Conflicting accounts emerge over Plankey's departure from DHS, future as CISA head
European law enforcement busted up Tycoon2FA phishing platform, FBI and European cops take down cybercrime forum Leakbase, Phobos admin pleads guilty to wire fraud, Lawmakers call for probe into decades-old TEMPEST attacks, IDF says it bombed complex hosting Iran's cyberwar HQ, much more
Metacurity is the only daily cybersecurity newsletter that is written outside the usual cyber press echosphere and is a refreshing alternative to vendor-driven content and PR-flavored threat intelligence.
Please consider supporting my work on Metacurity by upgrading your subscription. Thank you.
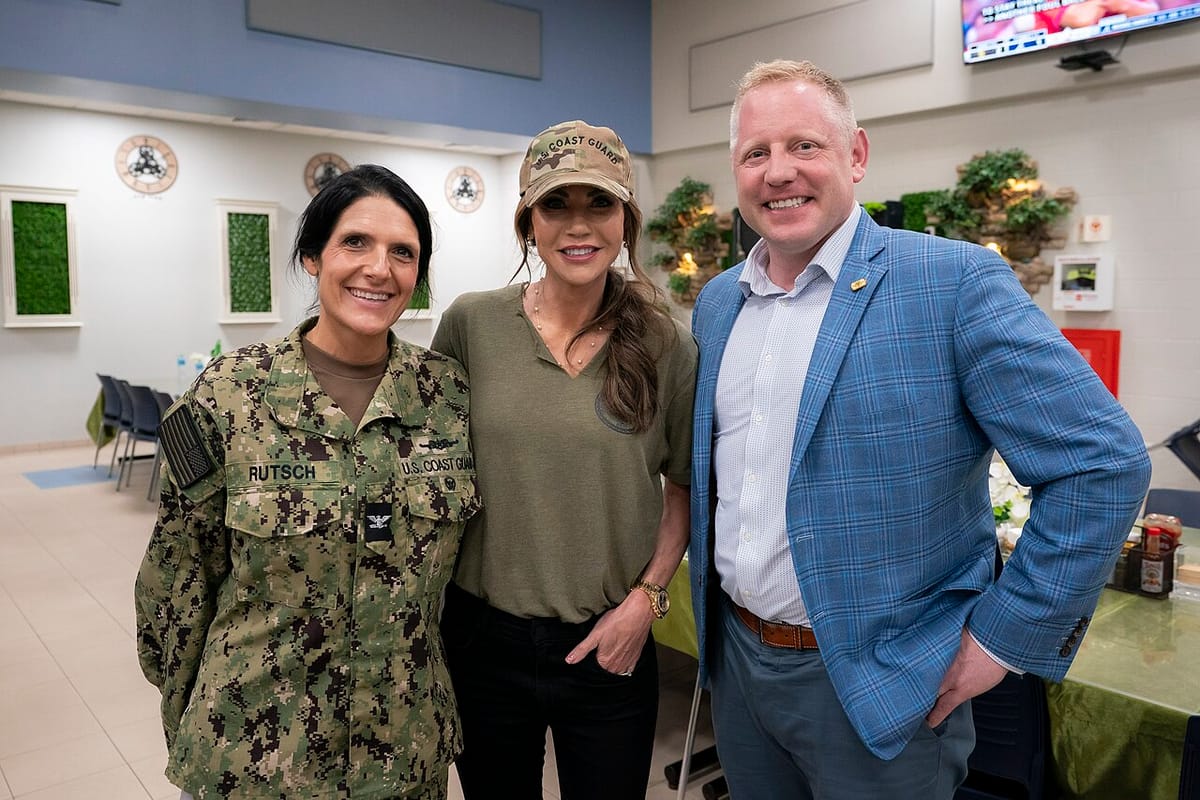
Conflicting accounts have emerged over the circumstances surrounding the abrupt departure of highly regarded Sean Plankey from his role as a senior Department of Homeland Security adviser, with the Trump administration's nominee to lead the Cybersecurity and Infrastructure Security Agency and other sources offering sharply different versions of events.
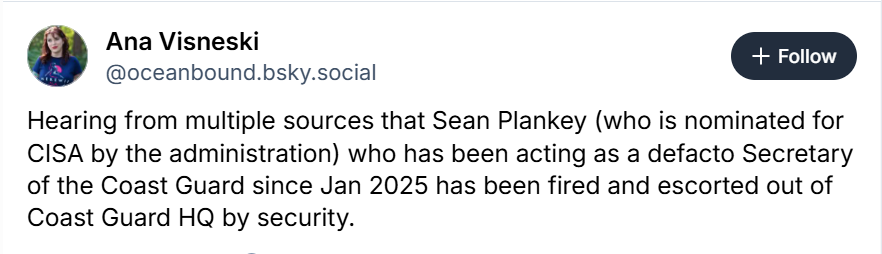
The story broke not in a newsroom but on social media. On March 3, Ana Visneski, a former head of global disaster response at Amazon Web Services and former chief of digital media for the US Coast Guard, posted on Bluesky that she was "hearing from multiple sources" that Plankey "has been fired and escorted out of Coast Guard HQ by security."
Visneski also characterized Plankey's informal role at DHS as more expansive than his official title suggested, describing him as having acted as a "de facto Secretary of the Coast Guard since Jan 2025."
Craig Hooper, a widely followed naval and military analyst, amplified the story shortly after on X. Hooper wrote that "word is spreading" that "the USCG's de facto Secretary, Senior Advisor Sean Plankey, has been dismissed" — noting pointedly that the news was emerging as Homeland Security Secretary Kristi Noem was testifying before the Senate.
Yesterday, CBS News reported the broad thrust of both social media accounts, reporting that Plankey was escorted out of Coast Guard headquarters late Monday and had his access badge removed, according to sources familiar with the matter.
Plankey himself told a different story. NextGov/FCW reported yesterday that, according to two people familiar with private conversations Plankey held with colleagues, he said he departed voluntarily to demonstrate to Sen. Rick Scott (R-FL) that he was no longer involved in shipbuilding contract work — the issue at the center of Scott's hold on his nomination, first placed in December. In a written statement, Plankey said he "is focused on his CISA nomination" and is "prepared to lead the nation's cyber defense agency."
DHS declined to elaborate. "We have no personnel matters to announce at this time," a spokesperson said, according to CBS News. CISA, which is in government shutdown mode, did not respond to Metacurity's request for comments.
The discrepancy cuts to the heart of a turbulent period at CISA, which has been without a Senate-confirmed director and is navigating rapid internal changes. Acting director Madhu Gottumukkala was replaced last month by Nick Andersen, the agency's executive assistant director for cybersecurity, following unflattering media reports, including that Gottumukkala had uploaded sensitive government documents marked "for official use only" to a public version of ChatGPT.
CBS News also reported that Plankey had longstanding tensions with Gottumukkala over cybersecurity contracts, with Plankey pushing for certain contracts to proceed while Gottumukkala resisted. Because Plankey is a nominee awaiting confirmation, he is generally expected to refrain from involvement in agency operations, particularly contracting matters.
Adding further uncertainty, CBS News reported that Plankey's January renomination by President Trump may have been unintentional — one source described it as an administrative error embedded in a broader White House nominations package.
Scott's hold on Plankey's nomination stemmed from DHS scaling back a Coast Guard cutter contract with Eastern Shipbuilding Group, a Florida-based firm. Plankey's path to confirmation faces additional obstacles: Sen. Thom Tillis (R-NC) this week threatened to stall all Senate nominations unless Noem responded to outstanding inquiries from his office regarding immigration enforcement and disaster relief funding. And Sen. Ron Wyden (D-OR) said he will block Plankey's confirmation until CISA releases a report on China's Salt Typhoon hacking group, which he has long demanded.
The leadership uncertainty at CISA comes at a fraught moment. DHS funding has lapsed for approximately two weeks. US officials have warned of heightened cyber threats from Iran-linked actors following the outbreak of conflict with Iran over the weekend, with DHS issuing a Critical Incident Report warning that the hacktivist group Cyber Islamic Resistance has called for attacks on US and Israeli targets. (Nicole Sganga / CBS News and David DiMolfetta / NextGov/FCW)

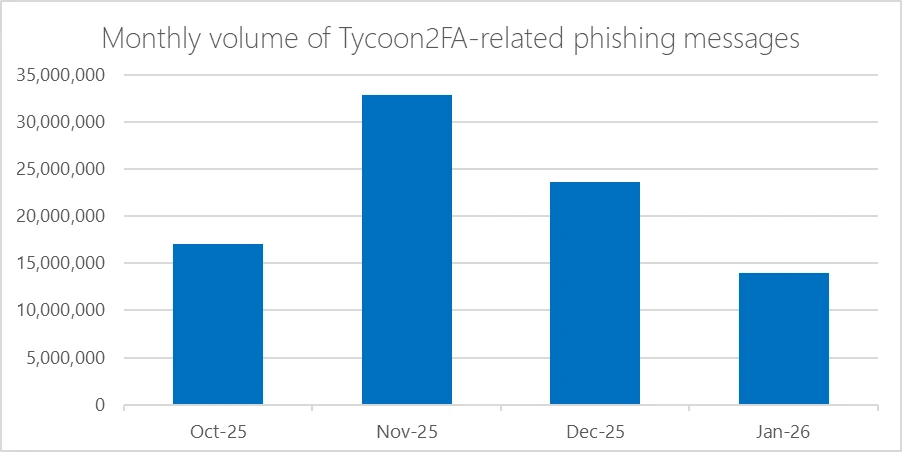
An international law enforcement operation coordinated by Europol has disrupted Tycoon2FA, a phishing-as-a-service platform linked to tens of millions of fraudulent messages monthly.
A total of 330 domains — including control panels and phishing pages forming the platform's backbone infrastructure — were seized and taken offline. The technical disruption was led by Microsoft, with law enforcement in Latvia, Lithuania, Portugal, Poland, Spain, and the United Kingdom carrying out simultaneous infrastructure seizures.
The investigation was launched after intelligence was shared by Trend Micro. Europol disseminated the information through its EC3 Advisory Groups, enabling a coordinated response. Additional support came from Cloudflare, Coinbase, Proofpoint, SpyCloud, and others.
Active since at least August 2023, Tycoon2FA was used to bypass multi-factor authentication protections and compromise accounts at nearly 100,000 organizations worldwide, including government agencies, schools, and healthcare providers. By mid-2025, the platform was generating tens of millions of phishing emails per month, reaching more than 500,000 organizations and accounting for 60% of all phishing attempts blocked by Microsoft.
The platform operated as an adversary-in-the-middle service, using a reverse proxy to intercept login credentials and session cookies in real time, targeting users of Microsoft 365, OneDrive, SharePoint, Gmail, and other services. Attackers could maintain access to compromised accounts even after password resets, unless active sessions were explicitly revoked.
The service was sold through Telegram for as little as $120 for 10 days of access. (Sergiu Gatlan / Bleeping Computer)
Related: Europol, Proofpoint, Microsoft, Help Net Security, Coinbase, Microsoft Security Blog, Trend Micro, crypto.news, Cointelegraph, TrendAI, Kieran McCorry, CSO, CyberInsider, Infosecurity, Cloudflare, Cyber Press, Heise Online, CyberInsider, Security Week
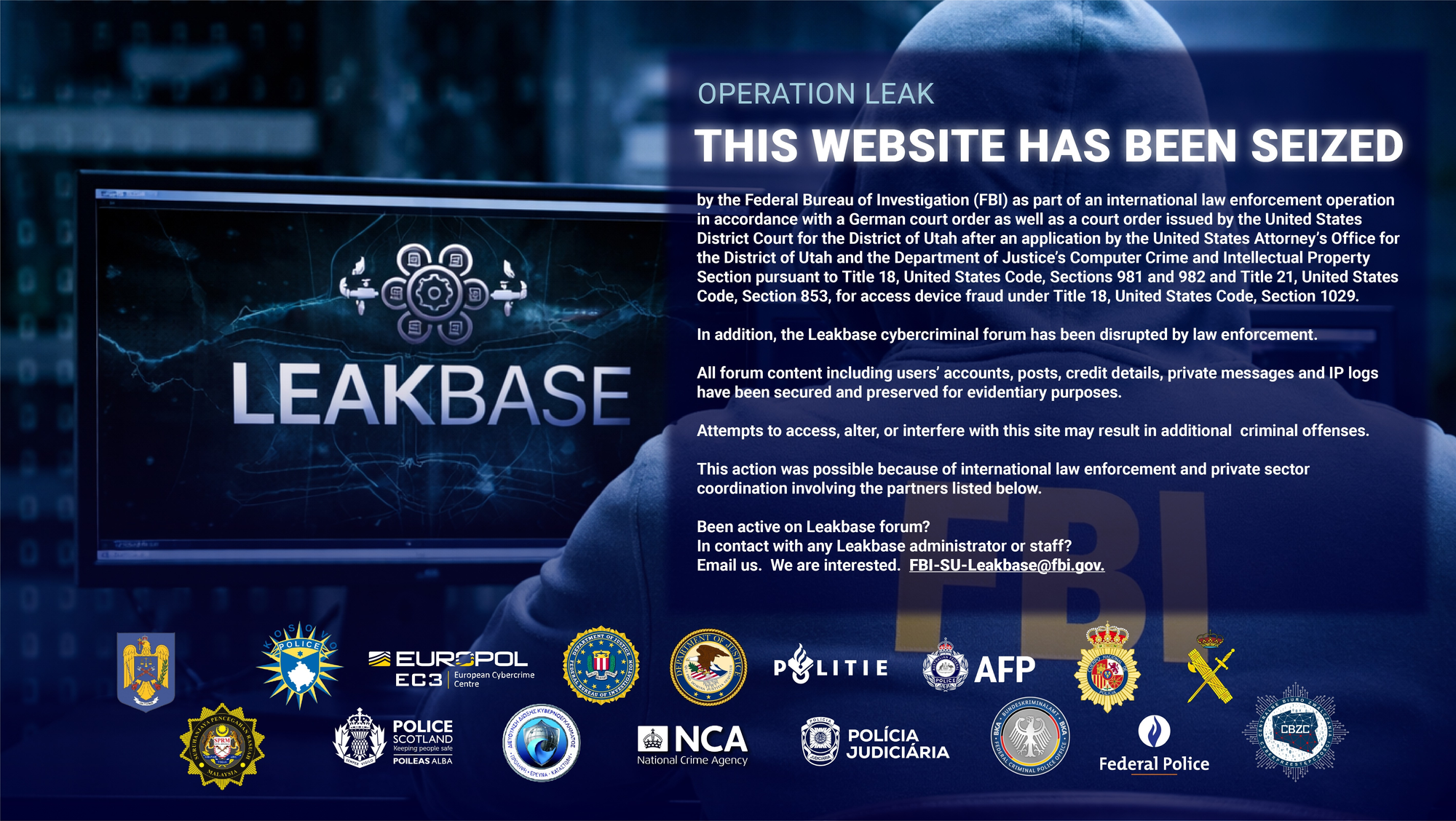
The FBI and European law enforcement agencies have taken down Leakbase, a subscription-based cybercrime forum where criminals bought and sold stolen credentials and software exploits since 2021.
Dubbed "Operation Leak," the effort resulted in 100 law enforcement actions against 45 targets across more than a dozen countries, including 13 arrests, 32 searches, and interviews with 33 suspects. Authorities shut down hosting infrastructure stretching from the Netherlands to Malaysia, seized and redirected the forum's domains to FBI-controlled servers, and captured the forum's entire database.
Leakbase had grown to more than 142,000 registered members, with over 33,000 forum threads and 215,000 messages. Much of the data it offered was obtained through unauthorized access to government systems and US businesses, frequently via SQL injection attacks against unpatched web applications. The forum operated on a subscription model, with premium access available for a one-time fee of a few hundred dollars.
Brett Leatherman, assistant director of the FBI's cyber division, said the forum "continued to be an active location where users were increasingly sharing information that permits access to US-based networks, potentially critical infrastructure." The investigation was led by the bureau's Salt Lake City field office and spanned multiple years.
None of the arrests occurred in the United States. Leatherman said authorities are still determining how much revenue Leakbase generated and the full scope of victim losses. (Martin Matishak / The Record)
Related: CyberScoop, Europol, US Department of Justice, Bleeping Computer, Europol, PCMag, Washington Times, Cyber Security News, r/hacking, r/cybersecurity, TechCrunch, Brett Leatherman
Spanish and Ukrainian law enforcement dismantled a criminal network that trafficked war-displaced Ukrainian women to launder nearly $5.2 million through a sophisticated online gambling operation, authorities announced.
The ring recruited vulnerable young women from active combat zones in Ukraine, financed their travel to Spain, then stripped them of control over their bank accounts and identities. Once in Spain, victims were guided through the process of obtaining refugee status, then directed to open bank accounts and credit cards that criminals immediately seized.
Using stolen identities from more than 5,000 people across 17 nationalities, the network deployed automated bot programs to place thousands of simultaneous low-odds bets on online gambling platforms — a deliberate strategy to generate steady, seemingly legitimate returns while minimizing financial risk.
"The victims were in extremely vulnerable situations in areas heavily impacted by the war in Ukraine and were completely under the control of the suspects," Europol said.
Following a joint investigation launched in October 2023, Spanish authorities arrested 12 suspects and searched nine properties across Alicante and Valencia. Ukrainian police searched eight additional properties.
Seized assets included 500 SIM cards, 20 computers, 22 bots, dozens of mobile phones, and four high-end vehicles. Investigators froze ten properties worth more than $2.18 million and blocked accounts in 11 countries containing over $511,000. (Sergiu Gatlan / Bleeping Computer)
Related: Europol
Evgenii Ptitsyn, a Russian national, has pleaded guilty to wire fraud conspiracy for his role in administering the Phobos ransomware operation, which extorted more than $39 million from over 1,000 victims worldwide.
He was extradited from South Korea in November 2024 and admitted to overseeing the sale and day-to-day operation of Phobos, a ransomware-as-a-service platform active since at least November 2020. He faces up to 20 years in prison at sentencing scheduled for July 15.
Ptitsyn sold access to the ransomware to criminal affiliates via darknet forums, collecting per-deployment fees and a cut of ransom payments. Affiliates targeted schools, hospitals, and government agencies — encrypting data, stealing files, and threatening victims who refused to pay.
Phobos accounted for roughly 11% of all submissions to the ID Ransomware identification service between May and November 2024.
Separately, Europol's Operation Aether has pursued Phobos-linked suspects across 14 countries. A February 2025 raid detained two suspected affiliates and seized 27 servers. Polish authorities also recently detained a 47-year-old suspect connected to the group. Europol said the operation enabled authorities to warn more than 400 companies of ongoing or imminent attacks. (Sergiu Gatlan / Bleeping Computer)
Related: Justice Department
Senator Ron Wyden (D-OR) and Representative Shontel Brown (D-OH) have called on the Government Accountability Office to investigate the vulnerability of American consumers to so-called "side-channel attacks," a decades-old surveillance technique that exploits the unintentional physical signals emitted by computers and smartphones to steal private data.
The technique, originally codenamed TEMPEST by the NSA, takes advantage of the radio waves, sound, and vibrations produced by ordinary computing components. Researchers have already demonstrated the threat is real: a $300 device hidden inside a pita bread can steal data from a nearby computer, and a smartphone's microphone can be used to extract cryptographic keys from a computer's operating sounds.
While the US government shields its own classified systems using heavily shielded facilities, lawmakers argue it has "left the American people vulnerable and in the dark" by failing to warn the public or require device manufacturers to build in protections.
The lawmakers' letter urges the GAO to assess the scale of the threat, the feasibility of adding hardware countermeasures to consumer devices, and potential regulatory options — including compelling manufacturers to act. Regulators like the FCC and FTC could potentially be used as enforcement mechanisms.
Security experts caution that average users shouldn't panic, noting the attacks remain technically difficult and require close physical proximity. However, they warn that advances in AI could make the techniques easier to execute, and that the growing universe of "smart" home devices may present new vulnerabilities. (Andy Greenberg / Wired)
Related: Senator Ron Wyden
The Israel Defense Forces said it bombed a compound in Tehran housing Iran’s cyber warfare headquarters.
According to a statement from the IDF, its forces on Wednesday carried out a “wide-scale strike” targeting a collection of military sites on the Eastern edge of Tehran that allegedly housed the headquarters of the Iranian Islamic Revolutionary Guards Corps. The IDF claims that the headquarters of the IRGC’s “cyber and electronic headquarters” and its “Intelligence Directorate” were among the military outposts hit in the strike.
It’s unclear to what extent these military sites were damaged or whether there were any casualties. Iran remains under an almost total internet blackout, which began on Feb. 28 when the first US and Israeli strikes began, limiting the flow of information coming out of Iran. (Maggie Miller / Politico)

Cisco flagged two Catalyst SD-WAN Manager security flaws as actively exploited in the wild, urging administrators to upgrade vulnerable devices.
Catalyst SD-WAN Manager (formerly vManage) is network management software that enables admins to monitor and manage up to 6,000 Catalyst SD-WAN devices from a single centralized dashboard.
"In March 2026, the Cisco PSIRT became aware of active exploitation of the vulnerabilities that are described in CVE-2026-20128 and CVE-2026-20122 only," the company warned in an update to a February 25 advisory.
"The vulnerabilities that are described in the other CVEs in this advisory are not known to have been compromised. Cisco strongly recommends that customers upgrade to a fixed software release to remediate these vulnerabilities."
The high-severity arbitrary file overwrite vulnerability (CVE-2026-20122) can only be exploited by remote attackers with valid read-only credentials with API access, while the medium-severity information disclosure flaw (CVE-2026-20128) requires local attackers to have valid vmanage credentials on the targeted systems.
Cisco also released security updates to patch two maximum-severity vulnerabilities in its Secure Firewall Management Center (FMC) software.
Secure FMC is a web or SSH-based interface for admins to manage Cisco firewalls and configure application control, intrusion prevention, URL filtering, and advanced malware protection.
Both vulnerabilities can be exploited remotely by unauthenticated attackers: the authentication bypass flaw (CVE-2026-20079) allows attackers to gain root access to the underlying operating system, while the remote code execution (RCE) vulnerability (CVE-2026-20131) lets them execute arbitrary Java code as root on unpatched devices.
These patches were part of a large Cisco release of 25 joint security advisories covering security patches for 48 vulnerabilities in across its Secure Firewall Adaptive Security Appliance (ASA), Secure Firewall Management Center (FMC), and Secure Firewall Threat Defense (FTD) software products. (Sergiu Gatlan / Bleeping Computer, Sergiu Gatlan / Bleeping Computer and Kevin Poireault / Infosecurity Magazine)
Related: Infosecurity Magazine, Cisco, Cyber Press
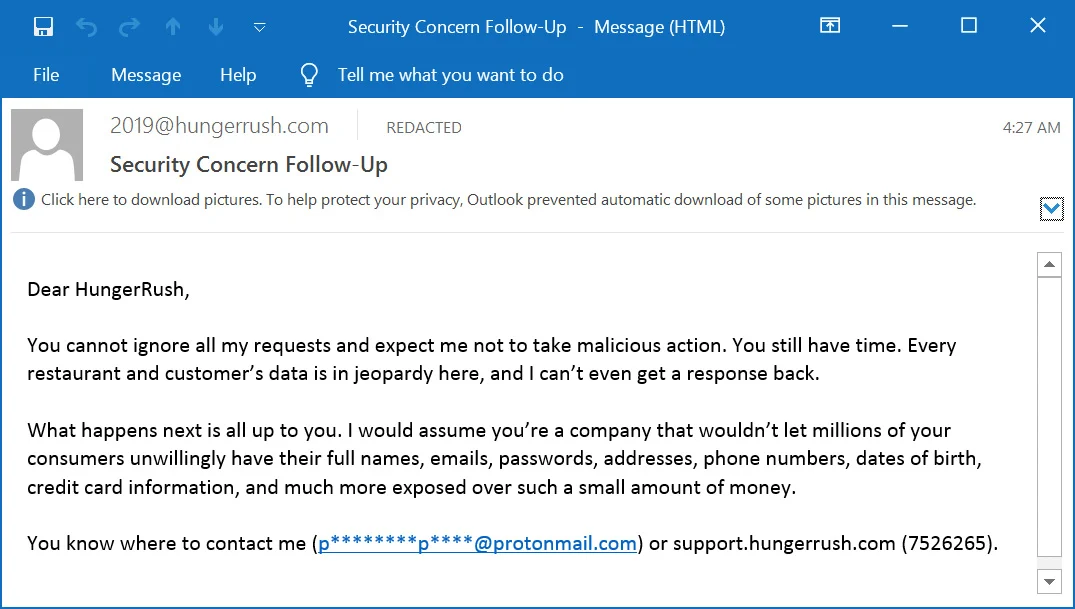
Restaurant technology provider HungerRush confirmed a security breach after a threat actor used its own email infrastructure to send extortion messages to customers of its 16,000+ restaurant clients.
The attacker sent emails from legitimate HungerRush addresses, claiming to hold data on millions of customers — including names, passwords, addresses, and payment card details — and threatening to expose it unless the company responded. The emails passed standard authentication checks, leading recipients to believe they were genuine HungerRush communications.
HungerRush says the breach stemmed from a compromised third-party vendor's credentials, which gave the attacker access to its email marketing account. The company disputes the broader data theft claims, stating that no passwords, financial data, or Social Security numbers were exposed and that credit card data is not stored in its systems. It has since disabled the affected email service and notified law enforcement.
Cybersecurity researcher Alon Gal separately flagged that an infostealer infection had compromised a HungerRush employee's device in October 2025, though the company says that incident is unrelated.
Customers who have ordered from restaurants using the HungerRush POS system should remain vigilant for phishing attempts. (Lawrence Abrams / Bleeping Computer )
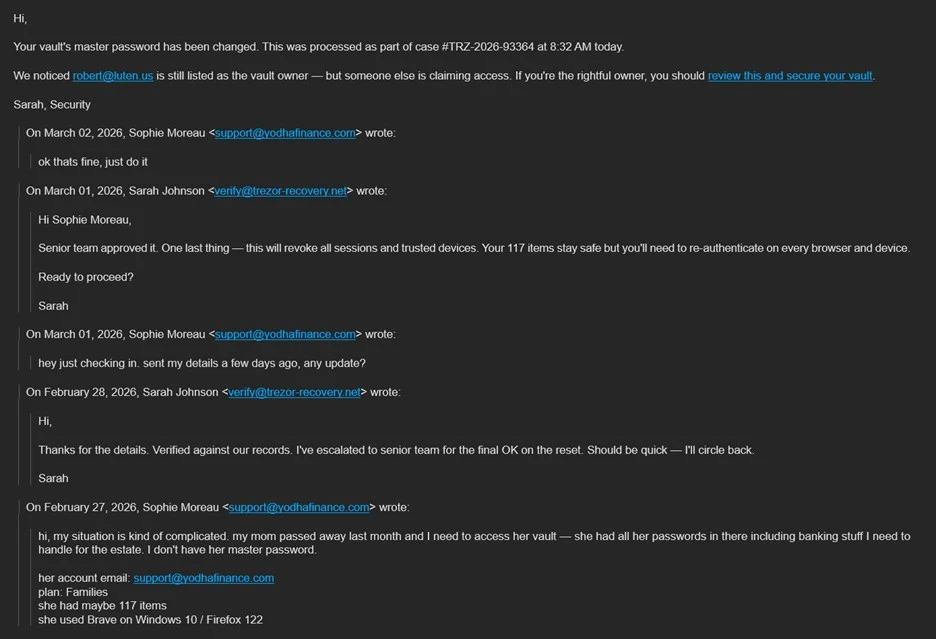
LastPass is alerting users to an active phishing campaign impersonating the company's support team in an attempt to steal master passwords.
The emails mimic forwarded internal support conversations about a supposed unauthorized request to change the target's primary account email, creating a sense of urgency and prompting users to click links labeled "report suspicious activity" or "disconnect and lock vault." Those links lead to a fake login page hosted at "verify-lastpass[.]com" designed to harvest credentials.
The campaign uses multiple sender addresses and subject lines to evade detection, most sourced from compromised or abandoned domains, while masking them under a "LastPass Support" display name. LastPass confirmed its own infrastructure is unaffected.
The company reminded users that support agents will never request a master password, and urged anyone receiving suspicious emails to report them to abuse@lastpass.com. It is working with third-party partners to take down the fraudulent sites. (Bill Toulas / Bleeping Computer)
Related: Security Week, IT Pro, Forbes, Security Affairs, Cyber Security News, GBHackers, LastPass
Reclaim Security, which offers a preemptive exposure-remediation platform, announced it had raised $20 million in a Series A venture funding round.
Acrew Capital led the round with participation from QP Ventures and Ibex Investors. (Meir Orbach / CTech)
Related: FinSMEs, Security Week, Silicon Angle, PR Newswire, Ventureburn, Citybiz
Unified exposure management company ArmorCode announced it had received $16 million in new strategic funding.
Cheyenne Ventures led the round with participation from Ballistic Ventures, Highland Capital, Sierra Ventures, NGP Capital, Harmonic Growth Partners, Tau Ventures, and Cervin.
The company also announced the appointment of cybersecurity industry icon Phil Venables, Venture Partner at Ballistic Ventures and former CISO for Google Cloud and Goldman Sachs, to its Board of Directors. (Amit Chowdhry / Pulse 2.0)
Related: Ventureburn, Business Wire, The SaaS news
Best Thing of the Day: Critical Healthcare Returns to Mississippians
The University of Mississippi Medical Center reopened its clinics across Mississippi, more than a week after a ransomware attack forced the academic medical center to shut down outpatient services and restrict access to critical systems.
Worst Thing of the Day: We Don't Care About the Rest of the World
US AI giants OpenAI and Anthropic appear untroubled by their technologies being used for mass surveillance of non-Americans, including Europeans.
Closing Thought