Leaked DarkSword iPhone spyware lowers bar for mass exploitation
FCC bans import of all new foreign-made routers, Foster City officially declares state of emergency following attack, German federal police visited Windchill and FlexPLM users in the wee hours to warn them of a severe flaw, Scioto County employees fell victim to phishing, much more


Check out my latest CSO piece that recaps the highlights from Mandiant's latest threat report released at RSAC, which found, among other things, that the median time between an initial access event and the hand-off to a secondary threat group dropped from more than eight hours in 2022 to 22 seconds in 2025.
If you rely on Metacurity to make sense of cybersecurity policy, industry developments, and security research, please consider supporting the newsletter with a paid subscription.
Metacurity is a daily infosec intelligence layer written independently of vendor marketing, PR-driven threat intelligence, and the cyber media echo chamber. Paid subscriptions make it possible to keep producing clear, straightforward analysis every day. Please consider upgrading your subscription. Thank you!
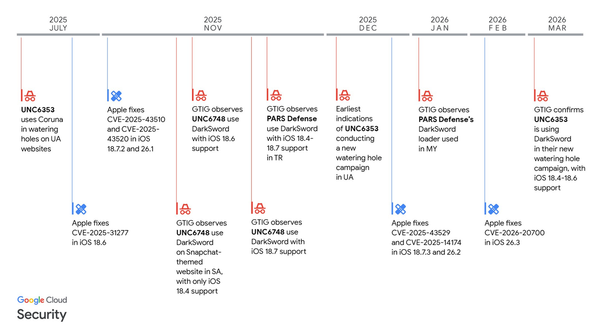
A newly leaked version of the DarkSword iPhone hacking toolkit has been published on GitHub, raising concerns among security researchers that cybercriminals could widely use the tool.
Originally identified in a targeted campaign, the updated spyware is reportedly easy to deploy and can exploit older Apple devices that have not been updated to the latest iOS 26, potentially putting hundreds of millions of iPhones and iPads at risk.
Experts say the leaked code requires little technical expertise to use, consisting largely of simple HTML and JavaScript files that can be quickly repurposed and hosted. Researchers warn that the exploit works “out of the box,” enabling attackers to extract sensitive data such as contacts, messages, call history, and stored credentials from compromised devices and transmit it to remote servers.
Apple said it has issued emergency updates for affected devices and emphasized that users running current software versions are not vulnerable, while also recommending features such as Lockdown Mode for additional protection.
The leak follows the recent discovery of another advanced toolkit, Coruna, underscoring growing concerns about the proliferation of sophisticated mobile spyware tools beyond government or intelligence use. (Lorenzo Franceschi-Bicchierai and Zack Whittaker / TechCrunch)
Related: Android Authority, Digital Trends, 9to5Mac, r/technology, r/technews, Gigazine
The US Federal Communications Commission announced a ban on the import of all new foreign-made consumer routers, citing national security concerns.
The move targets a market heavily dominated by Chinese manufacturers, which are estimated to supply at least 60% of home routers used in the United States. Existing devices will not be affected, but no new models will be allowed under the order.
The FCC said a White House-led review found that imported routers pose a “severe cybersecurity risk,” warning they could be exploited to disrupt critical infrastructure, conduct espionage, and enable intellectual property theft. Officials pointed to past cyber campaigns, including Volt and Salt Typhoon, as examples of how vulnerabilities in such devices have been leveraged by malicious actors.
The policy includes exemptions for devices cleared by the Pentagon and has drawn support from lawmakers concerned about Chinese technology in US networks. The move follows broader scrutiny of Chinese-linked tech firms, including legal action against router maker TP-Link, and mirrors earlier FCC restrictions on Chinese drones as part of a wider effort to secure critical infrastructure. (David Shepardson / Reuters)
Related: The Verge, FCC, FCC, BBC, 9to5Mac, Network World, Tom's Hardware, Gizmodo, Moneycontrol, PCMag, PCWorld, Bloomberg Law, Engadget, TechRadar, Bloomberg, Neowin, CNET, GSMArena.com, Advanced Television, CyberInsider, Tom's Guide, Tech Times, Mashable, Android Authority, ZeroHedge News, AppleInsider, XDA Developers, Digital Trends, DigiTimes, 9to5Google, Gizchina, DroneXL.co, Cord Cutters News, Cyber Daily, Telecompaper, TheVerge, Der Spiegel, Heise, r/Ubiquitir, r/technews, r/cybersecurity, r/news, r/technology, r/hardware
Foster City, CA, officials declared a state of emergency five days after a ransomware attack disrupted police and emergency systems.
The city council approved the measure 4-0, enabling access to government aid as officials continue responding to the incident. While 911 services have been restored, most municipal networks remain offline, with ongoing disruptions to email and phone systems and limited services available at City Hall.
City officials said they are working with state and federal authorities as well as independent cybersecurity specialists to investigate the breach and mitigate its impact. It remains unclear whether personal data was compromised, though residents who have interacted with the city were advised to update passwords and take precautions. (Alyce McFadden / San Francisco Chronicle)
Related: KION, SFGate, CBS News
At the behest of the Federal Criminal Police Office (BKA), officers from across Germany were dispatched to alert via phone or in-person visit companies affected by a severe vulnerability in product lifecycle management solutions Windchill and FlexPLM.
Administrators, whose weekends were disrupted, expressed their irritation, some of whom don't even use the compromised software.
The officers handed sleepy administrators a copy of the letter that manufacturer PTC had sent to all customers the previous day, containing instructions for a hotfix.
One affected employee reported: "The police were at our door at 3:30 in the morning. A production worker then informed the managing director, who in turn informed me and a colleague." He was surprised by the urgency of the action: "Our servers are only accessible internally and cannot communicate with the WAN. The number of authorized clients is also severely limited (different VLAN)." (Christopher Kunz / Heise)
Related: Heise
Scioto County officials in Ohio are investigating a potential data breach after several employees fell victim to a phishing scam, clicking on malicious email links that may have exposed county systems.
The emails appeared legitimate, allowing attackers a possible entry point into sensitive government networks.
County commissioners have approved hiring an outside law firm to conduct an independent investigation into the incident. Officials are working to determine the scope of the breach, including whether any personal or government data was accessed or compromised.
Authorities said the investigation is ongoing and have not confirmed any data exposure. (Cyn Mackley / Scioto County News)
Related: Portsmouth Daily Times, The Herald-Dispatch
Aleksei Volkov, a Russian cybercriminal identified as an initial access broker, has been sentenced to seven years in prison for assisting major cybercrime groups, including the Yanluowang ransomware group, in carrying out numerous attacks against US companies and other organizations.
Authorities said he played a key role in enabling attacks by breaching corporate systems and then providing that access to other criminals who carried out extortion operations.
Investigators found that the broker targeted multiple organizations, harvesting credentials and maintaining persistent access before selling it on cybercrime forums. His activities supported ransomware campaigns that caused significant financial damage to victims, highlighting the growing specialization within the cybercriminal ecosystem.
Officials said the case underscores the importance of disrupting access brokers, who serve as a critical link between network intrusions and ransomware deployment. (Mihir Bagwe / The Cyber Express)
Related: Justice Department, Infosecurity Magazine, IT Pro, Bleeping Computer
The State Department formally launched a new entity called the Bureau of Emerging Threats, charged with anticipating and responding to dangers posed by Iran and other US adversaries' weaponization of advanced technology.
Officials said the bureau will focus on threats from countries such as Iran, China, Russia, and North Korea, as well as foreign terrorist groups, particularly in areas like cyberattacks, space security, and critical infrastructure.
Announced as part of a broader reorganization led by Secretary of State Marco Rubio, the bureau is designed to anticipate both current and future threats tied to disruptive technologies such as AI and quantum computing. It will be led by senior official Anny Vu and structured into five divisions covering cybersecurity, critical infrastructure, disruptive technology, space security, and threat assessment.
The State Department notified Congress of the new bureau as the White House released a national AI policy framework emphasizing limited federal regulation, underscoring a broader government effort to balance innovation with security risks.
This move comes after the State Department shuttered its Bureau of Cyberspace and Digital Policy (CDP) and closed its Global Engagement Center (GEC), which tracked foreign disinformation last April. (Shannon K. Kingston / ABC News)
Related: PYMNTS, Defense24, Florida's Voice, Jewish News Service
South African insurance and financial services firm Liberty disclosed a data breach involving unauthorized access to parts of its systems, exposing customer personal information.
The company said it acted quickly to contain the incident and emphasized that its services, policies, and investments remain fully operational and unaffected. Affected data may include names and ID numbers, according to communications with clients.
Liberty said it is conducting a full investigation with the support of external experts and is notifying impacted customers in line with regulatory requirements. Under South Africa’s Protection of Personal Information Act, companies must promptly inform both regulators and affected individuals of breaches, providing details on potential risks and mitigation efforts. The company has apologized for the incident and said it is complying with all legal obligations.
The firm is urging customers to remain vigilant against potential fraud, advising them to avoid suspicious communications, monitor financial accounts, and use strong security practices such as unique passwords and multi-factor authentication. (Admire Moyo / IT Web)
Related: My Broadband
Semiconductor testing company Trio-Tech International warned regulators in an SEC filing that its subsidiary in Singapore suffered a ransomware attack earlier this month.
The company said the cyberattack was discovered on March 11 and led to the encryption of files within the subsidiary’s network.
“At that time, management determined that the incident was not material,” the company said. “On March 18, 2026, the incident escalated and resulted in the unauthorized disclosure of certain Company data. Following this development, management concluded that the incident may constitute a material cybersecurity event."
Trio-Tech International took its network offline and hired cybersecurity experts to deal with the attack after notifying law enforcement in Singapore. The company is still trying to restore systems.
It is unclear what data was taken, but the company said the subsidiary is “in the process of notifying affected parties.” (Jonathan Greig / The Record)
Related: SEC, Asian Business Review
Last week, a digital intrusion was discovered at the Dutch Ministry of Finance in 'systems for several primary processes' within the department.
Access to these systems was blocked on Monday, meaning that some employees can no longer log in.
A spokesperson declined to say which systems are involved. However, she did state that the government can continue to spend and receive funds as usual. "Implementing organizations such as the Tax and Customs Administration are not affected," the ministry announced. (RTL News)
Related: Ministry of Finance, NL Times, UA.news, RBC-Ukraine, Techzine, Bleeping Computer
AI-generated images and videos depicting child sexual abuse have surged to unprecedented levels, according to new findings from the Internet Watch Foundation (IWF).
The watchdog reported a 260-fold increase in AI-generated abuse videos over the past year, alongside a broader rise in extreme content. In 2025, analysts identified more than 8,000 realistic depictions, reflecting how advances in generative AI are enabling offenders to produce large volumes of highly convincing material with minimal technical skill.
The report found that AI-generated content is often more severe than traditional abuse material, with 65% of analyzed AI-generated videos classified in the most serious legal category under UK law, compared with 43% of non-AI videos. Analysts also observed offenders on dark web forums discussing ways to use real footage of children as source material for AI manipulation and competing to create increasingly extreme scenarios, highlighting how the technology is amplifying both scale and brutality.
The findings are intensifying pressure on governments and regulators to close legal gaps and impose stricter obligations on AI companies. Recent controversies, including the generation of illegal content by AI chatbots, have prompted calls for “safety-by-design” safeguards and expanded oversight. (Madhumita Murgia / Financial Times)
Related: Internet Watch Foundation, Euronews, The Guardian, The News International, Rappler, LBC
Three American men were sentenced for crimes they committed in furtherance of North Korea’s vast scheme to get operatives hired at US companies, the Justice Department said.
The trio — Audricus Phagnasay, 25, Jason Salazar, 30, and Alexander Paul Travis, 35 — pleaded guilty in November to wire fraud conspiracy for providing US identities to remote North Korean IT workers.
They hosted US company-provided laptops at their homes and installed remote-access software so North Korean operatives could appear to be working in the country. The group also helped remote IT workers pass employer vetting and, in the case of Travis and Salazar, took drug tests on behalf of the North Koreans, prosecutors said.
Travis, an active-duty member of the US Army at the time, received about $51,000 from the scheme. He was sentenced to one year in prison and ordered to forfeit about $193,000.
Phagnasay and Salazar each pocketed about $3,500 and $4,500, respectively, and were both sentenced to three years of probation and a $2,000 fine. A federal court ordered Salazar to forfeit about $410,000 and ordered Phagnasay to forfeit nearly $682,000.
“These men practically gave the keys to the online kingdom to likely North Korean overseas technology workers seeking to raise illicit revenue for the North Korean government — all in return for what to them seemed like easy money,” Margaret Heap, US attorney for the Southern District of Georgia, said in a statement. (Matt Kapko / CyberScoop)
Related: Plea agreement, GovInfoSecurity, WRDW, NK News, The Record
Researchers from Aikido report that the TeamPCP hacking group is targeting Kubernetes clusters with a new campaign that includes a destructive payload aimed specifically at systems configured for Iran.
The activity builds on earlier operations linked to the group, including the CanisterWorm campaign and a supply-chain attack on the Trivy vulnerability scanner, and reuses the same command-and-control infrastructure, backdoor code, and deployment techniques.
The researchers found that the malware checks systems for Iranian locale and timezone settings and, if matched, deploys a “kamikaze” payload that deletes all files on the host and forces a reboot. In Kubernetes environments, this is executed through a malicious DaemonSet using privileged containers with access to the host filesystem.
On non-Iranian systems, the malware instead installs a persistent Python backdoor, enabling continued access rather than destruction.
Aikido also observed newer variants shifting from Kubernetes-based lateral movement to SSH-based propagation, harvesting credentials from authentication logs and private keys to spread across networks.
The researchers highlighted indicators of compromise, including suspicious outbound SSH connections, access to unsecured Docker APIs, and privileged container activity, underscoring the campaign’s evolving tactics and its blend of espionage and targeted sabotage. (Bill Toulas / Bleeping Computer)
Related: Aikido, HackRead, Cyber Press, ITNews, KrebsonSecurity
CrowdStrike reports that the Tycoon2FA phishing-as-a-service platform has rapidly returned to normal operations following a law enforcement disruption on March 4.
The action, led by Microsoft and coordinated with Europol, seized 330 domains tied to the platform’s infrastructure and briefly reduced activity to about 25% of typical levels. Within days, however, phishing volumes rebounded to pre-disruption levels.
Tycoon2FA is a significant phishing operation targeting Microsoft 365 and Gmail accounts using adversary-in-the-middle techniques to bypass two-factor authentication. The platform has been linked to large-scale campaigns generating tens of millions of phishing emails per month and supporting activities such as business email compromise, account takeovers, and email thread hijacking.
After the takedown, operators quickly restored capabilities using similar tactics, including new phishing domains, malicious links, and abuse of legitimate platforms. CrowdStrike noted that some original infrastructure remained active, indicating the disruption was incomplete, and warned that without arrests or physical seizures, such services can rapidly recover as long as demand for phishing tools persists. (Bill Toulas / Bleeping Computer)
Related: CrowdStrike, Security Week
Researchers at Huntress say a phishing campaign tied to the AI cloud-hosting platform Railway has compromised Microsoft cloud accounts across hundreds of organizations in recent weeks.
The activity, attributed to a relatively small threat actor, escalated sharply in early March, with researchers observing a surge in attacks and dozens of successful compromises per day. The campaign has affected a wide range of sectors, including government, healthcare, finance, and manufacturing.
Huntress found the attackers used AI-generated phishing lures at scale, creating highly varied emails, QR codes, and file-sharing links that helped them evade traditional detection systems. The campaign exploited Microsoft’s device authentication flow, allowing attackers to obtain valid OAuth tokens without requiring passwords or multi-factor authentication, and maintain access to accounts for extended periods.
The researchers believe the attackers leveraged Railway’s platform to rapidly deploy phishing infrastructure, using compromised domains and bespoke lures to bypass security controls.
Despite mitigation steps by Railway, the campaign has persisted, underscoring how generative AI is enabling less sophisticated actors to operate with the speed and effectiveness of more advanced cyber threat groups. (Derek B. Johnson / CyberScoop)
Related: Huntress
Mazda Motor Corporation (Mazda) announced that information belonging to its employees and business partners had been exposed in a security incident detected last December.
The company said the attackers exploited a vulnerability in a system related to warehouse management for parts procured from Thailand. The system did not contain any customer data. Also, the breach is limited to 692 records.
“Mazda Motor Corporation has identified traces of unauthorized external access to a management system used for warehouse operations related to parts procured from Thailand,” reads Mazda’s announcement.
“Following this discovery, the Company promptly reported the matter to the Personal Information Protection Commission – an external bureau of the Japanese Cabinet Office – and implemented appropriate security measures and conducted an investigation in cooperation with an external specialist organization.” (Bill Toulas / Bleeping Computer)
Related: Mazda, Cyber Security News
The Department of Energy’s Office of Cybersecurity, Energy Security, and Emergency Response (CESER) has released a new strategic plan aimed at strengthening the security and resilience of the US energy sector against growing cyber and physical threats.
The plan emphasizes the need to protect critical infrastructure as adversaries increasingly target energy systems and calls for closer coordination between government and industry.
The strategy outlines three main priorities: developing practical security technologies in partnership with utilities, hardening energy infrastructure against cyber and physical risks, and improving response and recovery capabilities following disruptions. CESER plans to support the creation of tools and systems that can help energy operators detect threats earlier and restore operations more quickly after incidents.
Officials said the plan is designed to address both current and emerging risks, including cyberattacks, supply chain vulnerabilities, and the misuse of advanced technologies. By enhancing collaboration, resilience, and preparedness, CESER aims to ensure the reliability of the nation’s energy systems and reduce the potential impact of large-scale disruptions. (Miles Jamison / ExecutiveGov)
Related: Energy Department, Bank Info Security
The following is a quick round-up of noteworthy news reports coming out of this year's RSA conference:
- Google launched a new threat disruption unit within its threat intelligence operations aimed at actively interfering with cybercriminal and nation-state hacking activity. (David DiMolfetta / NextGov/FCW)
- Former NSA cyber boss Rob Joyce said the now-infamous Anthropic report about Chinese cyberspies abusing Claude AI to automate cyberattacks was a Rorschach test for the infosec community, with half of the industry viewing it as a meaningless distraction and half saying it offered significant insight into offensive operations. (Jessica Lyons / The Register)
- A panel of experts at RSA that lacked any government officials (who are boycotting the event due to its leadership by former CISA director Jen Easterly) said that public-private partnerships are essential to disrupting China's Typhoon threat groups. (Jessica Lyons / The Register)
- A panel of experts at RSA debated whether humans should remain in the loop when it comes to AI security, with the central arguments against this notion being that human-led defenses are often too slow to stop things like agent-led cyberattacks. (Alexander Culafi / Dark Reading)
- Even with no federal government representatives at RSA, representatives from a major cybersecurity vendor, consulting, venture capital, and law firm were quick to defend and evangelize the administration’s two-week-old cyber strategy. (Matt Kapko / CyberScoop)
Above Security (Above), the AI-native agentic managed insider threat platform, emerged from stealth and announced $50 million in funding.
Ballistic Ventures, Merlin Ventures, and Norwest led the funding, with participation from Jump Capital and QPV Ventures. (Meir Orbach / Calcalist)
Related: The SaaS News, Channel E2E, Globes, PR Newswire, Ynet News
Best Thing of the Day: Not That He Will Really Care, But Still
A federal judge in Washington will allow a lawsuit to go forward that accuses billionaire Elon Musk of unconstitutionally exercising executive power during his time in the Trump administration last year as a presidential adviser.
Bonus Best Thing of the Day: Steps Away from Penn Station
After last holding a HOPE conference in Manhattan in 2018, the offbeat and essential security event will return to the New Yorker hotel in Manhattan in August.
Worst Thing of the Day: Your Zoom Call May Be Less Boring Than You Think
WebinarTV, a company that bills itself as “a search engine for the best webinars,” is secretly scanning the internet for Zoom meeting links, recording the calls, and turning them into AI-generated podcasts for profit.
Closing Thought