US Cracks Down on Four Alleged Iranian Hackers With Sanctions, $10 Million Reward

TikTok ban passes but is no slam dunk, Hackers release part of El Salvador's Bitcoin code, State Department imposes visa restrictions on 13 people linked to spyware, DPRK hackers are exploiting antivirus update mechanism, Chinese and Russian hackers use edge devices in espionage attacks, Google delays end of third-party cookies again, New keyboard app flaws emerge that enable surveillance of Chinese users, much more
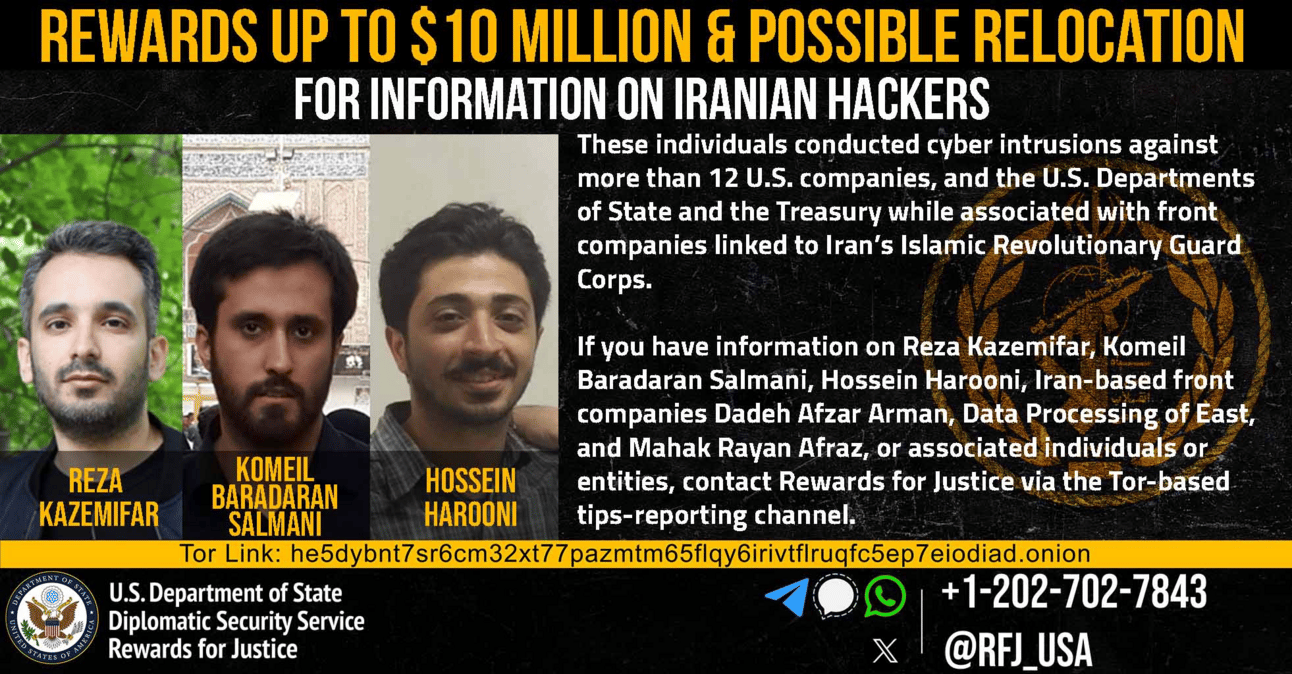
The US Department of Justice indicted and the US Treasury’s Office of Foreign Assets Control (OFAC) sanctioned four Iranian nationals, accusing them of participating in hacking operations that targeted the US Treasury and State departments, defense contractors, and two New York-based companies on behalf of the Iranian Islamic Revolutionary Guard Corps (IRGC).
In addition, the State Department is offering a reward of up to $10 million and possible relocation for any information on three of the men or the companies with whom they’re associated.
The accused defendants are Hossein Harooni, Reza Kazemifar, Komeil Baradaran Salmani, and Alireza Shafie Nasab. The men have various connections to a pair of IRGC front companies, which were used to carry out various aspects of the attacks, according to the Treasury Department: Mehrsam Andisheh Saz Nik (MASN), previously known as Mahak Rayan Afzar and Dadeh Afzar Arman (DAA)
All four were indicted and charged with conspiracy to commit computer fraud, conspiracy to commit wire fraud, and wire fraud. They each face up to five years in prison for the computer fraud conspiracy charge and up to 20 years in prison for each count of wire fraud and conspiracy to commit wire fraud.
Harooni was also charged with knowingly damaging a protected computer, which could result in an additional 10-year prison sentence. The Department of Justice said Harooni, Salamani, and Nasab were also charged with aggravated identity theft, which carries a mandatory consecutive term of two years in prison.
An indictment against Nasab was previously unsealed in February for the same charges, and the State Department had already offered a $10 million reward for information leading to his location.
The men are accused of participating in “a coordinated multi-year campaign to conduct and attempt to conduct computer intrusions” between 2016 through at least April 2021, the Department of Justice said in a statement. The group primarily targeted cleared defense contractors and companies authorized to access, receive, and store classified information supporting the US Department of Defense.
According to the indictment, the group also targeted an unnamed New York-based accounting firm and a New York-based hospitality company. (AJ Vicens / Cyberscoop)
Related: Treasury.gov, Justice.gov, Washington Examiner, The Record, CNN, Security Week, Bleeping Computer, Reuters, The National, Cybernews, Security Affairs, Cyber Daily, The Cyber Express
In a historic move, Congress passed legislation, which President Biden says he will sign, to ban or force the sale of Chinese-owned video-sharing platform TikTok after years of failed attempts to tackle the app’s alleged national security risks.
Once signed, the provision will give TikTok’s parent company, ByteDance, roughly nine months to sell the wildly popular app or face a national ban, a deadline the president could extend by 90 days.
Lawmakers pushing for the restriction have cited concerns that the company’s ownership structure could allow the Chinese government to gain access to Americans’ data, claims that TikTok disputes.
TikTok is expected to challenge the measure, setting up a high-stakes and potentially lengthy legal battle that will test the company’s argument that any such law would violate the free speech rights of millions.
Interviews with legal scholars suggest that the government will have difficulty proving that its effort to ban TikTok is constitutional on First Amendment grounds. But First Amendment cases are often unpredictable, they say, and it’s possible that the government’s appeals to national security could ultimately lead the Supreme Court to uphold the law.
Scholars said the government will likely struggle to make a convincing argument that banning TikTok is necessary to protect Americans’ data privacy. The data privacy argument may strike courts as particularly weak given the dramatic restriction on speech that will come with banning an app used by 170 million Americans.
According to experts, the strongest argument in the government’s toolkit is that banning TikTok is necessary to protect national security.
TikTok plans to fight the law vigorously, and sources say TikTok owner ByteDance sees a TikTok divestiture as a last resort. ByteDance expects it can get a restraining order on the legislation and then wage a legal battle that could last more than a year. (Cristiano Lima-Strong / Washington Post, Casey Newton / Platformer and Alex Barinka / Bloomberg)
Related: The White House, Australian Financial Review, Android Authority, Silicon Republic, CNBC, CNN, Semafor, Associated Press, Reuters, NBC News, ITV News, Sky News, The Seattle Times, NME, BBC, Bloomberg, Mashable, Hypebeast, Newsweek, GSMArena.com, Washington Post, Daily Sabah, GB News, Tech in Asia, Florida Politics, The Hindu, The Register, The Guardian, Forbes, CBC News, Politico, Social Media Today, Oneindia, Wired, The Star, Hindustan Times, The Information, Wall Street Journal, TheJournal.ie, Benzinga, Mothership.SG, New Jersey Globe, Gizmodo, New York Times, Yahoo News, Business Insider, The Daily Beast, Rolling Stone, Neowin, CBS News, Proactiveinvestors UK, Mastodon, The Economist, Engadget, Australia & World, Bloomberg, Al Jazeera, TechCrunch, The Hill, Digiday, Fortune, Variety, The Verge, Financial Times
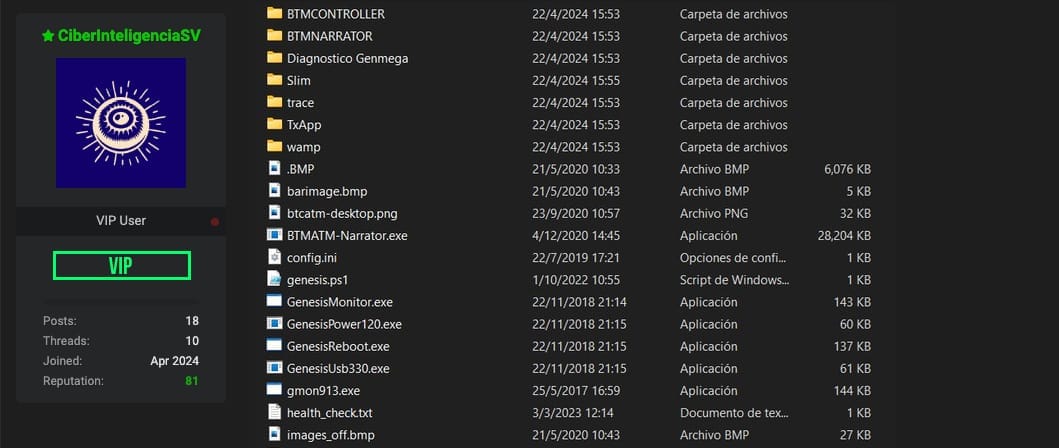
The hacker group known as CiberInteligenciaSV breached El Salvador’s state-operated Bitcoin and released part of the source code on the black hat hacking crime forum BreachForums.
“This time I bring you the code that is inside the Bitcoin Chivo Wallet ATMs in El Salvador, remember that it is a government wallet, and as you know, we do not sell, we publish everything for free for you,” the hacker group wrote.
The move follows a series of Chivo hack-related events, including the public exposure of the personal data of 5.1 million Salvadorans, or almost the entire adult population of the country.
The group signaled its intention in an earlier post on Telegram. “Tonight we will publish part of the source code and VPN access that belongs to Chivo Wallet, for free as always, unless one of you nosy government people wants to talk,” CiberInteligenciaSV’s Telegram post reads.
CiberInteligenciaSV also published the file Codigo.rar, which includes a compilation of code and VPN credentials from the Chivo Wallet ATM network.
El Salvador authorities have not released any official statement related to the hack. (Helen Partz / Cointelegraph)
Related: Unchained, Cryptonews, crypto.news, The Crypto Times, The Block, Protos, CoinGape
As announced in February, the Department of State has started imposing visa restrictions on mercenary spyware makers and peddlers, prohibiting their entry into the United States.
The crackdown, part of a broader US government crackdown on spyware, has begun with 13 individuals and their close families (i.e., spouses and children) linked to commercial spyware operations.
Under Section 212 (a)(3)(C) of the Immigration and Nationality Act, these visa restrictions allow the Secretary of State to exclude visa applications whose entry would have adverse foreign policy consequences for the US, effectively banning those linked to commercial spyware from entering the country.
"As part of the United States' efforts to counter the ongoing proliferation and misuse of commercial spyware as documented today in the Department of State's Country Reports on Human Rights Practices, the Department is taking steps to impose visa restrictions on 13 individuals who have been involved in the development and sale of commercial spyware or who are immediate family members of those involved," said State Department spokesperson Matthew Miller. (Sergiu Gatlan / Bleeping Computer)
Related: State Department, Bitdefender, Infosecurity Magazine, Dark Reading, Security Affairs
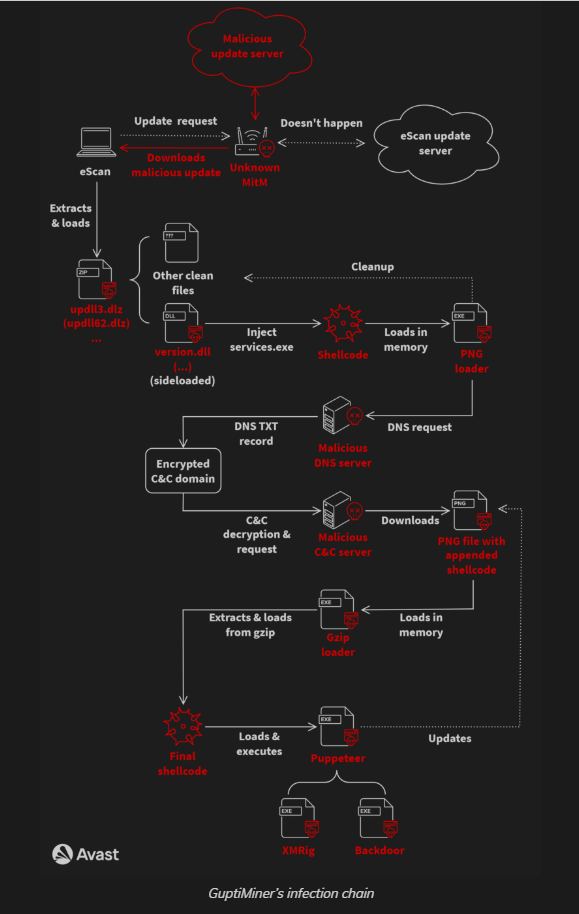
Researchers at Avast report that North Korean hackers have been exploiting the eScan antivirus updating mechanism to plant backdoors on big corporate networks and deliver cryptocurrency miners through GuptiMiner malware.
They describe GuptiMiner as "a highly sophisticated threat" that can perform DNS requests to the attacker's DNS servers, extract payloads from images, sign its payloads, and perform DLL sideloading.
Avast says that the threat actor behind GuptiMiner had an adversary-in-the-middle (AitM) position to hijack the normal virus definition update package and replace it with a malicious one named updll62.dlz.
Avast researchers say that GuptiMiner may be linked to the North Korean APT group Kimsuki based on similarities between its information-stealing function and the Kimsuky keylogger.
The researchers also discovered that some parts of the GuptiMiner operation suggest a possible connection to Kimsuki. A commonality is using the domain mygamesonline[.]org, which is ordinarily seen in Kimsuky operations.
Avast researchers disclosed the exploited vulnerability to eScan, and the antivirus vendor confirmed that the issue had been fixed.
eScan also said that the last similar report they received was in 2019. In 2020, the vendor implemented a more robust checking mechanism to ensure that non-signed binaries were rejected.
In the most recent implementation, eScan's update downloads occur over HTTPS to ensure encrypted communication for clients interacting with the vendor's cloud-facing servers.
However, Avast reports that it continues to observe new infections by GuptiMiner, which could indicate outdated eScan clients. A list of IOCs is available on Avast’s GitHub. (Bill Toulas / Bleeping Computer)
Related: Avast, Ars Technica, Cyber Security News, GitHub
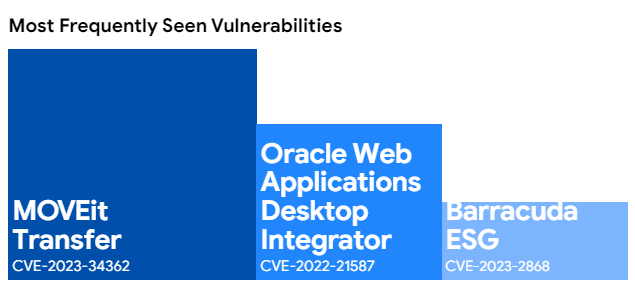
In its annual report on cyber investigations, Mandiant says Chinese and Russian hackers have turned their focus to edge devices such as VPN appliances, firewalls, routers, and Internet of Things (IoT) tools amid a startling increase in espionage attacks.
Charles Carmakal, chief technology officer at Mandiant, said there has been a significant shift in the tactics used by espionage hackers based in China and Russia. For years, incident responders saw the same playbook: employees would be targeted with malicious phishing emails containing malware that would give hackers a foothold into the system.
But last year, Carmakal said the most common way into companies was by finding a zero-day vulnerability in frequently deployed devices.
In its report, Mandiant says it saw a more than 50% growth in zero-day usage compared to 2022, both by espionage groups and financially motivated attackers.
In incidents handled by Mandiant, the company saw 38% of intrusions start with an exploit, a 6% increase from the year before, whereas 17% of intrusions started with phishing emails, a 22% drop. The third most common way hackers got into systems was through previous compromises repurposed for new attacks.
Mandiant researchers noted that zero-day vulnerabilities are no longer simply the domain of state-backed espionage hackers. An increasing number of criminal groups are also exploiting zero-days, the most prominent of which was seen in 2023 through the MOVEit file transfer attacks.
Mandiant investigators found that the Russia-based Clop ransomware gang — began scanning the internet for vulnerable instances of MOVEit 12 days before they started stealing data from more than 2,500 organizations worldwide. (Jonathan Greig / The Record)
Related: Mandiant, CRN, Dark Reading, GovInfoSecurity, Security Week, Silicon Angle
Google is delaying the end of third-party cookies in its Chrome browser again.
“We recognize that there are ongoing challenges related to reconciling divergent feedback from the industry, regulators, and developers, and will continue to engage closely with the entire ecosystem,” according to a statement Google posted on its website for the Privacy Sandbox. “It’s also critical that the CMA has sufficient time to review all evidence, including results from industry tests, which the CMA has asked market participants to provide by the end of June. Given these significant considerations, we will not complete third-party cookie deprecation during the second half of Q4.”
Google did not outline a more specific timetable beyond hoping for 2025.
This is the third time Google has pushed back its original deadline set in January 2020. (Seb Joseph / Digiday)
Related: The Privacy Sandbox, Android Authority, The Hindu, The Verge, Ad Age, AdNews News, AdExchanger, The Information, Thurrott, Business Standard, Social Media Today, Bloomberg, The Drum, Gigazine
Sponsor

Researchers at CitizenLab discovered critical vulnerabilities in eight of nine Chinese mobile vendors’ keyboard apps that malicious hackers could exploit to completely reveal the contents of users’ keystrokes in transit.
Most of the vulnerable apps can be exploited by an entirely passive network eavesdropper.
These vulnerabilities were in pinyin input method keyboard apps used chiefly by mainland Chinese users. The researchers analyzed the security of cloud-based pinyin keyboard apps from nine vendors: Baidu, Honor, Huawei, iFlytek, OPPO, Samsung, Tencent, Vivo, and Xiaomi.
Combining the vulnerabilities discovered in this analysis and a previous report analyzing Sogou’s keyboard apps, CitizenLab estimates that up to one billion users are affected by these vulnerabilities.
Given the scope of these vulnerabilities, the sensitivity of what users type on their devices, the ease with which these vulnerabilities may have been discovered, and the fact that the Five Eyes have previously exploited similar vulnerabilities in Chinese apps for surveillance, it is possible that such users’ keystrokes may also have been under mass surveillance.
CitizenLab reported these vulnerabilities to all nine vendors. Most vendors responded, took the issue seriously, and fixed the reported vulnerabilities, although some keyboard apps remain vulnerable. (Jeffrey Knockel, Mona Wang, and Zoë Reichert / CitizenLab)
Related: Citizen Lab, Cybernews, TechRadar
New York Times reporter Kashmir Hill discovered from her own experience that General Motors has been selling her and her husband's driving data to insurance companies even though they aren’t enrolled in Smart Driver, a gamified program that offers feedback and digital badges for good driving.
Their MyChevrolet app confirmed that their car was not enrolled in Smart Driver but GM.com, which said their car was enrolled in “OnStar Smart Driver+.”
GM says this discrepancy between the app and the website resulted from “a bug” that affected a “small population” of customers. That group got the worst possible version of Smart Driver: She couldn’t get insights into their driving, but insurance companies could.
In 10 federal lawsuits filed in the last month, drivers from across the country say they did not knowingly sign up for Smart Driver but recently learned that GM had provided their driving data to LexisNexis. According to one of the complaints, a Florida owner of a 2019 Cadillac CTS-V who drove it around a racetrack for events saw his insurance premium nearly double, an increase of more than $5,000 per year. (Kashmir Hill / New York Times)
Related: The Register
UK mobile phone maker Nothing, founded by Carl Pei, the co-founder of the Chinese smartphone maker OnePlus, experienced a data breach on its community forums that only came to light recently and affected thousands of users.
Most of the data included in the dump was already publicly available, like Nothing Community usernames. However, user emails (which are not public-facing on Nothing Community) were also leaked.
Some of the data that cropped up in an online database were first blurred and then eventually taken down to prevent bad actors from exploiting the data exposed in the database.
Nothing confirmed the data breach, stating that the vulnerability dated back to 2022.
"In December 2022, Nothing discovered a vulnerability, which impacted email addresses belonging to community members at the time," the company said. "No names, personal addresses, passwords, or payment information were compromised. Upon this discovery nearly a year and half ago, Nothing took immediate action to remedy the situation and bolster its security features." (Brady Snyder / Android Central)
Related: Tech Times, Android Authority, Mashable India, Hindustan Times, Business Today, NewsBytes, Mint, News18
A March 7 cyber attack on the Leicester City Council in the UK has left a number of streetlights stuck on all day.
A city council spokesperson said: “We are aware of a number of streetlights that are staying on during the day. This is due to a technical issue connected to the recent cyber attack when we were forced to shut down our IT systems. It means we are currently not able to remotely identify faults in the street lighting system.
"The default mode for faults is that the lights stay on to ensure that roads are not left completely unlit and become a safety concern. “There are a number of steps required to resolve the problem, and we are working through these as quickly as we can.” (Tom Mack / LeicesterLive)
Related: BBC News, SC Media, Security Affairs, The Register
Microsoft has released hotfix updates to address multiple known issues impacting Exchange servers after installing the March 2024 security updates.
Although the April 2024 HU is optional, it also supports ECC certificates and Hybrid Modern Authentication (HMA) for OWA/ECP.
If you have installed the March 2024 SU, have not experienced any known issues fixed in the optional update, and do not need the new features, you can wait for the next Exchange Server SU, which will include these hotfixes. (Sergiu Gatlan / Bleeping Computer)
Related: Microsoft
Data security vendor Veeam has acquired cyber incident extortion response company Coveware.
A new company, Coveware by Veeam, will operate independently initially, but the company will integrate elements over time. (Zeus Kerravala / Silicon Angle)
Related: Techzine, Channel Futures, CRN
Best Thing of the Day: Let There Be Light
Nina Jankowicz, who briefly led an agency at the Department of Homeland Security created to fight disinformation that right-wing legislators attacked, has launched a new nonprofit organization, the American Sunlight Project, to fight a coordinated campaign by conservatives and others to undermine researchers.
Worst Thing of the Day: Let’s Experiment on the Disadvantaged
Cybersecurity company Performanta reports that cyber attackers are experimenting with their latest ransomware on businesses in Africa, Asia, and South America before targeting richer countries with more sophisticated security methods.
Closing Thought





