Hackers turned to AI in attempted mass cyberattack, Google reveals
Trump's planned AI-enabled cyber EO stops short of requirements, German authorities shut down relaunched Crimenetwork, L3 Trenchant zero-day peddling exec order to pay $10m, Poland has thwarted many Russian sabotage efforts, IMF warns of financial shock from AI-enabled cyberattacks, much more
Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
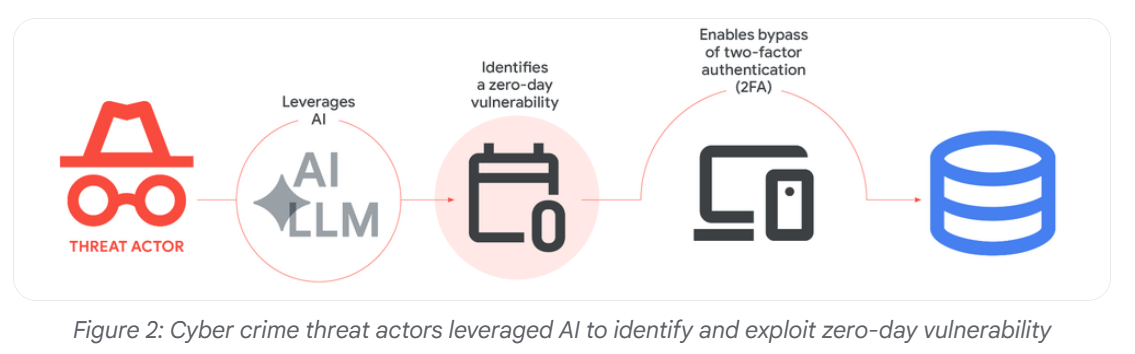
Google researchers published a report saying that a criminal hacking group recently attempted to launch a widespread cyberattack that appeared to rely on artificial intelligence to detect a previously unknown bug, highlighting the potential threat that AI poses to digital security.
“We have high confidence that the actor likely leveraged an AI model to support the discovery and weaponization of this vulnerability,” the report said.
The tech giant did not say precisely when the thwarted attack happened, whom it was targeting, or which AI platform the hackers used, but the company added that it did not believe it was its own Gemini chatbot.
The zero-day flaw was detected by the Google Threat Intelligence Group within the past few months and was exploited by “prominent cybercrime threat actors” in a script of the Python programming language. It would have allowed the hackers to bypass two-factor authentication on “a popular open-source, web-based system administration tool,” though the hackers also would have needed access to valid credentials like user names and passwords to be successful, the company said.
Google declined to identify the administration tool but said it notified the software maker quickly enough to allow for a patch before the attack could do damage. It also declined to identify the hackers. (Dustin Volz / New York Times)
Related: Google Cloud, CyberScoop, Bleeping Computer, CSO Online, Silicon Angle, Forbes, Bloomberg, Infosecurity Magazine
The Trump administration is preparing to order US agencies to partner with artificial intelligence companies to protect networks from AI-enabled cyber attacks, though the directive would stop short of requiring government approval for cutting-edge models, according to people familiar with the matter.
A draft executive order from President Donald Trump would revamp existing cybersecurity information-sharing programs to include AI companies and address threats posed by the emerging technology, said the people, who spoke on condition of anonymity to discuss confidential proceedings.
Those changes would make it easier to find and patch vulnerabilities across federal, state, and local networks, as well as critical US infrastructure, without mandating new oversight of AI models, the people said.
It’s unclear how soon Trump will sign the measure, which is still subject to change. Details on the latest plan for the order — and the evolution of policy ideas that had been considered but are unlikely to survive internal White House deliberations — have not yet been reported.
In response to a request for comment, a White House official characterized discussion of potential executive orders as speculation and said that any policy announcement would come directly from Trump. Spokespeople for top AI developers OpenAI and Anthropic PBC didn’t immediately respond to messages seeking comment. (Maggie Eastland and Courtney Subramanian / Bloomberg)
Related: Crypto Briefing, Raw Story, Politico, PYMNTS
German authorities have shut down a relaunch version of the criminal marketplace 'Crimenetwork' that generated more than 3.6 million euros, and arrested its operator.
Crimenetwork was the largest online cybercrime marketplace in Germany, operating since 2012 and with 100,000 registered users. The platform enabled the sale of illegal services, substances, and stolen data.
In late 2024, the Public Prosecutor's Office in Frankfurt am Main, the Central Office for Combating Cybercrime (ZIT), and the Federal Criminal Police Office (BKA) dismantled the operation by seizing the platform and arresting one of its administrators.
Just a few days later, a new version of the Crimenetwork emerged on a new infrastructure administered by a new operator.
Earlier this week, a 35-year-old German man suspected of administering the new Crimenetwork was arrested at his residence in Mallorca, Spain, by a special unit of the Spanish National Police under a European arrest warrant.
The rebooted version of the cybercrime platform offered a similar range of illicit goods and services, and quickly amassed 22,000 users and over 100 vendors.
In terms of revenue, evidence gathered during the police action suggests that the new version of Crimenetwork had generated at least €3.6 million ($4.2 milion) in revenue.
The police also seized approximately €194,000 ($228,000) in allegedly illicit assets and obtained substantial amounts of user and transaction data to facilitate further investigation. (Bill Toulas / Bleeping Computer)
Related: BKA, Infosecurity Magazine, Busted Again Crime Network, Karlsruhe Public Prosecutor's Office, Security Week, Crypto Briefing

Peter Joseph Williams, the former L3 Trenchant executive recently convicted of stealing zero-day exploits from his employer and selling them to a Russian broker, has been ordered to pay $10 million to his former employer and its parent company, according to a new judgment issued by a US district court judge.
He had previously been ordered to pay $1.3 million in restitution as part of his plea agreement, bringing his total restitution to $11.3 million, considerably less than the $35 million in restitution that prosecutors had sought.
Williams had told FBI agents last year, when he voluntarily met with them for an interview during their investigation into the theft of the code, that he believed that just two of the eight hacking tools he stole from his employer were worth about $35 million – meaning this was potentially the amount of revenue that L3 Trenchant and its parent company L3Harris Technologies lost from the theft of the tools. Prosecutors subsequently used this against Williams in demanding that the court set his restitution payments at $35 million. (Kim Zetter / Zero Day)
Related: TechCrunch
Poland’s Internal Security Agency published a report covering the last two years of the agency’s operations and threats the country faced, saying its intelligence service had thwarted multiple acts of sabotage from Russian government spies and hackers, who targeted military facilities, critical infrastructure, as well as civilian targets.
“The most serious challenge remains the sabotage activity against Poland, inspired and organized by Russian intelligence services. This threat was (and is) real and immediate. It requires full mobilization,” read the report.
The report did not specify whether the hackers behind the attacks on the water treatment facilities were the Russian government or spies. But Poland has recently been the target of several attempts by Russian government hackers to attack its infrastructure, including a failed attempt to bring down the country’s energy grid. That breach was later attributed to poor security controls at the targeted facilities. (Lorenzo Franceschi-Bicchierai / TechCrunch)
Related: Poland's Internal Security Agency, Security Week, United24, The Record, NewsBytes
The International Monetary Fund warns that advances in artificial intelligence can strengthen markets’ defense against cyber threats, but the technology now has the capacity to cause a macro-financial shock too.
The IMF's analysis suggests that extreme losses caused by a cyber incident could trigger funding strains, raise solvency concerns, and disrupt broader markets.
That adds to the chorus of concerns raised by authorities in the US, EU, and elsewhere about the dangers of AI tools capable of carrying out cyberattacks.
The IMF said that the recent release of Anthropic’s Claude Mythos model underscores how fast risks are rising.
“Mythos could find and exploit vulnerabilities in every major operating system and web browser—even when used by non-experts,” it said, foreshadowing how AI-driven cyber risks could destabilize the financial system if not managed carefully.
Such powerful models give attackers the advantage over defenders because it is faster to find weak spots than it is to patch and fix them, the fund said. (Fabiana Negrin Ochoa and Kimberley Kao / The Wall Street Journal)
Related: IMF, Decrypt, Asia Business Daily, Cryptopolitan, ComputerWeekly, Incrypted, Heise Online
Matthew Isaac Knoot, from Nashville, Tennessee, and Erick Ntekereze Prince, of New York, were each sentenced to 18 months in prison in separate cases involving how they misrepresented themselves as either an American IT worker or a company offering IT services performed by Americans, respectively, on behalf of North Korean scammers.
Both won jobs to perform IT work for US-based companies, and both provided space for company-owned laptops in their home or office, where remote access software was installed to allow North Koreans to work from overseas while appearing to be located in the States.
According to the DoJ, the pair generated more than $1.2 million in fraudulent revenue for North Korea, some of which was paid to them for their participation in the scheme. Knoot reportedly earned $15,100, which he will have to pay back as restitution to the companies and to the government; Prince will have to give back approximately $89,000 he got from Kim Jong Un's government.
Between them, Prince and Knoot forced the nearly 70 US companies they victimized to spend $1.5 million to audit and remediate their devices, systems, and networks to eliminate all traces of the Nork intruders. (Brandon Vigliarolo / The Register)
Related: Justice Department, HackRead
After roughly $209,000 was drained from Renegade.fi’s V1 Arbitrum dark pool at 8:27 am UTC on Sunday, about $190,000 was returned when the exploiter sent back more than 90% of the assets within 45 minutes.
What began as an Arbitrum dark pool exploit turned into a partial whitehat recovery, with funds flowing back to a wallet identified on Arbiscan as 0xE4A…5CFBE. The returned assets included USDC, wrapped Bitcoin, and wrapped Ether.
According to Blockaid, the attack worked by injecting malicious logic into a faulty function tied to Renegade’s resolver infrastructure. Soon after, Renegade made an on-chain offer: return the remaining funds and receive a 10% whitehat bounty.
The response came quickly. Within 45 minutes, the attacker had sent back more than 90% of the assets, turning a potentially larger loss into what is now being described as a Renegade whitehat crypto recovery. (The Cryptonomist)
Related: Cointelegraph, Cryptobriefing
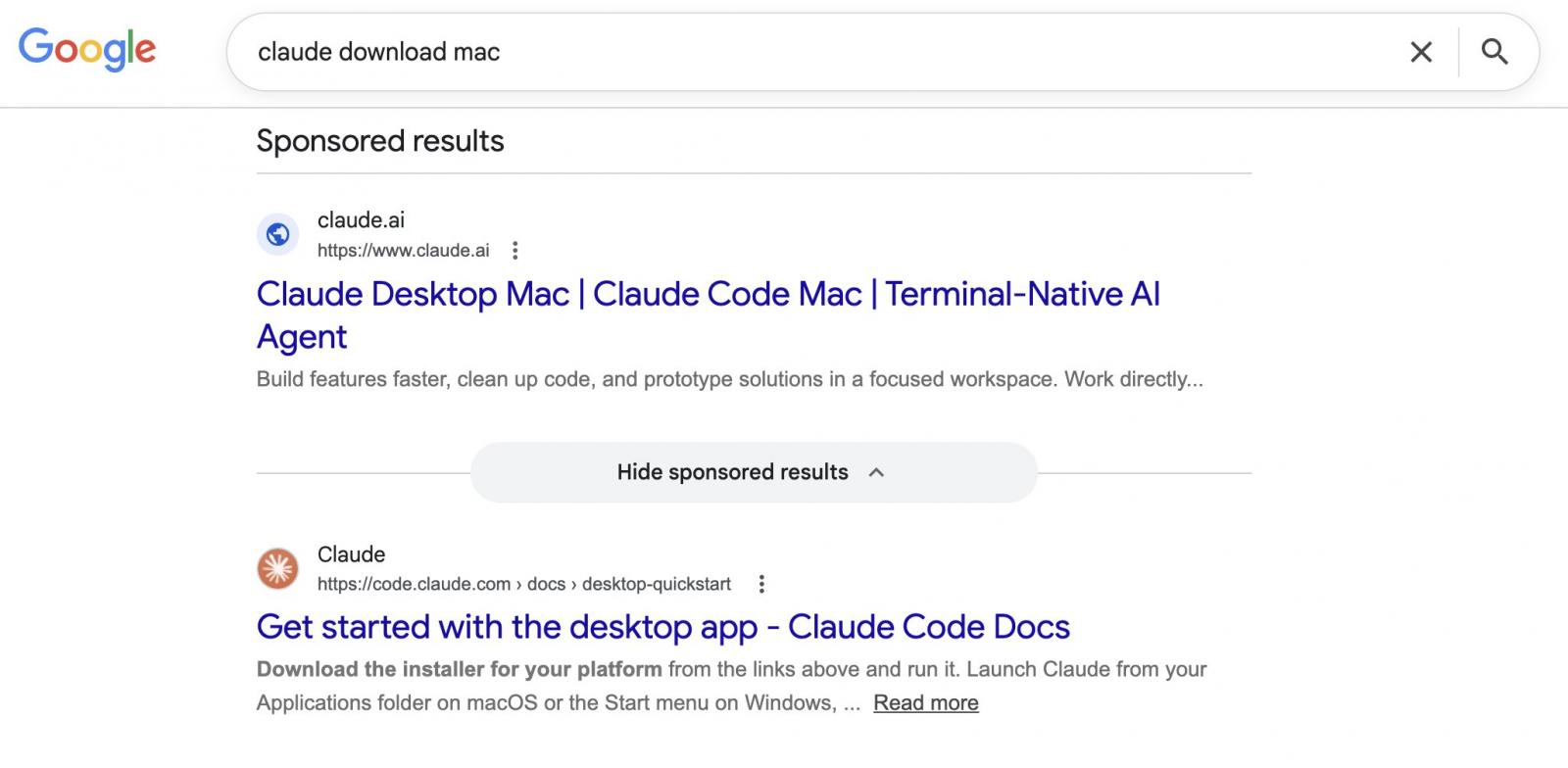
Berk Albayrak, a security engineer at Trendyol Group, spotted attackers abusing Google Ads and legitimate Claude.ai shared chats in an active malvertising campaign.
Users searching for "Claude mac download" may come across sponsored search results that list claude.ai as the target website, but lead to instructions that install malware on their Mac.
Albayrak identified a Claude.ai shared chat that presents itself as an official "Claude Code on Mac" installation guide, attributed to "Apple Support."
The chat walks users through opening Terminal and pasting a command, which silently downloads and runs malware on their Mac.
While attempting to verify Albayrak's findings, BleepingComputer landed on a second shared Claude chat carrying out the same attack through entirely separate infrastructure.
Users should navigate directly to claude.ai for downloading the native Claude app, rather than clicking sponsored search results. The legitimate Claude Code CLI is available through Anthropic's official documentation and does not require pasting commands from a chat interface. (Ax Sharma / Bleeping Computer)
Related: LinkedIn, Cyber Press
LayerZero issued a public apology Friday for its handling of the fallout from the April 18 exploit that drained roughly $292 million in rsETH from Kelp DAO's cross-chain bridge, marking a notable tonal shift from its earlier post-mortem that characterized the protocol as having "functioned exactly as intended."
"We've done a terrible job on comms over the past three weeks," LayerZero wrote in the blog post, also cross-posted to X. "We wanted to prioritize completeness in the form of a comprehensive post-mortem, but we should have led with directness."
The protocol said its internal RPC nodes, which its Decentralized Verifier Network (DVN) relied on to read source-chain state, were compromised by North Korea's Lazarus Group. The attackers poisoned those nodes' data feeds while simultaneously launching a DDoS attack against LayerZero's external RPC providers, forcing the DVN to fall over to compromised infrastructure and sign off on transactions that never actually occurred. LayerZero had earlier attributed the attack to the Lazarus subgroup known as TraderTraitor.
The post acknowledged a point that LayerZero had previously resisted: it should not have allowed its DVN to serve as the sole verifier for high-value transactions. "We believe developers should choose their own security configurations, but we made a mistake by allowing our DVN to act as a 1/1 DVN for high-value transactions," the company wrote. "We didn't police what our DVN was securing, which created a risk we simply didn't see." (Zack Abrams / The Block)
Related: LayerZero, CoinDesk, Bitcoin News, Blockchain.News, CryptoPotato, crypto.news
Hackers who gained access to the databases of Spanish fast-fashion retailer Zara stole data belonging to more than 197,000 customers, according to data breach notification service Have I Been Pwned.
As Inditex stated last month, when the data breach was widely reported, the compromised databases were hosted by a former tech provider and contained information about business relationships with customers in different markets.
However, Inditex noted that the attackers didn't gain access to affected customers' names, phone numbers, addresses, credentials, or payment information (such as bank cards).
It also added that its operations and systems were unaffected, but has yet to attribute the breach to a specific threat actor and to share the name of the hacked provider. (Sergiu Gatlan / Bleeping Computer)
Related: Inditex, Infosecurity Magazine
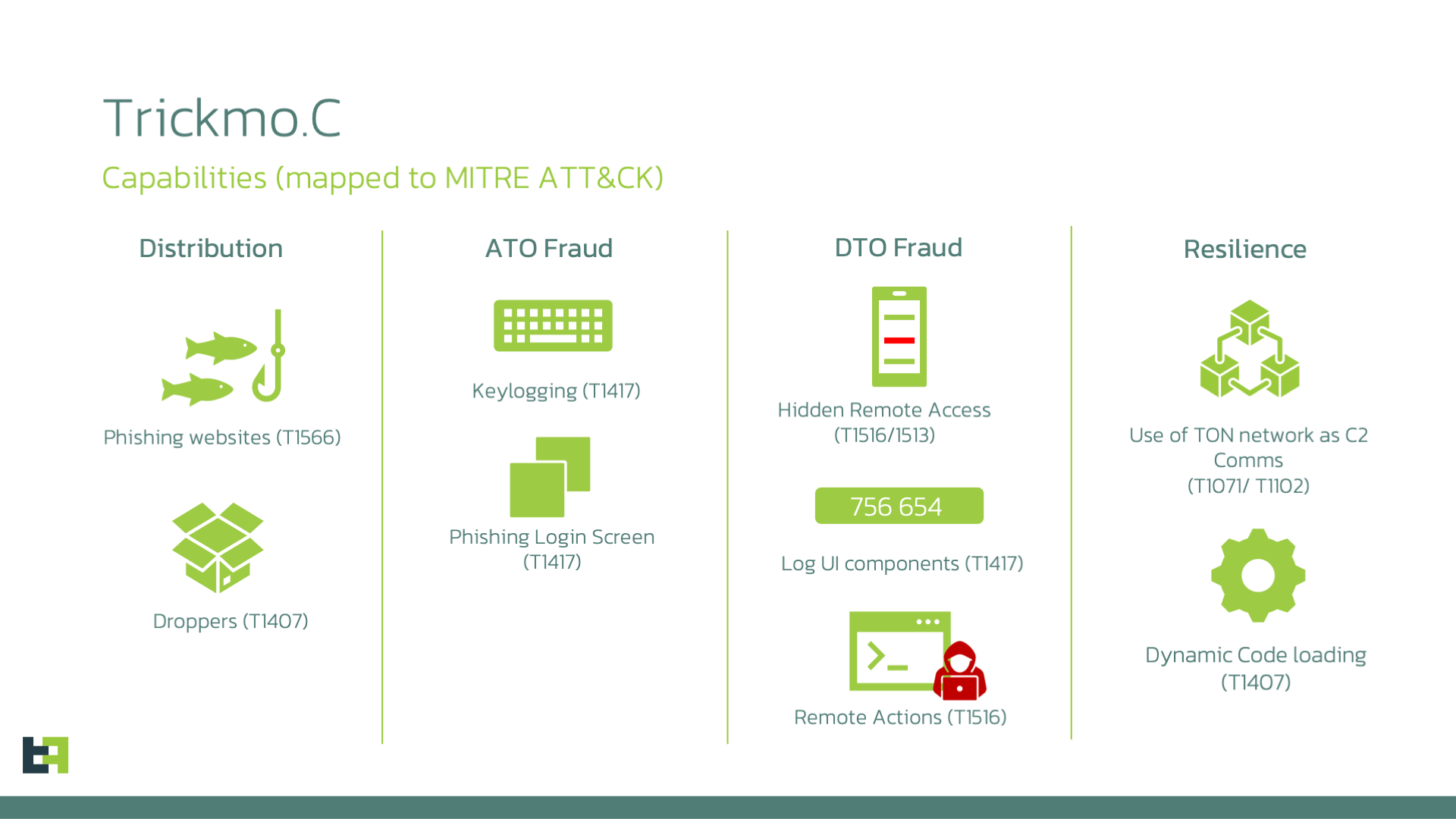
Researchers at ThreatFabric report that a new variant of the TrickMo Android banking malware, which they call Trickmo.C, delivered in campaigns targeting users across Europe, introduces new commands and uses The Open Network (TON) for stealthy command-and-control communications.
ThreatFabric says that the malware is disguised as TikTok or streaming apps and targets banking and cryptocurrency wallets of users in France, Italy, and Austria.
The key new feature in the current variant is the TON-based communication with the operator, which uses .ADNL addresses are routed through an embedded local TON proxy running on the infected device.
TON is a decentralized peer-to-peer network originally developed around the Telegram ecosystem that allows devices to communicate with the web via an encrypted overlay network rather than publicly exposed internet servers.
TON uses a 256-bit identifier instead of a normal domain, which hides the IP address and communication port, thus making the real server infrastructure more difficult to identify, block, or take down. (Bill Toulas / Bleeping Computer)
Related: ThreatFabric
The US Federal Communications Commission announced that it was extending temporary waivers allowing certain foreign-produced drones, drone components, and consumer routers to continue receiving software and firmware updates in the United States.
In late 2025 and early 2026, the FCC added these categories of equipment to its “Covered List,” which effectively blocked already-authorized devices from receiving post-approval software and firmware modifications. The agency subsequently issued waivers permitting critical security and functionality updates to continue through January 1, 2027, for drones and drone components, and through March 1, 2027, for consumer routers.
Under the updated waiver, manufacturers of affected devices will now be allowed to continue issuing software and firmware updates until at least January 1, 2029, provided the devices had already been authorized for use in the US before being added to the FCC’s “Covered List.” The extension also broadens the waiver to include certain Class II permissive changes involving software and firmware updates intended to mitigate consumer harm. (Etiido Uko / Tom's Hardware)
Project Eleven published a new report on Wednesday proposing that the inflection point of quantum computers breaking modern encryption, often referred to as "Q-Day," could come as early as 2030.
The startup, focused on post-quantum security, said a breakthrough is "more likely than not" by 2033, with estimates ranging a few years in either direction.
Project Eleven predicts that quantum advancements will happen in sudden leaps rather than a slow and linear progression.
It says progress in hardware and algorithms is compounding and could lead to a major jump in capabilities that it describes as "nothing, and then all at once." (Kyle Baird / The Block)
Related: Project Eleven, The Crypto Times, CoinCentral, Incrypted, Crypto Briefing, CoinDesk
Fictional portrayals of artificial intelligence can have a real effect on AI models, according to Anthropic.
Last year, the company said that during pre-release tests involving a fictional company, Claude Opus 4 would often try to blackmail engineers to avoid being replaced by another system. Anthropic later published research suggesting that models from other companies had similar issues with “agentic misalignment.”
Apparently, Anthropic has done more work around that behavior, claiming in a post on X, “We believe the original source of the behavior was internet text that portrays AI as evil and interested in self-preservation.”
The company went into more detail in a blog post stating that since Claude Haiku 4.5, Anthropic’s models “never engage in blackmail [during testing], where previous models would sometimes do so up to 96% of the time.”
The company said it found that training on “documents about Claude’s constitution and fictional stories about AIs behaving admirably improve alignment.” (Anthony Ha / TechCrunch)
Related: Anthropic, Business Insider, PCMag, Crypto Briefing, PCWorld
Best Thing of the Day: Canvas Coming Back Inch-by-Inch
The cloud-based learning platform Canvas is back online for some Australian schools and universities, though the deadline set by ShinyHunters is still looming.
Worst Thing of the Day: We'll Beat You Up, Bro
Cyber attackers are now going further in their efforts to extort their victims, with as much as 40% of ransomware attacks now accompanied by physical threats.
Bonus Worst Thing of the Day: Here's What Musk Thinks of Your Grok Complaints
Elon Musk’s AI company that runs X chatbot Grok has quietly moved its official European point of contact for users to Estonia, to a building whose owner says it has no contract with the company or its representatives.
Closing Thought





