Social media scams cost Americans $2.1 billion — and Facebook leads the pack
Medtronic hit by cyberattack, Toronto cops busted three people in connection with SMS blasters, Handala claims to have stolen personal info on 2,379 US Marines, Google agrees to Pentagon's anything goes for its AI but employees beg it not to, New BlackFile data theft group emerges, much more
Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
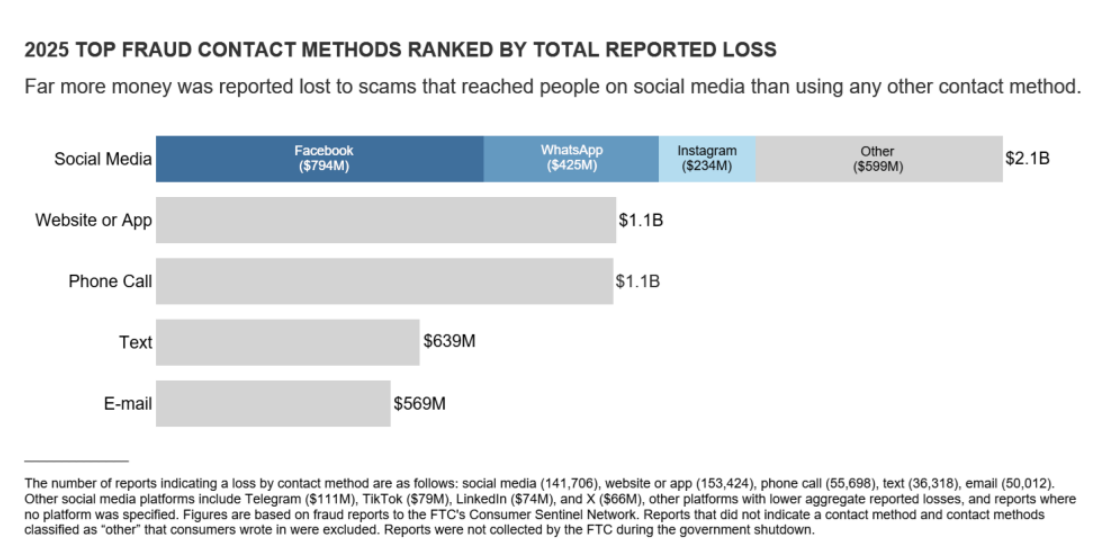
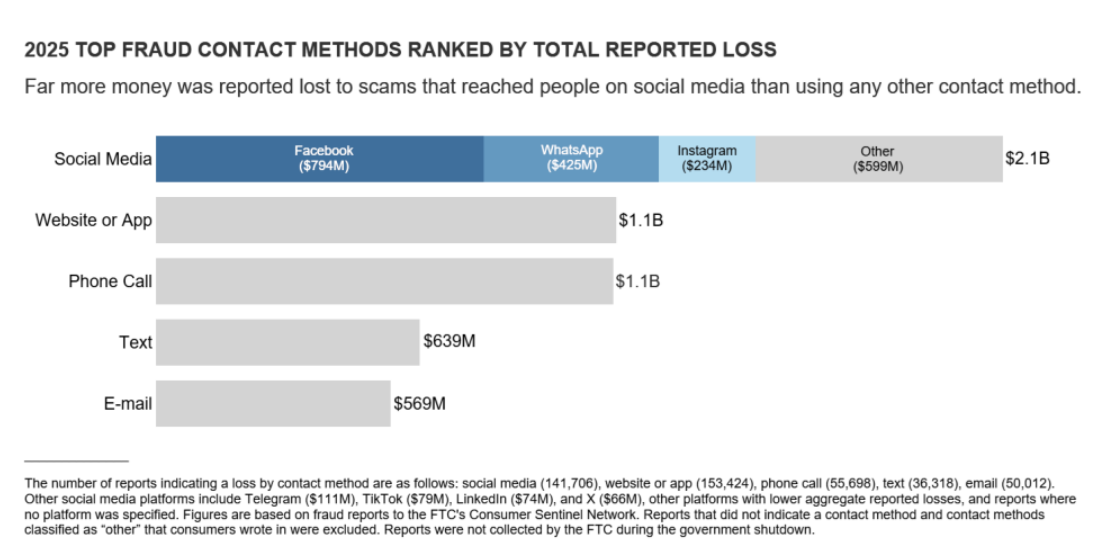
Americans lost $2.1 billion to social media scams in 2025, according to a new report from the US Federal Trade Commission (FTC).
The agency reports that losses from social media scams have increased eightfold and that social media scams resulted in higher losses than any other method scammers used to contact consumers.
Nearly 30% of people who reported losing money to scams said the schemes began on social media. More people reported losing money to scams that originated on Facebook than on any other social media platform, with WhatsApp and Instagram ranking a distant second and third. Additionally, people reported losing far more money to scams on Facebook alone than they reported losing to text or email scams.
The FTC’s data shows that social media scams take many forms, including shopping scams, which were the most reported type of social media scam last year. Over 40% of people who lost money to social media scams said they ordered an item they saw in an ad, ranging from clothing and cosmetics to car parts and even puppies. Many of these ads led to unfamiliar websites, while others sent people to fake sites for well-known brands that claimed to offer big discounts.
Another common type of social media scam involves investment schemes that begin with ads or posts offering to teach people how to invest. Other scammers pose as friendly advisers or create WhatsApp groups filled with fake testimonials. These types of investment scams led to $1.1 billion in losses.
Additionally, nearly 60% of people who reported losing money to a romance scam in 2025 said it started on a social media platform. (Aisha Malik / TechCrunch)
Related: FTC, FTC, FTC, Bleeping Computer, Bitdefender, PYMNTS, WGME, Tom's Guide, CNET, Tech Times
Medical device maker Medtronic said in a statement and an SEC filing that a cyberattack on its computer systems last week did not affect its products or ability to meet patient needs, and is not expected to materially impact its business or financial results.
Medtronic said the attack that hit the network supporting its corporate IT systems did not impact its products, patient safety, manufacturing, or distribution operations.
The incident underscores growing cyber risks for medical device makers, as attacks disrupt critical health services, raising concerns over patient safety and data security. The IT network remains separate from those that support its products, manufacturing, and distribution operations, Medtronic said.
Medtronic's breach disclosure follows ShinyHunters' claims that the data-theft-and-extortion crew broke into the medical device business and compromised "over 9M records containing PII and other terabytes of internal corporate data." (Sahil Pandey / Reuters and Jessica Lyons / The Register)
Related: Medtronic, SEC, Security Week, Security Magazine, Security Affairs, Mass Device, HealthExec, SC Media, Drug Delivery Business, The Cyber Express, The Register
Toronto police say they've arrested three people in connection with a cybercrime investigation that used "SMS blasters," a new technology not previously detected in Canada, that mimics a cell tower to defraud victims.
Three men from Markham and Hamilton, ranging in age from 21 to 27, have been arrested and charged with offenses including fraud and mischief.
Speaking at a news conference Thursday, Det.-Sgt. Lindsay Riddell said the investigation began in November 2025, when police were alerted to a suspected SMS blaster operating in downtown Toronto.
Police later determined that the blaster was operating out of a car, which allowed it to move around the city and Greater Toronto Area, Riddell said.
“We believe tens of thousands of devices connected to the blaster over several months," she said, noting that more than 13 million network disruptions were identified by police. (CBC News)
Related: Toronto Police Service, Gizmodo, Bleeping Computer, The Record, Tech Times, Global News, National Post, The Cyber Express, Toronto Star

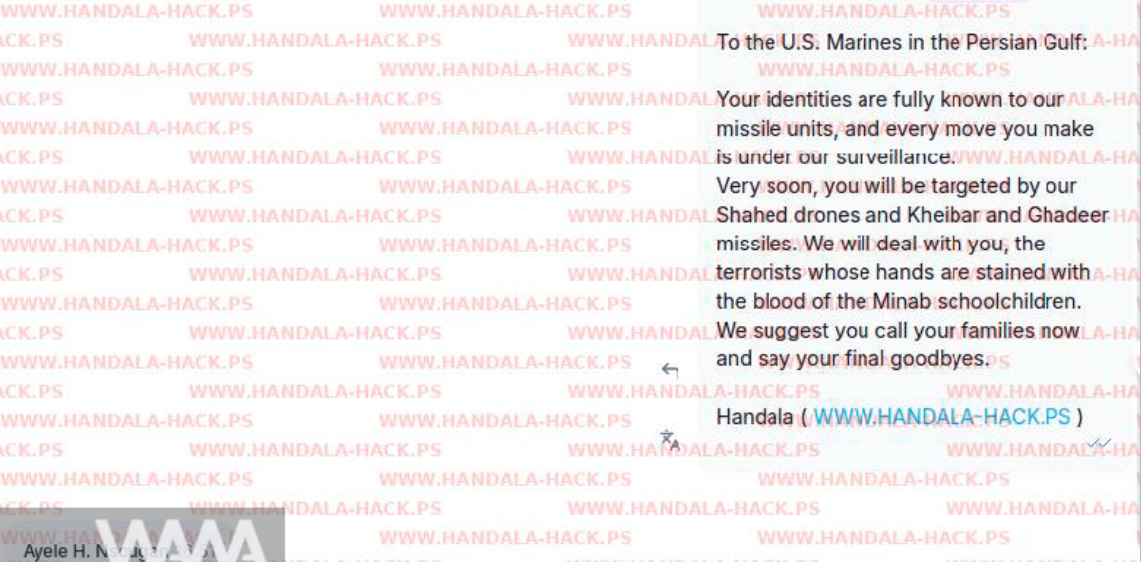
Handala, a hacking group linked to the Iranian government, has issued deadly threats to US Marines in the Middle East after leaking their personal information.
On its Telegram channel, Handala wrote: ‘Today, merely as a demonstration, and to prove the extent of our intelligence superiority, we have published the full personal details of 2,379 US Marines stationed in the Persian Gulf region.
‘This is just a drop in the ocean of our surveillance capabilities. The “security” that American commanders boast about is nothing more than an empty illusion, a childish fantasy.’
The message also claimed to know ‘detailed information’ about the Marines’ families, home addresses, bases, shopping habits, and ‘nightly activities.' (Sarah Hooper / Metro)
Related: WANA, PressTV, News.AZ
Google joined a growing list of technology firms to sign a deal with the US Department of Defense to use its artificial intelligence models for classified work, The Information reported, citing a person familiar with the matter.
The agreement allows the Pentagon to use Google's AI for “any lawful government purpose," the report added, putting it alongside OpenAI and Elon Musk's xAI, which also have deals to supply AI models for classified use.
The Pentagon had been pushing top AI companies such as OpenAI and Anthropic to make their tools available on classified networks without the standard restrictions they apply to users.
Meanwhile, hundreds of AI researchers at Google signed a letter urging Chief Executive Officer Sundar Pichai to refuse to make the company’s artificial intelligence systems available for classified workloads for US defense missions, according to organizers of the effort.
“We are Google employees who are deeply concerned about ongoing negotiations between Google and the US Department of Defense,” reads the letter. “As people working on AI, we know that these systems can centralize power and that they do make mistakes.” (Chandni Shah, Disha Mishra, Hyunsu Yim / Reuters, Katrina Manson and Julia Love / Bloomberg)
Related: The Information, Gizmodo, The Verge, Business Insider, Financial Times, Bloomberg, SiliconANGLE, People Matters, Jerusalem Post, Newsmax, The Hill, Crypto Briefing, The Information, The Sun Malaysia, The Next Web, Decrypt, r/ArtificialIntelligence, Financial Times, Washington Post
According to information shared by cybersecurity firm Palo Alto Networks' Unit 42 with the Retail & Hospitality Information Sharing and Analysis Center (RH-ISAC), a new financially motivated hacking group tracked as BlackFile has been linked to a wave of data theft and extortion attacks against retail and hospitality organizations since February 2026.
The group, also tracked as CL-CRI-1116, UNC6671, and Cordial Spider, is impersonating corporate IT helpdesk staff to steal employee credentials and demand seven-figure ransoms.
Unit 42 security researchers have also linked BlackFile with moderate confidence to "The Com," a loose-knit network of English-speaking cybercriminals known for targeting and recruiting young people for extortion, violence, and the production of child sexual exploitation material (CSAM).
RH-ISAC said that the group's attacks begin with phone calls to employees from spoofed numbers, in which the threat actors pose as IT support to lure staff to fake corporate login pages that ask them to enter their credentials and one-time passcodes.
Using stolen credentials, the BlackFile attackers register their own devices to bypass multifactor authentication, then escalate access to executive-level accounts by scraping internal employee directories.
BlackFile steals data from victims' Salesforce and SharePoint servers using standard API functions, searching specifically for files containing terms such as "confidential" and "SSN."
The exfiltrated documents are downloaded to attacker-controlled servers and published to the gang's dark web data leak site before victims are contacted with ransom demands via compromised employee email accounts or randomly generated Gmail addresses.
To reduce the success rate of BlackFile's attacks, RH-ISAC recommends that organizations strengthen their call-handling policies, enforce multifactor identity verification for callers, and conduct simulation-based social engineering training for frontline staff. (Sergiu Gatlan / Bleeping Computer)
Related: Retail and Hospitality ISAC, SC Media, Bleeping Computer, Infosecurity Magazine, CyberScoop
Popular Australian gelato franchiser Gelatissimo has less than five days to respond to hackers who claim to have stolen highly sensitive data related to the company’s employees.
Ransomware collective Dragonforce published a listing for Gelatissimo on its dark web leak site on Monday night. It claimed to have compromised 352.42 gigabytes from the gelato chain, though it neglected to describe precisely what was stolen.
Instead, Dragonforce shared six sample screenshots of what appeared to be stolen employee data and operational details.
The screenshots included part of a spreadsheet that listed alleged first and last names of Gelatissimo employees, along with limited payment details about gross earnings, paid leave, overtime, bonuses, and withheld taxes. The spreadsheet also appeared to list the last four digits of employees’ tax file numbers.
The ransomware gang also shared an alleged visa application form related to one of the company’s employees, which itself contained a passport number, phone number, professional email address, and home address, alongside other details.
Other information shared by Dragonforce included an incident report following an apparent workplace accident in 2025, as well as screenshots of an alleged bank transfer receipt and a detailed corporate bank statement. (Leonard Bernardone / Information Age)
Related: Insurance Business, Cyber Daily
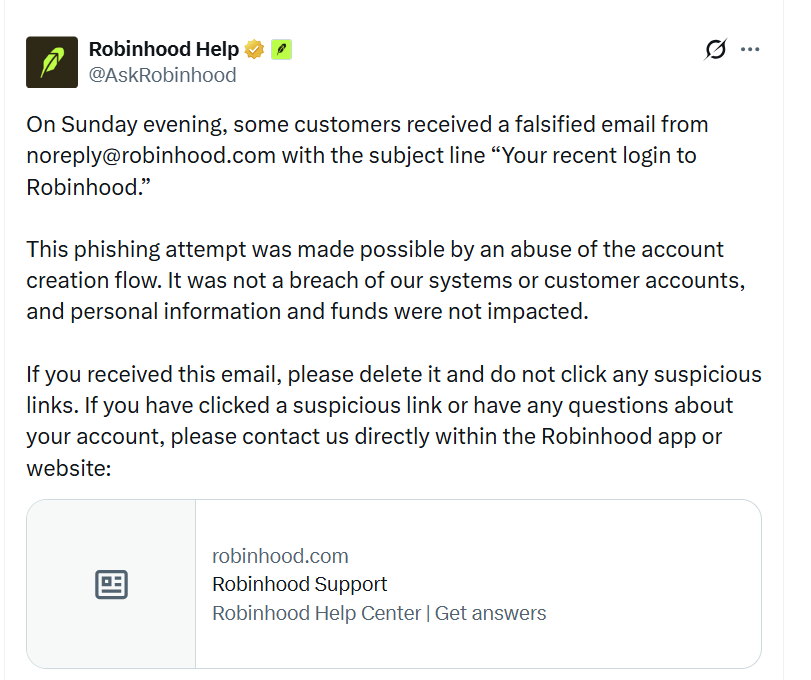
Online trading platform Robinhood's account creation process was exploited by threat actors to inject phishing messages into legitimate emails, tricking users into believing their accounts had suspicious activity.
Starting last night, Robinhood customers began receiving "Your recent login to Robinhood" emails stating that an "Unrecognized Device Linked to Your Account" was detected, containing unusual IP addresses and partial phone numbers.
"We detected a login attempt from a device that is not recognized," reads the phishing email. "If this was not you, please review your account activity immediately to secure your account."
Included in the email was a button titled "Review Activity Now", which led to a phishing site at robinhood[.]casevaultreview[.]com, which is now down.
However, screenshots on Reddit indicate that the site was likely used to try to steal Robinhood credentials.
Robinhood confirmed the incident in a statement posted to X.
"On Sunday evening, some customers received a falsified email from noreply@robinhood.com with the subject line 'Your recent login to Robinhood.'," posted RobinHood. (Lawrence Abrams / Bleeping Computer)
Related: Blockchain News, Help Net Security, The Street, Protos, CryptoPotato, The Coin Republic
Software security testing firm Checkmarx said data posted online appears to have come from one of its GitHub repositories after the Lapsus$ extortion crew claimed to have dumped the company’s source code, secrets, and other sensitive data.
Checkmarx said the investigation remains ongoing, and it's working to "verify the nature and scope" of the data. Current evidence, however, suggests that "this data originated from Checkmarx's GitHub repository, and that access to that repository was facilitated through the initial supply chain attack of March 23, 2026."
The security shop has since locked down access to the affected repo, and said if the investigation determines any customer information was posted online, it will notify "all relevant parties immediately."
A day earlier, Lapsus$ data thieves added Checkmarx to the list of victims on its leak site. In a post shared on X by Dark Web Informer, the extortionists claimed to have dumped a raft of sensitive information, including source code, API keys, MongoDB and MySQL login credentials, and employee details. (Jessica Lyons / The Register)
Related: Checkmarx, Sophos, eSecurity Planet, Bleeping Computer
The accidental exposure of student information from Missouri’s MOScholars program has reopened a broader fight over how much scrutiny the state’s private school voucher program should face.
After The Independent reported last week that student names, schools, and parent email addresses were accessible through the underlying data of a spreadsheet posted by the Missouri State Treasurer’s Office, Democratic lawmakers called for pausing new enrollments until a security review is completed and urged the Joint Committee on Education to hold an investigative hearing “as soon as possible.”
Republicans dismissed those demands as overreach, arguing the state should fix the problem without interrupting a program they say is working for families.
Still unresolved is whether parents were notified. The treasurer’s office said in a statement that it alerted the program’s seven educational assistance organizations, which it described as the “primary liaison” for families, but said it does not know whether any warnings have gone out to MOScholars participants.
By Wednesday, the treasurer’s office had removed the MOScholars spreadsheets from its website and replaced them with PDF files. (Annelise Hanshaw / Missouri Independent)
Related: Koran Manado, Missouri Independent, St. Louis Post-Dispatch, Columbia Daily Tribune
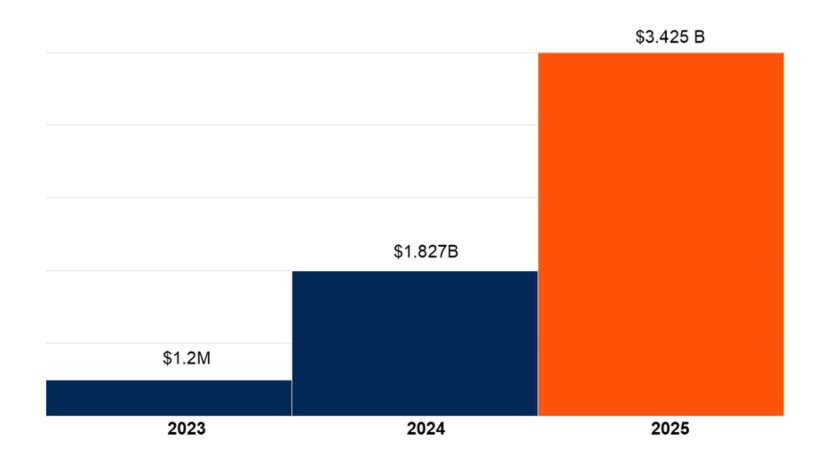
According to research and advisory firm Gartner, US states issued $3.45 billion in privacy-related fines to companies in 2025, a total larger than the last five years combined.
The increase is partly driven in part by stronger, more established privacy laws in states like California, new interstate partnerships built around enforcing laws across state lines, and a renewed focus to how AI and automation affect privacy.
The data indicates that “regulators are shifting their efforts away from awareness to full-scale enforcement,” marking a significant shift from even the last few years in how aggressively states are investigating and penalizing companies for privacy law violations. (Derek B. Johnson / CyberScoop)
Related: Gartner, Intellectia AI
Many of the most common metrics used to measure the effectiveness of the security operations center (SOC) are at best inaccurate and at worst actively harm SecOps teams, the National Cyber Security Centre (NCSC) has warned.
The NCSC’s CTO for architecture, Dave Chismon, wrote in a blog post that organizations often gravitate to measurements that can be easily expressed numerically to individuals who aren’t security specialists.
However, if “number of tickets processed” or “time taken to close a ticket” are used as metrics, staff may perversely be incentivized to rapidly triage and close them as false positives rather than investigate.
Similarly, “number of detection rules” may incentivize analysts to write as many rules as possible, driving up the number of false positives and ineffective rules.
In the same way, focusing on the volume of logs collected over the value of those logs is self-defeating if they don’t improve detection, Chismon said.
According to the NCSC, the only SOC metric that matters is: “does it detect (and respond to) attacks in a timely manner?” In other words, time to detect/time to respond (TTD/TTR). (Phil Muncaster / Infosecurity Magazine)
Related: NCSC
French authorities arrested a suspected hacker believed to be behind dozens of data breaches targeting public institutions, sports federations, and private organizations across the country, prosecutors said.
The suspect, a 20-year-old known online as HexDex, was detained in western France and placed in police custody as part of an investigation led by the cybercrime unit of the Paris prosecutor’s office. Citing authorities, local media reported that the individual is linked to roughly 100 reports of website breaches filed since late 2025.
The suspect admitted to using the alias HexDex to claim responsibility for hacks and publish stolen data on cybercrime marketplaces such as BreachForum and Darkforum, prosecutors said. Authorities seized the suspect’s Darkforum account and computer equipment, which will now undergo forensic analysis.
French officials said the hacker allegedly targeted a wide range of organizations, including a handful of national sports federations — among them sailing, athletics, motorsports, gymnastics, skiing, rugby league, aikido, university sports, mountaineering and climbing, and para-sports.
Other victims included food banks, hotel chains Logis Hôtels France and Brit Hotel, as well as the Philharmonie de Paris concert hall.
Related: Le Parisien, SC World, HackRead, Help Net Security
GCHQ's cyber arm has entered the hardware game with its first device designed to prevent cyberattacks on display devices.
Called SilentGlass, the small gadget's intellectual property is courtesy of the UK's National Cyber Security Centre (NCSC), and the signals intelligence agency licensed it out to UK-based Goldilock Labs to make it commercially available to all businesses and consumers.
SilentGlass is the NCSC's first branded device to hit the market. Announced publicly on Wednesday, the HDMI and DisplayPort-compatible device has already been deployed across "government estates" for several years and is capable of protecting "most high-threat environments." (Connor Jones / The Register)
Related: NCSC, Security Affairs, Cybersecurity Insiders
South Korean lawmakers protested what they described as US political pressure over a legal case involving Coupang Inc., with about 90 legislators planning to deliver a formal complaint to the US ambassador.
Lawmakers, including Park Hongbae from the ruling Democratic Party, said they would deliver a protest letter to the US envoy in Seoul, warning that attempts to influence legal proceedings in South Korea would amount to an infringement on judicial sovereignty.
“The investigation and adjudication of alleged criminal conduct are the exclusive authority of a sovereign state,” the lawmakers wrote in the letter Tuesday, adding that such processes must be conducted “independently and free from external pressure.”
The statement follows reports that some members of the US House of Representatives raised concerns about the treatment and safety of Coupang executives and linked the issue to broader diplomatic and security cooperation between the two countries. The e-commerce giant is based in the US and is widely popular in South Korea. (Heesu Lee / Bloomberg)
Related: Hankyoreh, The Korea Times, Nikkei Asia
Best Thing of the Day: Information Will Out, Baby
Russians of all stripes are openly questioning President Vladimir V. Putin’s moves to hamstring Internet access.
Bonus Best Thing of the Day: Do a Digital Detox With This Weird Faraday Cage
A new wrapper for the KitKat candy bar operates as a Faraday cage to block cell phone signals, advertising it under KitKat’s iconic “Take a Break” slogan.
Worst Thing of the Day: AI Agents Are Not Amusing
A Cursor coding agent running Claude Opus 4.6 found a credential mismatch that it fixed by deleting a Railway volume that contained production data and the recent backups.
Bonus Worst Thing of the Day: Abandon All Hope
A survey of Chief Information Security Officers (CISOs) from all 50 states and 2 territories found that just 26% of state CISOs are ‘extremely’ or ‘very’ confident that their state’s information assets are protected from cyber threats, down from 48% in 2022.
Closing Thought