OpenAI gives advanced cyber models to European defenders
Anthropic denied Chinese think tank Mythos access, Pentagon will use Mythos while moving ahead with Anthropic ban, House panel wants Instructure hearing, Nitrogen group hit Foxconn with cyberattack, West Pharmaceutical Services hit with ransomware, Microsoft issues 120 Patch Tuesday fixes, much more
Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
My new book, The NIST 2.0 Cybersecurity Framework: Practical Risk Management Using Real-World Incidents, is now available for pre-order from Wiley (and wherever books are sold) at a 20% pre-release discount for a limited time.
US artificial intelligence giant OpenAI said it was granting access to its latest models, including GPT-5.5-Cyber , to Deutsche Telekom, BBVA, and dozens more European companies to help bolster their resilience to vulnerabilities in their systems.
Other companies added to the scheme included Spain's Telefonica, Britain's Sophos, and German financial services firm Scalable Capital, Open AI said.
OpenAI's "Trusted Access for Cyber" program gives verified companies in vital sectors such as financial services, telecoms, energy, and public services access to its models, including precise safeguards for defensive work.
OpenAI's MD for EMEA, Emmanuel Marill, said there was an important balance to be struck between access, usefulness, and safety as AI became more capable."We need to block dangerous activity, while making sure trusted defenders have tools that are genuinely useful in protecting systems, finding vulnerabilities, and responding to threats quickly," he said.
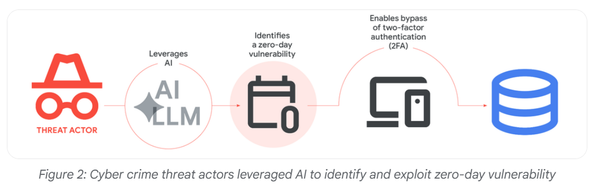
The release of Mythos by OpenAI's rival Anthropic last month significantly upped the risks posed to banks and other companies from new frontier AI models. (Paul Sandle / Reuters)
Related: Politico, CNBC, PYMNTS, IAPP, Quartz
Sources say a representative from a Chinese think tank approached officials from Anthropic at a meeting in Singapore last month to insist that the company change its stance and give Beijing access to its powerful new artificial intelligence model Mythos, but Anthropic refused.
The request was not an official demand from the Chinese government. But the talks in Singapore were a form of exchange that is often meant to pave the way for formal, direct diplomacy.
When officials from the National Security Council at the White House learned about the exchange at the meeting, which was convened by the Washington-based Carnegie Endowment for International Peace, they reacted with alarm. Some Trump administration officials saw it as another sign that Beijing would try every possible avenue to swiftly acquire the most powerful artificial intelligence model a US company has produced so far, according to people briefed on the discussions.
However subtle, the outreach is a sign of the intensifying competition between China and the United States over artificial intelligence, which a growing number of national security officials and analysts have begun to liken to the Cold War’s nuclear arms race. Chinese analysts see the release of the latest models from Anthropic and ChatGPT as a significant advance in American technology, one that could pose a threat to China. (Dustin Volz, Julian E. Barnes, Sheera Frenkel, and Tripp Mickle / New York Times)
Related: r/Anthropic, Sherwood News
Emil Michael, the Defense Department's chief technology officer and under secretary for research and engineering, said the Pentagon is deploying Anthropic's Mythos cybersecurity model to find and patch software vulnerabilities across the US government, even as it races to complete a transition away from the AI company.
Michael said the Pentagon continues to execute on its plan to remove Anthropic's products from its work in the coming months.
However, he said the Mythos issue "is a national security moment" where the government has hardened up networks, because that model has capabilities that are particular to finding cyber vulnerabilities and patching them.
Michael told attendees at a conference in Washington, DC, that while those vulnerabilities have always existed, artificial intelligence tools like Mythos mean they can now be found and patched faster — but also exploited faster.
He also said Anthropic's advantage is temporary, adding that models from OpenAI, xAI, and Google will come soon. (Mike Stone / Reuters)
Related: MeriTalk
The US House Committee on Homeland Security is calling on Instructure executives to testify about two cyberattacks by the ShinyHunters extortion group that targeted the company’s Canvas platform, allowing threat actors to steal student data and disrupt schools during final exams.
In a letter sent Monday afternoon to Instructure CEO Steve Daly, Homeland Security Committee Chairman Andrew R. Garbarino said the committee is investigating the massive breach at Instructure that impacts millions of students.
"The Committee on Homeland Security (Committee) is investigating the concerning reports related to recent cybersecurity incidents affecting Instructure Holdings, Inc. and the tens of millions of students, educators, and administrators who rely on its Canvas learning management platform," reads the letter.
On May 3, the ShinyHunters extortion gang claimed responsibility for the attack, telling BleepingComputer that they stole 280 million data records from 8,809 colleges, school districts, and online education platforms.
The ShinyHunters group conducted a second attack that defaced Canvas login portals at schools and universities across the United States, displaying extortion messages demanding that Instructure negotiate with the group. The disruption affected institutions across multiple states during final exams and end-of-semester activities, with some colleges forced to cancel exams. (Lawrence Abrams / Bleeping Computer)
Related: Committee on Homeland Security, Meritalk, Security Affairs
A ransomware group known as the Nitrogen group is attempting to extort the electronics manufacturing giant Foxconn, claiming that it stole 8 terabytes of data from the company, including schematics and project details from customers, including Dell, Google, Apple, and Nvidia.
Foxconn is a key manufacturing contractor for electronic components or entire devices, including Apple's iPhones.
The company acknowledged that some of its North American factories “suffered a cyberattack” in recent days, and that "affected factories are currently resuming normal production” after outages.
In addition to attempting to extort victims by threatening to release data stolen in an attack, Nitrogen also often deploys traditional ransomware that encrypts a target's systems. Researchers say that the group's ransomware program itself was built off of widely repurposed “Conti 2” code, but it has a problem.
Nitrogen's encryption mechanism has a design flaw that makes it impossible to decrypt data once it has been encrypted—even if the attackers want to release a victim's systems. (Lily Hay Newman / Wired)
Related: Silicon Republic, AppleInsider, The Record, Focus Taiwan, iClarified, DigiTimes, 9to5Mac, The Register, r/cybersecurity, r/pwnhub, Cybersecurity Insiders, Silicon Republic, Techzine, DigiTimes Asia, Economic Times, Bleeping Computer
West Pharmaceutical Services, a large Pennsylvania pharmaceutical company, said in an SEC filing that a ransomware attack has impacted critical systems used to ship, receive, and manufacture products.
A spokesperson said that West Pharmaceutical shut down and isolated the on-premise infrastructure that was affected, restricted access to enterprise systems, and notified law enforcement.
Palo Alto Networks’ incident response team, Unit 42, was hired to lead the investigation into the ransomware attack and to contain the incident.
West Pharmaceutical is still investigating what information was stolen during the initial breach and is still unsure of the financial impact of the attack. (Jonathan Greig / The Record)
Related: SEC, Dysruption Hub, Security Week
For its May Patch Tuesday updates, Microsoft issued fixes for 120 flaws, and no zero-days were disclosed.
This Patch Tuesday addresses 17 "Critical" vulnerabilities, 14 of which are remote code execution, 2 are elevation of privilege, and 1 is an information disclosure flaw.
The number of flaws does not include flaws in Mariner, Azure, Copilot, Microsoft Teams, and Microsoft Partner Center that were fixed by Microsoft earlier this month. 131 Microsoft Edge/Chromium flaws were fixed by Google this month, which were excluded. (Lawrence Abrams / Bleeping Computer)
Related: Security Brief, SC Media, Dark Reading, Redmond Magazine, Talos Intel, The Register - Security, Mobile Hacker, Microsoft Malware Protection Center, Qualys Blog, Talos Intel, CyberInsider, Cyberscoop, Krebs on Security, CSO Online, Security Week, Thurrott, Neowin, The Register, Zero Day Initiative, Infosecurity Magazine, Computer Weekly, Ask Woody, SANS Internet Storm Center, iTnews, Cyber Security News, Cyber Kendra
The UK's Information Commissioner's Office has fined South Staffordshire Water Plc and parent company South Staffordshire Plc £963,900 ($1.3 million) over a cyberattack that exposed the personal data of 663,887 customers and employees.
The company supplies 330 million liters of drinking water to 1.6 million consumers daily and, in 2022, disclosed that it was the target of a cyberattack that disrupted its IT operations.
At the time, the company dismissed claims from the Cl0p ransomware gang, which claimed the attack (after initially misidentifying their victim), but the leaked data samples appeared genuine.
The ICO’s investigation has now confirmed that the leaked data was indeed authentic, belonging to South Staffordshire Water Plc, and also noted that the compromise had actually started in September 2020.
“We have fined South Staffordshire Plc and South Staffordshire Water Plc (together South Staffordshire) £963,900 following a serious cyber attack that resulted in the personal information of 633,887 people being extracted and published on the dark web,” reads the ICO’s announcement. (Bill Toulas / Bleeping Computer)
Related: ICO, Industrial Cyber, Computer Weekly, Bitdefender, National Technology News
A Chinese national, who led a hacking scheme involving 131 Microsoft Edge/Chromium flaws, has been extradited to Korea from Thailand, the justice ministry said.
The 40-year-old arrived at Incheon International Airport on Tuesday from Bangkok to be handed over to police for investigation over allegations of stealing over 38 billion won ($25.4 million) from the victims, according to the ministry.
The police said they plan to seek a warrant for his formal arrest after questioning him and analyzing evidence.
The suspect is said to be part of a criminal ring accused of illegally collecting personal information of the victims from August 2023 to April 2025 by hacking into government and public agency websites, and using the data to withdraw cash from their accounts.
While Jungkook was targeted in the scheme, his agency, BigHit Music, took immediate action to prevent losses.
The criminal ring allegedly opened unauthorized brokerage accounts in Jungkook's name in January 2024 in an attempt to steal 8.4 billion won worth of his shares in Hybe, the company behind BTS, at the time. (Yohnap News)
Related: BBC News, The Chosun Daily, Korea JoongAng Daily, Zoom TV, Seoul Economic Daily, Manila Bulletin
Google announced several new and previously known Android security features that users can expect to roll out this year.
In light of the evolving threat landscape and the increasingly sophisticated tricks bad actors use to trap Android users, Google is making some welcome updates to existing Android features, including scam call protection, Live Threat Detection, Theft Protection, and others. Many of these features will roll out with Android 17. (Adamya Sharma / Android Authority)
Related: Google, SiliconANGLE, TechCrunch, AndroidGuys, Android Developers Blog, Android Central, Android Authority
Google launched a feature for Android phones for dedicated forensic logs about intrusions from sophisticated attacks like those by spyware vendors, in what design partners at Amnesty International hailed as an important first.
The tech giant has been ramping up the new feature, Intrusion Logging, since last year, and has now begun rolling it out.
“The new intrusion logging feature promises to be a major aid to digital forensics researchers undertaking investigations into sophisticated attacks on Android devices,” Amnesty International said. “This is the first time a major device vendor has released a feature specifically to enhance the ability to forensically detect and respond to advanced digital threats.”
To date, independent investigators have relied on records and often short-lived log files that weren’t meant for forensic use, and Amnesty said surveillance groups have grown increasingly aware of those forensic efforts. Intrusion Logging, a feature of Android Advanced Protection Mode, is designed specifically to keep track of possible intrusions for forensic purposes. It keeps records of security incidents like device unlocking, physical access, and spyware installation and removal. (Tim Starks / CyberScoop)
Related: Google, Amnesty International, TechCrunch
According to top executive Tisha van Lammeren, Dutch telco Odido did not realize that data belonging to millions of customers had been stolen until the hacker group told the company themselves two days later.
Odido was hacked in early February by the criminal group ShinyHunters. Customer data from telecom provider Ben was also stolen during the attack. After Odido refused to pay, the hacker group posted the data of over 6 million people on the dark web. "That was a dark day for all of us," says Van Lammeren.
It is the first time since the hack that Odido's top management has reflected on the attack in the media. Speaking to the NOS, Van Lammeren also says that the company, one of the country's largest telecom providers, could have communicated better about the attack. "Customers do resent us for the silence." (Stan Hulsen and Lisa Schallenberg / NOS)
Exaforce, an AI startup that detects and thwarts attacks in real time, announced it had raised $125 million in a Series B venture funding round.
Backers included HarbourVest, Peak XV, Mayfield, Khosla Ventures, Seligman Ventures, and AICONIC. (Marina Temkin / TechCrunch)
Related: Business Wire, Help Net Security, Security Week, Silicon Angle, Ventureburn, FinSMEs, CityBiz
Best Thing of the Day: Happy Cyber Days in the UK
The UK government hailed the continued growth of its burgeoning cybersecurity sector, which generated revenues of £14.7bn ($19.9bn) last year, up 17% year-over-year.
Worst Thing of the Day: Pervert Glasses Sales Are Booming
Meta's intrusive and privacy-violating smart glasses are selling briskly, with seven million pairs and counting having been sold.
Bonus Worst Thing of the Day: When No One Knows Whether AI Is Secure
The Berryville Institute of Machine Learning (BIML) published a research paper that examines why none of the existing tools for measuring AI security actually work.
Closing Thought