Microsoft bets $10 billion on Japan’s AI buildout and cyber defenses
EU pins EC attack on TeamPCP, Iowa AG sues UnitedHealth over 2024 attack, Residential proxies pose problems for IP reputation systems, Him & Hers report Feb. data breach, TA416 refocuses efforts back to Europe, Former engineer admits to hacking employer in $750k extortion bid, much more


Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
Microsoft plans to invest $10 billion in Japan over the next four years to develop artificial-intelligence infrastructure with partners and strengthen cybersecurity initiatives.
The US technology giant said that the investment plan is aimed at helping advance Prime Minister Sanae Takaichi’s goal of improving the nation’s economic security and promoting growth investments in advanced technologies.
Microsoft said it would team up with internet services providers SoftBank and Sakura Internet to consider jointly developing AI services to support the development of domestic large language models and other applications. The companies aim to create platforms that compute and store data in Japan, while allowing clients to access the platforms through Microsoft’s Azure cloud services.
The UA company said it would strengthen a tie-up with the country’s cybersecurity office and help the government and businesses detect cyberattacks early or preempt them. Microsoft also said it would help train one million engineers and developers by 2030 in cooperation with Japanese companies.
The announcement came just days after Microsoft disclosed investment plans for Singapore and Thailand. (Kosaku Narioka / Wall Street Journal)
Related: Microsoft, CNBC, Barron's, Reuters, Dataconomy, Bloomberg, Tech Wire Asia, The Japan Times
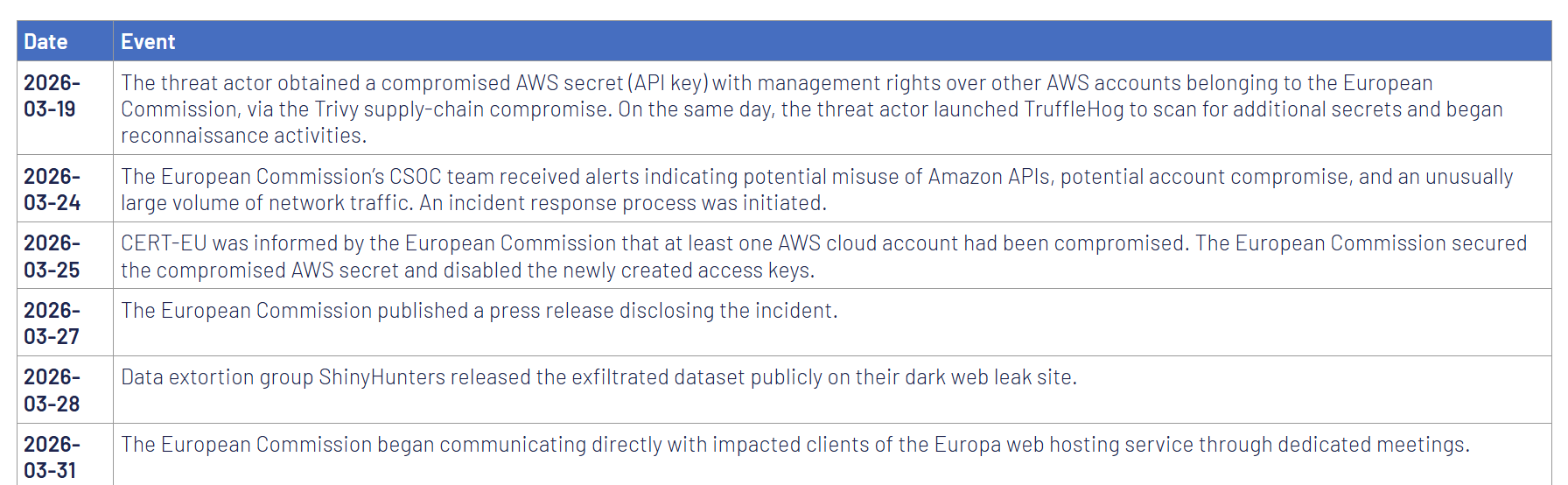
The European Union's Cybersecurity Service (CERT-EU) has attributed the European Commission cloud hack to the TeamPCP threat group, saying the resulting breach exposed the data of at least 29 other Union entities.
The European Commission publicly disclosed the incident on March 27. Two days earlier, the Commission notified CERT-EU of the hack, saying that its Cybersecurity Operations Center was not alerted to API misuse, potential account compromise, or any abnormal network traffic until March 24, five days after the initial intrusion.
On March 10, TeamPCP used a compromised Amazon Web Services API key with management rights over other European Commission AWS accounts (stolen in the Trivy supply-chain attack) to breach the Commission's Amazon cloud environment.
In the next stage of the attack, they used TruffleHog (a tool for scanning and validating cloud credentials) to search for additional secrets, then attached a newly created access key to an existing user to evade detection before conducting further reconnaissance and stealing data.
TeamPCP has been linked to supply-chain attacks targeting multiple other developer code platforms, such as GitHub, PyPi, NPM, and Docker.
The cybercrime gang has also compromised the LiteLLM PyPI package in an attack that impacted tens of thousands of devices using its "TeamPCP Cloud Stealer" information-stealing malware.
On March 28, data extortion group ShinyHunters published the stolen dataset on their dark web leak site as a 90GB archive of documents (approximately 340GB uncompressed), containing names, email addresses, and email content.
CERT-EU's analysis confirmed that the threat actors have stolen tens of thousands of files containing personal information, usernames, email addresses, and email content, and that the resulting data breach potentially affects 42 internal European Commission clients and at least 29 other Union entities using the europa.eu web hosting service. (Sergiu Gatlan / Bleeping Computer)
Related: CERT-EU, Help Net Security, Cyber Insider, Cyber Security News
Iowa State Attorney General Brenna Bird filed a lawsuit against UnitedHealth Group seeking financial damages, civil penalties, and improvements to the company's data security practices for alleged violations of state and federal laws stemming from the 2024 ransomware attack and mega-breach of its Change Healthcare unit.
Bird filed the lawsuit Tuesday in District Court for Polk County against UHG and its Optum and Change Healthcare business units. Optum acquired Change Healthcare, a healthcare IT services firm, in 2022 for $13 billion. Two years later, a ransomware attack disrupted Change Healthcare's operation for months, interrupted billing and other key services for thousands of providers, and compromised the data of nearly 193 million people across the United States, including 2.2 million Iowans.
Bird alleged violations of Iowa's Consumer Fraud Act and Personal Information Security Breach Protection Act, as well as federal laws such as HIPAA, delayed breach notification, and an array of other claims stemming from Change Healthcare's February 2024 cyberattack. (Marianne Kolbasuk McGee / GovInfoSecurity)
Related: Iowa Attorney General, Iowa Attorney General, The HIPAA Journal
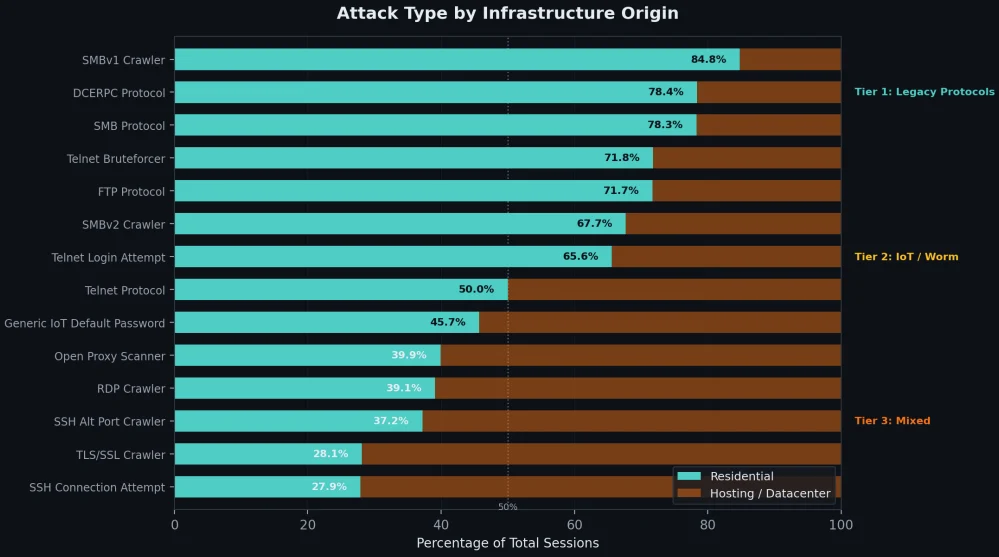
Researchers at Grey Noise warn that residential proxies used to route malicious traffic are a big problem for IP reputation systems, as there is no clear distinction between attackers and legitimate users.
This occurs because residential proxies are too short-lived, uninvolved, or systematically rotated, preventing defense systems from cataloging them in time.
GreyNoise determined this after examining a massive dataset of 4 billion malicious sessions targeting the edge over a three-month period, and also data from IPInfo.io.
Roughly 39% of those sessions appear to originate from home networks, most certainly part of residential proxies, but 78% of them are invisible to reputation feeds.
According to the company, most residential IPs are used once or twice, and then vanish, with attackers rotating them with others, keeping the pace at a level that reputation systems will not flag them.
About 89.7% of residential IPs are active in malicious operations for under a month, with only 8.7% lasting 2 months, and 1.6% persisting for 3 months.
Those that are kept alive for longer seem to carry a specialization according to the researchers, being SSH-focused and using Linux TCP stacks. (Bill Toulas / Bleeping Computer)
Related: Grey Noise, Wall Street Journal
Hims & Hers, the telehealth company that sells weight-loss drugs and sexual health prescriptions, said in a data breach notice filed with the California attorney general’s office that hackers stole data about user requests sent to the company’s customer support team.
The company said hackers broke into its third-party ticketing system between February 4 and February 7 and stole reams of support tickets, which contained personal information submitted by customers.
Although the company says customer medical records were not affected by the breach, the nature of customer support systems means that the data may contain sensitive information about a person’s account, personal information, and healthcare. (Zack Whittaker / TechCrunch)
Related: California Attorney General
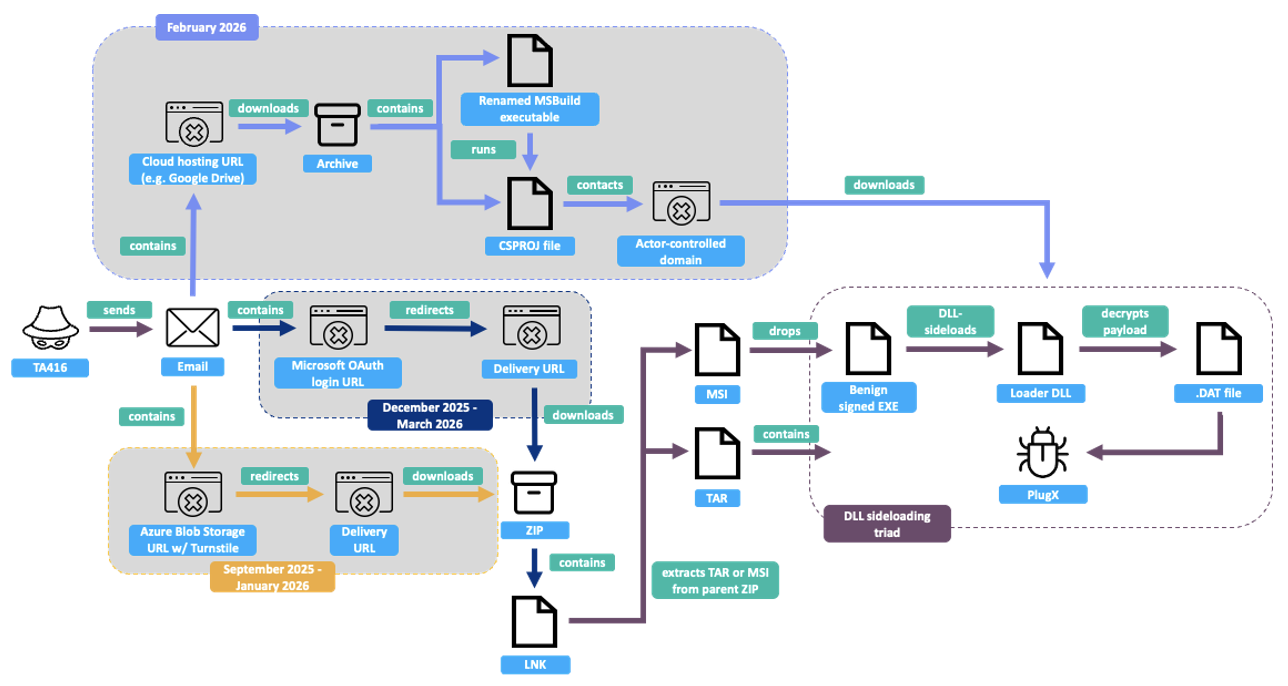
Researchers at Proofpoint report that a Chinese state-linked cyberespionage group, which it calls TA416 (also known as Twill Typhoon, Mustang Panda, among other names), has shifted its gaze back to Europe after years of focusing on other parts of the world.
The surge began in mid-2025, with a bevy of issues bubbling up between China and Europe, the company said.
Separately, the same group took up targeting the Middle East in March after the start of the conflict in Iran, something it had never been spotted doing before, Proofpoint found. (Tim Starks / CyberScoop)
Related: Proofpoint, Infosecurity Magazine, SC Media, Cyber Security News, Cyber Press
Daniel Rhyne, a former infrastructure engineer at an industrial company headquartered in New Jersey, admitted to hacking and extorting the company to try to collect $750,000 in Bitcoin.
He pleaded guilty in federal court to extortion in connection with a threat to cause damage to a protected computer and intentional damage to a protected computer.
Authorities said Rhyne, a New Jersey resident at the time of the incident in November 2023, was taking steps to hack the company’s computer network and extort the company into paying a ransom.
Rhyne remotely accessed a desktop and scheduled tasks that would trigger damage to the company’s network, including deleting administrator accounts, changing passwords, and shutting down servers, officials said.
On Nov. 25, 2023, Rhyne launched the attack and sent an extortion email to all employees, threatening to continue the attack until he was paid 20 bitcoin, the equivalent of $750,000 at the time of the attack, officials said. (Matthew Enuco / NJ.com)
Related: Justice Department, Bleeping Computer
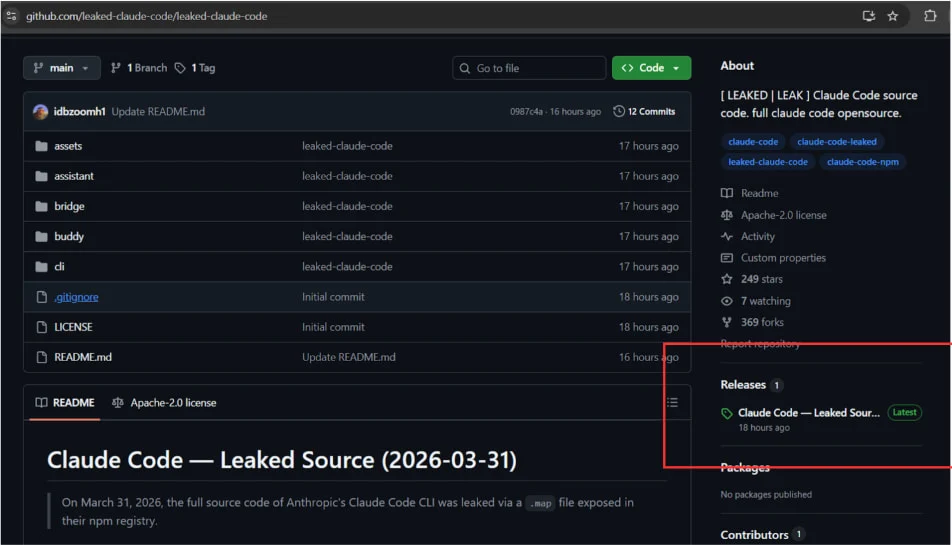
Researchers at Zscaler report that threat actors are exploiting the recent Claude Code source code leak by using fake GitHub repositories to deliver Vidar information-stealing malware.
Claude Code is a terminal-based AI agent from Anthropic, designed to execute coding tasks directly in the terminal and act as an autonomous agent, capable of direct system interaction, LLM API call handling, MCP integration, and persistent memory.
On March 31, Anthropic accidentally exposed the full client-side source code of the new tool via a 59.8 MB JavaScript source map included by accident in the published npm package.
The leak contained 513,000 lines of unobfuscated TypeScript across 1,906 files, revealing the agent’s orchestration logic, permissions, and execution systems, hidden features, build details, and security-related internals.
The exposed code was rapidly downloaded by a large number of users and published on GitHub, where it was forked thousands of times. The leak created an opportunity for threat actors to deliver the Vidar infostealer to users looking for the Claude Code leak.
The researchers found that a malicious GitHub repository published by user “idbzoomh” posted a fake leak and advertised it as having “unlocked enterprise features” and no usage restrictions.
To drive as much traffic to the bogus leak, the repository is optimized for search engines and is shown among the first results on Google Search for queries like “leaked Claude Code. (Bill Toulas / Bleeping Computer)
Related: Zscaler, eSecurity Planet, The Register
An Ohio man, Philip Durachinsky, who is on the autism spectrum and was accused in a widespread computer hacking case, was ordered released from jail on Thursday after spending more than nine years in pretrial lockup while waiting for a resolution in his case.
He was arrested on federal charges on Jan. 25, 2017, and will be released from the Mahoning County Jail within seven days of US District Judge Solomon Oliver’s ruling. Oliver said he would issue a separate ruling laying out restrictions imposed on Durachinsky while his case is pending. (Adam Ferrise / Cleveland.com)
The threat group known as ShinyHunters has issued what it calls a final warning to Cisco, setting a deadline of April 3, 2026, before it begins leaking data it claims to have stolen.
The message appeared on the group’s dark web leak site, where it has already been publishing data linked to earlier Salesforce-related incidents affecting companies worldwide.
According to the post, the group claims access to data from three separate breach paths, identified as UNC6040, Salesforce Aura, and compromised AWS accounts. In total, it alleges more than three million Salesforce records were taken, along with personally identifiable information, GitHub repositories, AWS storage buckets, and internal corporate data.
The group has described the warning as final and warns Cisco to make contact before the stated deadline, adding that failure to do so will lead not only to data leaks but also unspecified “digital problems.” (Waqas / HackRead)
Related: SC Media, CX Today, Cyber Security News
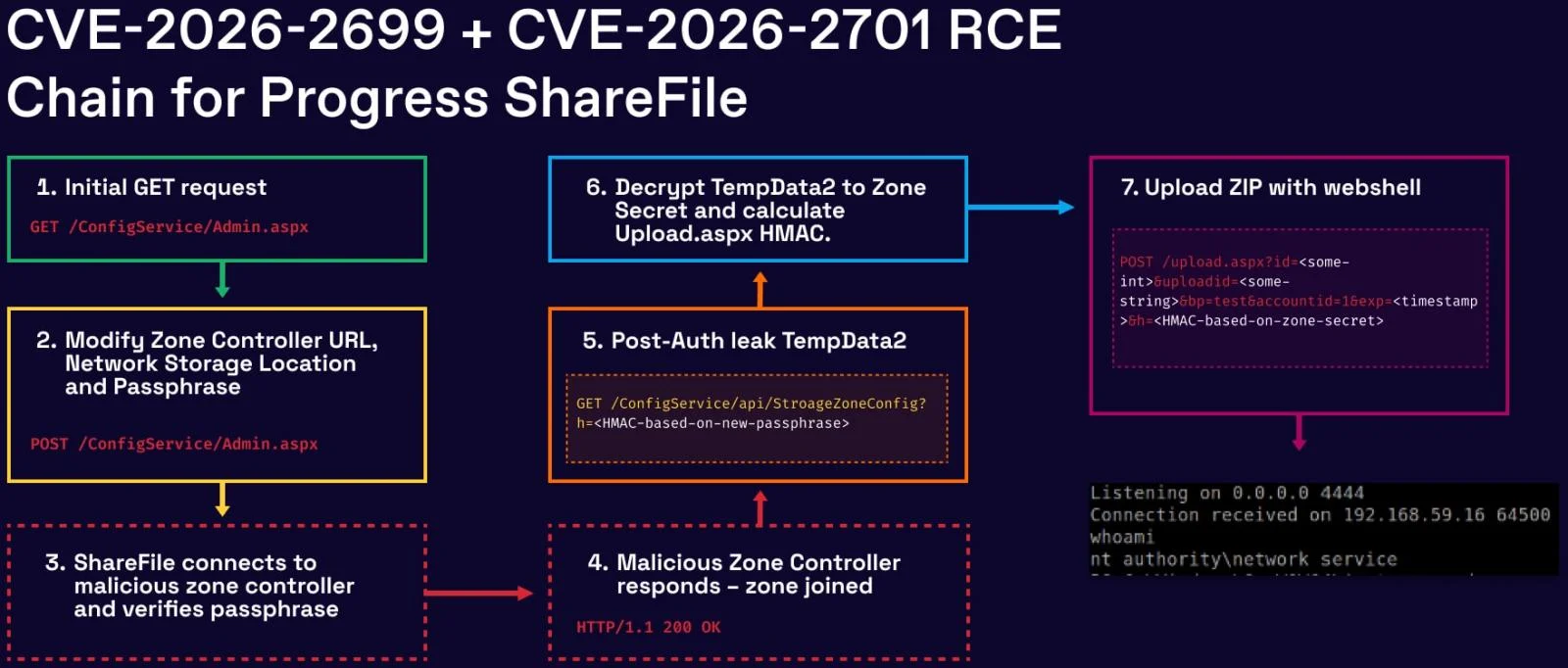
Researchers at watchTowr report that two vulnerabilities in Progress ShareFile, an enterprise-grade secure file transfer solution, can be chained to enable unauthenticated file exfiltration from affected environments.
watchTowr discovered an authentication bypass (CVE-2026-2699) and a remote code execution (CVE-2026-2701) in the Storage Zones Controller (SZC) component present in branch 5.x of Progress ShareFile.
SZC gives customers more control over their data by allowing them to store it on their infrastructure (either on-prem or in a third-party cloud provider) or on the Progress systems.
By watchTowr's scans, there are about 30,000 Storage Zone Controller instances exposed on the public internet.
The ShadowServer Foundation currently observes 700 internet-exposed instances of Progress ShareFile, most of which are located in the United States and Europe.
watchTowr discovered the two flaws and reported them to Progress between February 6 and 13, and the full exploit chain was confirmed on February 18 for Progress ShareFile 5.12.4. The vendor released security updates in version 5.12.4, released on March 10. (Bill Toulas / Bleeping Computer)
Related: watchTowr Labs
A staff report from the US government's Privacy and Civil Liberties Oversight Board (PCLOB) praises the value of Section 702 of the Foreign Intelligence Surveillance Act, which allows the FBI, NSA, and others to collect communications of foreigners abroad without a warrant, which is due to expire on April 20 unless renewed by Congress.
The law remains controversial because it can incidentally sweep up Americans’ communications, raising concerns among critics about compliance with the Fourth Amendment. The authority is set to expire on April 20 unless renewed by Congress.
In 2024, lawmakers reauthorized the program for two years, adopting several reforms focused largely on FBI compliance with targeting procedures. The reforms didn’t include a long-sought measure from privacy advocates to include a warrant requirement for searches of US person data collected under 702.
In the report, issued under a “Sub-Quorum Policy” without a full board, the staff concluded that Section 702 continues to provide significant intelligence value and that recent reforms have improved compliance. The board, at a full slate, normally has five members, and a three-member quorum is required to conduct oversight business.
The report says that declining FBI searches for Americans’ information within Section 702 data may reflect hesitation that could affect the detection of threats against the nation, a notable emphasis for a watchdog that has historically focused on the misuse of authority. (David DiMolfetta, / NextGov/FCW)
Related: PCLOB
Anurag Sen, a security researcher at CyPeace, discovered that a publicly accessible Amazon-hosted storage server allowed anyone with a web browser to access potentially hundreds of thousands of people’s personal data without needing a password, including driver’s licenses, passports, and other personal information collected by the Duc App, a money-transfer service owned by Toronto-based Duales.
The Canadian fintech company said it resolved the data exposure on Tuesday after TechCrunch alerted its chief executive that one of the company’s cloud storage servers was publicly listing its contents, without a password.
The data was also stored unencrypted, meaning anyone with a link to the data was able to view it in full. (Zack Whittaker / TechCrunch)
Related: Silicon Canals
Payday loan company Check City Partnership confirmed it notified 322,687 people about a March 2025 data breach that compromised a range of personal and financial data, including financial account numbers and credit and debit card numbers.
The Clop cybercrime gang, on May 9, 2025, took credit for breaching the payday loan company on its data leak site. To prove its claim, Clop posted sample images of what it says are documents stolen from Check City. (Paul Bischoff / Comparitech)
Related: PYMNTS
The personal data of potentially thousands of French gun owners has been stolen following the cyber attack on a government website.
The French Interior Ministry confirmed that it had recently detected “unauthorized access, through a malicious action,” to an account belonging to a company using the Système d’information sur les armes (SIA), the government database where gun owners must register their weapons.
The breach resulted in “the extraction of commercial data contained in that account, some of which may include personal data of firearm owners as well as data relating to firearm transactions,” the ministry said.
The Interior Ministry said it had reported the matter to the Paris Public Prosecutor, “with a view to opening an investigation.” (Paul Willis / The Connexion)
Researchers at BlackFog report that developing ClickFix-style attacks has just gotten much easier, thanks to a newly distributed malware-as-a-service (MaaS) platform that automates every step of the social engineering technique for would-be attackers.
A developer operating under the name "VenomStealer" is selling a MaaS platform of the same name on cybercriminal forums and networks, the researchers say. Venom Stealer allows attackers to create a persistent, multistage pipeline from initial infection to credential theft, cryptocurrency wallet access, and data exfiltration based on the initial ClickFix interaction. (Elizabeth Montalbano / Dark Reading)
Related: BlackFog, Biometric Update, SC Media, Security Week

Florida Republican Congressman Randy Fine says Iran's military recently targeted him in a cyberattack that might have pinpointed his location, placing him in immediate danger.
He said that the House Office of Cyber Security and Capitol Police informed him that Iran's Islamic Revolutionary Guard Corps was likely involved.
Fine is a vocal supporter of the US-Israel war on Iran. (Mark Harper / Daytona Beach News-Journal)
Related: Daytona Beach News-Journal, CBS Austin, Palm Beach Post
Best Thing of the Day: At Least Wiper Attacks Allow for Recovery
Stryker Corporation says it's fully operational three weeks after many of its systems were wiped out in a cyberattack claimed by the Iranian-linked Handala hacktivist group.
Worst Thing of the Day: One More App With a Dodgy E2EE Claim
TeleGuard, an app that markets itself as a secure, end-to-end encrypted messaging platform, implements its encryption so poorly that an attacker can trivially access a user’s private key and decrypt their messages.
Bonus Worst Thing of the Day: It's Not Like Adversaries Are Targeting the US Government or Anything
Hundreds of CyberCorps students and recent graduates are striking out in the pursuit of US government cybersecurity jobs in the face of Trump administration budget cuts.
Closing Thought