AI safety red lines tested as OpenAI replaces Anthropic in last-minute Pentagon deal
Israel reportedly hacked a widely used Iranian prayer app to urge military defections, Unconfirmed reports suggest large-scale cyberattacks in Iran, S. Korea's tax service exposed millions of crypto wallets' seed phrases, European retailer ManoMano breach exposed 38m customers' PII, much more


Don't miss my piece for Computerworld and other publications on the news of how the Pentagon banned Anthropic and agreed to replace it with OpenAI, and what the implications of this switch-out are.
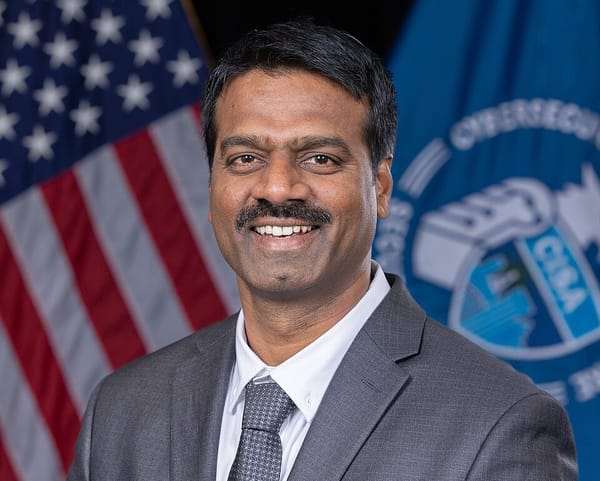
OpenAI reached an agreement with the US Defense Department to deploy its artificial intelligence models on classified Pentagon networks, stepping in after negotiations between the military and rival startup Anthropic collapsed over the scope of AI safety guardrails.
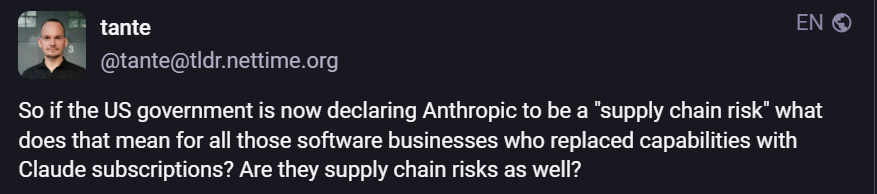
The deal follows a public dispute between Anthropic and Defense Secretary Pete Hegseth over whether AI systems used by the military should be subject to explicit contractual prohibitions on mass domestic surveillance and fully autonomous weapons. After Anthropic declined to remove certain restrictions, Donald Trump directed federal agencies to halt use of the company’s technology, and Hegseth said he would pursue designating Anthropic a “supply chain risk.”
OpenAI Chief Executive Sam Altman said the company’s Pentagon agreement preserves its core “red lines,” including bans on the use of its models for mass domestic surveillance and on directing autonomous weapons without human oversight. In a separate statement detailing the arrangement, OpenAI described a system of “layered protections,” including contractual restrictions, retention of its safety controls, secure cloud deployment, and involvement of cleared personnel to monitor compliance. The company said violations of the agreement could result in termination.
Anthropic, in its own statement responding to the Defense Secretary’s comments, said it had negotiated in good faith and supports lawful national security uses of its Claude model with two narrow exceptions: mass surveillance of Americans and fully autonomous weapons systems. The company said those limitations had not interfered with any Defense Department missions to date and argued that labeling it a supply chain risk would be unprecedented for a US AI company. Anthropic said it would challenge such a designation in court.
While OpenAI and the Pentagon say the new agreement balances national security needs with strong safeguards, some experts say the contract’s language — which restricts certain uses but does not explicitly bar the collection of publicly available information about Americans — leaves room for potential surveillance concerns similar to those raised during the Anthropic negotiations.
The episode highlights escalating tensions between leading AI developers and the US government over how advanced generative AI should be deployed in defense settings, and whether companies’ voluntary ethical boundaries can withstand pressure from national security demands in the absence of comprehensive federal AI regulation.
Ironically, within hours of declaring that the federal government would end its use of artificial-intelligence tools made by tech company Anthropic, Trump launched a major air attack in Iran with the help of those very same tools.
Commands around the world, including US Central Command in the Middle East, use Anthropic’s Claude AI tool, people familiar with the matter confirmed.
Finally, former OpenAI researcher Sarah Shoker, who led OpenAI’s Geopolitics Team, argued that major AI developers currently lack clear, coherent public policies on what military applications are permitted or prohibited.
Shoker suggested that the language companies use to describe allowed uses, such as “all lawful purposes,” is often vague by design and can obscure the realities of how systems might be used in defense contexts. (Rachel Metz and Katrina Manson / Bloomberg, Maria Curi / Axios. Reuters, Anthropic, Marcus Weisgerber, Amrith Ramkumar, and Shelby Holliday / Wall Street Journal and Sarah Shoker / fishbowlification)
Related: OpenAI, Business Insider, IBTimes.co.uk, DataBreachToday.com, TechCrunch, WWL-TV, TechRadar, Türkiye Today, Axios, Hartford Courant, Business Insider, Rohan's Bytes, Reuters, DigiTimes, Engadget, Flux, Tech in AsiaWashington Examiner, WashingtonExaminer.com, Mercury News, The Atlantic, Fortune, Computerworld, MS NOW, Bloomberg Law, The Hill, Benzinga, Livemint, Cointelegraph, Inc.com, CBS News, Sky News, The Atlantic, Moneycontrol, MarketWatch, PYMNTS.com, Al Jazeera
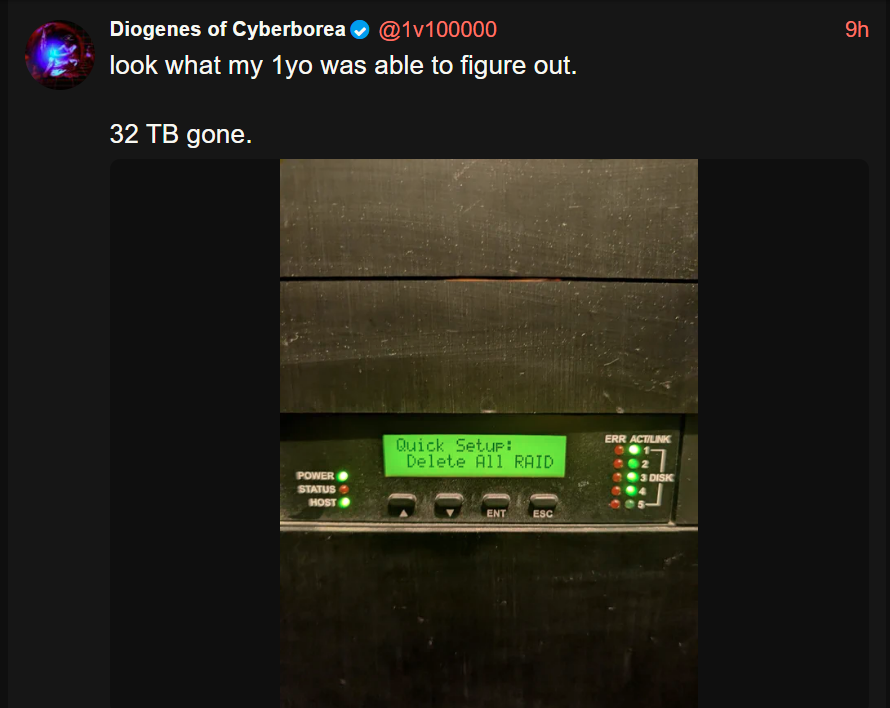
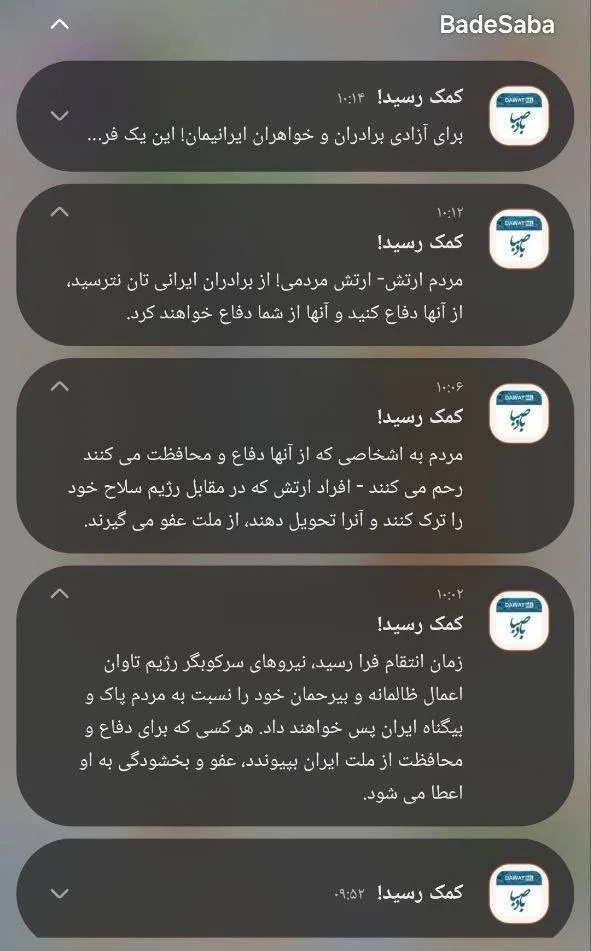
Sources say Israel hacked a widely used Iranian prayer and calendar mobile application to send mass push notifications urging members of Iran’s military and security forces to defect.
The messages, delivered in Persian to potentially millions of users, called on security personnel to lay down their arms and join efforts to oppose the Iranian government. Screenshots circulating online showed notifications telling recipients that “help has arrived” and encouraging resistance.
The targeted app, which provides daily prayer times and religious guidance, has a broad user base inside Iran, giving the operation significant reach. The move came amid escalating hostilities between Israel and Iran.
Detailed independent verification of the breach or a public acknowledgment of responsibility from Israeli officials has yet to be released. (Dov Lieber and Dustin Volz / Wall Street Journal)
Related: Wired, Straight Arrow News, r/Israel, The Financial Express, NDTV, The Cyber Press
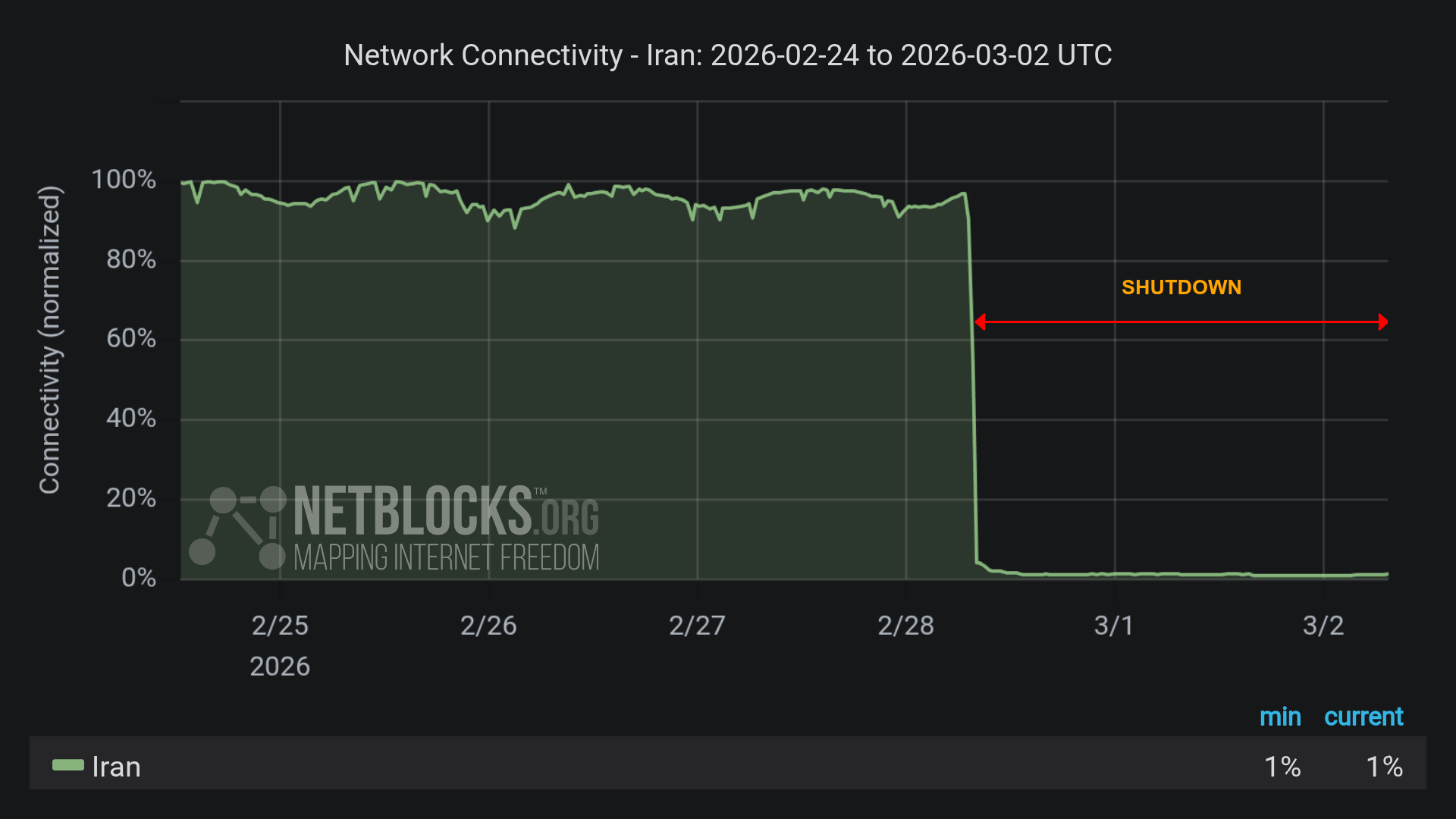
Unconfirmed reports on Saturday indicated that Iran entered an almost complete digital fog in what appeared to be a large-scale cyberattack accompanying Operation “Roar of the Lion.”
Critical infrastructure, official news sites, and security communications systems reportedly stopped functioning, leaving the leadership in a communications blackout at home and abroad.
NetBlocks confirmed on Saturday that internet connectivity in Iran plunged to an extremely low level, reaching 4% of normal traffic, signaling an almost total shutdown of nationwide access.
The attack reportedly also hit the regime’s propaganda arms: the IRNA website was taken offline for an extended period, and Tasnim, which is identified with the IRGC, experienced severe disruptions and hacks that reportedly displayed subversive messages against Supreme Leader Ali Khamenei.
Western intelligence sources said the damage to the IRGC's communications infrastructure was meant to prevent coordination of counterattacks and disrupt the ability to launch drones and ballistic missiles by Iranian cyber and electronic units.
Beyond website outages, reports from Tehran and other major cities, including Isfahan and Shiraz, described failures of local apps and government digital services.
The operation was presented as the peak of a campaign that began in January, when government satellite broadcasts were hacked, and content calling for the regime’s overthrow was reportedly aired to millions of households. (Dr. Itay Gal / The Jerusalem Post)
Related: Kurt the Cyber Guy, DefenseOne, Globe and Mail
South Korea’s National Tax Service inadvertently exposed the seed phrases for cryptocurrency wallets it had seized, allowing an unknown party to access and transfer roughly 4 million Pre-Retogeum (PRTG) tokens from the wallets, according to Decrypt.
The disclosure occurred when the agency published a photo in a press release that showed handwritten recovery phrases alongside confiscated hardware wallets. Seed phrases function as master keys that allow full control over digital assets stored in a wallet.
After the phrases were made public, the tokens, nominally valued at about $4.8 million, were moved to another Ethereum address. However, the tokens were returned to the original wallets within about 20 hours.
It was unclear whether the transfer was carried out by a white-hat actor seeking to demonstrate the vulnerability or by someone who later realized the tokens would be difficult to liquidate. (Logan Hitchcock / Decrypt)
Related: Bleeping Computer, Bitcoin.com, The Block, Yellow, Forklog, Blockonomi
European online DIY retailer ManoMano said it is notifying about 38 million customers that their personal information was exposed in a data breach after hackers compromised a third-party service provider earlier this year.
ManoMano, a French e-commerce company that operates in several European countries, including France, Germany, Italy, Spain, and the United Kingdom, confirmed the incident was identified in January and involved unauthorized access through a subcontractor’s systems.
The company said the breach resulted in the extraction of customer names, email addresses, phone numbers, and customer service communications. Passwords and core company systems were not accessed, and no data was modified on ManoMano’s own servers.
A threat actor using the alias “Indra” claimed responsibility for the attack on a hacker forum, alleging it held data on roughly 37.8 million accounts along with support tickets and attachments.
ManoMano said it has revoked the subcontractor’s access, strengthened controls, and alerted relevant French authorities, including the national data protection watchdog and cybersecurity agency, while advising customers to monitor for phishing or social engineering attempts. (Bill Toulas / Bleeping Computer)
Related: TechRadar, Security Week, Security Affairs, SC Media, Tech Republic, The Register
The University of Hawaiʻi Cancer Center said a cyberattack on its Epidemiology Division may have exposed sensitive personal information held in research records, potentially affecting more than a million people.
The center, part of the University of Hawaiʻi system in Honolulu, said the breach involved data containing Social Security numbers, driver’s license numbers collected in 2000, and voter registration records from 1998, which were used in long-running studies including the Multiethnic Cohort Study.
The university said about 87,493 study participants were directly impacted, and an additional approximately 1.15 million people may have had their personal information included in the historical records.
Officials said the attack did not affect clinical trials, patient care, student records, or other divisions of the center. The university reported that an unauthorized party encrypted and may have exfiltrated data, and that law enforcement and cybersecurity experts were engaged to obtain a decryption tool and secure assurances that any accessed information was destroyed.
Notices offering credit monitoring and identity protection services have been issued to those potentially affected, and dedicated call centers have been established to assist individuals. University leaders said they regret the incident and are committed to strengthening data protections. (Hawai'i News Now)
Related: University of Hawai'i News, Kauai Now News
Cybersecurity journalist Brian Krebs said he has identified the individual believed to be behind Kimwolf, one of the world’s largest and most disruptive botnets.
The botnet operator uses the alias “Dort” and has been linked to a series of coordinated distributed denial-of-service attacks, doxing, and email flooding, including attacks on a security researcher who disclosed a vulnerability that was used to build Kimwolf, as well as attacks on Krebs. The assaults have included attempts to provoke a law enforcement response to Krebs' home.
Publicly available intelligence suggests Dort may be a Canadian born in August 2003 who has used multiple online aliases such as “CPacket,” “M1ce” and “DortDev.” A search on the username CPacket at the open source intelligence platform OSINT Industries finds a GitHub account under the names Dort and CPacket that was created in 2017 using the email address jay.miner232@gmail.com.
The breach tracking service Constella Intelligence finds the password used by jay.miner232@gmail.com was reused by just one other email address: jacobbutler803@gmail.com.
Searching this email address at DomainTools.com reveals it was used in 2015 to register several Minecraft-themed domains, all assigned to a Jacob Butler in Ottawa, Canada.
Early online activity under these names includes contributions to game-cheating software and the development of tools to bypass online security measures like CAPTCHA. Investigators traced accounts associated with Dort to various cybercrime forums and linked the same email address to multiple handles used over several years, indicating a long history in hacking communities. (Brian Krebs / Krebs on Security)
Senator Ron Wyden (D-OR), a senior member of the Senate Intelligence Committee, is blocking the confirmation of Lt. Gen. Joshua Rudd to lead both US Cyber Command and the National Security Agency.
Wyden said Rudd, currently deputy commander of US Indo-Pacific Command, lacks the necessary background in cyber operations and digital intelligence to assume the dual role immediately, and raised concerns about his understanding of surveillance authorities and civil liberties protections during his confirmation hearing.
Wyden’s hold forces a formal Senate vote rather than approval by unanimous consent, potentially delaying the process. The leadership posts have been without a permanent appointee since last year, when the previous chief was removed, and the Pentagon has urged the Senate to act quickly on Rudd’s nomination.
Wyden, known for his focus on privacy rights, wrote in a letter included in the Congressional Record that constitutional protections require leaders who fully grasp both cybersecurity threats and legal safeguards. (Martin Matishak / The Record)
Related: DefenseOne, The Hill, MeriTalk, Congress.gov
Samsung and the State of Texas have reached a lawsuit settlement agreement over the alleged unlawful collection of content-viewing information through its smart TVs.
The lawsuit alleged that Samsung used Automated Content Recognition (ACR) technology to capture information about what consumers were watching in order to build advertising profiles, without clearly informing users or securing proper consen,ere confusing and did not meet requirements under the Texas Deceptive Trade Practices Act.
Under the settlement, Samsung will implement clearer consent mechanisms on its televisions and update its privacy disclosures for Texas residents. The company did not admit wrongdoing but agreed to enhance transparency around its data collection practices.
Paxton said the agreement represents a step toward protecting consumers from undisclosed tracking through connected devices, and indicated that investigations into other smart TV manufacturers remain ongoing. (Bill Toulas / Bleeping Computer)
Related: Texas Attorney General
Delhi Police arrested 27 people across 10 states after a weeklong operation targeting cyber fraud syndicates.
The raids, carried out from Delhi to West Bengal and other states, were linked to a range of online scams, including investment frauds, malicious APK file distribution, social media impersonation, credit card deception, task-based earning schemes, and visa-related cheating, authorities said.
The cases were connected to about 150 complaints on the National Cyber Crime Reporting Portal, with financial scrutiny uncovering suspicious transactions worth nearly 14 million rupees tied to the suspects’ bank accounts.
Police seized mobile phones, SIM cards, bank cards, and other items believed to have been used in the frauds as part of the coordinated action. The accused, ranging in age from early 20s to early 40s, were taken into custody as investigations continue. (The Times of India)
Related: The420, Rediff, The Pioneer, Devdiscourse, Press Trust of India, News4hackers
The French Health Ministry said a major cyberattack on a widely used medical software system provided by the Cegedim Sante company has exposed the personal and medical information of more than 15 million people, officials and media reported.
The ministry said the breach, discovered late last year, involved administrative details and doctors’ notes from some 1,500 medical practices that used the affected software, which is widely deployed across the country.
The data reportedly included names, phone numbers, and postal addresses, and for a smaller subset of patients, doctors’ annotations that could contain sensitive information.
French authorities have not publicly identified the group responsible for the medical data hack, and the software provider involved has lodged a criminal complaint and pledged cooperation with investigators. (Rébecca FRASQUET, Chloé RABS / AFP)
Best Thing of the Day: How to spot Cell Site Simulators
Cooper Quintin, a security researcher and senior public interest technologist with the Electronic Frontier Foundation (EFF), described to 404 Media an easy-to-install tool that can easily spot nearby IMSI catchers.
Worst Thing of the Day: Does the White House Consider SCIF Security Woke?
White House Chief of Staff Susie Wiles breached a major cybersecurity rule when she wore an electronic fitness device on her wrist next to the President while he bombed Iran.
Closing Thought