ShinyHunters hits Rockstar Games, threatens data dump after cloud breach
Basic-Fit data breach exposes data on 1m+ members, Operation Atlantic disrupted $45m pig butchering network, Hackers exploited Hyberbridge flaw for $237k gain, Booking [dot] com suffered breach exposing customer details, UK finance regulators are assessing Anthropic's Claude Mythos, much more


Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
Grand Theft Auto developer Rockstar Games confirmed an attack claimed by the virulent cybercriminal group ShinyHunters, marking the second time in three years hackers have targeted the company.
The criminals said they gained access to Rockstar servers managed by a third-party cloud provider and would publish stolen material online unless paid a ransom.
But Rockstar, confirming the hack to gaming publication Kotaku, downplayed the breach - saying "this has no impact on our organisation or our players".
"We can confirm that a limited amount of non-material company information was accessed in connection with a third-party data breach," a Rockstar spokesperson told the outlet.
ShinyHunters said the stolen data would be published online as their demands had not been met. (Liv McMahon and Joe Tidy / BBC News)
Related: The Express Tribune, heise online News, Forbes, PC Games, TweakTown, Polygon, Times of India, Video Games Chronicle, Insider Gaming, Games Industry.biz, The Verge, Engadget, HackRead, IGN, Kotaku, GamerBraves, ETV Baharat, GameReactor, Gadgets360, The Cyber Express, Gameranx, Gosu Gamers, Auto Evolution, Cyber Daily, News Bytes, FirstPost, The Verge, Men's Journal, TechSpot, The Register, Moneycontrol, The CyberSec Guru, Video Games Chronicle, Mirror, The Indian Express, TechRadar, The Movie Blog, The Cyber Express, Gameranx, Digital Trends, Hackread, GamingBolt, Forbes, XDA Developers, The Verge, TechSpot, IGN, Neowin, VideoCardz.com, Tom's Hardware, Rock, Paper, Hacker News, r/GameFeed, BBC News
Gym operator Basic-Fit has suffered a data breach involving around 1 million members , with 200,000 in the Netherlands alone, a company spokesperson said.
Basic-Fit owns gyms serving over 4.5 million customers across six European countries, including France, Germany, and Spain. It also runs a franchise model in six other countries, which uses a separate system and was not affected by the leak.
The breach involves members' bank account details, names, birth dates, and contact information.
Basic-Fit says the unauthorized access was detected by its system monitoring tools and was stopped within minutes. (Jakob Van Calster / Reuters)
Related: The Next Web, WTVB, Global Banking and Finance, NL Times, Gadgets Now
US, UK, and Canadian law enforcement said that they disrupted a $45 million global cryptocurrency scam, freezing $12 million in stolen funds and identifying more than 20,000 cryptocurrency wallet addresses linked to so-called pig butchering fraud victims across 30 countries.
The week-long effort, dubbed Operation Atlantic, also identified an additional $33 million believed to be linked to investment fraud schemes and will further investigate these funds.
Operation Atlantic is a joint initiative led by the US Secret Service, the UK National Crime Agency, the Ontario Provincial Police, and the Ontario Securities Commission, working with private‑sector partners, to identify and contact potential victims and help them recover stolen funds.
Over the course of the operation, international cops identified and directly contacted more than 3,000 victims and returned $12 million to their wallets. (Jessica Lyons / The Register)
Related: US Secret Service, NCA, Ontario Provincial Police, Wired-Gov, SC Media, TRM Labs, Elliptic, Bitbo, Cryptorank, Decrypt

Hackers have exploited a vulnerability in the Hyperbridge gateway contract to mint 1 billion unauthorized bridged DOT tokens on Ethereum, according to onchain analysts.
Hyperbridge is a cross-chain interoperability protocol built on Polkadot.
Blockchain security firm CertiK reported the exploit targeting the Hyperbridge gateway contract, in which a vulnerability allowed the attacker to forge messages and seize administrative control of the token contract on Ethereum.
The attackers then minted 1 billion DOT (Polkadot) tokens on Ethereum and quickly sold them, profiting approximately $237,000, according to CertiK. (Timmy Shen / The Block)
Related: Cryptonews.net, r/CryptoCurrency, The Street, Bitcoin Foundation, Bloomingbit, CryptoRank, CryptoPotato, The Cryptonomist, Forklog, Yellow
The accommodation reservation website Booking.com has suffered a data breach with “unauthorised parties” gaining access to customers’ details.
The platform said it “noticed some suspicious activity involving unauthorised third parties being able to access some of our guests’ booking information”.
“Upon discovering the activity, we took action to contain the issue,” it said. “We have updated the PIN number for these reservations and informed our guests.”
The company, which is headquartered in Amsterdam, lists more than 30m accommodation venues around the world and says it connects “millions of travellers” with experiences, transport and places to stay.
An email from the company to affected customers said the hackers may have been able to access “certain booking information” associated with a previous reservation the customer made.
“Based on the findings of our investigation to date, accessed information could include booking details and names, emails, addresses, phone numbers associated with the booking, and anything that you may have shared with the accommodation,” it said. (Lauren Almeida / The Guardian)
Related: News.com, RNZ, Sky News, 9News, ABC.net.au, Techzine, Perth Now, IB Times
British financial regulators are holding urgent talks with the government's cyber security agency and major banks to assess risks posed by the latest artificial intelligence model from Anthropic, the Financial Times reported.
Bank of England, Financial Conduct Authority and Treasury officials are in talks with the National Cyber Security Centre to examine potential vulnerabilities in critical IT systems highlighted by Anthropic's latest AI model, the FT said, citing two people briefed on the talks.
Representatives from major British banks, insurers, and exchanges are expected to be briefed on the cybersecurity risks posed by the model, Claude Mythos Preview, at a meeting with regulators in the next fortnight, the newspaper said. (Mihika Sharma / Reuters)
Related: Business Today, Benzinga, Security Boulevard, France 24, TechCrunch, New York Times, Financial Times
Japanese shipping giant NYK posted a notice that the marine fuel procurement system it used was accessed without authorization by a third party.
As a result, certain data — including personal information — was accessed and exfiltrated.
The company said it detected the unauthorized access on the afternoon of 24 March.
“It was determined that certain data, including personal information, may have been taken from the system. Upon discovering the breach, we immediately isolated the system from the network and suspended its use,” the company said in the notice.
The system was restored on 27 March 27 and on the same day, the company submitted a preliminary report to the Personal Information Protection Commission of Japan and other relevant authorities in the applicable jurisdictions as necessary. (Manifold Times)
Related: NYK, Ship and Bunker, ship.energy
The Iran-linked hacker group Handala claimed to have launched a large-scale cyberattack against three Dubai government organizations, alleging it destroyed six petabytes of data and extracted 149 terabytes of classified documents.
The group said in a statement on April 12 that it had targeted the Dubai Courts Department, Dubai Land Department, and Dubai Roads and Transport Authority, describing the attack as retaliation for what it called the UAE's "betrayal of the Resistance Axis."
Handala claimed the operation had caused "unprecedented and widespread disruptions" to the targeted organizations and wider city operations.
The group said six petabytes of data had been "completely destroyed and rendered irrecoverable." (Intellinews)
Related: Presstv
The French government said it plans to move some of its government computers currently running Windows to the open source operating system Linux to reduce its reliance on US technology further.
In a statement, French minister David Amiel said (translated) that the effort was to “regain control of our digital destiny” by relying less on US tech companies. Amiel said that the French government can no longer accept that it doesn’t have control over its data and digital infrastructure.
This move is the latest effort by France to reduce its dependence on US tech giants and use technology and cloud services originating within its borders, known as digital sovereignty, following growing instability and unpredictability on the part of the Trump administration. (Zack Whittaker / TechCrunch)
Related: Numerique.gov.fr, Linuxiac, Tom's Hardware, XDA Developers, MakeUseOf, PC Gamer, Engadget, Gadget Review, Gizmodo, Cyber Security News, Implicator.ai, It's FOSS, The Verge, Pixel Envy
Dutch police arrested eight men on suspicion of identity fraud, forgery, and cybercrime this week in connection with a multi-million-dollar fake ID platform that generated nearly a million forged documents for scammers worldwide.
The nationwide operation, carried out on April 7 and 8, targeted users of VerifTools, a now-shuttered website that allowed users to enter false personal data and generate fake identity documents, according to a Dutch National Police statement.
“Images of documents purchased via the site are used by criminals for various forms of crime, including phishing and bank helpdesk fraud,” authorities said.
Nine additional suspects—seven men and two teenage girls—have been summoned to report to police. During searches, officers seized electronic devices, cash, cryptocurrency, weapons, or items resembling them. (James Dowsett / OCCRP)
Related: Politie, Help Net Security
Almost 800 Hungarian government email addresses and associated passwords are circulating online, revealing basic vulnerabilities in the security protocols of ministries involved in classified and sensitive work.
A Bellingcat analysis of breach data shows that 12 out of the government’s 13 ministries have been affected, which, in some cases, have exposed the confidential information of military personnel and civil servants posted abroad.
Among those affected were a senior military officer responsible for information security, a counter terrorism coordinator in the foreign affairs department, and an employee whose role was to identify hybrid threats against the country.
The revelations come ahead of Hungarians heading to the polls yesterday to decisively vote out of office Viktor Orbán, the leader of the right-wing populist party Fidesz and the country’s longest-serving prime minister. (Bellingcat)
Related: The Register, Sri Lanka Guardian, CSO Online
Researchers at Sysdig report that hackers started exploiting a critical vulnerability in the Marimo open-source reactive Python notebook platform just 10 hours after its public disclosure.
The flaw allows remote code execution without authentication in Marimo versions 0.20.4 and earlier. It tracked as CVE-2026-39987 and GitHub assessed it with a critical score of 9.3 out of 10.
CVE-2026-39987 is caused by the WebSocket endpoint ‘/terminal/ws’ exposing an interactive terminal without proper authentication checks, allowing connections from any unauthenticated client.
According to Sysdig, attackers created an exploit from the information in the developer's advisory and immediately started using it in attacks that exfiltrated sensitive information.
Marimo users are recommended to upgrade to version 0.23.0 immediately, monitor WebSocket connections to ‘/terminal/ws,’ restrict external access via a firewall, and rotate all exposed secrets. (Bill Toulas / Bleeping Computer)
Related: Sysdig, Security Week, Rescana, Security Affairs
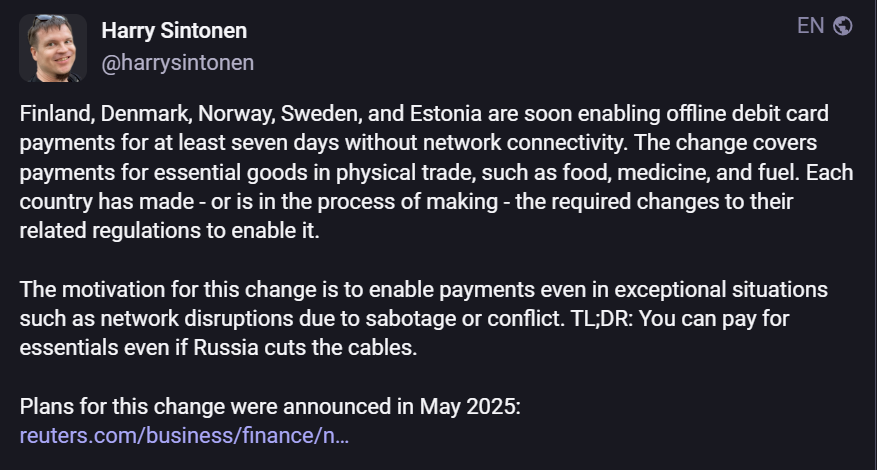
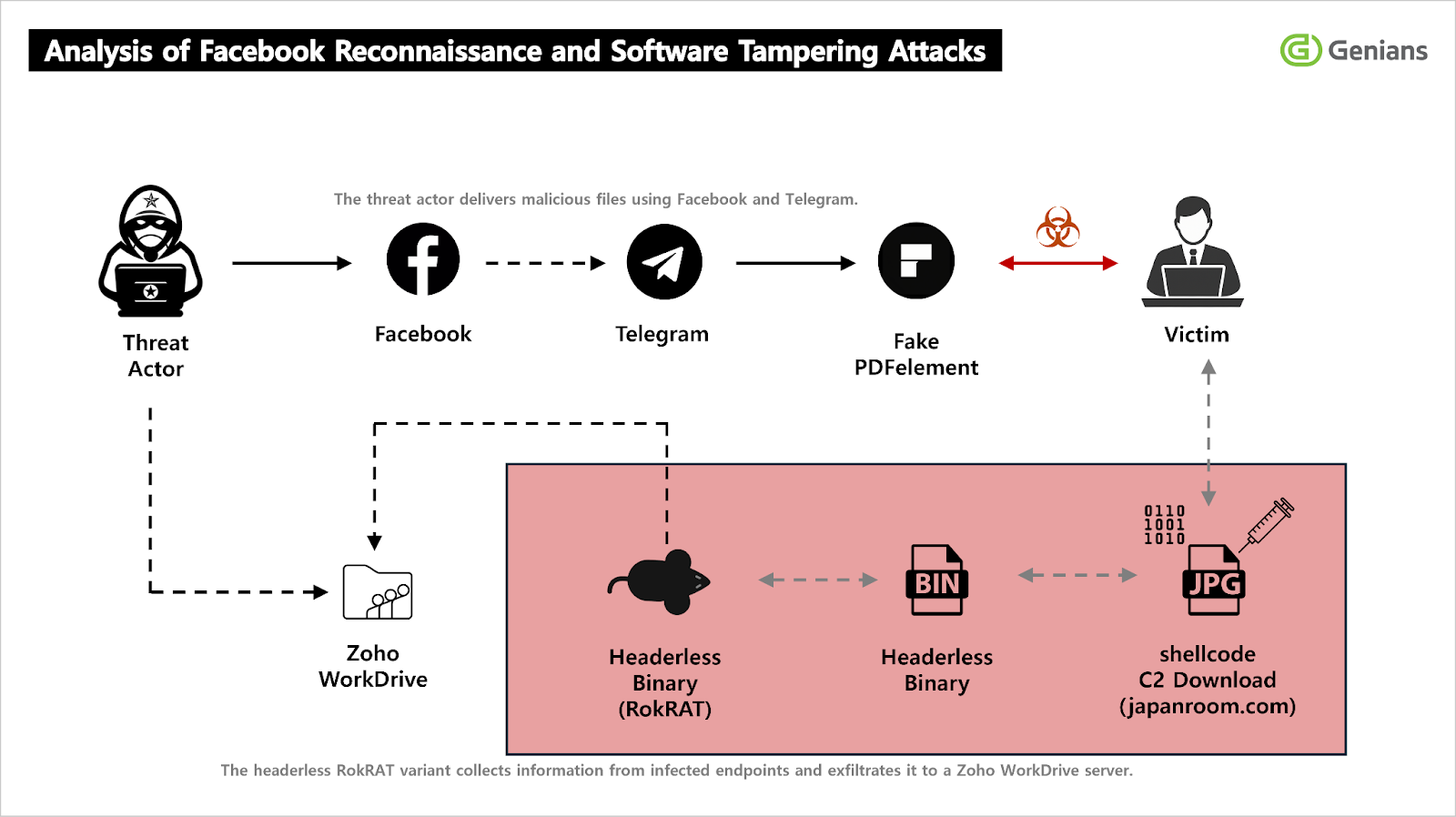
According to Genians Research Center, North Korea's APT37 is running a new social-engineering-driven cyber‑espionage campaign that abuses Facebook, Telegram, and a trojanized Wondershare PDFelement installer to deliver a RokRAT‑like backdoor and exfiltrate sensitive data via Zoho WorkDrive.
The operation shows a clear evolution of APT37’s long‑standing TTPs toward social‑network reconnaissance, tampered installers, and multi‑stage, fileless payload delivery.
Genians analyzed a recent intrusion campaign in which APT37 used two Facebook accounts listing Pyongyang and Pyeongtaek, North Korea, as their locations to identify and screen targets in defense‑related sectors. (Varshini / CyberPress)
Related: Genians, Korea JoongAng Daily, GBHackers
OpenAI said that it found evidence that one of its internal tools downloaded a compromised update from a recently infected, legitimate open-source software library.
The incident could have allowed hackers to exfiltrate a certificate that could make phony OpenAI apps look legitimate — although OpenAI says it hasn't seen this happen.
Researchers at Google linked the broader campaign to a North Korean group tracked as UNC1069.
OpenAI said that a GitHub workflow that the company uses to sign certificates for MacOS applications downloaded a malicious update from the Axios software on March 31. Axios, a widely used JavaScript library for making HTTP requests, is not affiliated with Axios Media. (Sam Sabin / Axios)
Related: OpenAI, Livemint, 9to5Mac, Reuters
Sources say Palo Alto Networks founder Nir Zuk agreed to buy local California lender Liberty Bank, with plans to use Liberty as a launchpad for artificial-intelligence tools aimed at financial services.
Zuk has sought approval from US regulators to acquire the largest stake in Liberty from private-equity firms Stone Point Capital and Reverence Capital Partners, the people said. Betsy and Daniel Cohen, the mother-and-son fintech entrepreneurs, also plan to invest in the deal, the people said.
The planned acquisition is a fusion of several investment themes Zuk has pursued outside of his role at cybersecurity giant Palo Alto. He is the co-founder of eOS, an AI-agentic platform, and brought the startup’s technology to Esh Bank, an Israeli lender and one of his other investments. Esh recently agreed to sell itself to Isracard, Israel’s biggest credit-card company.
People familiar with Zuk’s thinking said the technologist was eager to invest in a US banking industry on the cusp of its embrace of artificial intelligence. (Justin Baer / The Wall Street Journal)
Cisco Systems is in talks to acquire Astrix Security, a five-year-old Israeli cybersecurity startup that sells software to monitor and secure AI agents, for between $250 million and $350 million, according to people with knowledge of the deal.
That would represent at least a 25% premium to the startup’s last valuation of around $200 million, one of the people said. (Valida Pau and Stephanie Palazzolo / The Information)
Best Thing of the Day: Burst the Hype Bubble Surrounding Iran's Supposed Cyber Prowess
Georgia Institute of Technology professor Jon R. Lindsay appears to be the sole source of reason in the media in arguing that Iran lacks cybersecurity prowess and is at a relative disadvantage when it comes to cyberwarfare.
Worst Thing of the Day: Please God, No, One Mark Zuckerberg Is Too Much As It Is
Meta is building an artificial intelligence version of Mark Zuckerberg that can engage with employees in his stead, as part of a broader push to remake the Big Tech company around AI.
Bonus Worst Thing of the Day: You Can't Get Sober or Naked These Days Without Everyone Knowing
WebinarTV, a site that scrapes Zoom webinars without permission, has downloaded and posted Zoom Webinars for anonymous addiction recovery meetings, support groups for caregivers and people who suffer from chronic illness, and a meeting of nudists.
Closing Thought