Russian-speaking hacker used multiple genAI services to breach 600+ FortiGate firewalls
Spanish cops bust four Anonymous members for 2025 DDoS attacks, Wynn Resorts is the latest casino victim of ShinyHunters, PayPal business loan app was breached, UAE claims it thwarted multiple cyberattacks, Italian cops spotted cyberattacks on Chinese groups, much more
Metacurity is a daily intelligence layer for people who must stay current on the critical happenings in the cybersecurity realm.
We scan thousands of sources on the web to decode the narrative, surface overlooked signals, and connect the dots others miss.
Every day, Metacurity delivers independent, analytical, and daily intelligence that sits outside the cybersecurity echo chamber and reputation economy of other newsletters. Along with the headline-grabbing news items, Metacurity delivers news of developments you won't see in other cybersecurity newsletters.
Please consider supporting Metacurity's continued existence by upgrading your subscription. Thank you.
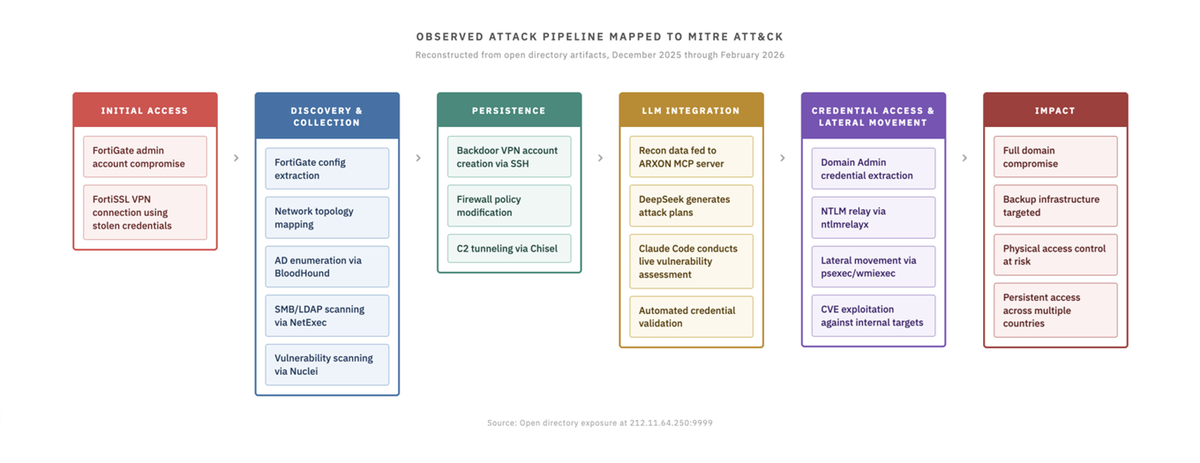
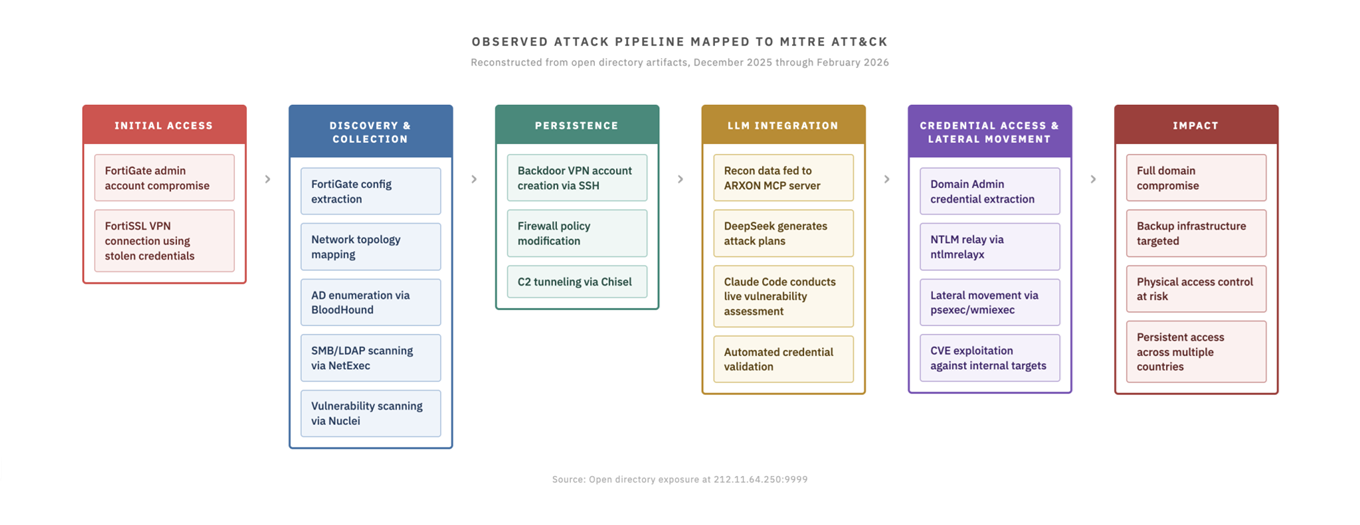
Amazon is warning that a Russian-speaking hacker used multiple generative AI services as part of a campaign that breached more than 600 FortiGate firewalls across 55 countries in five weeks.
A new report by CJ Moses, CISO of Amazon Integrated Security, says that the hacking campaign occurred between January 11 and February 18, 2026, and did not rely on any exploits to breach Fortinet firewalls.
Instead, the threat actor targeted exposed management interfaces and weak credentials that lacked MFA protection, then used AI to help automate access to other devices on the breached network.
Moses says the compromised firewalls were observed across South Asia, Latin America, the Caribbean, West Africa, Northern Europe, and Southeast Asia, among other regions.
Amazon says it learned about the campaign after finding a server hosting malicious tools used to target Fortinet FortiGate firewalls.
As part of the campaign, the threat actor targeted FortiGate management interfaces exposed to the internet by scanning for services running on ports 443, 8443, 10443, and 4443. The targeting was reportedly opportunistic rather than against any specific industries.
Rather than exploiting zero-days, as we commonly see targeting FortiGate devices, the actor used brute-force attacks with common passwords to gain access to devices.
Once inside, the threat actor used a variety of tools to automate reconnaissance on the breached networks by analyzing routing tables, classifying networks by size, running port scans using the open-source gogo scanner, identifying SMB hosts and domain controllers, and using Nuclei to look for HTTP services.
The researchers say that while the tools were functional, they commonly failed in more hardened environments.
Operational documentation written in Russian detailed how to use Meterpreter and mimikatz to conduct DCSync attacks against Windows domain controllers and extract NTLM password hashes from the Active Directory database.
Separate research published on the Cyber and Ramen security blog provides additional technical details about how AI and large language models were incorporated directly into the intrusion campaign.
The researcher shared that the misconfigured server at 212.11.64[.]250, also found by Amazon, exposed 1,402 files, including stolen FortiGate configuration backups, Active Directory mapping data, credential dumps, vulnerability assessments, and attack planning documents.
"The server at 212.11.64[.]250:9999, hosted on AS4264 (Global-Data System IT Corporation, Zurich, Switzerland), contained 1,402 files across 139 subdirectories," explained the threat researcher.
In the exposed files was a custom Model Context Protocol (MCP) server named ARXON, which acted as a bridge between reconnaissance data and commercial large language models. The researcher said they were unable to find any public references to ARXON, indicating it was likely a custom MCP framework created by the threat actor.
CronUp security researcher Germán Fernández also found a different server exposing a directory containing what appear to be AI-generated tools targeting FortiWeb. These tools do not appear to be part of the FortiGate campaign. (Lawrence Abrams / Bleeping Computer)
Related: Amazon Web Services, Bloomberg, Tech in Asia, The Hacker News, NextBigWhat, Cyber Security News, Cyber and Ramen, Steve Schmidt on LinkedIn
Spanish police say four self-proclaimed members of Anonymous are in custody after allegedly carrying out several cyberattacks on public authorities in the wake of the 2024 DANA floods.
Guardia Civil officers arrested two of Anonymous Fénix's "most active members" last week in Ibiza and Móstoles, Madrid. These bring the total to four, following the arrest of two group leaders in Alcalá de Henares, Madrid, and Oviedo, Asturias, in May 2025.
All four were detained for carrying out distributed denial-of-service (DDoS) attacks on government ministries, political parties, and public institutions, which they claimed were "responsible for the tragedy" of the floods.
The police declined to name any of the four members, but a court order allowed the seizure of Anonymous Fénix's X profile and YouTube account, and officials closed its Telegram account. (Connor Jones / The Register)
Related: Guardia Civil, Euronews

Las Vegas hotel and casino giant Wynn Resorts appears to be the latest victim of data-grabbing and extortion gang ShinyHunters.
On Friday, the cybercrime crew listed the hospitality company on its blog, claiming to have stolen more than 800,000 records containing employees' Social Security numbers and other private details. The extortionists set a February 23 deadline for Wynn to "reach out" and threatened to leak the data, "along with several annoying (digital) problems that'll come your way," if the resort chain did not comply with the demands.
Samples of the stolen data seen by The Register contain employees' full names, emails, phone numbers, positions, salaries, start dates, birthdays, and other personal information.
Wynn Resorts, which owns five resorts, 81 restaurants, and 200 high-end retail outlets, did not immediately respond to The Register's inquiries. We will update this story when we hear back from the company.
ShinyHunters set a fee of 22.34 Bitcoin (about $1.5 million) as the "starting price" for the stolen files, according to a spokesperson for the crime group, who told The Register that the digital intruders gained initial access to Wynn's systems in September 2025 via an Oracle PeopleSoft vulnerability using an employee's credentials.
Shiny declined to say if it got the Wynn employee to give up the credentials via a social engineering trick or paid the individual for access. The group has previously used Telegram to solicit insider access, and in one case reportedly claimed it agreed to pay a CrowdStrike employee $25,000 for access, though the security shop said no systems were breached.
The claimed Wynn Resorts breach follows a slew of recent ShinyHunters intrusions, several of which involved voice phishing to obtain single-sign-on codes from users of Okta, Microsoft, and Google services.
It's also notable that nearly three years ago, a group with ties to ShinyHunters' crime collaborative hacked two other major Vegas hotel and casino chains: Caesars Entertainment and MGM Resorts. (Jessica Lyons / The Register)
Related: Gambling News, Casino.org, Hoodline, Nevada Globe
PayPal is notifying customers of a data breach after a software error in a loan application exposed their sensitive personal information, including Social Security numbers, for nearly 6 months last year.
The incident affected the PayPal Working Capital (PPWC) loan app, which provides small businesses with quick access to financing.
PayPal discovered the breach on December 12, 2025, and determined that customers' names, email addresses, phone numbers, business addresses, Social Security numbers, and dates of birth had been exposed since July 1, 2025.
The financial technology company said it has reversed the code change that caused the incident, blocking attackers' access to the data one day after discovering the breach.
"On December 12, 2025, PayPal identified that due to an error in its PayPal Working Capital ("PPWC") loan application, the PII of a small number of customers was exposed to unauthorized individuals during the timeframe of July 1, 2025, to December 13, 2025," PayPal said in breach notification letters sent to affected users.
PayPal also detected unauthorized transactions on the accounts of a small number of customers as a direct result of the incident and has issued refunds to those affected.
The company now offers affected users two years of free three-bureau credit monitoring and identity restoration services through Equifax, which require enrollment by June 30, 2026.
PayPal has also reset passwords for all impacted accounts and said that users will be prompted to create new credentials upon their next login if they have not already done so. (Sergiu Gatlan / Bleeping Computer)
Related: Security Week, WION, Forbes, The Register, Cyber Press
The United Arab Emirates said it has thwarted organized cyber attacks targeting the country's digital infrastructure and vital sectors.
The attacks "included attempts to infiltrate networks, deploy ransomware and conduct systematic phishing campaigns targeting national platforms," and involved artificial intelligence technologies to develop offensive tools, it added. The report did not say who was to blame for the attacks. (Ahmed Elimam and Hatem Maher / Reuters)
Related: The Cyber Express, The Times of India, Gulf News, The Hindu, Tribune India, Islam Times, Intelligent CIO, Firstpost, Dawn, Bloomberg, Jerusalem Post
Italian police said they had detected cyberattacks against the interior ministry seeking information on dissident Chinese citizens and officers investigating Chinese groups in Italy.
“No sensitive data related to operational activities appears to have been taken,” police said in a statement, saying their findings had been passed to judicial authorities.
They did not give a timeframe. but the La Repubblica daily had earlier reported that the interior ministry suffered a cyber-attack between 2024 and 2025. (AFP)
Related: Decode39, Techpression, dpa International
Shares of cybersecurity software companies tumbled Friday after Anthropic PBC introduced a new security feature into its Claude AI model.
Crowdstrike Holdings was among the biggest decliners, falling 8%, while Cloudflare Inc. slumped 8.1%. Meanwhile, Zscaler dropped 5.5%, SailPoint shed 9.4%, and Okta Inc. declined 9.2%. The Global X Cybersecurity ETF fell 4.9% and closed at its lowest since November 2023.
Anthropic said the new tool “scans codebases for security vulnerabilities and suggests targeted software patches for human review.” The firm said the update is available in a limited research preview for now.
Jefferies analyst Joseph Gallo expects cybersecurity will ultimately be a net winner from AI, but “headline headwinds are likely to intensify before clarity & cyber inflection from securing AI materializes.”
The broader implications of Anthropic’s announcement, he added, are that AI providers “will announce more products & compete for incremental cyber budget dollars.” (Ryan Vlastelica / Bloomberg)
Related: Anthropic, CTech, Investor's Business Daily, Silicon Angle, Fortune, PCMag, Help Net Security, DevOps.com, CyberScoop
The English-language edition of Wikipedia is denylisting Archive. today after the controversial archive site was used to direct a distributed denial of service (DDoS) attack against a blog.
In the course of discussing whether Archive. today should be deprecated because of the DDoS, Wikipedia editors discovered that the archive site altered snapshots of webpages to insert the name of the blogger who was targeted by the DDoS. The alterations were apparently fueled by a grudge against the blogger over a post that described how the Archive. Today, the maintainer hides their identity behind several aliases.
“There is consensus to deprecate the archive immediately. today, and, as soon as practicable, add it to the spam denylist (or create an edit filter that blocks adding new links), and remove all links to it,” stated an update today on Wikipedia’s Archive. today discussion. “There is a strong consensus that Wikipedia should not direct its readers towards a website that hijacks users’ computers to run a DDoS attack (see WP:ELNO#3). Additionally, evidence has been presented that archive. today’s operators have altered the content of archived pages, rendering it unreliable.”
More than 695,000 links to Archive. today are distributed across 400,000 or so Wikipedia pages. The archive site is commonly used to bypass news paywalls, and the FBI has sought information on the site operator’s identity with a subpoena to domain registrar Tucows. (Jon Brodkin / Ars Technica)
Related: Wikipedia, TechCrunch, Tech in Asia, PCMag, Tom's Hardware, r/chaoticgood, r/LinusTechTips, r/skeptic, r/wikipedia, r/france, r/GamePreservationists, r/technews, r/technology, Lobsters, Slashdot, Ars OpenForum, Hacker News (ycombinator), Pixel Envy
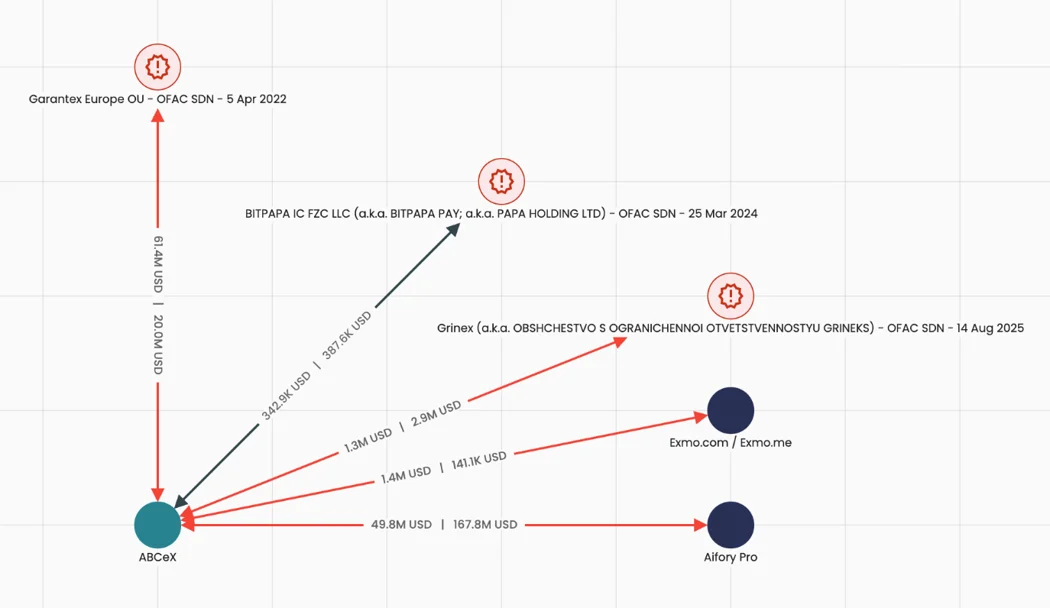
Five crypto exchanges are allegedly helping Russians skirt international sanctions, filling a vacuum left by Russian exchange Garantex after it was taken down last year, according to crypto analytics firm Elliptic.
Elliptic said that the crypto exchanges Bitpapa, ABCeX, Exmo, Rapira, and Aifory Pro are allowing Russian ruble-to-crypto conversions. The crypto can then be transferred across borders “without passing through any intermediaries” and converted to another fiat currency.
“Despite growing regulatory pressure, many of these exchanges, some with nominal registrations outside Russia, still facilitate high volumes of cryptoasset trading linked to sanctioned entities,” the company said.
The network reportedly sprang up after authorities took down the Russian exchange Garantex’s website in March, which was heavily sanctioned in mid-2022 for facilitating crypto linked to illicit activity and helping Russia skirt sanctions imposed after the country invaded Ukraine that year.
Chainalysis reported last month that sanctions had pushed the total value of crypto received by illicit addresses in 2025 to $154 billion — the highest-ever figure — due to “unprecedented volumes associated with nation-states.” (Jesse Coghlan / Cointelegraph)
Related: Elliptic, Cryptonews, The Block, BeInCrypto, crypto.news, Blockonomi, Cointelegraph
Sergey Zolotukhin, an expert at F6 cybersecurity company, said attackers can penetrate "smart" vacuum cleaners through router vulnerabilities or a weak Wi-Fi password, and then gain access to all gadgets on the network.
According to Zolotukhin, it is impossible to determine a hack visually — the vacuum cleaner will continue to clean the apartment properly. The main goal of hackers is to obtain personal data that can be used for blackmail or manipulation. If the device has a microphone and camera, they can technically be activated for surveillance, even if it is programmatically prohibited.
He emphasized that security depends only on the users themselves — their cyber literacy and responsible attitude to "smart assistants." (www1.ru)
Related: En.iz.ru, Logos Press
The Cyber Investigation Unit of the Seoul Metropolitan Police Agency announced that the perpetrators who leaked the personal information of 4.62 million users of Seoul’s public bicycle service “Ttareungyi” were identified as teenagers in their 10s, not a professional hacking organization.
The unit said that it had arrested high school students A and B on charges of violating the Information and Communications Network Act and referred them to the prosecution without detention and referred them to the prosecution without detention on charges of infiltrating the Ttareungyi server and stealing user data (violation of the Information and Communications Network Act).
According to police, the two suspects, who met through Telegram, conspired to commit the crime while self-studying in the field of information security. No connections to professional hacking groups or access to the dark web were found.
They accessed the server in June 2024 by exploiting vulnerabilities in Ttareungyi’s weak authentication process and retrieved user information by querying member data.
The leaked data included IDs, mobile phone numbers, email addresses, residential addresses, birthdates, genders, and weights—approximately 4.62 million records. It was confirmed that unique identifiers such as names or resident registration numbers were not included.
This case came to light during a separate cybercrime investigation. While arresting suspect B on charges of conducting a DDoS attack against another shared mobility service provider, police discovered Ttareungyi-related data during an analysis of seized electronic devices. This led to the identification of accomplice A through online account tracking.
Regarding the motive, suspect B stated during police questioning, “I committed the crime out of curiosity and a desire to show off.” Suspect A, however, refused to make a statement. The police applied for a bench warrant twice for A, but it was not issued due to considerations regarding his status as a juvenile offender. (Koo A-mo / The Chosun Daily)
Related: Maeil Business Newspaper, The Asia Business Daily
The Grand Hotel in Taipei warned customersof a possible data breach after discovering unauthorized access to its information systems earlier this week.
In a statement, the hotel said it was issuing the notice as a precaution, especially given that the scope and targets of the attack have yet to be fully assessed, while also apologizing to people for any concern caused by the situation.
According to the hotel, when it discovered the attack, it activated its highest-level cybersecurity response measures.
They included disconnecting affected systems, conducting a comprehensive security review, strengthening account and access management, notifying the competent authorities, and requesting the Ministry of Justice Investigation Bureau to investigate the incident. (Liu Shih-yi and Wu Kuan-hsien / Focus Taiwan)
Related: Taipei Times, Taiwan News, Travel Weekly Asia
According to the 2026 Global Automotive and Smart Mobility Cybersecurity Report by Upstream Security, 44% of last year’s automotive and smart mobility incidents were ransomware-related, more than double the share recorded in 2024.
Ninety-two percent of attacks were conducted remotely, and most required no physical proximity to the vehicle.
The firm analyzed 494 publicly reported incidents worldwide and found what it describes as a “material escalation” in risk, driven by expanded APIs, AI-driven architectures, and increasingly organized threat actors.
“AI is also enabling attackers to move faster, at greater scale, and with more automation while the industry is still relying on security models built for a far more static world,” said Yoav Levy, Co-Founder and CEO of Upstream, in a statement.
Upstream’s report found that 67% of incidents involved telematics and cloud systems, underscoring that exposure increasingly sits in backend infrastructure, APIs, and remote management platforms rather than in physical tampering with vehicles.
Upstream’s report notes that some of 2025’s most severe incidents triggered operational disruptions across manufacturers and suppliers. In one case, a cyberattack on a European OEM reportedly halted production for weeks and had broader economic effects. (Zachy Hennessey / CTech)
Related: Upstream Security, IoT Business News, Collision Repair Mag, Canadian Auto Dealer
After the public outcry against its move to require users to show government IDs or video selfies to be processed by an age-assurance vendor, Persona, Discord is now backing away from this supplier.
Critics warned that Palantir co-founder Peter Thiel’s Founders Fund was a major investor in Persona, and security researchers discovered that frontend components tied to identity vendor Persona were accessible on the open web, prompting debate over how securely the platform handles sensitive age checks.
“In 2,456 publicly accessible files, the code revealed the extensive surveillance Persona software performs on its users, bundled in an interface that pairs facial recognition with financial reporting—and a parallel implementation that appears designed to serve federal agencies,” the researchers reported.
Beyond offering simple services to estimate your age, Persona’s exposed code compares your selfie to watchlist photos using facial recognition, screens you against 14 categories of adverse media from mentions of terrorism to espionage, and tags reports with codenames from active intelligence programs consisting of public-private partnerships to combat online child exploitative material, cannabis trafficking, fentanyl trafficking, romance fraud, money laundering, and illegal wildlife trade.
In addition to facial recognition, Persona’s software is able to perform checks on financial data — including running checks on sanctions lists, running checks on cryptocurrency activity via the blockchain analysis firms Chainalysis and TRM Labs, and an interface to file suspicious activity reports (SARs) directly with US and Canadian federal agencies.
However, Discord now says that only a small number of users were included in the experiment, which ran for less than one month. That test has since concluded, Discord confirmed, and Persona is no longer an active vendor partnering with Discord. Moving forward, Discord promised to “keep our users informed as vendors are added or updated.” (L0la L33tz / The Rage and Ashley Belanger / Ars Technica)
Related: Hot Hardware, Kotaku, Interesting Engineering, PC Gamer
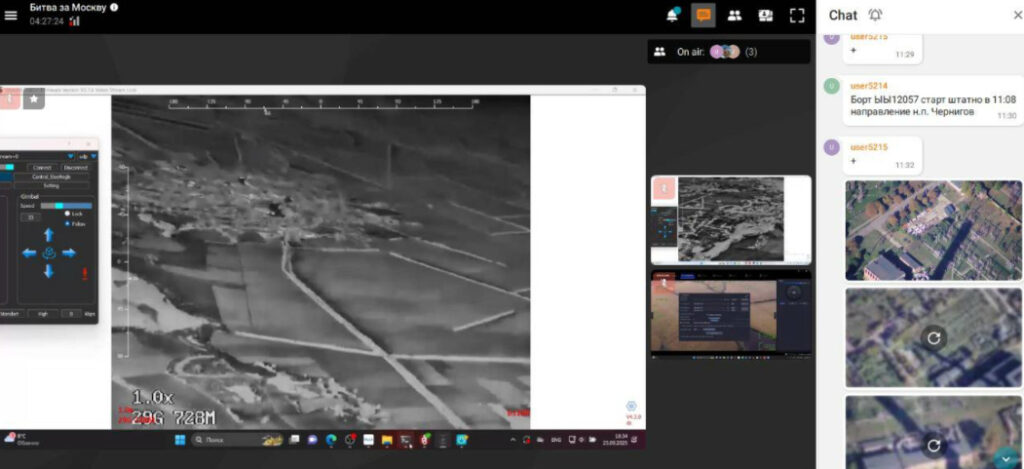
Inform Napalm reported that Ukrainian hackers infiltrated Russian drone operator systems for six months, exposing how Russia weaponized Belarusian civilian infrastructure to strike Ukraine and test attack routes into NATO countries.
The cyber operation was carried out by hackers from the Fenix analytical cyber center with support from InformNapalm volunteers. The team broke into accounts of dozens of Russian military personnel and gained access to monitoring systems used by attack drone operators, InformNapalm says. They organized round-the-clock covert surveillance, carefully hiding their presence.
The cyber operation was carried out by hackers from the Fenix analytical cyber center with support from InformNapalm volunteers. The team broke into accounts of dozens of Russian military personnel and gained access to monitoring systems used by attack drone operators, InformNapalm says. They organized round-the-clock covert surveillance, carefully hiding their presence.
Analysis of intercepted chats revealed Russia was using Belarusian civilian cell towers to route strike drones, providing a stable signal along the border and extending strike range to targets near northern and western Ukraine's borders. Russia also deployed signal repeaters on Belarusian territory in the second half of 2025, reaching targets from Kyiv Oblast to Volyn. Some attacks on energy and railway infrastructure would not have been possible without this assistance. (Yuri Zoria / Euromaidan)
Related: Inform Napalm
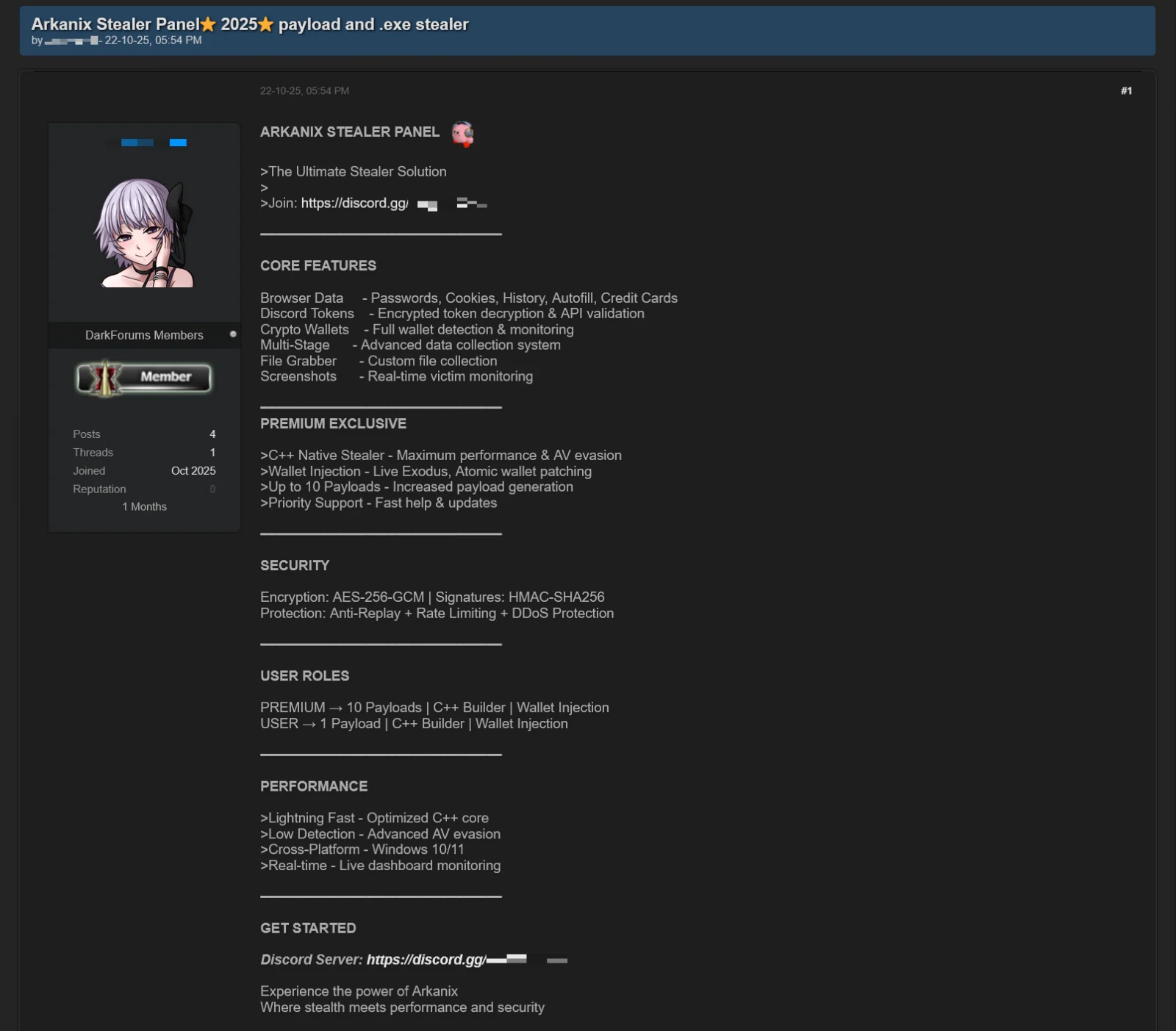
Researchers at Kaspersky report that an information-stealing malware operation named Arkanix Stealer, promoted on multiple dark web forums towards the end of 2025, was likely developed as an AI-assisted experiment.
Arkanix started being promoted on hacker forums in October 2025, offering two tiers to potential customers: a basic level with a Python-based implementation, and a “premium” one with a native C++ payload using VMProtect protection, integrating AV evasion and wallet injection features.
The project included a control panel and a Discord server for communication with users, but the author took them down without notification, just two months after the operation began.
Arkanix offered many of the standard data-stealing features that cybercriminals are used to, along with a modular architecture and anti-analysis features.
The researchers found clues indicating LLM-assisted development, which "might have drastically reduced development time and costs." They believe that Arkanix was a short-lived project for quick financial gains, which makes detection and tracking much more difficult.
Arkanix malware can collect system information, steal data stored in the browser (history, autofill info, cookies, passwords), and cryptocurrency wallet data from 22 browsers. Kaspersky researchers say that it can also extract 0Auth2 tokens on Chromium-based browsers. (Bill Toulas / Bleeping Computer)
Related: Securelist
The University of Mississippi Medical Center (UMMC) announced that its clinics will remain closed on Monday, Feb. 23, and Tuesday, Feb. 24, following a ransomware cyberattack that hit its information technology systems and led to an initial closure of all 35 statewide locations on Thursday, Feb. 19.
UMMC shared that its internal groups are collaborating with national cybersecurity experts and national and state agencies to respond to last week’s attack.
“Our phone systems and ability to receive or send emails remain down or unreliable,” the press release said. “The UMMC Emergency Departments and hospitals in Jackson, Madison County, Grenada, and Holmes County are open and caring for patients. The Medical Center is actively working on a solution for patients who need to contact us with routine medical and/or medication needs.”
UMMC has also reached out to patients in need of time-sensitive care to receive treatment. Elective, non-emergency appointments were canceled on Feb. 19. (Clay Hale / The Daily Mississippian)
Related: Tippah News, Super Talk
Rest in Power: Farewell to One of the OG Hackers
Jason Snitker, AKA Parmaster, a legend in the early underground hacking scene, has departed this earthly realm.
A teenager from Salinas, California, who breached Citibank, slipped into defense contractor networks at TRW, traded exploits with groups across four continents, evaded the United States Secret Service for over two years, did time at Rikers Island—where he taught murderers how to play Dungeons & Dragons—and then reinvented himself as a cyber defense professional.
Best Thing of the Day: Action Is Better Than Inaction
Regulatory scrutiny of South Korea's online platform industry is intensifying following a personal data breach at Coupang, raising concerns that expanding oversight could dampen innovation among startups.
Worst Thing of the Day: How to Steal $1.5 Billion and Face No Consequences
A year after the $1.46 billion Bybit theft, the DPRK's cryptoasset theft operation continues with no sign of slowing down.
Bonus Worst Thing of the Day: Making Sure Lawyers Don't Get Paid
UK justice minister Sarah Sackman has said that legal aid solicitors in the UK will not be compensated for losses related to the cyberattack on the UK Legal Aid Agency last year.
Closing Thought