OpenAI, Pentagon revise AI deal's surveillance limits, but commitments may be hollow
Israel spent years hacking Tehran's traffic cameras and phone networks, Iranian hacking groups' efforts have been negligible and opportunistic, Internet collapse in Iran has cut off hackers, Gulf ships bombarded with GPS attacks, Starlink has sustained Iran's Handala hackers, much more


Metacurity is the daily intelligence layer for people who must stay current on the critical happenings in the cybersecurity realm.
We scan thousands of sources on the web to decode the narrative, surface overlooked signals, and connect the dots others miss.
Every day, Metacurity delivers independent, analytical, and daily intelligence that sits outside the cybersecurity echo chamber and reputation economy of other newsletters. Along with the headline-grabbing news items, Metacurity delivers news of developments you won't see in other cybersecurity newsletters.
Please consider supporting Metacurity's continued existence by upgrading your subscription. Thank you.
OpenAI and the Pentagon have agreed to amend their recently signed contract to more explicitly prohibit domestic mass surveillance of Americans, following widespread backlash that the original language left a significant loophole.
The deal came together after negotiations between the Pentagon and Anthropic collapsed over whether the military could use AI to conduct mass surveillance of American citizens and operate fully autonomous weapons, conditions Anthropic refused to drop.
Within hours of Donald Trump directing federal agencies to stop using Anthropic's technology, and hours before the US carried out strikes on Iran, OpenAI announced it had reached its own agreement with the Defense Department, a sequence that drew immediate accusations of opportunism.
The revised contract language now bars use of the AI system for "deliberate tracking, surveillance, or monitoring of US persons or nationals, including through the procurement or use of commercially acquired personal or identifiable information," closing a significant gap in the original agreement, which named only "private information" and left geolocation data, browsing history, and personal financial records purchased from data brokers potentially available for government use.
OpenAI CEO Sam Altman, who personally approached Pentagon undersecretary Emil Michael to rework the deal, also said the Defense Department confirmed its services would not extend to intelligence agencies like the NSA without a separate contract modification — an important guardrail given the increasingly blurry line between military and intelligence activities. Critics, however, questioned whether even the strengthened language would hold under pressure, noting that broad references to "lawful use" and existing surveillance authorities leave room for interpretation.
Altman acknowledged the original Friday announcement was poorly handled. In an internal post he later shared publicly on X, he wrote that the timing "looked opportunistic and sloppy" and that the issues "are super complex, and demand clear communication." In the same post, Altman outlined the principles he said guided the decision — "alignment, democratization, empowerment, and individual agency" — insisting that "OpenAI should not decide the fate of the world; no private company should."
He also sounded an urgent note about the stakes involved, writing that "there are real dangers coming to the world, and maybe pretty soon," and that he had considered how he would feel "the day after an attack on the US or a new bioweapon we could have helped prevent."
Meanwhile, as of Monday night, the Pentagon had not yet formally issued the "supply chain risk" designation against Anthropic that Defense Secretary Pete Hegseth had threatened, with Altman continuing to push for the same amended contract terms to be offered to his rival.
Experts suggest that the specific actions Hegseth and Trump took in labeling Anthropic a supply chain risk have serious legal problems. The designation exceeds what the statute authorizes. The required findings don't hold up. And Hegseth's own public statements may have doomed the government's litigation posture before it even begins.
Hundreds of tech workers — including signatories from OpenAI, Slack, IBM, Cursor, and Salesforce Ventures — signed an open letter urging the DOD to withdraw its designation of Anthropic as a "supply chain risk" and calling on Congress to examine whether the use of such authorities against an American company is appropriate.
Some reports suggest the dispute comes down to a “breakdown in trust between Anthropic and the Pentagon, where Anthropic doesn’t trust that the Pentagon knows enough to use their technology responsibly and the Pentagon doesn’t trust that Anthropic will be willing to work on important use cases that it needs,” Michael Horowitz, a former Defense Department official who worked on AI policy. That lack of trust is caused by, or at least exacerbated by, the contrasting personalities and worldviews of Anthropic CEO Dario Amodei and Defense Secretary Pete Hegseth.
Amodei, who over a year earlier had assured anxious employees that the company’s contract with the US military was mostly about paperwork, has more recently framed the clash with the Pentagon as one with grave implications for the future of modern warfare and even society at large.
Lawmakers are also joining the fray, with Sen. Ron Wyden of Oregon, the top Democrat on the Senate Finance Committee, vowing to “pull out all the stops” to fight back after Donald Trump barred Anthropic from all government business, and said he plans to seek bipartisan backing for legislation to address the issue.
Amid the fray, market intelligence provider Sensor Tower said that US app uninstalls of ChatGPT’s mobile app jumped 295% day-over-day on Saturday, February 28.
Finally, three more US cabinet-level agencies, the departments of State, Treasury, and Health and Human Services, moved to cease use of Anthropic's AI products on Monday, joining the Pentagon in switching to rivals such as OpenAI under a new White House directive. (Cade Metz and Julian E. Barnes / New York Times, Sam Altman on X, Maria Curi / Axios, Dylan Butts / CNBC, Katherine Li / Business Insider, Steven T. Dennis / Bloomberg, Amrith Ramkumar, Keach Hagey, and
Marcus Weisgerber / Wall Street Journal, Raphael Satter and Courtney Rozen / Reuters, Michael Endrias, Alan Z. Rozenshtein / Lawfare, Sarah Perez / TechCrunch and Rebecca Ballen / TechCrunch)
Related: Financial Times, Engadget, MarketWatch, Australian Financial Review, The Decoder, Digit, The Information, The Economic Times, Techdirt, Gizmodo, Platformer, Implicator.ai, TechCrunch, TheStreet, Axios, Business Standard, Implicator.ai, Reuters, Wall Street Journal, Reuters, Wall Street Journal
Most but not all cybersecurity experts believe that Iran is not a potent cyber force, with its actions mostly limited to defacements and DDoS attacks. However, numerous press reports suggest that cyber was used to engage in surveillance against the Iranian regime for years, and phones and traffic cameras were remotely tampered with to ensure the US operation was a success. On top of that, GPS interference spiked ahead of and during the operation.
The following are some of the most relevant reports related to cyber and adjacent malicious activity that came into play surrounding the initial US assault.
- Israel spent years hacking nearly all of Tehran's traffic cameras and penetrating mobile phone networks to build pattern-of-life profiles on Khamenei's security detail, while disabling mobile towers near his compound on the morning of the strike to block warnings. An Israeli intelligence official told the FT that before the strike, Israeli forces "knew Tehran like we know Jerusalem." (Mehul Srivastava, James Shotter, and Neri Zilber / Financial Times)
- Iran's feared hacking groups have played a negligible role in the conflict, with active pro-Iranian groups collapsing from 130+ to just 17 since the 2025 war, per Recorded Future. The internet blackout is the primary cause, though one researcher argued Iran's cyber capabilities were always overhyped. US Cyber Command was a first mover in disrupting Iranian communications, a prayer app was hijacked to urge the IRGC to surrender, and the pro-Israeli group Predatory Sparrow's trademarks are visible in current operations even though the group hasn't been formally attributed to the new war. (Patrick Howell O'Neill / Bloomberg)
- CrowdStrike had not observed large-scale state-sponsored cyber campaigns, but noted a surge in claimed activity from Iran-aligned hacktivist groups, including DDoS, defacements, and alleged interference across the Middle East, US, and parts of Asia, with threat cluster HYDRO KITTEN specifically signaling financial sector targets. (David DiMolfetta / NextGov/FCW,)
- Iran-backed hackers are signaling an expansion beyond regional targets toward global economic disruption, though activity remains largely opportunistic and concentrated on targets like Jordan for now, per Flashpoint. Experts quoted throughout — including former White House cyber official Neal Higgins, ex-CISA official Matt Hartman, and ex-FBI cyber deputy Cynthia Kaiser — warned that Iran will likely rely on proxy groups and offshore hosting infrastructure to compensate for its domestic internet blackout, and that critical infrastructure sectors, including energy, water, and financial services, should assume they could become targets of convenience. (Angus Loten and James Rundle / Wall Street Journal)
- Talos reported no significant cyber impacts as of publication, observing only small-scale defacements and DDoS attacks, and assessed the conflict as having a "large focus on kinetic activity" for now. The post's practical value is largely in its defensive guidance: MFA, third-party supplier risk mapping, and warnings that cybercriminals will exploit the conflict as cover for phishing and malware campaigns using conflict-themed lures. (Cisco Talos)
- Iran's connectivity collapsed to 1–4% of normal from Feb. 28, effectively cutting off state-sponsored hacking units. Unit 42 assessed sophisticated attacks are unlikely in the near term but warned that isolated units may deviate from established patterns and that dispersed operators outside Iran could develop tactical autonomy, making their actions harder to predict and attribute. (Palo Alto Networks Unit 42)
- More than 1,100 ships across the Gulf have had GPS or AIS systems disrupted since Feb. 28, with vessels falsely placed at airports, a nuclear power plant, and on Iranian land, per maritime intelligence firm Windward. The Joint Maritime Information Center issued a "critical" warning on March 1, shipping through the Strait of Hormuz has nearly halted, and at least three tankers have been damaged in the conflict. (Matt Burgess / Wired)
- Iranian hacker group Handala, linked to MOIS and described by Check Point as the regime's most notorious hacking crew, has been sustaining operations through Starlink despite the nationwide internet blackout, exploiting the same black-market terminal infrastructure the Trump administration helped build to support Iranian protesters. A second MOIS-linked group, Fatimiyoun Electronic Team, attempted to deploy wiper malware against Israeli computers following the strikes. (Thomas Brewster / Forbes)
- Google GTIG chief analyst John Hultquist warned that Iran will "absolutely" retaliate with cyber operations against a much wider target set than Israel, including Gulf states hosting US bases that lack Israel's mature defenses. He specifically cautioned that some attacks will be disguised as hacktivism or ransomware but will be IRGC-directed operations. (Danny Palmer / Infosecurity Magazine)
- Misrepresented images related to the war were spreading rapidly online, including years-old footage presented as current, false claims of destroyed US military vehicles, and fabricated casualty imagery. The most viral false claim — an image purporting to show Khamenei's body under rubble — was determined to be AI-generated, with Google's Gemini app detecting SynthID watermarking confirming it was created or edited by Google's AI models. The piece serves as an early signal that the information environment around this conflict is already heavily polluted with AI-generated and recycled content, a pattern consistent with what researchers have observed in previous Middle East conflicts. (Melissa Golden / Associated Press)
A group of hacktivists calling themselves “Department of Peace” claimed to have hacked the Department of Homeland Security (DHS), leaking allegedly stolen documents online.
On Sunday, the nonprofit transparency collective DDoSecrets published data relating to contracts between DHS, Immigration and Customs Enforcement (ICE), and more than 6,000 companies, including defense contractors Anduril, L3Harris, Raytheon, and surveillance provider Palantir, as well as tech giants Microsoft and Oracle.
The hacktivist said the data comes from the Office of Industry Partnership, a unit within DHS that procures technology from the private sector.
Department of Peace explained their motives in a document alongside the hack, citing the recent killings of two peaceful protesters, US citizens Alex Pretti and Renée Good, earlier this year in Minneapolis by federal agents.
“Why hack the DHS? I can think of a couple Pretti Good reasons! I’m releasing this because the DHS is killing us, and people deserve to know which companies support them and what they’re working on,” the hackers wrote. (Lorenzo Franceschi-Bicchierai / TechCrunch)
Related: DDoSecrets, Data.ddosecrets, Cyber Daily, TechRadar, DHS Contracts Explorer
British games studio Cloud Imperium Games (CIG), maker of the crowdfunded multiplayer title Star Citizen, has admitted to a data breach that occurred on January 21st, in which attackers gained unauthorized read-only access to backup systems containing users' personal data — including names, contact details, usernames, and dates of birth.
The company says no passwords, financial information, or payment data were compromised, and that no data was modified or injected. CIG quietly disclosed the incident weeks later via a low-key popup "Service Alert" on its website, rather than through direct emails or prominent front-page notices.
The handling of the disclosure has infuriated the game's community, with users criticizing both the delay of roughly six weeks and the dismissive framing of the announcement. (Simon Sharwood / The Register)
Related: Roberts Space Industries, Bleeping Computer
According to researchers at Arctic Wolf Labs, SloppyLemming, also known as Outrider Tiger and Fishing Elephant, ran an extensive cyber espionage campaign from January 2025 through January 2026, targeting government bodies and critical infrastructure operators in Pakistan and Bangladesh.
The group is assessed with moderate confidence to be India-aligned, and its targeting of Pakistani nuclear regulators, defense logistics, and telecom infrastructure, alongside Bangladeshi energy utilities and financial institutions, points to intelligence collection tied to regional strategic competition in South Asia. (Anna Ribeiro / Industrial Cyber)
Related: Arctic Wolf Labs
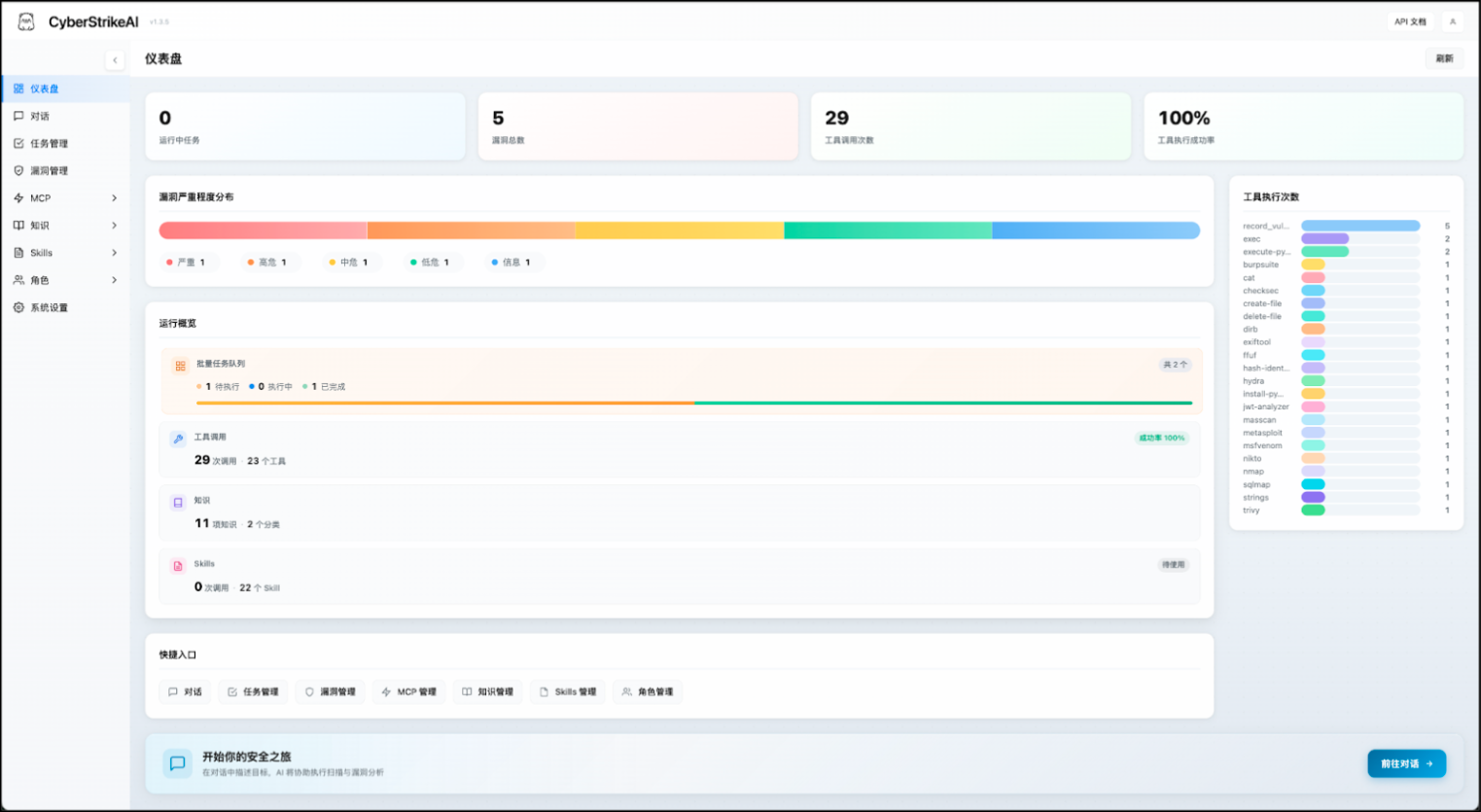
Researchers at Team Cymru have linked a newly discovered open-source platform called CyberStrikeAI to a threat actor who recently compromised over 500 Fortinet FortiGate firewalls in a five-week campaign.
By analyzing network traffic data, they traced a specific IP address used in the FortiGate attacks to a server actively running CyberStrikeAI, with that infrastructure last seen active on January 30, 2026. The platform, built in Go, integrates more than 100 security tools, including network scanners, exploitation frameworks, and password crackers, all orchestrated by an AI decision engine compatible with models like GPT, Claude, and DeepSeek.
What makes CyberStrikeAI particularly concerning is that it automates the entire attack chain, from initial reconnaissance to post-exploitation, allowing even low-skilled operators to carry out sophisticated attacks. Between late January and late February 2026, Team Cymru spotted 21 unique IP addresses running the tool, with servers concentrated in China, Singapore, and Hong Kong, plus additional infrastructure in the US, Japan, and Europe. Researchers warn that this kind of AI-native orchestration engine could accelerate automated targeting of exposed edge devices like firewalls and VPN appliances.
The platform's developer, known online as "Ed1s0nZ," has also built related tools, including PrivHunterAI and InfiltrateX, both focused on privilege escalation. Their GitHub activity shows connections to organizations linked to Chinese government cyber operations, including sharing CyberStrikeAI with Knownsec 404 — a Chinese cybersecurity firm with alleged government ties — and previously referencing an award from China's National Vulnerability Database (CNNVD), which is believed to be operated by Chinese intelligence. Researchers caution that tools like this are rapidly lowering the barrier to complex network exploitation. Sonnet 4.6 (Lawrence Abrams / Bleeping Computer)
Related: Team Cymru, Cyber Press, GBHackers, Cyber Security News
Google's March 2026 Android security update patches 129 vulnerabilities, including an actively exploited zero-day (CVE-2026-21385) in a Qualcomm display component.
The flaw is an integer overflow in Qualcomm's Graphics subcomponent that allows local attackers to trigger memory corruption, and it affects 235 Qualcomm chipsets. Google has acknowledged "limited, targeted exploitation" but hasn't shared details on who is being targeted or by whom.
Beyond the zero-day, the update addresses 10 critical flaws across the System, Framework, and Kernel components. The most severe of these requires no user interaction and could allow a remote attacker to execute arbitrary code without needing any special privileges, a particularly dangerous scenario.
Google issued two patch levels (March 1 and March 5), with the latter covering additional third-party and kernel fixes that may not apply to all devices. Pixel phones get updates immediately, while other Android devices typically take longer as manufacturers adapt the patches for their specific hardware. (Sergiu Gatlan / Bleeping Computer)
Related: Qualcomm, Android, Cyber Press, CyberScoop, Beta News, Cyber Security News
In a post on X, Microsoft Threat Intelligence warned of a campaign distributing fake gaming tools, specifically trojanized versions of Xeno.exe and RobloxPlayerBeta.exe through browsers and chat platforms.
When victims run these files, a remote access trojan (RAT) is silently installed. The initial file acts as a downloader that installs a portable Java runtime and launches a malicious Java archive to continue the infection. hackread
Rather than using obvious malware components, the attackers abuse built-in Windows tools, known as living-off-the-land binaries (LOLBins), such as PowerShell and cmstp.exe, making the malicious activity blend in with normal system processes. A PowerShell script then reaches out to remote domains, including a PythonAnywhere-hosted endpoint, to download and execute a file called update.exe.
Once installed, the malware adds itself to Microsoft Defender's exclusion list to avoid detection. It establishes persistence through scheduled tasks and a startup script called world.vbs, ensuring it survives reboots. The final payload gives attackers broad, long-term control — functioning as a loader, downloader, and remote access tool. Microsoft Defender can already detect this campaign, but Microsoft advises users and organizations to be cautious about downloading gaming utilities from unofficial sources like chat groups or forums. hackread Sonnet 4.6. (Waqas / HackRead)
Related: Microsoft on X, SC Media, Heise Online, Security Affairs, Cyber Press
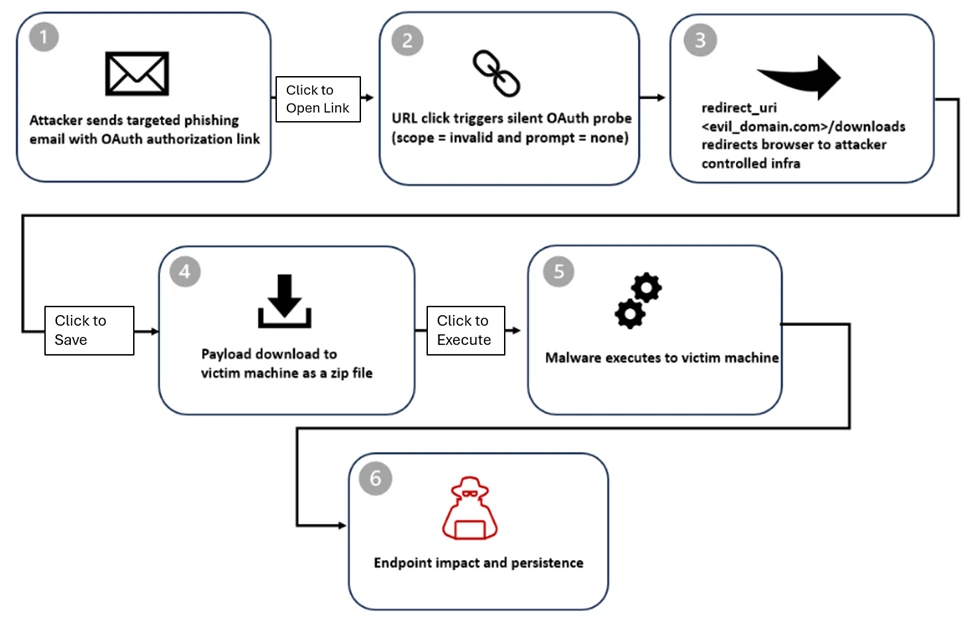
Microsoft warned organizations about ongoing OAuth abuse scams targeting government and public-sector organizations, using phishing emails and URL redirects to deliver malware.
OAuth has a legitimate feature that redirects users to a landing page when certain errors are triggered, and criminals exploit this by crafting URLs through Microsoft Entra ID or Google Workspace that send victims to attacker-controlled pages where malware is silently downloaded.
The attacks begin with phishing emails disguised as e-signature requests, Teams meeting recordings, Microsoft 365 password reset notices, or political content, with the malicious link sometimes embedded in the email body and sometimes hidden inside a PDF attachment.
Notably, the attackers aren't after OAuth access tokens. Instead, they deliberately trigger a sign-in error so the redirect mechanism delivers malicious payloads to the victim's machine.
In one documented campaign, victims were redirected to a download path that dropped a ZIP file containing LNK shortcut files. Opening the shortcut executed a PowerShell reconnaissance command, then launched a legitimate-looking file (steam_monitor.exe) to side-load a malicious DLL, which ultimately connected the infected machine to an attacker-controlled server.
Microsoft Entra has disabled the malicious OAuth apps involved, but warns that related activity is ongoing and requires continued monitoring. (Jessica Lyons / The Register)
Researchers at Moonlock Lab say that crypto criminals are impersonating venture capital firms on LinkedIn, using polished fake websites and AI-generated staff photos to lure targets into a supposed video call.
Once on the fraudulent call page, victims are shown a fake Cloudflare verification checkbox that silently copies a malicious command to their clipboard, then tricks them into pasting and running it in their own terminal, ForkLog, bypassing traditional security tools entirely since the victim executes the attack themselves.
A compromised Chrome extension called QuickLens was also used to spread the same technique, with new owners pushing a malicious update just two weeks after acquiring it. (Diya Poddar / Invezz)
Related: Moonlock Lab, Bitget

Researchers at IMDEA Networks Institute have discovered that tire pressure monitoring systems (TPMS), mandatory in most modern cars since the late 2000s, can be exploited to track drivers' movements.
The core problem is that these sensors broadcast a unique, unencrypted ID number via wireless signals, meaning anyone with a basic radio receiver nearby can capture and recognize the same vehicle repeatedly — without ever reading a license plate.
This is potentially more concerning than camera-based surveillance because the radio signals pass through walls and vehicles, allowing hidden receivers to pick them up without line-of-sight. The necessary equipment costs as little as $100 per receiver.
To demonstrate the risk, the team built a network of low-cost receivers near roads and parking areas, collecting over six million tire sensor messages from more than 20,000 cars over ten weeks. eurekalert They were able to identify movement patterns, daily routines, and work schedules, and could capture signals from moving vehicles at distances greater than 50 meters.
Current vehicle cybersecurity regulations don't specifically address TPMS security, and the researchers are urging manufacturers and policymakers to add encryption and authentication to future systems so that safety features don't become surveillance tools. (IMDEA Networks Institute)
Related: Supercarbblondie, Security Week, Road and Track, CNET, Bro Bible, The Autopian, Hackster.io
HP Wolf Security reports that cyber criminals are increasingly assembling malware from modular, off-the-shelf components purchased on crime forums in what they call "flat-pack" malware.
Rather than building attacks from scratch, hackers reuse the same intermediate scripts and installers across campaigns, swapping out only the lures and final payloads. Multiple unrelated groups have been observed using identical building blocks, making it easy to scale attacks rapidly and cheaply.
AI is accelerating this trend significantly. Threat actors are using it to automate malware delivery, generate convincing fake documents, and even reverse-engineer existing malware strains from publicly available security research — a technique Trend Micro calls "vibe coding." Google has also flagged abuse of its Gemini models for malware creation, underscoring how broadly AI has been adopted across the cyber criminal ecosystem.
Despite the basic nature of these campaigns, researchers stress they remain effective. HP found that 14% of email threats bypassed at least one email gateway scanner. The key takeaway from HP's principal threat researcher is that attackers aren't using AI to get smarter; they're using it to get faster and cheaper, and that combination is proving dangerous enough. (Ross Kelly / IT Pro)
Researchers at Cydome warn that the maritime industry's rapid adoption of AI is leaving it increasingly vulnerable to autonomous cyberattacks.
Notably, up to 60% of newly discovered software vulnerabilities on ships and onshore are being weaponized within 48 hours, a dramatic acceleration from 2018 when the average time from disclosure to attack was 63 days.
AI-driven tools have compressed that window even further, with some systems being targeted within 15 minutes of a flaw being identified.
AI is also transforming social engineering attacks, with 83% of phishing emails now using AI to target multinational crews in their native languages, contributing to a massive surge in voice phishing where AI clones the speech patterns of executives to authorize fraudulent transactions. (Rob O'Dwyer / Smart Maritime Network)
Best Thing of the Day: Cyber Budgets Are Going Back Up
Even if CISOs need to shift around where their investment dollars are going, recent research suggests CFOs approved larger cybersecurity budgets this year.
Worst Thing of the Day: 4chan v. Women Athletes
Users on 4chan and other sites quickly generated and shared “nudified” or sexualized imagery of multiple female US athletes, including figure skaters Alysa Liu, Amber Glenn, and Isabeau Levito, as well as skiers Mikaela Shiffrin and Eileen Gu (who competed for China).
Closing Thought