2026-3502 in zero-day attacks targeting government entities in Southeast Asia.
“An attacker who gains control of the on-premises TrueConf server can replace the expected update package with an arbitrary executable, presented as the current application version, and distribute it to all connected clients,” CheckPoint says. (Bill Toulas / Bleeping Computer)
Related: Check Point, SC Media, Help Net Security, Cyber Press
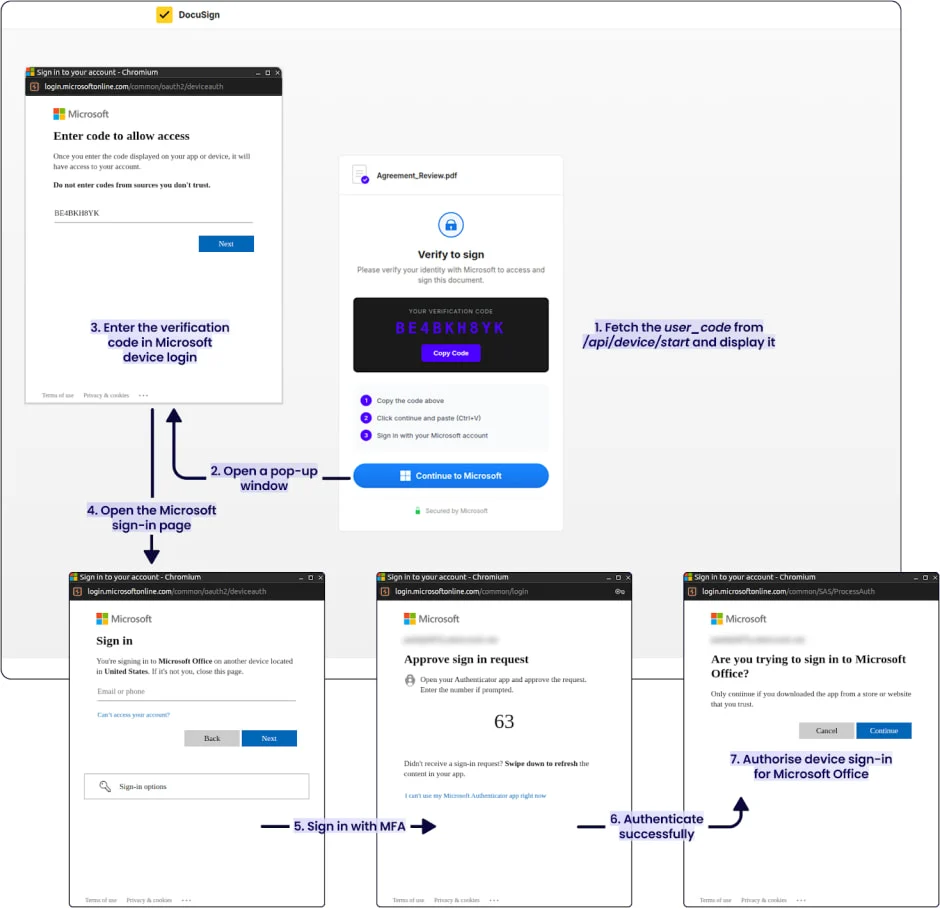
Researchers at threat detection and response company Sekoia report that a new malicious kit called EvilTokens integrates device code phishing capabilities, allowing attackers to hijack Microsoft accounts and provide advanced features for business email compromise attacks.
The kit is sold to cybercriminals over Telegram and is under continuous development, its author stating that they plan to extend support for Gmail and Okta phishing pages.
Device code phishing attacks abuse the OAuth 2.0 device authorization flow, in which attackers gain access to a victim's account by tricking the owner into authorizing a malicious device.
The technique is well-documented and has been used by various threat actors, including Russian groups tracked as Storm-237, UTA032, UTA0355, UNK_AcademicFlare, and TA2723, and the ShinyHunters data extortion group. (Bill Toulas / Bleeping Computer)
Related: Sekoia, Help Net Security, Cyber Security News
Arrest documents allege that three Dallas men – Mickael Toloza Parra, Luis Oviedo Rico, and Elvis Oviedo Rico – worked together to install malware on a bank ATM in Tyler for financial gain in December.
The men are being held in the Smith County Jail on charges of engaging in organized criminal activity in connection with a Dec. 19 incident at a Southside Bank location in Tyler. The Oviedo Rico brothers were arrested Jan. 30 and remain jailed on $1 million bonds. Toloza Parra was arrested on March 30 and remains jailed on a $1.5 million bond.
According to arrest affidavits, the three men participated in a cyber-physical crime known as “jackpotting,” in which suspects install malicious software or hardware onto an ATM’s hard drive or computer system.
The documents state that during the overnight hours of Dec. 19, 2025, suspects opened the ATM enclosure, removed the internal hard drive, and installed a device designed to intercept signals and redirect them to remote partners. Surveillance video captured a vehicle approaching the ATM and individuals opening the machine. (Zak Wellerman / CBS19)
According to cybersecurity firm Synology, organizations in Thailand are dealing with more than 3,200 cyberattacks a week on average, a level about 164% higher than the global average.
At the same time, ransomware incidents in Thailand have exceeded 109,000, the highest total recorded in Southeast Asia.
Recent data also point to a broader deterioration in the cyber risk environment. In the first five months of 2025, Thailand recorded more than 1,000 cyber incidents, with ransomware, data leaks, and account-based attacks among the main threats.
Separately, Check Point Software has reported that about 3,201 cyberattacks per week hit organizations in Thailand in the first half of 2025, also 164% above the global average, reinforcing concerns over the country’s expanding attack surface. (The Nation)
Related: Money and Banking Online
The European Commission has told some of its most senior officials to shut down a Signal group they were using to exchange information over fears it was a hacking target.
Department chiefs and deputy chiefs were members of the group chat on the encrypted messaging app, according to three Commission officials with knowledge of the issue. The embargo comes as the EU grapples with a series of spying allegations, with the Commission saying last week it was investigating a cyberattack on its websites.
The Commission became aware of the group chat last month and asked its members to delete it, fearing they could be targeted by hackers, two of the officials said. There is no evidence any member of the group was intercepted, and the order to stop using the chat was issued due to increasing security concerns about messaging apps in the institution, one of the officials said. (Zoya Sheftalovich, Sam Clark, and Sebastian Starcevic / Politico)
Russia is going to further clamp down on Virtual Private Networks (VPNs), which are used by millions of Russians to get around internet controls and censorship, Russia's digital minister said.
In what has been cast by diplomats as Russia's "great crackdown", the authorities have repeatedly blocked mobile internet and jammed major messenger services while giving sweeping powers to cut off mass communications.
"The task is reduce VPN usage," Digital Minister Maksut Shadayev said on state-backed messenger MAX late on Monday, adding that his ministry was trying to impose the limits with minimal impact on users.
He said decisions had been taken to restrict access to several unidentified foreign platforms without giving details.
After the 2022 invasion of Ukraine, Russia imposed the most repressive laws seen since Soviet times, ordering censorship and bolstering the influence of the Federal Security Service, the main successor to the Soviet-era KGB.
But in recent months, the state has gone much further: it blocked WhatsApp, slowed down Telegram, and has repeatedly jammed mobile internet in Moscow and other cities and regions. (Guy Faulconbridge / Reuters)
Related: The Moscow Times, TechRadar, The Independent, New York Times, The Kyiv Independent, United24Media, OC Media
Variance (fka Intrinsic), a San Francisco, CA-based company developing AI investigative agents for risk and compliance, announced it had raised $21.5 million in Series A funding.
Ten Eleven Ventures led the round, with participation from 645 Ventures, Y Combinator, Urban Innovation Fund, and Okta Ventures. (Ryan Lawler / Axios)
Related: Variance, Ventureburn, FinSMEs, Business Wire, Ycombinator, Security Week
Best Thing of the Day: AI Is Good for Pentesting
Amazon has seen a 40 percent efficiency gain by using AI tools to pentest its products before and after launch, according to security chief CJ Moses.
Worst Thing of the Day: OpenAI Secretly Pushing AI Age Verification Requirements
According to a report from the San Francisco Standard, several people involved in the California-based Parents and Kids Safe AI Coalition were blindsided to learn their efforts were secretly being funded by OpenAI.
Bonus Worst Thing of the Day: Justice for Jonathan!
News outlets, including the BBC, Daily Mail, and USA Today, falsely reported the death of a 195-year-old tortoise named Jonathan after an X account posing as Jonathan’s vet broke the news, with the imposter vet soliciting crypto donations.
Closing Thought