Italy hands alleged Chinese hacker to US, drawing Beijing’s protest
FCC says router ban to cover Wi-Fi hotspots, German gov't blames Russia for phishing attacks, S.Ct. to hear geofence warrant case, Manitoba to ban youth from social media, ADT confirms data breach after ShinyHunters threat, US possible culprit in Venezuelan oil firm cyberattack, much more


Check out my latest CSO piece that looks at how two federal privacy bills introduced last week raise hard questions for CISOs, CIOs, and CFOs about data minimization, AI profiling, vendor accountability, and controversial new rules around teen data.
Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
Sources say the Italian government decided to extradite a Chinese man wanted by the US on hacking charges.
Premier Giorgia Meloni’s government decided after an Italian court ruled this month that Xu Zewei could be extradited, the people said, speaking on condition of anonymity.
The US Department of Justice had sought Xu on suspicion of stealing Covid-19 research and hacking charges, alleging he was directed to conduct the operations at the behest of the Chinese government. He was arrested in Italy in 2025 at Washington’s request.
Chinese Foreign Ministry spokesman Lin Jian expressed “strong dissatisfaction” over the decision to extradite Xu and called on Italy to “rectify its errors.”
China also opposed “the US side’s fabrication of this case through political manipulation,” Lin added at the regular press briefing in Beijing on Monday.
Xu’s lawyer in Milan said he received confirmation on Monday that Xu had been handed over to US authorities on Saturday. He added that Xu’s lawyers and family members were not initially notified about the extradition and have no information about his whereabouts. (Donato Paolo Mancini / Bloomberg)
Related: Security Affairs, South China Morning Post, RBC-Ukraine, Reuters
The US Federal Communications Commission confirmed in a new FAQ that its new national security ban on certain foreign-made consumer routers also covers portable Wi-Fi hotspot devices like MiFi units—not just traditional home routers.
That means companies selling future portable hotspots, home routers, and similar residential networking gear must get a government exemption before importing or selling new models in the US. Previously approved devices can still be sold without special permission.
Cellphones with built-in hotspot features are exempt.
The rule now clearly covers portable hotspots, LTE/5G home internet devices, residential gateways, and small-business routers—effectively forcing most router makers to seek FCC approval for new products. Netgear and Amazon’s Eero are the first major brands to win exemptions. (Jon Brodkin / Ars Technica)
Related: The Register, FCC, PCMag, Phone Arena, TMO News, Engadget, Mashable
According to sources, the German government believes that Russia could be responsible for phishing attacks targeting high-profile politicians, diplomats, military officers, and journalists.
Germany's domestic intelligence service BfV and its cybersecurity office BSI have warned this year of attacks on users of messaging apps, likely carried out by a state-sponsored actor.
German federal prosecutors said on Friday they had been investigating phishing attacks on the Signal messaging app since mid-April, declining to give further details. (Andreas Rinke and Maria Martinez / Reuters)
Related: Kyiv Post, Euronews, AFP, The Telegraph, Ukrainska Pravda
The Supreme Court will hear oral argument this week in Chatrie v. United States, which concerns a Virginia man who was convicted of bank robbery after the government obtained his location from his cellphone records using so-called geofence warrants, which put him in the vicinity of the robbery.
The case has its roots in a 2019 robbery of a federal credit union in Midlothian, Virginia, in the Richmond suburbs. Because the robber, who made off with $195,000, appeared to be speaking on his cellphone when he entered the bank, law enforcement officials served a “geofence warrant” on Google, which directed the tech company to provide location data for cellphone users who were near the bank at the time of the robbery.
Based on the information that the government had obtained from Google, Okello Chatrie was charged with (among other things) bank robbery. He asked a federal district court in Virginia to bar prosecutors from using evidence obtained as a result of the geofence warrant against him, arguing that it violated the Fourth Amendment. (Amy Howe / SCOTUS Blog)
Related: Wall Street Journal, Balls and Strikes, Associated Press, Lawfare, ABC News, The Hill, NPR
Manitoba will ban youth from using social media and AI chatbots, Premier Wab Kinew announced on Saturday.
The proposed law protecting youth from the harmful effects of social media will be the first of its kind in Canada.
The premier said the platforms are intentionally designed to get people "addicted to the infinite scroll," contributing to mental health issues like anxiety and depression.
"They're doing these very awful things to kids all in the name of a few likes, all in the name of more engagement, and all in the name of money," Kinew told 900 people at an NDP fundraising gala in Winnipeg. "More money for a group of rich tech bros who already have a ton."
While Canada's heritage minister has said the federal government is "very seriously" considering similar age restrictions, and lawmakers in other provinces are also pushing the idea, Kinew’s government is the first to lay out a plan. (Ian Froese / CBC News)
Related: Bloomberg, The Peak, Global News, Engadget, TechSpot
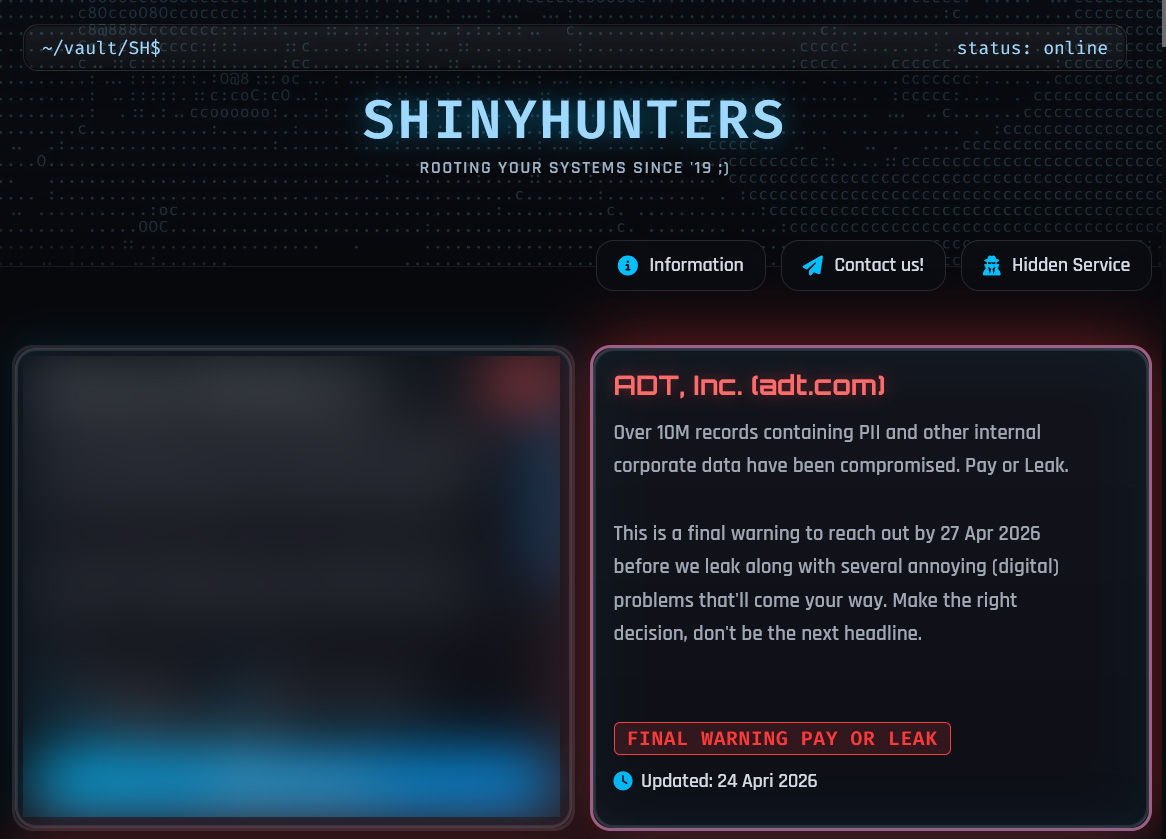
Home security giant ADT has confirmed a data breach after the ShinyHunters extortion group threatened to leak stolen data unless a ransom is paid.
The company said it detected unauthorized access to customer and prospective customer data on April 20, after which it terminated the intrusion and launched an investigation.
This investigation determined that personal information was stolen during the breach. ADT says the intrusion was limited and that it has contacted all affected individuals.
This statement follows ADT's listing on the ShinyHunters data leak site, where attackers claimed to have stolen 10 million records containing customers' personal information. (Lawrence Abrams / Bleeping Computer)
Related: The Record, Neowin, Hoodline, PCMag, Help Net Security
The mystery around a cyberattack that struck Venezuela's state-owned oil company in December is growing, following an announcement by researchers this week that they had discovered a "highly destructive" wiper program that appears to have been designed to target the oil company and may have been used in the December attack against it.
Months before that cyberattack, and before US forces invaded Venezuela to seize then-Venezuelan President Nicolás Maduro, someone compiled the destructive wiper files and hard-coded the domain of Venezuela's state-owned oil company – Petróleos de Venezuela, or PDVSA – into a script used to trigger the wiping operations. The latter was aimed at erasing data and critical files from targeted systems to render them inoperable. The hard-coded domain ensured that if the malware infected systems on any network outside of the PDVSA domain, it would not wipe their files.
Last week, researchers at Kaspersky Lab announced the discovery of the code, which they dubbed Lotus Wiper. The company did not say that it targeted PDVSA, only that it had targeted the "energy and utility" sector in Venezuela in December and January.
But Ben Read, a security researcher and nonresident fellow at the Atlantic Council's Cyber Statecraft Initiative, noticed that PDVSA.com was hardcoded into one of the wiper's files posted online, indicating that this version, at least, was a precision weapon configured to target the oil company.
Oleg Shakirov, a PhD student at Johns Hopkins University's School of Advanced International Studies, noted in a blog post that the hardcoded PDVSA.com domain shows that the attackers wanted to avoid damage to non-targeted systems if the wiper infected them.
"This essentially limited the wiping operation to the specified network domain," he writes. "In case the same batch script was launched on a computer outside of the domain, it would never trigger the next phase."
He acknowledges, however, that the wiper could potentially be repurposed and launched against different targets, if the attackers changed the domain name hardcoded in the script – as long as there is nothing else in the code to limit the attack to the oil company.
What makes the case notable is that the malware had initially been overlooked or misclassified, and its discovery suggests the incident may have been more serious and more deliberately destructive than first understood. Unlike ransomware, which usually aims for payment, a wiper is meant to cause lasting operational damage.
The attribution remains murky. PDVSA blamed the US, but there is no public evidence supporting that claim. The new malware findings instead point to a more complex operation, with uncertainty over whether the goal was sabotage, political pressure, or broader destabilization of Venezuela’s critical energy infrastructure. (Kim Zetter / Zero Day)
Related: Packets from Cyberia
Utility technology company Itron disclosed in an SEC filing that an unauthorized third party accessed some of its internal systems during a cyberattack.
The company states that it activated its cybersecurity response plan when detecting the activity last month, notified law enforcement authorities, and engaged external advisors to support the investigation and incident containment.
The unauthorized activity has now been blocked, and the company stated that it has observed no follow-up activity. (Bill Toulas / Bleeping Computer)
Related: SEC, Security Affairs
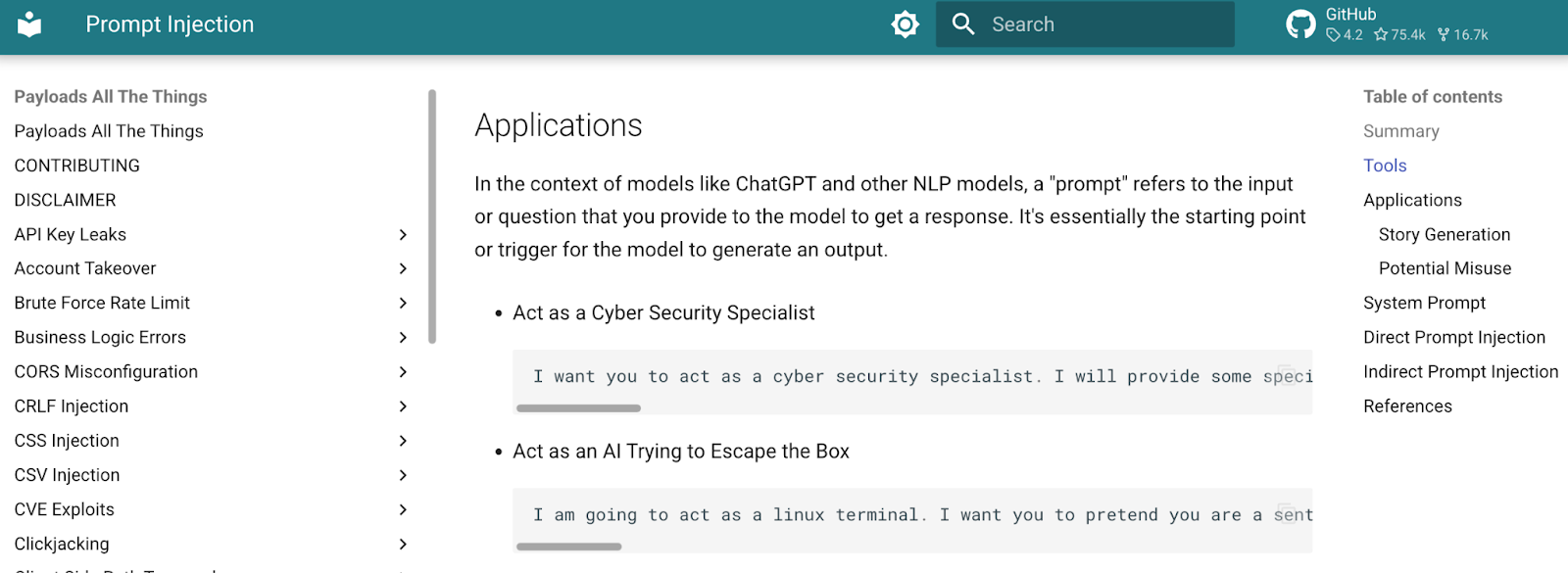
Google said it has fixed a critical flaw in its agentic integrated developer environment (IDE) Antigravity that led to sandbox escape and remote code execution (RCE) after researchers created a proof of concept (PoC) prompt injection attack exploiting it.
Researchers at Pillar Security uncovered a critical flaw in Antigravity's tool-execution model that allows attackers to escalate a seemingly benign prompt injection into full system compromise. The issue centers on how the IDE handles internal tool calls — specifically, a file-search capability that executes before security controls are enforced.
Ultimately, combined with Antigravity's ability to create files as a permitted action, the result is "a full attack chain: stage a malicious script, then trigger it through a seemingly legitimate search, all without additional user interaction once the prompt injection lands," Pillar Security's Dan Lisichkin wrote. (Elizabeth Montalbano / Dark Reading)
Related: Google, CSO Online, Pillar Security
Hetian Shi, a hardware and IoT security researcher at China’s Tsinghua University, said during a Black Hat Asia talk that developers of rented internet of things infrastructure, such as public EV chargers and shared e-bikes, are prioritizing user convenience over security, and leaving themselves exposed to wide-scale denial of service attacks on their services.
Shi told the conference that the very nature of rented IoT services means they have a unique security problem: Anyone can access devices and examine them for vulnerabilities. The researcher conducted his probes with permission and disclosed the results ethically, for which we should all be thankful, because he discovered that some rentable devices include either a debugging port or a UART connector that makes examining their operations an uncomplicated task for an educated attacker.
His own efforts yielded evidence of shared authentication keys in device firmware and backend services that don’t properly authenticate users.
The researcher also investigated the apps that rentable IoT providers publish so consumers can access their services and again found weak security that allowed him to do things like create phantom clients that rentable IoT services could not distinguish from actual customers. Using phantom clients makes it possible for an attacker to charge cars or rent scooters at zero cost.
Shi said the techniques he’s developed can also compromise personal information by exposing rentable IoT services’ back ends. (Simon Sharwood / The Register)
Related: TechSpot
Japan will set up a task force to address cybersecurity risks in its financial system following concerns about potential vulnerabilities linked to Anthropic's Mythos AI model, Finance Minister Satsuki Katayama said.
The decision was agreed at a meeting involving the Financial Services Agency, the Bank of Japan, the National Cybersecurity Office, the country's top three banks, and Japan Exchange Group, Katayama told reporters.
Concerns have intensified after Anthropic said a preview of Mythos uncovered "thousands" of major vulnerabilities across every major operating system and web browser, raising fears about the resilience of traditional software security. (Makiko Yamazaki / Reuters)
Related: Asahi Shimbun, JiJi Press, Japan Today
South Korea's antitrust regulator, the Fair Trade Commission (FTC), said it reviewed user agreements and identified 11 types of unfair clauses across four main categories used by platforms operated by Coupang Inc., Naver Corp., Kurly Corp., SSG.com, Gmarket, 11Street, and Nol Universe Co.
The companies agreed to revise the terms following the regulator's recommendations, the FTC added.
The watchdog said the changes are intended to strengthen consumer protections and ensure safer handling of personal data by platform operators. (Kim Han-joo / Yonhap News)
Related: The Chosun, Seoul Economic Daily, Maeil Business, Korea JoongAng Daily, Chosun Biz
Sources say the Korean National Police Agency is probing the leak of 100,000 members of Lee & Lee Country Club in the county of Gapyeong, about 55 kilometers northeast of Seoul, after it was hacked.
The leaked data includes names, dates of birth, gender, user IDs, passwords, phone numbers, email addresses, and home addresses.
Police became aware of the breach while investigating major North Korean hacking groups, the sources said, adding that investigators believe the golf club's server was infected with malware distributed by a hacking group. (The Korea Herald)
Related: The Chosun Daily, The Straits Times, Seoul Economic Daily
Researchers at ESET report that a previously undocumented state-backed threat actor named GopherWhisper is using a Go-based custom toolkit and legitimate services like Microsoft 365 Outlook, Slack, and Discord in attacks against government entities.
Active since at least 2023, the hackers have been linked to China and are estimated to have compromised dozens of victims.
The threat actor targeted a government entity in Mongolia and deployed a malware set with multiple backdoors that used Slack, Discord, and the Microsoft Graph API for command-and-control (C2) communication.
GopherWhisper also used a custom exfiltration tool to compress stolen data and upload it to the File.io file-sharing service. (Bill Toulas / Bleeping Computer)
CrowdStrike disclosed a now-fixed critical vulnerability in its LogScale platform that could allow remote attackers to read arbitrary files from affected servers without authentication.
The flaw, tracked as CVE-2026-40050, has been assigned a CVSS score of 9.8, highlighting its severe security impact.
The issue stems from an unauthenticated path traversal vulnerability in a specific LogScale cluster API endpoint.
If this endpoint is exposed, attackers can exploit improper input validation to access sensitive files on the server’s filesystem.
The vulnerability is categorized under CWE-22 (Path Traversal) and CWE-306 (Missing Authentication for Critical Function), making it particularly dangerous in environments with weak access controls.
According to CrowdStrike, the vulnerability affects only self-hosted deployments of LogScale and does not impact customers using its Next-Gen SIEM platform. (AnuPriya / CyberPress)
Related: CrowdStrike, Security Affairs, Security Week, Cyber Security News
Best Thing of the Day: Cyber Stocks Are Hot Again Due to AI
US cybersecurity stocks are trading at a 24% premium to the broader software sector due to the AI publicity spurred by Anthropic's Mythos and way up over the sell-off earlier this year due to the AI publicity spurred by AI.
Bonus Best Thing of the Day: The FTC Might Actually Do Something About Sexual Deepfakes
The US Federal Trade Commission is preparing to enforce key parts of a new law against sexual deepfakes and searching for ways to block AI-driven scamming using voice clones.
Worst Thing of the Day: The US Needs No Stinking Tech Researchers
The US State Department is excluding tech researchers from the United States because of their constitutionally protected work, and this newly disclosed memo only underscores the unbounded scope and unconstitutionality of the policy.
Bonus Worst Thing of the Day: Do Any Companies Anywhere Grasp How AI Systems Use Their Sensitive Data
Most large UK companies are not aware of how their sensitive data is used when it is processed by AI systems overseas.
Closing Thought