Snowflake Hackers Demand Up to $5 Million as Hacking Scheme Enters Extortion Stage

Signal president says EU CSAM scanning threatens web security, DragonForce hit Oahu transit services with ransomware attack, Cleveland still coping with ransomware attack, Law enforcement portal hackers plead guilty, Cryptoscammers target Trump supporters, New malware campaign uses fake browsers, Suspected Chinese actors targeting F5 BIG-IP appliances for espionage, much more

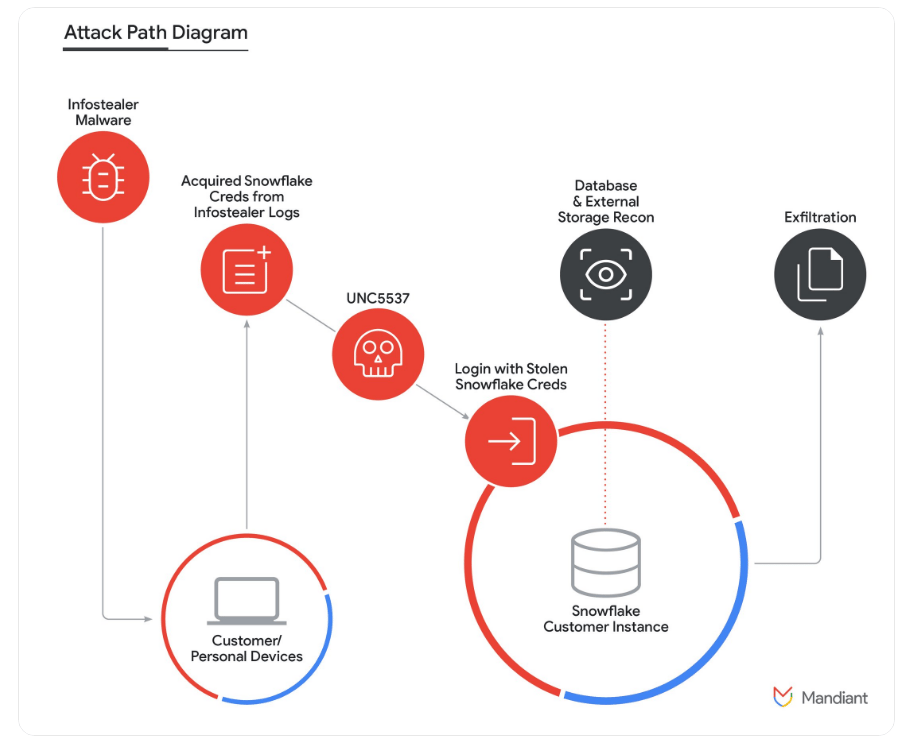
Researchers at Mandiant report that cybercriminals are demanding payments of between $300,000 and $5 million apiece from as many as ten companies breached in a campaign that targeted cloud company Snowflake’s customers.
According to Mandiant, the hacking scheme has entered a “new stage” as the gang looks to profit from the most valuable information it has stolen, including auctioning companies’ data on illegal online forums to pressure them into making payments.
Mandiant said the hacking group used stolen login details to access the Snowflake accounts of as many as 165 customers and steal data. The group has also used the stolen information to attempt to extort money from five to ten of Snowflake’s customers. It wasn’t immediately clear which of Snowflake’s clients had been affected.
Mandiant has attributed the attack to a group it calls “UNC5537,” with members based in North America and Turkey. Larsen said members of the gang have made death threats against cybersecurity experts investigating it. In one case, UNC5537 used artificial intelligence to create fake nude photos of a researcher to harass them,
Mandiant said it was investigating the “possibility” that a UNC5337 hacker collaborated with a diffuse cybercriminal group known as “Scattered Spider” on at least one intrusion within the past six months. However, the nature of such a relationship remains murky.
Mandiant found that illicit data brokers are now seeking prices above typical black-market rates for the data stolen from Snowflake customers, possibly to pressure the affected firms to pay a ransom.
Mandiant released guidance for companies on detecting UNC5537 hackers based on recent activity. (Charles Gorrivan, Margi Murphy, and Brody Ford / Bloomberg)
Related: Mandiant, Mandiant, PYMNTS, Cybernews, Silicon Angle
Meredith Whittaker, president of the nonprofit foundation behind the end-to-end encrypted (E2EE) messaging app Signal, warned that a controversial European Union legislative proposal to scan citizens' private messages to detect child sexual abuse material (CSAM) risks the future of web security.
“There is no way to implement such proposals in the context of end-to-end encrypted communications without fundamentally undermining encryption and creating a dangerous vulnerability in core infrastructure that would have global implications well beyond Europe,” she said in a blog post.
The European Commission presented the original proposal for the mass scanning of private messaging apps to counter the spread of CSAM online back in May 2022. Since then, Members of the European Parliament have united in rejecting the approach. They also suggested an alternative route last fall, which would have excluded E2EE apps from scanning. However, the European Council, the legislative body made up of representatives of Member State governments, continues to push for strongly encrypted platforms to remain in the scope of the scanning law.
The most recent Council proposal, which was put forward in May under the Belgian presidency, includes a requirement that “providers of interpersonal communications services” (aka messaging apps) install and operate what the draft text describes as “technologies for upload moderation,” according to a text published by Netzpolitik.
Article 10a, which contains the upload moderation plan, states that these technologies would be expected “to detect, prior to transmission, the dissemination of known child sexual abuse material or of new child sexual abuse material.”
Last month, Euractiv reported that the revised proposal would require users of E2EE messaging apps to consent to scanning to detect CSAM. Users who did not consent would also be prevented from using features that involve the sending of visual content or URLs, essentially downgrading their messaging experience to basic text and audio.
Whittaker’s statement skewers the Council’s plan as an attempt to use “rhetorical games” to try to rebrand client-side scanning, the controversial technology that security and privacy experts argue is incompatible with the strong encryption that supports confidential communications. (Natasha Lomas / TechCrunch)
Related: Signal, WebProNews, The Record, Cointelegraph, Blockonomi, Restore Privacy, r/privacy, Hacker News (ycombinator), Euractiv, Decipher
Oahu Transit Services in Hawaii are coping with its third day of a network outage due to a ransomware attack cybersecurity firm Falcon Feeds said is attributable to the threat actor DragonForce,
While TheBus and TheHandi-Van are still running, their websites are down. In a statement, OTS said its network went down at approximately 1 a.m. Saturday.
“Oahu Transit Services’ (OTS) online services, including the www.thebus.org website, HEA, and related real-time transit and GPS apps, are currently unavailable,” OTS said.
“OTS is currently working on restoring all systems for TheBus and TheHandi-Van and is investigating the cause. Passengers may experience delays in service today, Saturday, and we apologize for any inconvenience to our riders,” the statement continued. (Mahealani Richardson / Hawaii News Now)
Related: Honolulu Civil Beat, Honolulu Star-Advertiser
Cleveland City Hall remains closed because of the ongoing problems caused by a ransomware attack on the city’s computer systems.
The ransomware attack was uncovered more than a week ago and City Hall has been closed during that time as the city deals with the fallout. The city has not said how long the closure could drag on, but efforts have taken weeks, even months, in other US cities that have fallen victim to similar attacks.
The city says residents can still receive some services online, such as submitting applications for building and housing permits, certificates of disclosures, and lead certificates. Residents requesting birth or death certificates can also submit applications online with the Ohio Department of Health.
“We thank the public for their patience and understanding during this challenging time,” the city said. “City Hall remains committed to ensuring the security and integrity of our systems and services as we continue to recover from the cyber attacks.” (Cliff Pinckard / Cleveland.com)
Related: Cleveland19News, News5Cleveland, WKYC, Spectrum News, Signal Cleveland, The Record
Sagar Steven Singh and Nicholas Ceraolo, charged in March 2023 for hacking into a nonpublic portal maintained by a US law enforcement agency, pleaded guilty in federal court to conspiring to commit computer intrusion and aggravated identity theft.
Officials said the hackers threatened to "harm" victims' families unless they were provided with login credentials to their Instagram accounts.
The hackers called themselves "ViLe" and used doxing and other extortion tactics to extract money from their victims. Singh and Ceraolo collected victims' sensitive information, including Social Security and driver's license numbers. Then, they sought to post that data on a public site until they were paid to remove it.
Singh and Ceraolo both face a maximum of seven years in prison. (Chris Riotta / BankInfoSecurity)
Related: Justice Department
Researchers at cybercrime detection firm Netcraft found dozens of scam websites seeking to target Trump supporters and trick them out of their crypto a month after Donald Trump announced that his campaign would accept donations in cryptocurrency.
Netcraft found that in the days leading up to the announcement, scammers registered domains with common misspellings, hoping to capture supporters intending to access donaldjtrump.com. One domain registered to donalbjtrump.com was a near-perfect replica of the actual Trump campaign website. While the Trump campaign accepts donations via Coinbase, a cryptocurrency exchange, some scam websites instead appear to be using portals meant to look like Coingate, a blockchain and crypto payment processor.
A second surge of fake websites appeared immediately after Trump’s May 30 felony conviction on 34 counts of falsifying business records to pay off the porn star Stormy Daniels. In the hours after his conviction, the campaign raised more than $34 million in donations. Cybercriminals seemed to anticipate this interest, and were ready to capitalize on the donations pouring into the Trump campaign in the wake of the verdict. (Vittoria Elliott / Wired)

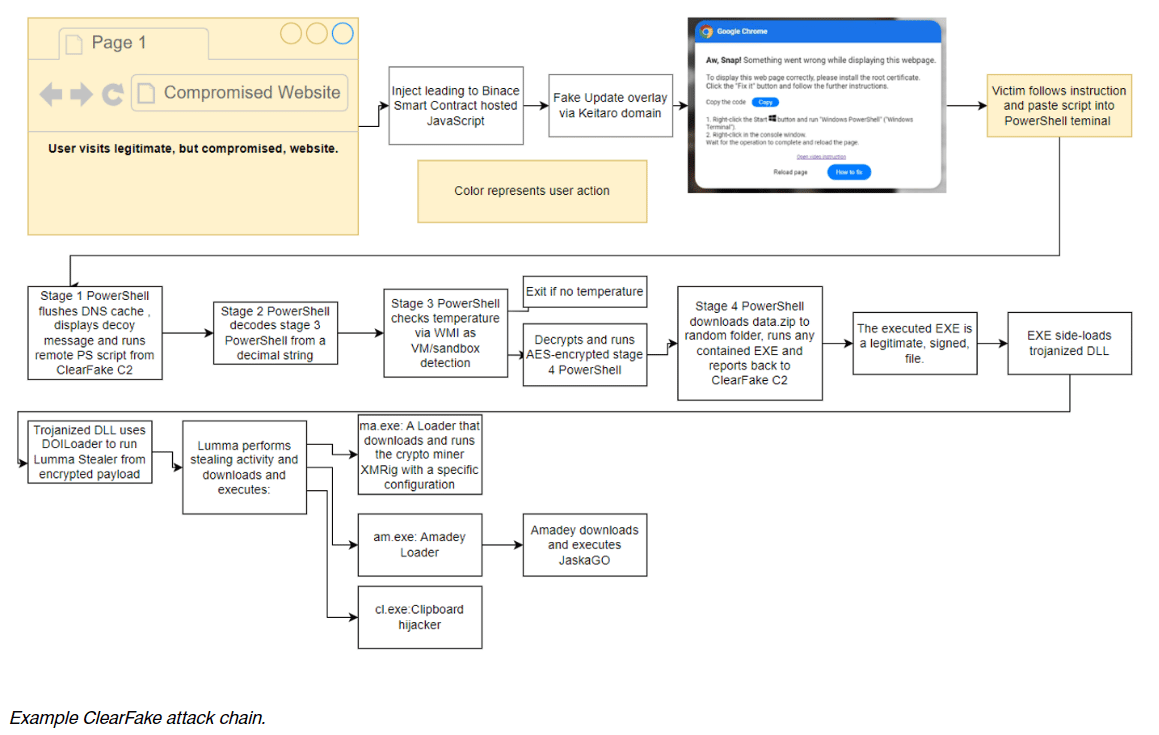
Researchers at Proofpoint report that a new malware distribution campaign uses fake Google Chrome, Word, and OneDrive errors to trick users into running malicious PowerShell "fixes" that install malware.
The new campaign was observed being used by multiple threat actors, including those behind ClearFake, a new attack cluster called ClickFix, and the TA571 threat actor, known for operating as a spam distributor that sends large volumes of email, leading to malware and ransomware infections.
Previous ClearFake attacks utilized website overlays that prompt visitors to install a fake browser update that installs malware. Threat actors also utilized JavaScript in HTML attachments and compromised websites in the new attacks. However, now, the overlays display fake Google Chrome, Microsoft Word, and OneDrive errors.
These errors prompt the visitor to click a button to copy a PowerShell "fix" into the clipboard and then paste and run it in a Run: dialog or PowerShell prompt.
Proofpoint analysts observed three attack chains that differentiate mainly on their initial stages, with only the first not being attributed with high confidence to TA571. In this first case, associated with the threat actors behind ClearFake, users visit a compromised website that loads a malicious script hosted on the blockchain via Binance's Smart Chain contracts.
This script performs some checks and displays a fake Google Chrome warning stating a problem displaying the webpage. The dialog then prompts the visitor to install a "root certificate" by copying a PowerShell script into the Windows Clipboard and running it in a Windows PowerShell (Admin) console.
When the PowerShell script is executed, it performs various steps to confirm that the device is a valid target and then downloads additional payloads.
In all cases, the threat actors exploit their targets' lack of awareness about the risks of executing PowerShell commands on their systems. They also take advantage of Windows' inability to detect and block the malicious actions initiated by the pasted code. (Bill Toulas / Bleeping Computer)
Related: Proofpoint, SC Media, Decipher, The Cyber Express, TechNadu
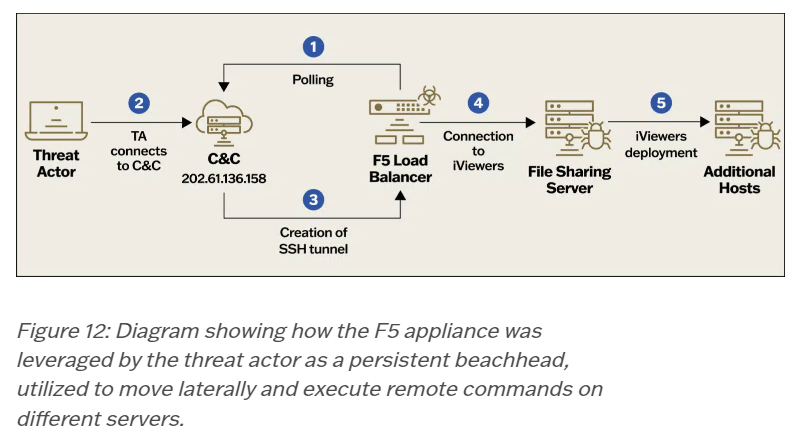
Researchers at Sygnia discovered that Velvet Ant, a group of suspected Chinese cyberespionage actors, is deploying custom malware on F5 BIG-IP appliances to gain a persistent connection to the internal network and steal data.
In one attack investigated by Sygnia, Velvet Ant established multiple footholds using various entry points across the network, including a legacy F5 BIG-IP appliance that served as an internal command and control (C2) server.
Using the compromised F5 BIG-IP devices, the threat actors could stealthily steal sensitive customer and financial information from the company for three years without being detected.
The attack started by compromising two outdated F5 BIG-IP appliances the victim organization used for firewall, WAF, load balancing, and local traffic management.
Both appliances were exposed online and ran vulnerable OS versions. Sygnia says they were both compromised by using known remote code execution flaws to install custom malware on the networking devices.
The attackers used this access to access internal file servers, where they deployed PlugX, a modular remote access Trojan (RAT) that various Chinese hackers have been using for data collection and exfiltration for over a decade.
The attackers used the compromised F5 BIG-IP appliance to retain persistence on the network, allowing them to access the internal network while blending attacker traffic with legitimate network traffic, making detection more difficult.
This method bypasses corporate firewalls and lifts outbound traffic restrictions, enabling attackers to steal customer and financial information without raising alarms for nearly three years.
Sygnia recommends several measures to detect attacks like these, including restricting outbound connections to minimize C&C communications, implementing strict controls over management ports, enhancing network segmentation, prioritizing replacing legacy systems and tightening security controls, deploying robust EDR systems with anti-tampering features and enabling security measures like Windows Credential Guard and enhancing security for edge devices through patch management, intrusion detection, and migration to cloud-based solutions. (Bill Toulas / Bleeping Computer)
Related: Sygnia, Dark Reading, Security Affairs, TechNadu
Hardware manufacturer Asus has released updates patching multiple critical vulnerabilities that allow hackers to remotely take control of a range of router models with no authentication or interaction required of end users.
The most critical vulnerability, CVE-2024-3080, is an authentication bypass flaw that allows remote attackers to log into a device without authentication. According to the Taiwan Computer Emergency Response Team / Coordination Center (TWCERT/CC), the vulnerability carries a severity rating of 9.8 out of 10.
A second vulnerability tracked as CVE-2024-3079 affects the same router models. It stems from a buffer overflow flaw and allows remote hackers who have already obtained administrative access to an affected router to execute commands.
TWCERT/CC is warning of a third vulnerability affecting various Asus router models. It’s tracked as CVE-2024-3912 and allows remote hackers to execute commands without user authentication. The vulnerability carries a severity rating of 9.8. (Dan Goodin / Ars Technica)
Related: ASUS, TWCert.org
Best Thing of the Day: Is It Real or Is It AI?
The Tow Center for Digital Journalism at Columbia Journalism School is now tracking the news outlets and tech organizations populating their platforms with AI-generated content.
Worst Thing of the Day: OK, Anyone Is a Legitimate Target
Notorious Pegasus spyware maker argued in a court filing that it is appropriate for its global clients to target any high-ranking government or military official with its technology because their jobs categorically make them “legitimate intelligence targets.”
Bonus Worst Thing of the Day: Maybe If We Sweep It Under the Rug, No One Will Notice
Healthcare giant Kaiser Permanente waited five months to report the data leak that potentially exposed the personal information of 13.4 million customers, far beyond the sixty days that HHS regulations require healthcare organizations to report breaches.
Closing Thought