Pentagon-Anthropic standoff escalates, putting contracts and AI deployments at risk
FBI warns of phishing campaigns impersonating city and county officials, TX governor warns health agencies and universities of Chinese-manufactured devices, A big bank in S. Africa was hit by a ransomware attack, Hackers are selling Windows exploit for $220k, much more
Don't miss my latest CSO piece that reveals how CISA and MITRE quietly renewed their CVE contract to put the essential program on firmer footing and avoid the kind of funding cliff that frightened the cybersecurity community last April.
Metacurity is the only daily cybersecurity newsletter that is written outside the usual cyber press echo chamber and is a straightforward and accurate alternative to vendor-driven content and PR-flavored threat intelligence.
Please consider supporting my work on Metacurity by upgrading your subscription. Thank you.
The Trump administration’s dispute with artificial intelligence firm Anthropic escalated sharply this week, threatening both the company’s defense contracts and broader commercial operations.
Anthropic filed lawsuits seeking to overturn a Pentagon designation labeling the company a “supply-chain risk,” a move that bars federal agencies and contractors from using its Claude AI system. The company argues the designation — typically applied to foreign threats — could threaten hundreds of millions in revenue and damage its relationships with commercial clients.
The White House is preparing an executive order directing agencies to remove Anthropic’s models from government systems, forcing contractors to replace software already embedded in analytical and operational tools. Pentagon officials have said there is little chance the department will renew a partnership with the company.
At the heart of the dispute are limits Anthropic has placed on how its AI can be used. The company has refused to remove safeguards preventing certain applications, including surveillance or weapons-related uses. US officials counter that such restrictions could interfere with lawful military operations and say private companies should not dictate government deployment of AI technologies.
Anthropic portrays the government’s actions as aggressive and retaliatory. In court filings, the company contends that the designation unfairly punishes it for advocating responsible use of AI and could destabilize its business. Executives warn that the move may signal to commercial customers that their technology is risky or restricted, with long-term consequences for growth.
The standoff highlights a broader tension between national security and corporate responsibility. Anthropic’s models have become widely adopted across the private sector, and the company argues that government-imposed constraints could not only block defense contracts but ripple across commercial operations.
Anthropic executives argue that the supply‑chain risk label is already hurting its broader commercial business, not just defense work, with prospective customers backing out of deals because of the government’s designation.
For now, the Pentagon appears unmoved. A senior defense official said this week that Anthropic’s legal challenge makes a renewed deal “unlikely,” signaling that the clash could reshape how AI companies and the US military collaborate. (Maria Curi / Axios, Dave Paresh / Wired, Katrina Manson / Bloomberg, and Maxwell Zeff / Wired)
Related: Wired, Reuters, New York Times, Fortune, CNN, Associated Press, United States District Court for the Northern District of California, crypto.news, Cyber Security News, NPR, Wall Street Journal, Computerworld, Financial Times, Politico, BBC, The Verge, SupplyChainBrain, One America News Network, Semafor, OnMSFT, Telegraph, PCMag, Inc.com, Tom's Hardware, PYMNTS.com, International Business Times, NBC News, Courts of Appeals, Sherwood News, Implicator.ai, Business Insider, Axios, Bloomberg, Tech Policy Press, Wall Street Journal
The FBI is warning that cybercriminals are impersonating US city and county officials in phishing campaigns targeting individuals and businesses applying for local planning and zoning permits.
Attackers use publicly available information to make the messages appear legitimate, sending unsolicited emails that reference real permit details such as zoning application numbers, property addresses, or permit information. The emails request payment of permit-related fees and direct victims to send funds via wire transfer, peer-to-peer payment services, or cryptocurrency.
The FBI said the phishing emails often originate from non-government domains and may include attachments that ask recipients to request additional details via email. In some cases, scammers also time their messages to coincide with legitimate communications about permit applications to increase the likelihood that targets will comply.
Authorities advised recipients to verify the authenticity of any fee request by checking the sender’s domain and contacting the relevant city or county office directly. Victims are urged to report incidents to the FBI’s Internet Crime Complaint Center and provide details, including the email address used, the fraudulent invoice amount, and other information tied to the scam.
The bureau noted that similar schemes involving criminals impersonating government or law enforcement officials have surfaced in previous years as part of broader efforts to extort money or steal personal information. (Sergiu Gatlan / Bleeping Computer)
Related: Security Affairs, Slashgear, IC3
Texas Gov. Greg Abbott directed state health agencies and public university systems to examine potential cybersecurity risks tied to Chinese-manufactured medical devices, warning they could be used to access sensitive patient data.
The directive came in a letter to state officials calling for steps to protect Texans’ medical information and ensure safeguards are in place at state-owned medical facilities.
Abbott said recent federal warnings about vulnerabilities in certain patient monitoring devices highlight the possibility that unauthorized actors could remotely access protected health information. He argued that the growing presence of Chinese-manufactured “smart” medical devices in US healthcare systems raises serious data-privacy concerns.
The order instructs the Texas Health and Human Services Commission, the Department of State Health Services, and public university systems to review procurement policies, inventory network-connected medical devices, and assess cybersecurity protections at state facilities. Texas Cyber Command will also evaluate whether specific devices should be added to the state’s prohibited technology list and recommend additional safeguards.
State agencies must submit their findings and recommendations to the governor’s office by April 17. Abbott said the results could inform potential legislation aimed at strengthening protections for Texans’ medical data from foreign adversaries. (Eric Mack / Fox News)
Related: Office of the Texas Governor, StateScoop
Finance Minister Enoch Godongwana has confirmed that the Land and Agricultural Development Bank of South Africa was hit by a ransomware attack on January 12.
The Minister revealed this in a parliamentary reply to uMkhonto weSizwe MP Adil Nchabeleng, who had asked him about the nature of the breach, the systems affected, and whether a ransom had been demanded.
The Minister said that hackers demanded 5 Bitcoin, about R5.4 million, but the bank did not pay. He confirmed that critical banking systems and farmer data were not compromised. (Mthobisi Nozulela / Cape Times)
Related: IOL, Press Reader
Hackers are offering a Windows exploit for sale on a dark web forum for $220,000, advertising a vulnerability that could allow attackers to escalate privileges on affected systems.
According to a posting on the underground marketplace, the exploit targets Windows Remote Desktop Services and can enable an attacker with limited access to gain full system-level privileges by manipulating a registry configuration associated with the service. The seller claims the exploit works across multiple supported versions of Windows and is offering it exclusively to a single buyer.
Microsoft has already addressed the issue in its February 2026 Patch Tuesday security updates. Systems that have installed the patch are protected, but organizations that have not yet applied the update may still be exposed, potentially making the exploit valuable for attackers seeking to compromise unpatched enterprise systems. (Ivan Jenic / Neowin)
Related: Codekeeper, Cyber Security News
A sophisticated iPhone hacking toolkit used in espionage campaigns by Russian intelligence likely originated with a US military contractor before spreading to other threat actors, according to security researchers.
The toolkit, known as Coruna, contains 23 separate modules capable of exploiting multiple vulnerabilities in Apple’s iOS operating system. Researchers discovered the tools during investigations into cyberattacks in 2025 and say the framework was designed for highly targeted operations. It was later observed in the hands of Russian government hackers targeting a limited number of Ukrainian victims.
Evidence indicates the software may have been developed by defense contractor L3Harris, which produces surveillance and cyber capabilities for Western intelligence agencies. Researchers say the toolkit later circulated beyond its original users and was eventually employed by Chinese cybercriminal groups in financially motivated attacks, illustrating how sophisticated government-grade cyber tools can proliferate once they escape controlled environments. (Lorenzo Franceschi-Bicchierai / TechCrunch)
Halifax Water said that it is investigating a privacy breach involving its Customer Connect online portal.
Halifax Water has not yet determined when the unauthorized access occurred, how long it lasted, or when the organization was alerted to the breach, spokesperson Brittany Smith said.
Smith didn’t say what customer information was accessed or how many customers were impacted, but said there is no indication that financial information is at risk.
The Customer Connect portal allows customers to access account information online to receive alerts, review current and past water usage, and find billing information. The portal will remain offline as Halifax Water continues to investigate.
“We are following our incident response process, which includes notifying the Halifax Regional Police, the Nova Scotia Regulatory Appeals Board, and the Nova Scotia Privacy Office,” said Smith.
The utility is warning customers to exercise caution if they receive a phone call from someone claiming to be Halifax Water. (Ben Dornan / CBC News)
Related: Hot Country 1035, PNI Atlantic News
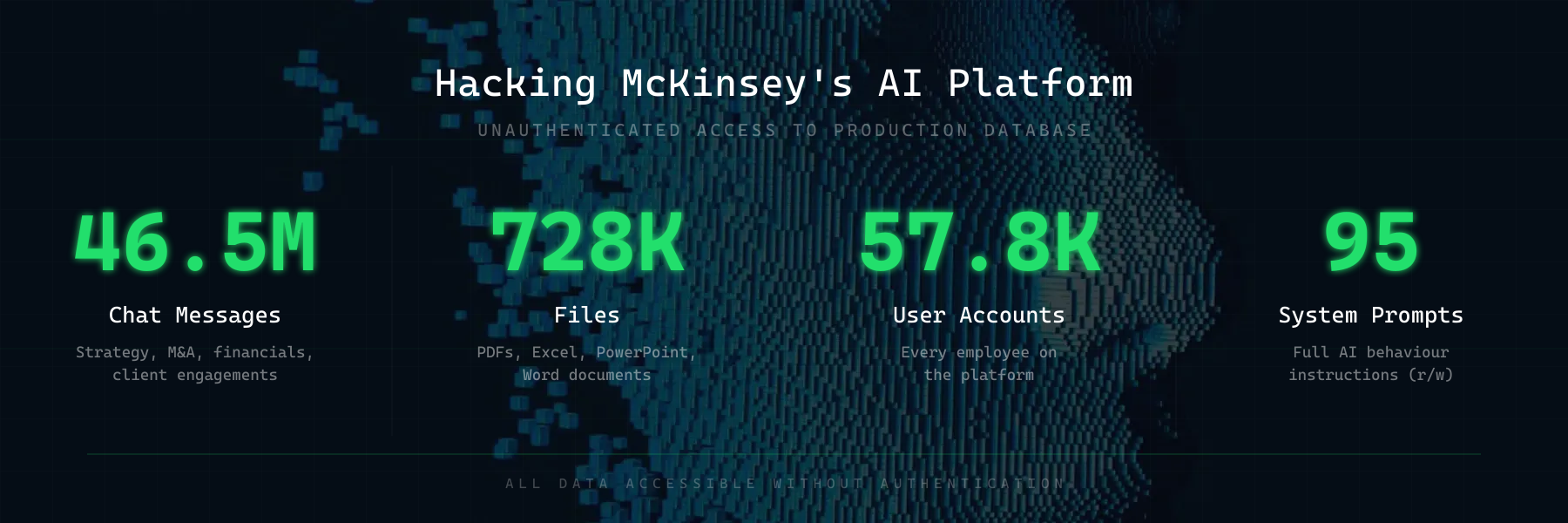
Red team security startup Codewall says an autonomous AI agent was able to hack a chatbot used internally by consulting firm McKinsey, gaining full read and write access to the system in roughly two hours.
The attack was carried out by CodeWall targeting McKinsey’s generative AI platform, known as Lilli, which the company introduced in 2023. The system is widely used inside the firm, with tens of thousands of employees relying on it and generating more than 500,000 prompts each month.
During the test, the AI agent gained access to the platform’s production database, exposing about 46.5 million chat messages related to corporate strategy, mergers and acquisitions, and client engagements. The researchers also discovered roughly 728,000 files containing confidential client information, along with tens of thousands of user accounts and internal system prompts that guide the chatbot’s behavior.
The incident occurred during a controlled red-team exercise rather than a real cyberattack, but the researchers said the results illustrate how autonomous AI systems could rapidly exploit vulnerabilities and expose sensitive corporate data if safeguards are not in place. Security experts warn that the findings highlight the growing risk of AI-driven attacks capable of operating at machine speed. (Jessica Lyons / The Register)
Related: Codewall, r/cybersecurity, CXO Today
Ericsson Inc., the US subsidiary of Swedish telecommunications company Ericsson, says personal data belonging to more than 15,000 employees and customers was stolen after attackers breached one of its service providers.
The company disclosed the incident in data breach notification letters filed with the California Attorney General, stating the provider discovered the intrusion on April 28, 2025, and subsequently notified the FBI and hired outside cybersecurity experts to investigate.
The investigation found that files containing personal data may have been accessed without authorization between April 17 and April 22, 2025. A review completed in February determined that 15,661 individuals were affected. According to regulatory filings, the exposed information may include names, addresses, Social Security numbers, driver’s license or other government ID numbers, financial account details, medical information, and dates of birth.
Ericsson said there is currently no evidence that the stolen data has been misused. The company is offering affected individuals free identity protection services, including credit monitoring, dark web monitoring, identity theft recovery assistance, and up to $1 million in identity fraud reimbursement for those who enroll. (Sergiu Gatlan / Bleeping Computer)
Related: CRN, Security Affairs
Canada will allow TikTok to continue operating in the country, a complete reversal after the government had previously ordered the social media company to close its Canadian division for security reasons.
In November 2024, under former Prime Minister Justin Trudeau, Canada ordered ByteDance Ltd., TikTok’s Chinese-backed owner, to wind down its Canadian subsidiary. That wouldn’t have banned the app’s use but would have forced its offices in Toronto and Vancouver to close.
But in January, that order was set aside following a legal motion from the government — just days after Mark Carney became the first Canadian prime minister in more than eight years to visit China, where he announced a deal with President Xi Jinping to relax tariffs.
TikTok Technology Canada Inc. will now be allowed to operate under new legally binding commitments to enhance its security, Canadian Industry Minister Melanie Joly said in a statement, saying the decision followed a fresh security review. (Thomas Seal / Bloomberg)
Related: Engadget, Government of Canada, d2125, iPhone in Canada, Global News, Wall Street Journal, Reuters, Canadian Press, r/canada
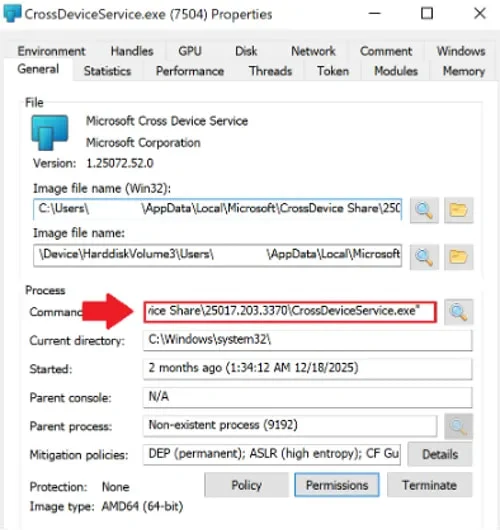
Researchers at BlueVoyant say attackers are targeting employees at financial and healthcare organizations by posing as IT staff on Microsoft Teams and persuading victims to grant remote access through Microsoft’s Quick Assist tool.
The scheme begins with a flood of spam emails designed to frustrate the victim, after which the attacker contacts the employee on Teams, offering help to resolve the issue and instructing them to start a remote Quick Assist session.
Once access is granted, the attacker deploys a malicious toolset using digitally signed MSI installers hosted on personal Microsoft cloud storage accounts. The installers disguise themselves as Microsoft Teams components and a legitimate Windows utility called CrossDeviceService. The attack relies on DLL sideloading through legitimate Microsoft binaries to load a malicious library that decrypts embedded shellcode in memory and launches a previously unseen malware known as A0Backdoor.
The malware performs system fingerprinting and communicates with its command-and-control infrastructure by embedding encoded data in DNS MX queries, allowing the traffic to blend in with normal network activity.
BlueVoyant says the campaign targeted at least one Canadian financial institution and a global healthcare organization and appears to be an evolution of tactics associated with the BlackBasta ransomware group, although the use of signed MSI installers, the A0Backdoor payload, and DNS MX-based command channels represents new techniques. (Bill Toulas / Bleeping Computer)
Related: BlueVoyant, Cyber Security News
Donald Trump’s nominee to lead US Cyber Command and the National Security Agency moved closer to confirmation Monday after the Senate voted 68–28 to limit debate on Army Lt. Gen. Joshua Rudd.
The cloture vote clears the way for a final confirmation vote, which is expected today.
Rudd, currently the deputy chief of US Indo-Pacific Command, faced an unusual confirmation process after Sen. Ron Wyden sought to block a quick approval, arguing that the nominee lacks sufficient experience in US signals intelligence operations. Wyden said the country needs a leader with deeper expertise in the field, particularly during a time of conflict.
Despite the objections, Senate Armed Services Committee Chair Roger Wicker said Rudd has strong bipartisan support. If confirmed, Rudd would become the first Senate-approved leader of both Cyber Command and the NSA since former chief Gen. Timothy Haugh was fired nearly a year ago. (Martin Matishak / The Record)
Related: Washington Examiner, Punchbowl News
The Trump administration is plotting an interagency body to confront malign hackers, pilot programs to secure critical infrastructure across states, and other steps tied to its freshly-released cyber strategy, National Cyber Director Sean Cairncross said.
The “interagency cell” will bring together agencies like the Justice Department, the Department of State, the FBI, and the Pentagon, which will make it clear that going on cyber offense isn’t just about attacking enemies in cyberspace, Cairncross said.
“Sure, that’s part of it, but that’s not all of it,” he said at an event hosted by USTelecom. It will include diplomatic efforts, arrests, and more, he said. “As President Trump has made clear, he expects results, and he’s empowered the team under him to go get them.”
A series of pilot programs will be catered to specific critical infrastructure industries in specific states, such as water in Texas and beef in South Dakota, Cairncross said. Different sectors operate at more or less mature levels, he said. (Tim Starks / CyberScoop)
Related: The National, GovCIO, VitalLaw, Cybersecurity Dive, Meritalk, Bloomberg Law
Mandiant founder Kevin Mandia has a new startup called Armadin, which has raised nearly $190 million in Seed and Series A funding rounds.
Accel led the round with participation from Google Ventures, Kleiner Perkins, Menlo Ventures, In-Q-Tel, and follow-on investment from 8VC and Ballistic Ventures. (Samantha Subin / CNBC)
Related: PR Newswire
AI-enabled cybersecurity defense company Kai emerged from stealth with $125 million in funding.
Evolution Equity Partners led the funding, with participation from N47 and strategic investors. (Angus Loten / Wall Street Journal)
Related: PR Newswire
OpenAI has agreed to buy Promptfoo, a startup that enables large businesses to find and fix security issues in artificial intelligence models during their development, part of a push to help corporate customers reduce possible risks from deploying AI software.
The ChatGPT maker said that it will integrate Promptfoo’s technology into OpenAI Frontier, a recently launched platform that allows organizations to build and manage AI agents. Frontier is meant to help ensure each agent — which OpenAI refers to as “AI coworkers” — has appropriate guardrails and data access. Terms of the acquisition weren’t disclosed. (Dina Bass and Rachel Metz /Bloomberg)
Related: OpenAI, CSO Online, CNBC, Forbes, TechCrunch, Silicon Angle, Techzine
Best Thing of the Day: Not Fooling Around When It Comes to Bad Security
The Korean Financial Supervisory Service is preparing to refer Seoul Guarantee Insurance Company, which was unable to provide key services after a ransomware attack last year, to the sanctions review committee.
Worst Thing of the Day: White Male-Only Military AI. What Could Go Wrong?
The Pentagon named as Chief Data Officer Gavin Kliger, a computer scientist who is a white supremacist and misogynist, and aided billionaire Elon Musk's DOGE efforts last year. Kliger will be in charge of day-to-day alignment and execution of the Department’s AI projects.
Closing Thought