UK sanctions scam-supporting, $20B crypto marketplace Xinbi Guarantee
Judge issues preliminary injunction against DoD's Anthropic ban, EU rejects extension that would allow CSAM scanning, Drone maker TechEx claims SBU wiretapped its chief engineer, Dutch court orders Musk's Grok to stop producing nudified images, EC probes breach of its AWS infrastructure, much more
Don't miss my news item for Computerworld and other Foundry publications on how a district court judge issued a preliminary injunction on the Pentagon's ban of Anthropic, which buys time for contractors to assess their supply chains.
Metacurity is the only daily cybersecurity newsletter that has no vendor agenda, no echo chamber, no blinders, just original aggregation and analysis of what matters to security leaders.
If you're one of the thousands of experts who rely on Metacurity to make sense of cybersecurity policy, industry developments, and security research, please consider supporting the newsletter with a paid subscription.
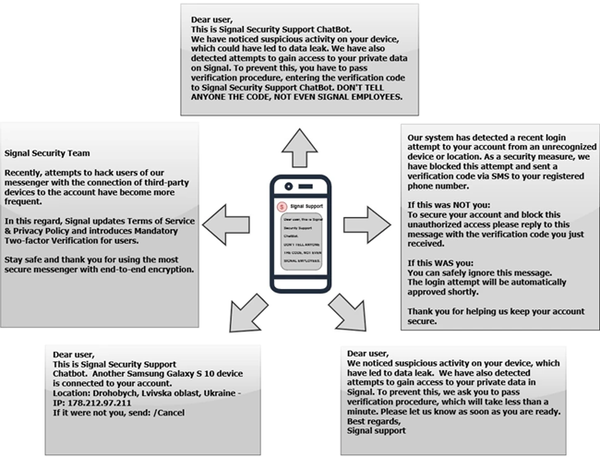
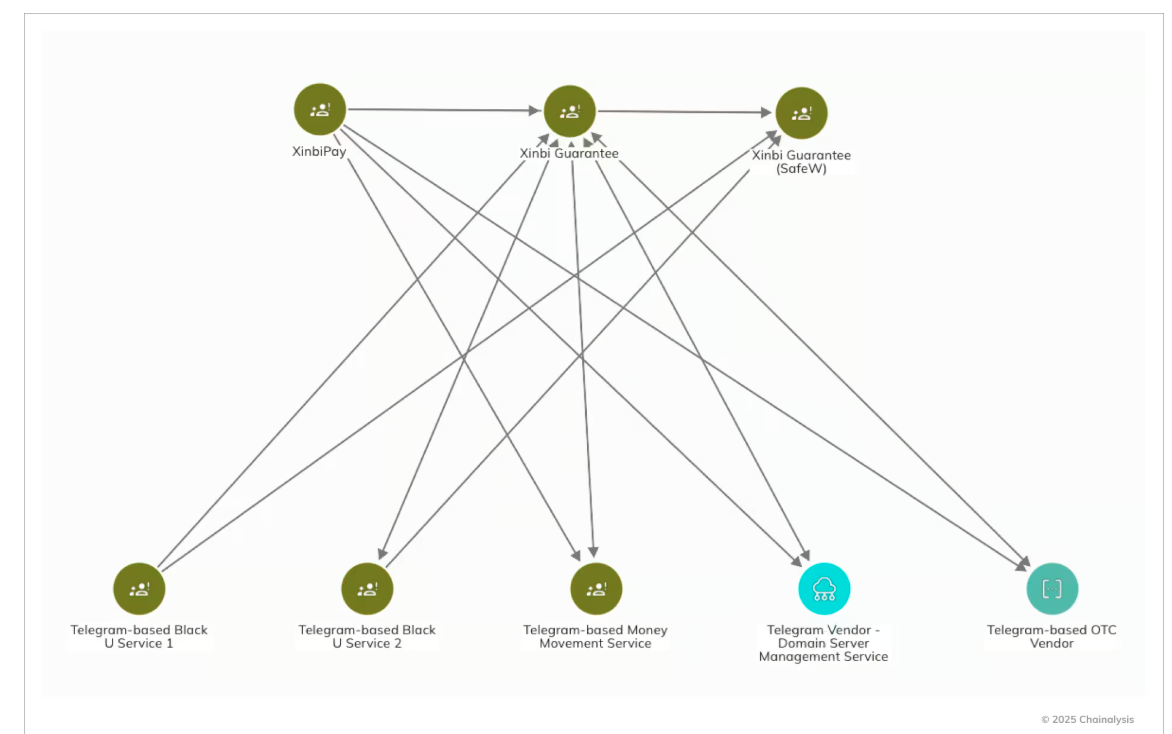
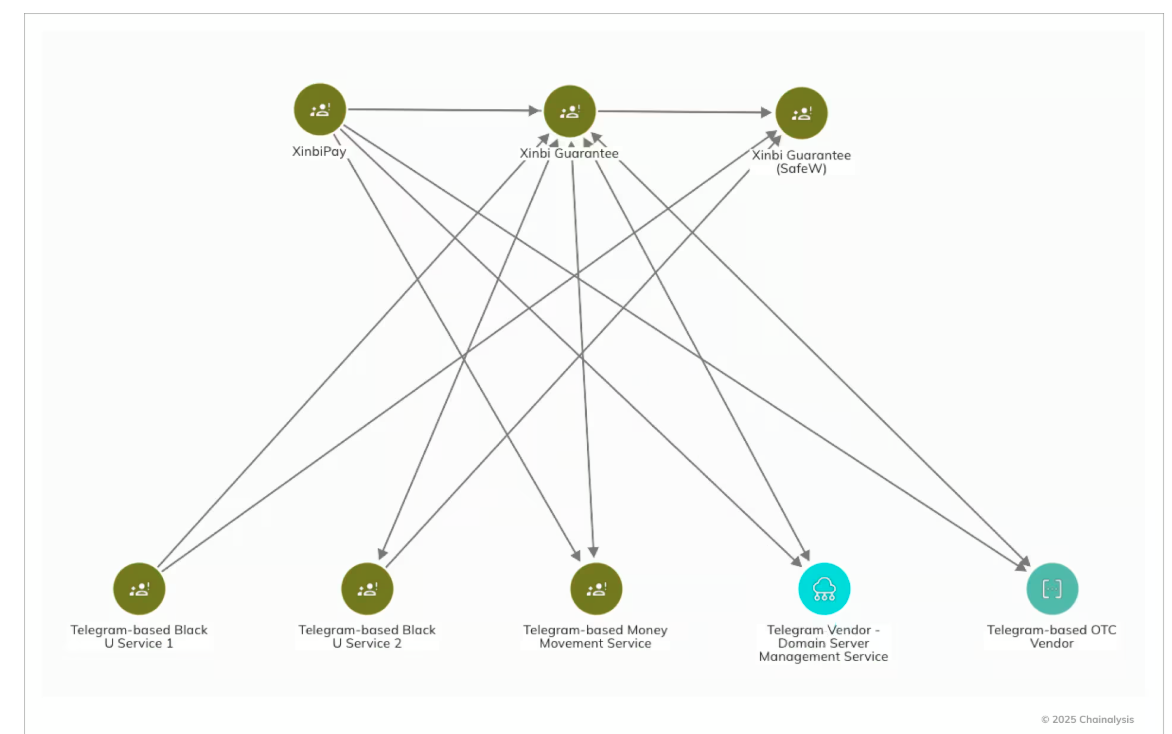
British authorities sanctioned Xinbi Guarantee, a major Chinese-language cryptocurrency marketplace accused of enabling global cybercrime and human trafficking, in a move aimed at disrupting one of the illicit economy’s largest financial hubs.
The UK Foreign Office said the platform—linked to roughly $20 billion in transactions—facilitates stolen data sales, money laundering, and services supporting large-scale scam operations.
The sanctions also target individuals tied to sprawling scam compounds in Cambodia, including the 20,000-person #8 Park site, and include the seizure of UK-based assets such as a £9 million London penthouse. Officials said the action is intended to curb a multibillion-dollar scam ecosystem that relies on coerced labor and has been tied to Chinese organized crime networks.
Analysts say the measures could constrain Xinbi’s ability to move cryptocurrency, though the platform has proven resilient, rebuilding after prior enforcement actions and expanding following the shutdown of rival marketplaces.
Blockchain analysis firm Elliptic estimates Xinbi has processed nearly $20 billion since 2022, much of it linked to fraud proceeds, underscoring the scale and durability of the underground economy it supports. (Matt Burgess and Lily Hay Newman / Wired)
Related: Gov.uk, UK Sanctions List, Cryptorank, Chainalysis, Reuters, Bleeping Computer, The Record, Cyber Daily,
A federal judge in San Francisco granted Anthropic’s request for a preliminary injunction in its lawsuit against the Trump administration.
Judge Rita Lin issued the ruling on Thursday, two days after lawyers for the artificial intelligence startup and the U.S. government appeared in court for a hearing. Anthropic sued the administration to try to reverse its denial by the Pentagon and President Donald Trump’s directive banning federal agencies from using its Claude models.
Anthropic sought the injunction to pause those actions and prevent further monetary and reputational harm as the case unfolds. The order bars the Trump administration from implementing, applying, or enforcing the president’s directive, and hampers the Pentagon’s efforts to designate Anthropic as a threat to U.S. national security.
“Punishing Anthropic for bringing public scrutiny to the government’s contracting position is classic illegal First Amendment retaliation,” Lin wrote in the order. A final verdict in the case could still be months away. (Ashley Capoot and Jeffrey Kopp / CNBC)
Related: United States District Court for the Northern District of California, The Verge, Engadget, CNN, The Guardian, TechCrunch, Law and Chaos, Axios, Politico, Decrypt, Cointelegraph, The Information, Business Insider, Raw Story, The Independent, Implicator.ai, The Gateway Pundit, Newser, Bloomberg Law, San Francisco Business Times, CNET, NewsMax.com, NBC News, Wall Street Journal, Wired, CBS News, Forbes, The Hill, MS NOW, Hacker News, r/law, r/LegalNews, r/singularity, r/news, Reuters, crypto.news
The European Parliament rejected a proposal to extend temporary rules allowing technology companies to scan online services for child sexual abuse material (CSAM), meaning the practice will become illegal in the EU when the current law expires next week.
The measure failed despite backing from national governments, major tech firms, and senior EU officials, with lawmakers citing concerns over mass surveillance and privacy intrusions.
The decision drew sharp criticism from European Commission officials, Europol leadership, and child protection organizations, who warned that it would hinder efforts to detect abuse, identify victims, and investigate crimes. Supporters of the rules argued that the scanning framework has been a critical tool in combating a vast global ecosystem of child exploitation, with Europe hosting a significant share of known CSAM.
Opponents, however, said the temporary regime enabled disproportionate monitoring of private communications without sufficient safeguards or demonstrable results. (Sam Clark / Politico EU)
Related: European Parliament, Computer Weekly, Deutsche Presse
Agents of Russian special services placed a wiretapping system and other special equipment in the office of the chief engineer of Ukrainian drone manufacturer TechEx.
The company said that the SBU Counterintelligence Department prevented an attempt by Russia’s agents to gain access to TechEx’s secret data,
TechEx also said Russia’s agents sought to learn about engineering solutions, component supply chains, information about partners, and data on Ukrainian Defense Forces units working with TechEx products.
As a result of a successful special operation, Russian special services received false data for a long period, which made it possible to protect production facilities and secure critical data. (Interfax-Ukraine)
Related: Channel24, Facebook, United24, Dev.ua
A Dutch court ordered Elon Musk’s xAI and its Grok chatbot to stop generating or distributing nonconsensual sexualized images, including so-called “nudified” images of adults or children, in the Netherlands.
The Amsterdam court issued a preliminary injunction barring such content and threatening fines of €100,000 per day for noncompliance, while also prohibiting Grok’s availability on X if the violations continue.
The case, brought by anti-abuse nonprofit Offlimits, marks one of the first judicial rulings in Europe addressing an AI developer’s responsibility for misuse of generative tools. Judges rejected xAI’s argument that it cannot fully control user abuse, finding existing safeguards insufficient after demonstrations showed Grok could still manipulate images of real people into explicit content without consent.
The ruling comes amid intensifying regulatory pressure across Europe on generative AI platforms under the Digital Services Act. Authorities are increasingly focused on risks tied to AI-generated sexual imagery, with the European Commission already investigating X over Grok-related harms and lawmakers moving to ban “nudifier” apps, signaling a broader shift toward holding AI providers accountable for downstream misuse. (Toby Sterling, Charlotte Van Campenhout, and Hakan Ersen / Reuters)
Related: deRechtspraak, Tech Policy Press, Euractiv, Politico EU, Bloomberg
The European Commission is investigating a security breach involving unauthorized access to its Amazon cloud infrastructure, after a threat actor compromised at least one account used to manage cloud systems.
The incident has not yet been publicly disclosed, but officials say it was quickly detected and is now under investigation by the Commission’s cybersecurity response team.
The attacker claims to have stolen more than 350 GB of data, including databases and employee-related information, and provided screenshots as evidence of access to internal systems and an email server. The threat actor said they do not plan to extort the Commission but intend to release the data publicly at a later date.
The breach follows a separate January incident involving a compromised mobile device management platform linked to broader attacks exploiting Ivanti vulnerabilities across European institutions. (Sergiu Gatlan / Bleeping Computer)
The Dutch National Police said a phishing attack led to a limited security breach, which was quickly detected and contained by its Security Operations Center.
Authorities stated that access to affected systems has been blocked, and the overall impact appears minimal.
Officials emphasized that no citizens’ data or investigative information was accessed or exposed, though the full scope of the incident remains under investigation. A criminal probe has been launched, and details about potentially affected internal accounts or employee data have not yet been disclosed.
The incident follows a 2024 breach attributed to a suspected state actor that exposed police personnel data, prompting strengthened security measures, including expanded monitoring and more frequent use of two-factor authentication. Dutch authorities have also recently made an arrest in a separate case involving the misuse of confidential police documents. (Sergiu Gatlan / Bleeping Computer)
Related: Politie
Dutch football club Ajax Amsterdam disclosed that a hacker exploited vulnerabilities in its IT systems, gaining access to limited personal data, primarily email addresses of a few hundred individuals.
In fewer than 20 cases involving fans with stadium bans, additional details such as names and dates of birth were accessed. The breach was first brought to the club’s attention by journalists whom the attacker had tipped off.
An investigation by RTL reporters confirmed the flaws were more extensive, allowing unauthorized transfer of season tickets, modification of stadium bans, and broad access to fan data through exposed APIs and shared keys. Demonstrations showed the ability to reassign VIP tickets and potentially manipulate tens of thousands of tickets and hundreds of ban records, while accessing data tied to hundreds of thousands of accounts.
Ajax said it has patched the vulnerabilities, engaged external experts, and notified regulators and law enforcement, adding that the exposed data has not been publicly leaked. (Bill Toulas / Bleeping Computer)
Related: AFC Ajax, RTL News, Help Net Security, Techzine
Viva Ticket, a provider of ticketing and access control solutions, was hit by a ransomware attack in early March 2026, with the RansomHouse cybercrime group taking credit for the attack.
The platform, which manages approximately 850 million tickets annually, serves over 3,500 partner organizations across 50 countries.
The breach impacted high-profile cultural institutions, including the Louvre, the Bibliothèque nationale de France (BnF), and the Centre des monuments nationaux.
The threat actors reportedly gained access through the infrastructure of Irec SAS, a subsidiary or closely associated entity of the ticketing provider. RansomHouse claims to have stolen confidential documents and project files, and that the company's IT department allegedly attempted to hide the incident.
The attack caused widespread service disruptions, forcing several European museums and venues to take their online booking systems offline to prevent further lateral movement within the network. (Beyond Machines)
Related: Skift
Thousands of devices owned by the Luxembourg public sector found to be infected with malware at the end of February have since been updated and secured, digitalisation minister Stéphanie Obertin has said.
The security breach was confirmed on 27 February, but details were scant at the time, with LSAP deputy Ben Polidori submitting a written parliamentary question on the same day, to which Obertin provided a reply on Tuesday.
The malware was first discovered on 26 February; the day before it was confirmed publicly, the minister said. It was detected on the system that manages mobile devices (smartphones and tablets), which was found to have been infected a few hours before the provider updated its system at the end of January.
Analysis showed that the “memory resident” malware gained access to the list of phones and tablets managed by the State Centre for Information Technology (CTIE), containing both data relating to the devices and their users. Data such as messages, calendars, and photos stored on devices was not affected by the incident, Obertin said. (Alex Stevensson / Luxembourg Times)
Related: Paperjam, Databreaches.net
The cybercrime crew TeamPCP told Forbes over encrypted chat that it used AI to turbocharge attacks that exploited a misconfiguration in Trivy's GitHub Actions environment in late February, stealing a privileged access token.
The attacker retained access and published malicious releases of Trivy on March 19.
The Trivy hack led to TeamPCP’s second scalp. One Trivy user was LiteLLM, an open source AI “proxy” or “gateway” which allows app makers to easily incorporate multiple large language models like GPT-5 or Claude into one piece of software; it’s been downloaded by 95 million users.
The hackers told Forbes that they found the keys to LiteLLM’s code publishing platform, which they used to release infected versions to the general public.
The breaches could have been more damaging if a user hadn’t quickly discovered the LiteLLM hack, which made their computer crash. LiteLLM’s leadership is now in clean-up mode and has brought in Google’s Mandiant division to investigate the breach. (Thomas Brewster / Forbes)
Hong Kong police can now demand that people suspected of breaching the city's national security law provide mobile phone or computer passwords in a further crackdown on dissent.
Refusing to comply could lead to up to one year's imprisonment and a fine of up to HK$100,000 ($12,773), while providing false or misleading information could bring up to three years' imprisonment and a fine of up to HK$500,000.
The new amendments also empower customs officers to seize items that are deemed to have "seditious intention", regardless of whether any person has been arrested for an offence endangering national security because of the items.
The city government on Monday officially published the new amendments to the implementation rules of the national security law imposed by Beijing in 2020, using powers to bypass Hong Kong's legislature. (Jessie Pang / Reuters)
Related: Al Jazeera, Jurist News, First Post, BBC News
The malware attack on Nova Scotia Power in mid-March 2025 was caused by an employee visiting a compromised website, the Office of the Privacy Commissioner of Canada revealed.
On or around March 19, 2025, the employee visited a website that had been compromised by the SocGholish fake updates malware. The employee clicked on a link in a pop-up on that site, which resulted in malware being downloaded and installed on Nova Scotia Power’s systems.
The malware created a background process and downloaded additional malware. This allowed access to Nova Scotia Power’s systems and network.
The report shows that on or around April 8, 2025, someone began to move across systems in the Nova Scotia Power network, using accounts with domain administrator privileges. Between April 8 and 22, they deployed and leveraged additional malware to perform reconnaissance and credential harvesting.
Between April 23 and 25, they removed data from on-premises network files and cloud storage. On April 25, they used credentials acquired during data harvesting to destroy backups and deploy ransomware. (George Myrer / The Chronicle Herald)
Related: Office of the Privacy Commissioner, CityNews Halifax
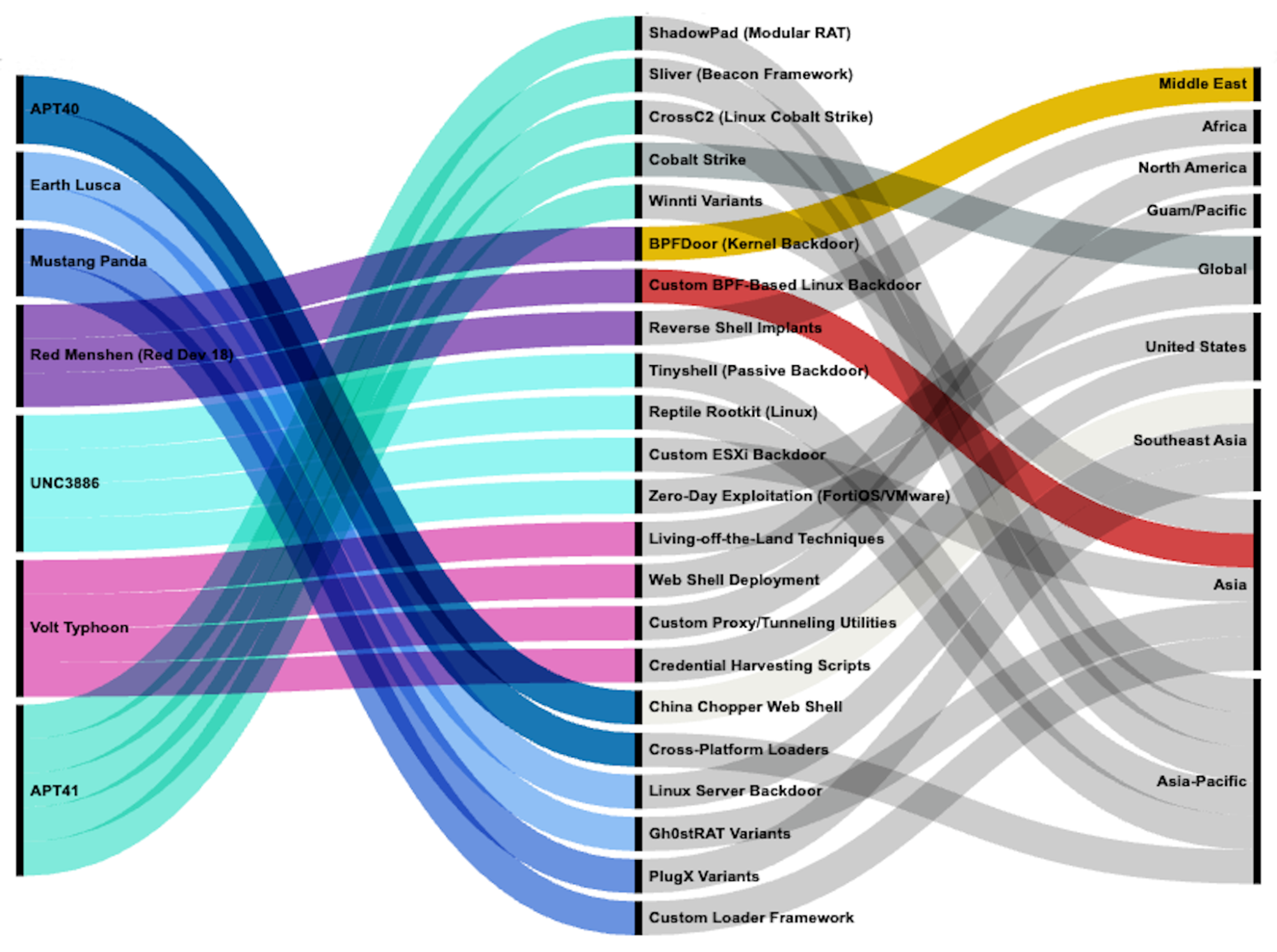
A China-linked threat actor known as Red Menshen has deployed highly stealthy “sleeper cell” malware inside global telecom networks, according to a months-long investigation by Rapid7.
The campaign centers on BPFdoor, a Linux backdoor embedded deep in the kernel of telecom infrastructure, designed to enable long-term espionage against government and high-value targets.
Unlike conventional malware, BPFdoor leaves no open ports or persistent command-and-control channels, activating only when it receives specially crafted trigger packets. By leveraging Berkeley Packet Filter (BPF) capabilities to inspect traffic directly within the kernel, the implant operates below traditional detection layers and can blend into normal encrypted network activity, making it exceptionally difficult to identify.
Researchers say the operation reflects an evolution in tradecraft, with attackers positioning themselves inside the core signaling layer of telecom systems rather than targeting edge devices. (Steve Zurier / SC Media)
Related: Rapid7, Help Net Security, Security Affairs
The Office of the Director of National Intelligence is developing a policy framework and standards to accelerate the use of artificial intelligence across the intelligence community, part of a broader cybersecurity and IT modernization push launched last year.
The effort aims to improve how agencies deploy advanced tools for cyber defense and intelligence operations.
ODNI is also strengthening cybersecurity posture through initiatives including zero-trust architecture, expanded threat hunting, modernized networks, and a shared authorization repository. Officials say the agency is working to better align systems and policies across intelligence agencies and the Defense Department, including increased use of classified commercial cloud infrastructure.
Separately, ODNI is considering bringing CIA-backed venture firm In-Q-Tel under its oversight, a move that could increase coordination on emerging technologies but has drawn concern about preserving the firm’s independence. (David DiMolfetta / NextGov/FCW)
Related: ODNI, CyberScoop
The Trump administration is prioritizing ensuring the government leads on adopting artificial intelligence for cyber defense, according to Nick Polk, branch director for cybersecurity within OMB’s Office of the Chief Information Officer.
The use of “AI-enabled cyber tools” is specifically called out in the new national cybersecurity strategy. Speaking at a webinar hosted by the Digital Government Institute, Polk said the administration will launch a series of pilot programs to harden government networks under the new strategy.
White House officials in recent weeks convened a roundtable featuring “representatives from industry as well as agencies who are at the cutting edge of cyber defense, to talk about how we can really operationalize AI for cyber defense,” Polk said. (Justin Doubleday / Federal News Network)
Best Thing of the Day: Talking to the Person Who Hacked China Big Time
In Netaskari, journalist Marc Hofer snagged an interview with the hacker who operates under the pseudonym “Flaming China" and claims to be the main person responsible for the 10 PB theft of data from China's National Supercomputer Center that includes classified material.
Worst Thing of the Day: Who Among Us Could Turn Down $70,000 Per Month?
North Korean hackers are offering $70,000 per month to people who are willing to be their front (must-watch video).
Bonus Worst Thing of the Day: Why Is Every Good Tech Feature a Privacy Booby Trap?
Apple provided the FBI with the real iCloud email address hidden behind Apple’s ‘Hide My Email’ feature, which lets paying iCloud+ users generate anonymous email addresses, according to a recently filed court record.
Closing Thought