Russia aids Iran with satellite targeting, cyber ops against Middle East infrastructure, report
Cyber-enabled fraud reached $17.6b in 2025, Hackers accessed files of Jones Day, Storm-1175 deploys n-day and zero day exploits, GPU rowhammering enters new territory, CISA orders FortiClient EMS fixes, Wynn Resorts breach affected 21k+ people, Hong Kong hospital breach affected 56k patients, more


Check out my latest CSO piece on the rise of proactive cyber as the US government and private sector organizations, such as Google, take steps to move upstream to disrupt adversaries.
Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
Russian satellites have made dozens of detailed imagery surveys of military facilities and critical sites across the Middle East to help Iran strike US forces and other targets, according to a Ukrainian intelligence assessment, which also found that Russian and Iranian hackers were collaborating in the cyber domain.
Hacking groups controlled by Iran have stepped up operations since late February, targeting mainly critical infrastructure and telecommunications companies in the Gulf, they said.
The Ukrainian assessment said Russian and Iranian hacker groups were interacting via Telegram and noted collaboration between the Russian groups "Z-Pentest Alliance", "NoName057(16)", and "DDoSia Project" and Iran's "Handala Hack".
For example, last month, it said groups including Handala Hack published a warning on Telegram about attacks on the information and communication systems of Israeli energy companies.
The Russian groups simultaneously published access credentials to control systems at critical infrastructure facilities in Israel, it said.
Iranian hacker groups have also used some techniques in operations that indicated they had obtained them from Russian military intelligence hackers, it said. For instance, it said, Iranian hacker groups "Homeland Justice" (UAC-0074) and "Karmabelow80" used ProfitServer, a Russian VPS provider from Chelyabinsk, to register domains.
Separately, the Jerusalem Post reports that Russian intelligence has provided Iran with a detailed list of 55 critical energy infrastructure targets within Israel.
The report, which highlights the deepening military and intelligence cooperation between Moscow and Tehran, suggests that the information that was shared enables Iran to launch precision missile strikes against Israel’s energy grid. (Tom Balmforth and John Irish / Reuters and Amichai Stein / Jerusalem Post)
Related: TVP World, Euronews, Times of India
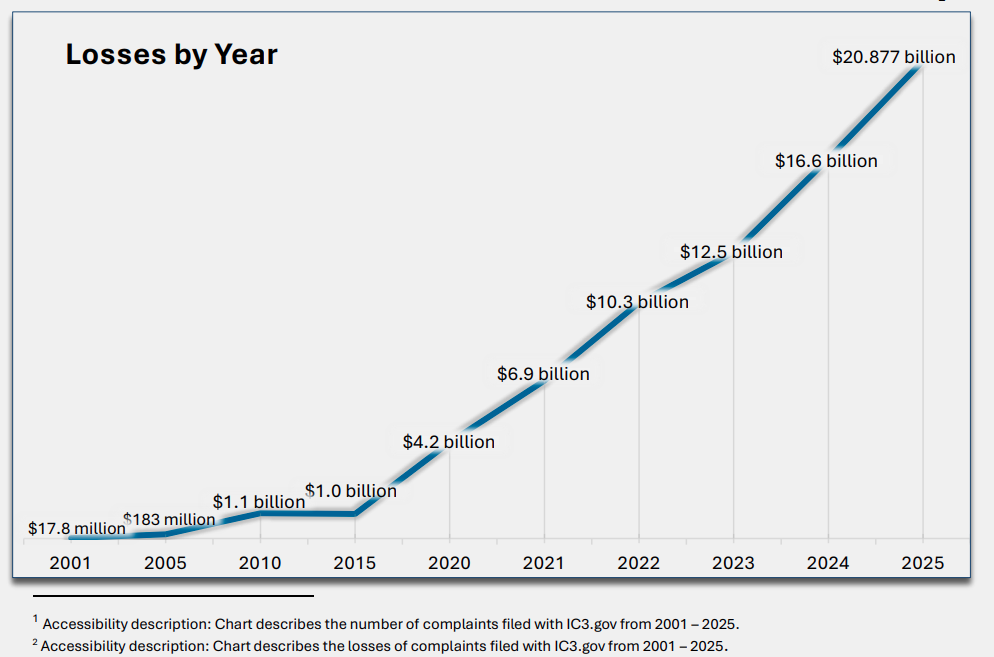
Cyber-enabled fraud accounted for the overwhelming majority of all losses reported to the FBI’s Internet Crime Complaint Center (IC3) in 2025, with a staggering $17.6 billion stolen.
The center’s annual report offers a snapshot of the law enforcement agency’s myriad efforts to combat digital threats, especially ransomware, which increasingly harms individuals, businesses, and the US critical infrastructure.
Cyber-enabled fraud was behind 85% of all losses reported to the hub in 2025 and constituted 45% of the 1,008,597 complaints it received overall. Investment fraud led in total dollars lost at $8.6 billion, followed by business email compromise (BEC) scams at over $3 billion and tech support fraud at $2.1 billion.
Speaking to reporters, Cyber Division Section Chief Taushiana Bright highlighted the ongoing scourge of ransomware, noting the agency is currently investigating over 200 ransomware variants, actors, and enablers.
Sixty-three new ransomware variants were identified last year, according to Bright, resulting in 3,611 complaints tied to more than $32 million in losses. That is an increase from 2024, when there were 3,156 complaints totaling just over $12 million regarding ransomware losses. Complaints filed to IC3 represent just a small fraction of the overall ransomware ecosystem.
“Cybercriminals have indiscriminately attacked hospitals, emergency responders, schools, and entire city governments. I can't think of anything that's off limits to them,” she said. (Martin Matishak / The Record)
Related: IC3, NextGov/FCW, Click2Houston, ITNews, The Cyber Express, Politico
Hackers breached the big law firm Jones Day and accessed the files of 10 clients with the prolific cybercriminal group known as Silent, taking credit for the attack.
“Jones Day recently experienced a cyber ‘phishing’ incident in which an unauthorized third party accessed a limited number of dated files for 10 clients,” spokesperson Dave Petrou said in a statement. “All impacted clients have been notified.”
The identities of the affected clients weren’t immediately clear. Hackers also stole data belonging to Jones Day in 2021.
The law firm has represented a huge number of large American companies, including Goldman Sachs Group Inc., McDonald’s Corp., and General Motors Co. The firm was hired in February to defend JPMorgan Chase in a case in which President Donald Trump sued the bank for its closure of his accounts in 2021.
The hacking group Silent specifically targets American law firms, stealing data and extorting them, according to a 2025 FBI alert. The hackers take advantage of the “the highly sensitive nature of legal industry data,” according to the FBI. (Patrick Howell O'Neill / Bloomberg)
Related: Databreaches.net, Reuters, The Lawyer, Bitget
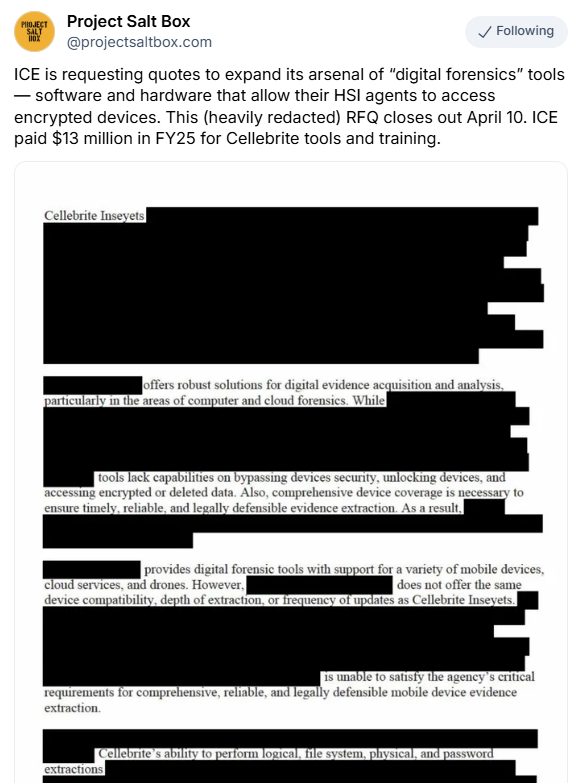
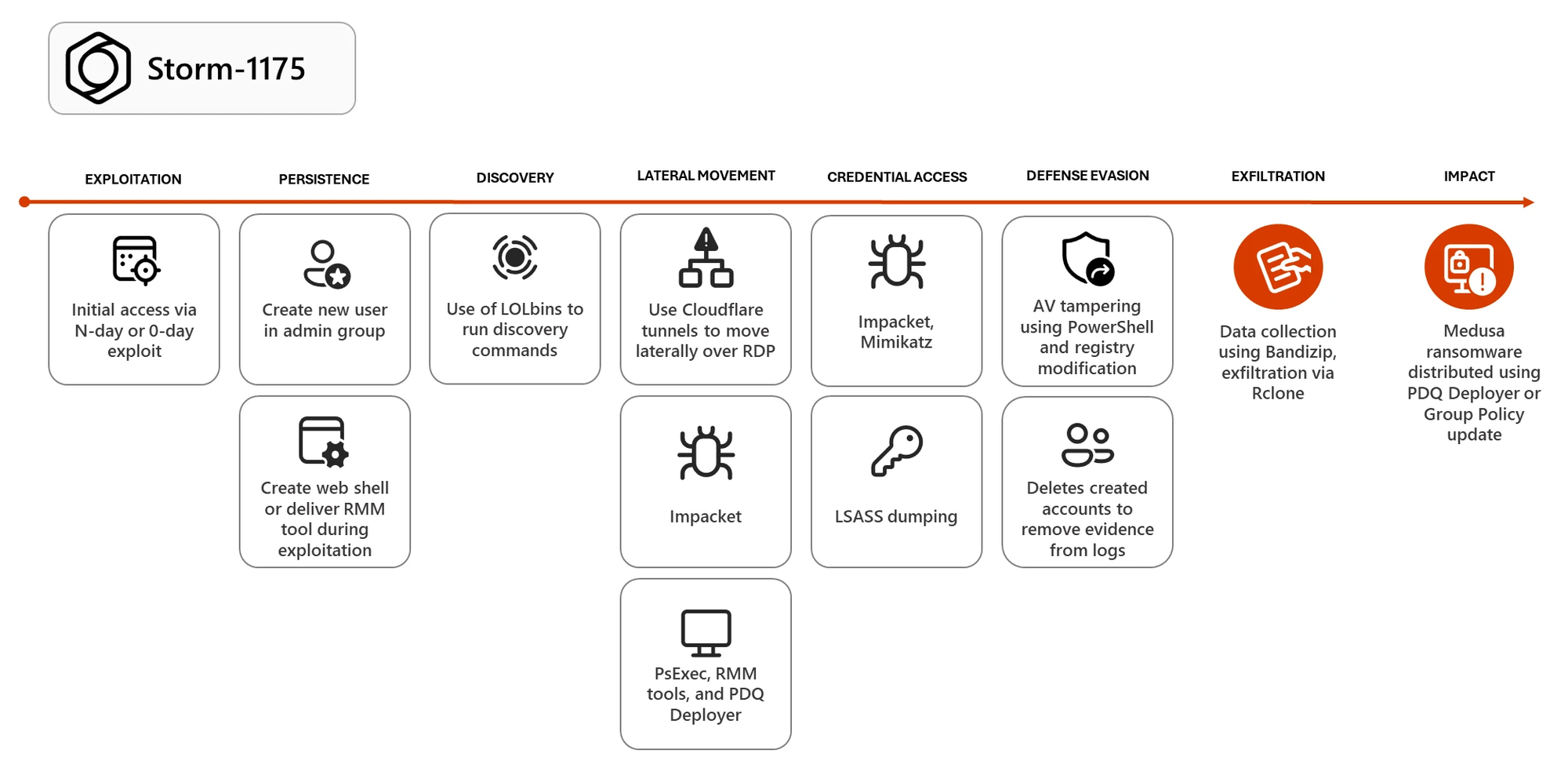
Researchers at Microsoft report that Storm-1175, a China-based financially motivated cybercriminal group known for deploying Medusa ransomware payloads, has been deploying n-day and zero-day exploits in high-velocity attacks.
This cybercrime gang quickly shifts to targeting new security vulnerabilities to gain access to its victims' networks, weaponizing some of them within a day and, in some cases, exploiting them a week before patches are released.
"Storm-1175 rapidly moves from initial access to data exfiltration and deployment of Medusa ransomware, often within a few days and, in some cases, within 24 hours," Microsoft said.
Microsoft has also observed Storm-1175 operators chaining multiple exploits to gain persistence on compromised systems by creating new user accounts, deploying remote monitoring and management software, stealing credentials, and turning off security software before dropping ransomware payloads. (Sergiu Gatlan / Bleeping Computer)
Related: Microsoft, Security Week, The Record, Cyber Press, Cyber Security News
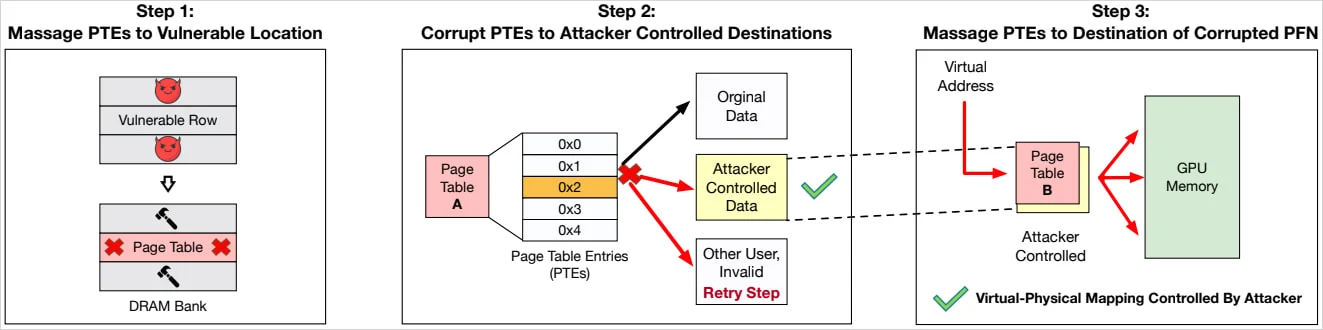
Two research teams, working independently of each other, demonstrated attacks against two cards from Nvidia’s Ampere generation that take GPU rowhammering into new—and potentially much more consequential—territory: GDDR bitflips that give adversaries full control of CPU memory, resulting in full system compromise of the host machine.
For the attack to work, IOMMU memory management must be disabled, as is the default in BIOS settings.
“Our work shows that Rowhammer, which is well-studied on CPUs, is a serious threat on GPUs as well,” said Andrew Kwong, co-author of one of the papers. “GDDRHammer: Greatly Disturbing DRAM Rows—Cross-Component Rowhammer Attacks from Modern GPUs.” “With our work, we… show how an attacker can induce bit flips on the GPU to gain arbitrary read/write access to all of the CPU’s memory, resulting in complete compromise of the machine.”
On Friday, researchers unveiled a third Rowhammer attack that also demonstrates Rowhammer attacks on the RTX A6000, which, achieves privilege escalation to a root shell. Unlike the previous two, the researchers said, it works even when IOMMU is enabled.
“By corrupting GPU page tables, an unprivileged CUDA kernel can gain arbitrary GPU memory read/write, and then chain that capability into CPU-side escalation by exploiting newly discovered memory-safety bugs in the NVIDIA driver,” the researchers explained. “The result is system-wide compromise up to a root shell, without disabling IOMMU, unlike contemporary works, making GPUBreach a more potent threat.”
The three attacks are called GDDRHammer, GeForge, and GPUBreach. (Dan Goodin / Ars Technica)
Related: GDDR Fail, GPU Breach, SC Media, Security Week, Tom's Hardware, Wccftech, Bleeping Computer
The US Cybersecurity and Infrastructure Security Agency (CISA) ordered federal agencies to secure FortiClient Enterprise Management Server (EMS) instances against an actively exploited vulnerability by Friday.
Tracked as CVE-2026-35616, this security flaw was discovered by cybersecurity firm Defused, which described it as a pre-authentication API access bypass that can allow attackers to bypass authentication and authorization controls entirely.
Fortinet released emergency hotfixes over the weekend to address the vulnerability and said the security issue stems from an improper access control weakness that unauthenticated attackers can exploit to execute code or commands via specially crafted requests. (Sergiu Gatlan / Bleeping Computer)
High-end casino and hotel operator Wynn Resorts says more than 21,000 individuals are affected by the recently disclosed data breach.
Wynn Resorts confirmed in late February that hackers had obtained employee data.
The admission came after the notorious ShinyHunters cybercrime group claimed to have stolen more than 800,000 records containing personally identifiable information, including SSNs.
The hackers later removed Wynn from their leak website. This removal suggested that it had decided to pay a ransom, but the Las Vegas-based company declined to comment when contacted by SecurityWeek at the time.
In a data breach notification filed in recent days with the Maine Attorney General’s Office, Wynn shared more details on the incident.
“The threat actor has stated that all data has been deleted,” Wynn said in its notification to impacted individuals, which further reinforces the theory that a ransom has likely been paid.
The hackers had reportedly sought a ransom of more than 22 bitcoin (roughly $1.5 million). (Eduard Kovacs / Security Week)
Related: Maine Attorney General
Hong Kong’s privacy watchdog and police are investigating a large-scale data leak involving more than 56,000 patients served by the Hospital Authority, which reported the unauthorized retrieval of a variety of information.
The authority on Saturday apologized to affected victims – patients of hospitals in Kowloon East – for the breach that compromised their names, identity card numbers, genders, dates of birth, dates of hospital visits, and details of surgical procedures, among other information.
The authority’s monitoring system detected a suspected unauthorized retrieval of patient information and a leak on a third-party platform at around 2 am on Friday, although a subsequent review of its internal network systems did not indicate a cyberattack.
“[The authority] has conducted a thorough review of its internal network systems upon discovering the incident, confirming that the systems are operating normally and securely, with no indication of a cyberattack or similar factors. The authority immediately suspended the contractor’s system maintenance work,” it said. (Edith Lin / South China Morning Post)
Related: rthk, The Standard, Healthcare Asia
Ambulances were being diverted from Signature Healthcare Brockton Hospital on Monday as the Massachusetts facility dealt with a cybersecurity incident.
But other services continued amid the investigation into the suspicious activity that affected some of the Signature Healthcare information systems, according to a statement.
Emergency services for walk-ins, inpatient services, surgeries and some procedures were still ongoing on Monday, and urgent care and ambulatory physician appointments were expected to continue Tuesday, though potentially with delays after the hospital moved to what it called "down-time procedures to ensure high-quality patient care and safety."
Chemotherapy infusions at the Greene Cancer Center were canceled for Tuesday, and the hospital's Brockton and East Bridgewater pharmacies were set to be closed on Tuesday as well. (Asher Klein / NBC Boston)
Related: Boston Globe, Daily Mail, Mass Live, WHDH, Boston25, Patch, The Enterprise, WCVB
Korean retail giant Coupang’s estimated payment amount last month increased to 5.7136 trillion won (approximately $3.8 billion), nearing the level seen before its data breach incident.
According to the retail analysis service Wiseapp·Retail on April 7, Coupang’s estimated payment amount for March was 5.7136 trillion won, a 12% increase from the 5.1113 trillion won recorded in the previous month.
This figure is an estimate based on the credit and debit card payment history of a panel of Korean consumers. It does not include bank transfers, cash transactions, or gift certificate payments, and therefore differs from the actual sales revenue.
Coupang’s estimated payment amount, excluding Coupang Eats, had increased to 5.9005 trillion won in October of last year before decreasing slightly to 5.8929 trillion won in November. (Kim Eun-jin / Business Korea)
Related: KED Global, The Investor, Korea Biz Wire, Maeil Business
Best Thing of the Day: Say Kim Jong Un's Mother Wears Army Boots Too
This terrific video shows just how easy it is to trap N. Korean hackers seeking IT jobs into exposing their false identities.
Bonus Best Thing of the Day: Let's Make OpenAI Safe and Aligned
OpenAI has launched the OpenAI Safety Fellowship, a new program for external researchers, engineers, and practitioners to pursue rigorous, high-impact research on the safety and alignment of advanced AI systems.
Worst Thing of the Day: Sam Altman Is a Big Fat Liar
OpenAI CEO Sam Altman's colleagues believed that he was not trustworthy enough to, as one put it, “have his finger on the button.”
Bonus Worst Thing of the Day: Please Keep Your Focus on Protecting Helpless Fish and Wildlife
Florida’s Fish and Wildlife Conservation Commission (FWC) police are performing dozens of license plate lookups on Flock cameras for Immigration and Customs Enforcement (ICE).
Extra Bonus Worst Thing of the Day: A Morally Uncomfortable Exercise Indeed
Tens of thousands of people have been paid by a company part-owned by Meta to train AI by combing Instagram accounts, harvesting copyrighted work, and transcribing pornographic soundtracks.
Closing Thought