US dismantles major botnet networks, but Mirai’s evolution keeps the threat alive
Cops take down 373k scam darknet sites posting as CSAM sites, FBI seizes two Handala sites, Man convicted on extortion counts after sensitive contractor data theft, Man pleads guilty to AI-assisted streaming fraud, Admin unveils AI legislative framework, much more


If you rely on Metacurity to make sense of cybersecurity policy, industry developments, and security research, please consider supporting the newsletter with a paid subscription.
Metacurity is a daily infosec intelligence layer written independently of vendor marketing, PR-driven threat intelligence, and the cyber media echo chamber. Paid subscriptions make it possible to keep producing clear, straightforward analysis every day. Please consider upgrading your subscription. Thank you!
US law enforcement dismantled four of the world’s largest botnets—Aisuru, Kimwolf, JackSkid, and Mossad—in a coordinated operation led by the Justice Department and the Defense Criminal Investigative Service.
These networks of more than 3 million compromised devices were used to launch massive distributed denial-of-service (DDoS) attacks and were often rented out to other cybercriminals. Authorities seized the command-and-control infrastructure behind the botnets, though no arrests have yet been announced, with investigations continuing alongside partners in Canada and Germany.
Among the takedowns, Aisuru and its offshoot Kimwolf stood out for their scale and impact. Together comprising over a million infected devices—from webcams and DVRs to Android-based smart TVs—they were responsible for some of the largest DDoS attacks ever recorded. One attack in November reached more than 30 terabits per second, nearly tripling previous records and demonstrating the growing destructive potential of botnet-driven campaigns.
All four botnets were variants of the Mirai malware, a codebase that has underpinned IoT-based cyberattacks for nearly a decade. These newer versions expanded on Mirai’s capabilities, exploiting a broader range of internet-connected devices and introducing novel techniques, such as leveraging residential proxy networks to infiltrate home systems. Researchers say these innovations have undermined traditional assumptions about the security of consumer networks and enabled attacks capable of disrupting critical infrastructure or even national connectivity.
Despite the success of the takedown, experts caution that it represents only a temporary disruption. Botnet operators have shown resilience and adaptability, using tactics like blockchain-based infrastructure to evade shutdowns. As long as vulnerable devices remain widespread, new botnets are likely to emerge, continuing the ongoing “cat-and-mouse” cycle between cybercriminals and law enforcement. (Andy Greenberg / Wired)
Related: US Department of Justice, Help Net Security, Security Affairs, Livemint, Reuters, Cyber Security News, Security Week, Heise Online, Krebs on Security, Akamai, Bleeping Computer
International law enforcement agencies took down more than 373,000 darknet sites in a coordinated effort known as Operation Alice, replacing them with warning banners and launching investigations into hundreds of users.
The sites, spread across more than 100 servers and 32 platforms, were designed to lure individuals seeking child sexual abuse material but were in fact scams that took payment without delivering any content. Authorities have issued an arrest warrant for the suspected operator and are investigating around 600 individuals connected to the platforms.
The operation uncovered a large-scale scheme in which the sites advertised illegal content using explicit imagery and charged users in Bitcoin for access to supposed downloads. Prices ranged from $20 to $250, with offerings spanning gigabytes to terabytes of material, alongside additional cybercrime services like stolen data. In reality, the platforms were designed solely to defraud users, though law enforcement treated all interactions seriously, given the nature of the content and the risk to children.
Investigators used darknet monitoring tools and cryptocurrency tracing to identify the alleged operator, a 35-year-old Chinese national, and track payments through a legitimate service provider.
The operation, coordinated by Europol and involving 23 countries, also led to real-world interventions where children were at risk and multiple arrests and searches, particularly in Germany. Authorities emphasize that investigations are ongoing, with additional suspects still being identified and pursued. (Dirk Knop / Heise Online)
Related: Europol, The Economic Times

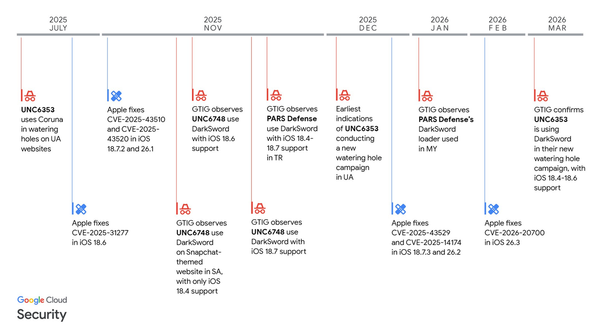
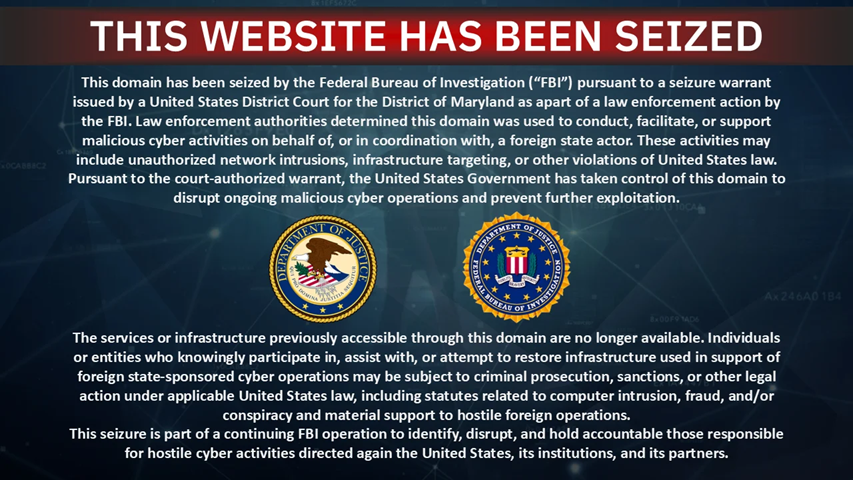
The FBI seized two websites used by the Handala hacktivist group following a major cyberattack on medical technology company Stryker that wiped roughly 80,000 devices.
The domains now display a federal seizure notice stating they were used to support malicious cyber activities tied to a foreign state actor. Handala, an Iranian-linked pro-Palestinian group associated with Iran’s Ministry of Intelligence and Security, has conducted destructive attacks primarily targeting Israeli organizations using malware designed to erase systems. (Lawrence Abrams / Bleeping Computer)
Related: TechCrunch, Times of India, Times of Israel, Cyber Daily, NBC News, Jewish News Service, Axios
North Carolina man Cameron Nicholas Curry was convicted of six counts of extortion after stealing sensitive corporate data while working as a contractor for a DC-based technology company.
Using his access as a data analyst, Curry exfiltrated employee and compensation data and later demanded payment to prevent its release, ultimately obtaining about $2.5 million from the company in early 2024.
After his contract ended, Curry launched a sustained extortion campaign, sending more than 60 threatening emails to employees and executives over six weeks. He claimed the stolen data exposed pay inequities and framed his actions as promoting salary transparency, while attaching screenshots of confidential employee information and threatening regulatory complaints and legal action.
Investigators quickly identified Curry due to basic operational security failures, including linking ransom payments to accounts tied to his family. He was arrested weeks after the payment, and authorities say the scheme was motivated by the non-renewal of his contract.
Curry now faces up to 12 years in prison, highlighting the significant insider threat risks posed by contractors with access to sensitive systems. (Matt Kapko / CyberScoop)
Related: Justice Department, Data Breaches.net, Bleeping Computer, Security Week, Cyber Press, CyberInsider
Michael Smith, a North Carolina man, has pleaded guilty in what prosecutors describe as the first US criminal case involving AI-assisted streaming fraud.
He admitted to one count of conspiracy to commit wire fraud and faces up to five years in prison, along with more than $8 million in forfeiture. Sentencing is scheduled for July 29. Smith was first indicted and arrested in September 2024 in what was the first criminal case of its kind in the US.
At that time, he was charged with three felony counts: wire fraud, wire fraud conspiracy, and money laundering conspiracy, each carrying a maximum sentence of 20 years in prison.
Prosecutors say Smith used artificial intelligence to generate hundreds of thousands of songs and deployed thousands of bot accounts across major streaming platforms to play them billions of times. By spreading streams across a vast catalog to evade detection, he fraudulently collected over $8 million in royalties that would otherwise have gone to legitimate artists.
The scheme was uncovered in part by the Mechanical Licensing Collective, which flagged anomalies in Smith’s unusually large music output. The case highlights growing concerns about AI-enabled fraud in the music industry, as well as the increasing role of detection systems and law enforcement in combating large-scale manipulation of streaming platforms. (Music Business Worldwide)
Related: Rolling Stone, US Department of Justice, Digital Music News, Billboard, Stereogum
The White House has unveiled a new federal legislative framework for regulating artificial intelligence, emphasizing the need for a unified national approach rather than a patchwork of state laws.
The plan focuses on protecting children, communities, and small businesses while promoting continued AI innovation and signals the administration’s preference for Congress to establish a single, nationwide regulatory structure.
The administration is now pushing Congress to act quickly to turn the framework into legislation, amid ongoing disagreements on Capitol Hill over how to regulate AI.
Lawmakers are under increasing pressure to deliver a cohesive policy, but divisions remain over issues like federal preemption of state laws and specific safeguards, meaning the framework serves as both a policy blueprint and a call to accelerate legislative action. (Katharine Jackson and Doina Chiacu / Reuters and Maria Curi, Ashley Gold / Axios)
Related: White House, White House
A French naval officer inadvertently exposed the location of the aircraft carrier Charles de Gaulle after logging a workout on the fitness app Strava.
The publicly shared GPS data revealed the ship’s position in the Mediterranean near Cyprus, raising alarm given heightened regional tensions involving Iran, Israel, and the United States. What appeared to be a routine fitness activity became a significant operational security breach.
French authorities acknowledged the breach and said it violated security protocols, with possible disciplinary action for those involved. (Asia Balluffier , Sébastien Bourdon , Liselotte Mas and Antoine Schirer / Le Monde)
Related: The Sunday Guardian, Security Affairs
Foster City, CA, is reporting a cybersecurity breach that occurred early Thursday and is "widely impacting city services."
The city did not provide many details on the nature of the breach but said all public services outside of emergency responses have been temporarily paused.
The City Manager's Office is in the process of declaring a state of emergency that will allow the city to get financial help from outside agencies to respond to the breach, according to a statement issued by the city Thursday afternoon.
"It is possible that public information has been accessed in the breach, but that remains uncertain at this time," the city's statement said, adding that people who have done business with Foster City are encouraged to change passwords to protect their data.
"Foster City staff, with the assistance of outside cybersecurity experts, are working diligently to restore the integrity of the city's system and ensure there are no further security issues impacting services to our community," City Manager Stefan Chatwin said in the statement. (Bay City News Service)
Related: Foster City, San Mateo Daily Journal, East Bay Times, Mercury News
Navia Benefit Solutions, a third-party administrator for employee healthcare and spending accounts, disclosed a data breach affecting about 2.7 million people.
Hackers accessed its systems between late December and mid-January, stealing sensitive information including names, Social Security numbers, dates of birth, contact details, and health plan data tied to HRAs, FSAs, and COBRA plans.
The breach was discovered on January 23 and reported to federal authorities, with some impacted records dating back to 2018.
The incident has raised concerns given Navia’s role serving more than 10,000 companies and public-sector programs, including thousands of workers in Washington state. While no claims or financial data were exposed, the scale and sensitivity of the data have triggered multiple class action lawsuits. (Jonathan Greig / The Record)
Related: Navia, Maine Attorney General, Tom's Guide, Bleeping Computer, Cyber Daily
Researchers at Threat Fabric report that a newly identified Android malware called Perseus is spreading through fake IPTV apps distributed on unofficial app stores, exploiting users who sideload pirated streaming services.
Once installed, the malware can take full control of a device, enabling screen capture, overlay attacks, and remote manipulation. Researchers say it primarily targets financial institutions and cryptocurrency apps, with a strong focus on users in Turkey and Italy.
Perseus stands out for a novel capability: scanning personal note-taking apps such as Google Keep, Evernote, and Microsoft OneNote to extract sensitive information like passwords, recovery phrases, and financial details. This marks a shift beyond traditional credential theft toward harvesting more contextual, user-curated data.
The malware uses Android Accessibility Services to navigate devices, log activity, and stealthily collect information while hiding its actions from victims.
The malware also incorporates advanced evasion techniques, assessing device characteristics to avoid detection and using a “suspicion score” to determine whether to proceed with an attack. (Bill Toulas / Bleeping Computer)
Related: Threat Fabric, The Record, WION, The Cyber Express, Mezha, Android Police
Stacy Bostjanick, the leading force behind the Defense Department’s Cybersecurity Maturity Model Certification (CMMC) program for much of the last six years, is retiring. is leaving federal service after 37 years on April 30.
Sources say Buddy Dees, the director of the program management office, is expected to take over as the new director of the DIB cybersecurity program on an interim basis.
Sources say Bostjanick is likely to move into a new job in the private sector. (Jason Miller / Federal News Network)
Cape, the privacy-minded mobile carrier based in the United States, announced it had raised $100 million in a Series C funding round.
Bain Capital Ventures and IVP led the round with additional participation from other investors. (Thomas Brewster / Forbes)
Related: Ventureburn
Cybersecurity startup Oasis Security announced it had raised $120 million in a Series B funding round.
Craft Ventures led the round with participation from existing investors Cyberstarts, Sequoia Capital, and Accel. The new capital brings the company’s total funding to $195 million. (Meir Orbach / Calcalist)
Related: PR Newswire, Bloomberg, FinTech Global, Silicon Angle
Allure Security, a Boston, MA-based AI-native disinformation defense company, announced it had raised $17 million in a Series B funding round.
Riverside Acceleration Capital led the round with participation from existing investors Curql, Glasswing Ventures, and Gutbrain Ventures. (Ionut Arghire / Security Week)
Related: FinTech Global, Pulse 2.0, PR Newswire, FinSMEs
Best Thing of the Day: Meta Did Something Right
Signal creator Moxie Marlinspike says the technology powering his encrypted AI chatbot, Confer, will be integrated into Meta AI.
Worst Thing of the Day: Meta Did Something Not So Right
Meta's decision to eliminate end-to-end encryption for Instagram DM could be the first major domino to fall for end-to-end encryption tech worldwide.
Closing Thought