Medical device giant Stryker hit by wiper attack, Iranian hacktivist takes credit
Poland foiled a cyberattack on its nuclear research center that ostensibly originated in Iran, Cyberattackers defaced ad signs in Tel Aviv train station, Albania's parliament hit by cyberattack, Apple issues updates to address Coruna exploit, US charges former ransomware negotiator, much more


Metacurity is the only daily cybersecurity newsletter that is written outside the usual cyber press echo chamber and is a straightforward and accurate alternative to vendor-driven content and PR-flavored threat intelligence.
Please consider supporting my work on Metacurity by upgrading your subscription. Thank you.
Michigan-based Stryker, a leading US medical device maker, was hit early Tuesday by a destructive cyberattack that knocked out systems globally, with workers in the US, Australia, India, and Ireland reporting widespread outages.
Cork, where Stryker operates six manufacturing and R&D facilities and employs over 5,000 people — making it the company's largest hub outside the US — was among the hardest hit.
An Iranian hacktivist group known as Handala claimed responsibility, defacing internal login and admin pages with its logo and sending emails to company executives, taking ownership of the attack. The group said the assault was partly in retaliation for the US bombing of a girls' school in Iran during the opening of a US-Israeli assault on the country. Handala also claimed responsibility Tuesday for hacking Israel's Academy of the Hebrew Language website, suggesting a coordinated campaign.
The attack was a wiper attack in which hackers pushed an operating system reset to computers and phones connected to Stryker's network, wiping servers clean and leaving employees unable to log into accounts. Workers on Reddit reported that colleagues' phones were also wiped, and those who used their phones for two-factor authentication lost access to personal accounts as well.
"The entire company is at a complete stop," one employee wrote. Handala claimed to have struck more than 200,000 servers, systems, and devices, and to have stolen 50 terabytes of data. Iran has a long history with such attacks, most notably the 2012 Shamoon assault that erased data from more than 30,000 systems at Saudi Aramco.
Stryker confirmed it was experiencing "a global network disruption affecting the Windows environment" and told staff it was "a severe, global disruption."
The 56,000-employee company manufactures surgical equipment, defibrillators, hospital beds, and joint-replacement systems, and holds a $450 million US Defense Logistics Agency contract to supply medical and patient monitoring equipment to the military — making it among the most strategically sensitive corporate targets yet struck in an escalating Iranian hacktivist campaign. (Sara Rountree / Cork Beo and Kim Zetter / Zero Day)
Related: Stryker, Wall Street Journal, Mirror, Bleeping Computer, TechCrunch, Firstpost, Irish Mirror, ZERO DAY, Krebs on Security, Bloomberg, BleepingComputer, Irish Examiner, Reuters, Gizmodo, The Register, Bloomberg, PCMag, Cybersecurity Dive, CNN, Bloomberg, UPI, Hackread, Washington Times, Mashable, Associated Press, iTnews, Security Affairs, Bloomberg Law, DataBreaches.Net, The Record, TechCrunch, BankInfoSecurity.com, The Hill, Newsweek, Nextgov/FCW, RTÉ, WPDE-TV, Fast Company, Financial Express, r/technology, Hindustan Times, Times of India, IB Times, Business Standard, USA Today, UNN, HackRead, UPI, The Detroit News, Security Magazine, Security Week, Silicon Republic, The Verge, The Guardian, The Independent
Poland has foiled a cyberattack on its nuclear research centre and is examining signs that Iran may be behind it, the government said, cautioning the indicators might be a deliberate misdirection to hide the attackers’ true location.
Poland says it has been the target of numerous cyberattacks since Russia's full-scale invasion of Ukraine in 2022. Moscow has repeatedly denied involvement.
Minister for Digital Affairs Krzysztof Gawkowski told private broadcaster TVN24+ that the attack on Poland's National Centre for Nuclear Research had taken place "in the past few days."
"The attack may not have been on a huge scale, but there was an attempt to break through the security that was stopped. Appropriate services are already working", Gawkowski said, adding that the centre was safe.
"The first identifications of the entry vectors, i.e., those places from which (the centre) was attacked, are related to Iran," he said. "When there is final information and the services will check it, we will verify it, but there are many indications that it took place on the territory of Iran." (Anna Wlodarczak-Semczuk / Reuters)
Related: Mezha, Politico EU
A cyberattack targeted advertising signs in the passenger halls at Herzliya Station and Shalom Train Station in Tel Aviv.
It is estimated that Iranian hackers took control of the signs and posted messages claiming that the stations were expected to be attacked by Iranian missiles and instructing the public to evacuate immediately.
Israel Railways clarified that these signs are not connected to the railway infrastructure and are located on platforms as part of a private provider’s advertising and information system. Shortly after the incident, the screens were taken offline. (Hofit Cohen Azulay / Calcalist)
Related: Jewish News Service
Albania’s parliament said that it had been targeted by a “sophisticated” cyberattack aimed at deleting data and compromising several internal systems.
In a statement shared with local media, parliament said its main systems and official website remained operational but confirmed that internal email services used by the parliamentary administration had been temporarily suspended. The disruption affected both incoming and outgoing communications.
Local media reported that parliamentary staff and lawmakers were unable to access computers and email systems for several hours following the attack.
Authorities have not publicly attributed the incident, but earlier this week, a hacker group known as Homeland Justice claimed responsibility, saying it had obtained internal communications involving Albanian lawmakers. The group also posted screenshots of what it said were leaked documents on its Telegram channel.
Albanian authorities have not publicly verified the hackers’ claims, and the country’s cybersecurity agencies are still investigating the incident.
Security researchers and Western officials have previously linked Homeland Justice to Iran’s Islamic Revolutionary Guard Corps (IRGC). The group has claimed responsibility for a series of cyberattacks against Albanian targets in recent years, including operations against the country’s parliament, national airline, telecommunications firms, and national statistics agency. (Daryna Antoniuk / The Record)
Related: Balkanweb, Euronews Albania
Apple has released security updates for older iPhones and iPads that address the recently disclosed “Coruna” exploit, extending protections to devices that cannot run the latest versions of its operating systems.
The updates — iOS 16.7.15, iOS 15.8.7, iPadOS 16.7.15, and iPadOS 15.8.7 — were initially described only as containing “important security fixes,” but Apple later confirmed they specifically mitigate vulnerabilities tied to the Coruna attack chain.
The Coruna exploit, revealed by researchers at Google and security firm iVerify, links together multiple vulnerabilities to compromise iPhones running older software. Researchers said the campaign involves five exploit chains and at least 23 vulnerabilities affecting devices running versions of iOS from 13 through 17.2.1. The flaws include weaknesses in the kernel and in Apple’s WebKit browser engine that could allow malicious apps or crafted web content to execute arbitrary code or corrupt memory on targeted devices.
Apple said the new patches bring fixes previously introduced in newer versions of iOS to older hardware that can no longer upgrade to the latest operating system. Affected devices include models such as the iPhone 6s, iPhone 7, first-generation iPhone SE, iPhone 8, iPhone X, and several older iPads. Security experts say users of legacy devices should install the updates promptly, as standalone patches for older systems typically address serious or actively exploited vulnerabilities. (Marcus Mendes / 9to5Mac)
Related: Apple Support, Apple Support, MacRumors, OS X Daily, Digit, Neowin, AppleInsider, iClarified, iPhone in Canada, Hacker News (ycombinator), r/Apple
US prosecutors have charged a former ransomware negotiator, Angelo Martino, at incident response firm DigitalMint, for allegedly collaborating with the BlackCat (ALPHV) ransomware group while handling negotiations for victims.
Martino was charged with one count of conspiracy to interfere with interstate commerce by extortion and surrendered to US Marshals on March 10, according to newly unsealed court documents.
Authorities allege that while working at DigitalMint, Martino shared confidential information about active ransomware negotiations with BlackCat operators. Between April 2023 and April 2025, prosecutors say he also participated directly in ransomware attacks with accomplices Kevin Tyler Martin, another former DigitalMint employee, and Ryan Goldberg, a former incident response manager at Sygnia.
Martino had previously been identified only as “Co-Conspirator 1” in an October 2025 indictment charging Martin and Goldberg, both of whom have pleaded guilty and are scheduled to be sentenced in April. Prosecutors say the defendants operated as BlackCat affiliates, threatening to leak stolen data from victim networks and paying the ransomware group a 20 percent share of collected ransoms in exchange for access to its malware and extortion infrastructure.
At least five US. organizations were targeted, including a Tampa-based medical device manufacturer that paid a $1.27 million ransom, according to prosecutors. DigitalMint said it terminated the employees after discovering the conduct and has cooperated with law enforcement. (Sergiu Gatlan / Bleeping Computer)
Related: CyberScoop
Tire maker Michelin has confirmed it was impacted by a large-scale cybercrime campaign targeting organizations running Oracle’s E-Business Suite (EBS), after attackers exploited zero-day vulnerabilities in the enterprise software.
The Cl0p ransomware and extortion group has claimed responsibility for the campaign, which has affected more than 100 organizations listed on its leak site.
Michelin said its internal investigation determined that attackers exploited an Oracle EBS zero-day vulnerability to gain access to some company files. The company said it took corrective action quickly and that the incident has been resolved. According to Michelin, the breach involved only a small, localized volume of data and did not expose sensitive or technical IT information, and the company said its global systems were not disrupted.
Despite Michelin’s statement, the attackers have published more than 315GB of files they claim were stolen from the company. A review of the leaked archive structure suggests that at least some of the data originated from an Oracle EBS environment. Other organizations have also confirmed being targeted in the campaign, including Madison Square Garden, which acknowledged the incident after hackers leaked more than 210GB of alleged company data. (Eduard Kovacs / Security Week)
Bonk.fun, a community-driven Solana token issuance platform backed by Raydium and the BONK, warned users to avoid its website after hackers hijacked a team account and installed a crypto drainer on the domain.
The operator, known as Tom, said only users who signed a fake terms-of-service message on the compromised site after the breach were affected.
Tom said the incident was detected quickly, with losses not yet disclosed. (Omkar Godbole / CoinDesk)
Related: crypto.news, The Block, Decrypt, BeInCrypto, Crypto Briefing, Invezz, Reddit-hacking
Recently hacked Dutch telco Odido forwarded for years sensitive data from customers' routers to the American AI company Lifemote without clearly disclosing this in its privacy statement, the Telegraaf reports.
According to the newspaper, the telecom company seems to have stopped this practice after the newspaper’s questions about it.
Odido routers forwarded the names and MAC addresses of all devices on a home network, along with the names of those devices, like “Jan’s iPhone,” or “Apple TV in the living room.” The routers also shared the names and MAC addresses of surrounding Wi-Fi networks and hotspots.
MAC stands for “media access control.” The MAC address is the unique identification number of every device you connect to the internet. The Dutch Data Protection Authority considers MAC addresses to be personal data.
Ethical hacker Spoke Mellema told the Telegraaf that this data is extremely sensitive because it can be used to track where devices, and therefore the people attached to them, are. The data can be used for extremely targeted advertising, for example.
Odido did not inform customers that it was sharing their personal data. Its privacy policy only states that Odido collects the MAC addresses and device data from its modems, not that the company then forwards this data to an artificial intelligence company in the United States.
The Dutch internet service provider would not tell the Telegraaf why it shared customers’ personal data with Lifemote, only referring the newspaper to its privacy statement. The company did say that it has updated the router software and stopped sharing data with Lifemote. (NL Times)
Related: Telegraaf
Some customers using Bank of Scotland, Lloyds, and Halifax apps were able to see other users' transactions on their accounts.
Lloyds Banking Group customers reported being able to view charges and payments from other sources on Thursday morning.
A Lloyds Banking Group spokesperson apologised for the issue and said the incident had been quickly resolved.
One woman told BBC Scotland News she was able to see the accounts of six different users on the Bank of Scotland app, including some National Insurance numbers, over a 20-minute period.
Those included transactions from a pub in Newcastle, 154 miles from her home in Kirkcaldy, Fife, fees for using one card abroad, and wage payments from a company based in England. The 55-year-old also reported being able to view benefits payments from the Department of Work and Pensions (DWP), which uses the National Insurance numbers of recipients as a payment reference. (BBC News)
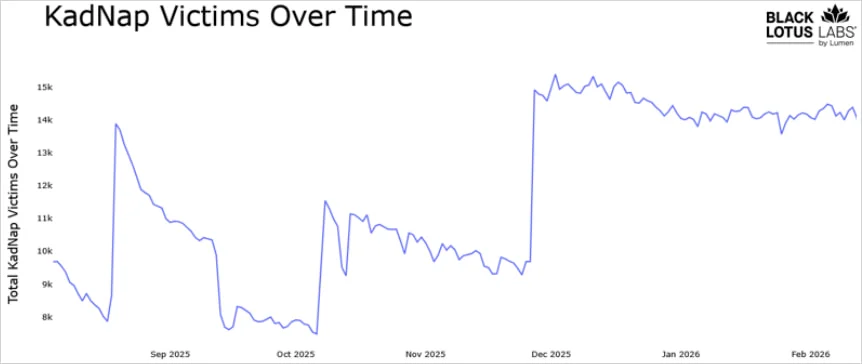
Researchers at Black Lotus Labs discovered a new botnet malware called KadNap that is targeting ASUS routers and other edge networking devices to turn them into proxies for malicious traffic.
Since August 2025, KadNap has grown to 14,000 devices that are part of a peer-to-peer network and connect to the command-and-control (C2) infrastructure through a custom version of the Kademlia Distributed Hash Table (DHT) protocol.
Nearly half of the KadNap network is connected to C2 infrastructure dedicated to ASUS-based bots, and the rest communicate with two separate control servers.
Most infected devices are located in the United States, which accounts for 60% of the total, followed by significant percentages in Taiwan, Hong Kong, and Russia.
Black Lotus Labs researchers say that the KadNap botnet is linked to the Doppelganger proxy service, believed to be a rebrand of the Faceless service, previously associated with the TheMoon malware botnet, which also targeted ASUS routers. (Bill Toulas / Bleeping Computer)
Related: Black Lotus Labs, Security Affairs, Technology.org, SC Media
ELECQ, maker of smart electric vehicle (EV) chargers, is warning customers that their personal details may have been stolen in a ransomware attack that encrypted and copied user data from its cloud systems.
In a notice sent to customers, the EV charging outfit said that it detected "unusual activity" on its AWS cloud platform on March 7 and quickly discovered that attackers had launched a ransomware attack against parts of its infrastructure.
According to the message, some databases were both encrypted and copied during the intrusion, meaning that the crooks likely walked off with user information before the company pulled the plug.
ELECQ, a Chinese outfit that builds smart EV charging gear for homes and businesses, says that the compromised data is limited to fairly standard account details: names, email addresses, phone numbers, and home addresses.
It insists no financial data, such as payment records or credit card information, was involved, and stressed that the attack did not affect the charging devices themselves, which it says remain "fully secure and operational." (Carly Page / The Register)
Related: Fleetworld, SC Media
Bombadil Systems security researcher Chris Aziz developed a new technique dubbed “Zombie ZIP” that helps conceal payloads in compressed files specially created to avoid detection from security solutions such as antivirus and endpoint detection and response (EDR) products.
Trying to extract the files with standard utilities like WinRAR or 7-Zip results in errors or corrupted data. The technique works by manipulating ZIP headers to trick parsing engines into treating compressed data as uncompressed.
Instead of flagging the archive as potentially dangerous, security tools trust the header and scan the file as if it were a copy of the original in a ZIP container.
Aziz found that it works against 50 of the 51 AV engines on VirusTotal.
The CERT Coordination Center (CERT/CC) published a bulletin to warn about “Zombie ZIP” and raise awareness of the risks posed by malformed archive files.
While a malformed header may trick security solutions, the agency says that some extraction tools are still able to correctly decompress the ZIP archive.
The CVE-2026-0866 identifier has been assigned for the security issue, which the agency says is similar to a vulnerability disclosed more than two decades ago, CVE-2004-0935, affecting an early version of the ESET antivirus product. (Bill Toulas / Bleeping Computer)
Related: Bombadil Systems, SANS Internet Storm Center, KB Cert
Bell Ambulance, a prominent ambulance service in Milwaukee, WI, confirmed that hackers targeted their systems last year and stole sensitive information on more than 235,000 people.
Bell Ambulance filed breach notifications in Maine this week, confirming that 237,830 people had information impacted by a data breach discovered in February 2025.
The company said Social Security numbers, driver’s license numbers, financial accounts, medical information, and health insurance information were stolen during the cyberattack.
According to letters sent to victims, Bell Ambulance became aware of the attack on February 13, 2025, and hired cybersecurity experts to assist with the recovery effort. The company began notifying some who were affected in April 2025, but more victims were discovered throughout the fall.
The company has stations across Milwaukee, Wauwatosa, Waukesha, Racine, Mount Pleasant, Kenosha, and other cities across Wisconsin. There are more than 750 employees who handle about 140,000 ambulance calls each year.
The attack on Bell Ambulance was claimed at the time by the Medusa ransomware gang, which demanded a $400,000 ransom in exchange for the 219 GB of data that was stolen.
One month after the Bell Ambulance incident, the FBI and several US law enforcement agencies released an urgent advisory about the ransomware gang’s attacks on critical infrastructure organizations across the US.
The group targeted governments and healthcare facilities in Minnesota, Illinois, and Texas, as well as the car racing league, NASCAR. (Jonathan Greig / The Record)
Related: Security Affairs, The HIPAA Journal, Security Week
Researchers at Aryaka report that an ongoing campaign, probably originating from a Russian-speaking threat actor, uses social engineering to trick victims into downloading an ISO file from cloud storage services such as Dropbox.
Once mounted, the ISO file seems to be a legitimate part of the system and can be directly accessed by the victim. Opening a file within it will trigger a chain that downloads malware, including a module Aryaka has dubbed BlackSanta.
This campaign targets hiring because HR is accustomed to, and routinely opens, attachments – an apparent resume found in the ISO appears to be legitimate and already on site.
Aryaka has no proof of how the victim is persuaded to download the malicious ISO file, but assumes spear phishing. If the spear phishing target is in HR, that person would be unsurprised to find what appears to be an expected resume within the mounted ISO file – and would be more likely to open it. (Kevin Townsend / Security Week)
Related: Aryaka, CSO Online, Infosecurity Magazine, SC Media
Israeli cyber company Onyx Security, which develops a security and control platform for AI agents in enterprises, has raised $35 million in a Series A funding round.
Conviction and Cyberstarts funded the round. (Meir Orbach / Calcalist)
Related: Techzine, Citybiz, Pulse 2.0
Milan-based Cleafy, a cybersecurity company focused on the banking sector, has raised €12 million (around $13.9 million) in a Series B funding round.
United Ventures and eCAPITAL led the round. (Tamara Djurickovic / TechEU)
Related: Cleafy, The Next Web
Bold Security today emerged from stealth and announced a $40 million funding round.
Bessemer Venture Partners, Picture Capital, and Red Dot Capital Partners. (Newswire)
Deepfake detection company the GmbH (formerly Neuraforge) has closed a €1.7 million (around $1.96) pre-seed funding round.
Vanagon Ventures led the round with participation from Bayern Kapital and a group of additional venture capital firms and business angels. (Tamara Djurickovic / TechEU)
Best Thing of the Day: The EU Knows How to Scrutinize Big Tech
Big Tech’s power across the full chain of AI technologies is under scrutiny for possible competition distortions, according to the European Union’s antitrust chief.
Worst Thing of the Day: A Small Price to Pay for Seriously Bad Security
South Korea's Personal Information Protection Commission fined Lotte Card $6.8 million after an investigation revealed that Lotte Card violated regulations by storing resident registration numbers and other personal data in plain text within logs related to online payments and failed to implement adequate encryption measures for log files.
Closing Thought