AI cyber skills now doubling in months, not years
Microsoft's AI-driven MDASH system discovered 16 new Windows vulnerabilities, France's Mistral AI competes with Mythos for European banks, Dream Market admin busted by German and US cops, Shadowy firm BlackCore probed for French election interference, Signal to exit Canada if C-22 passes, much more
What if the next global arms race isn’t about nukes — but AI systems that can autonomously find and exploit software vulnerabilities at machine speed? Check out my latest CSO piece that explores the narrowing US-China AI gap and the implications of China developing its own “Mythos”-class cyber AI.
Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
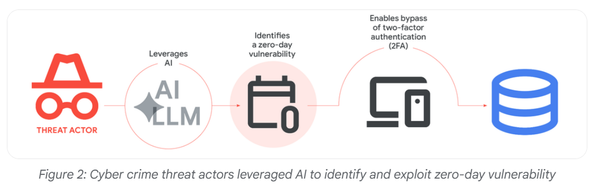
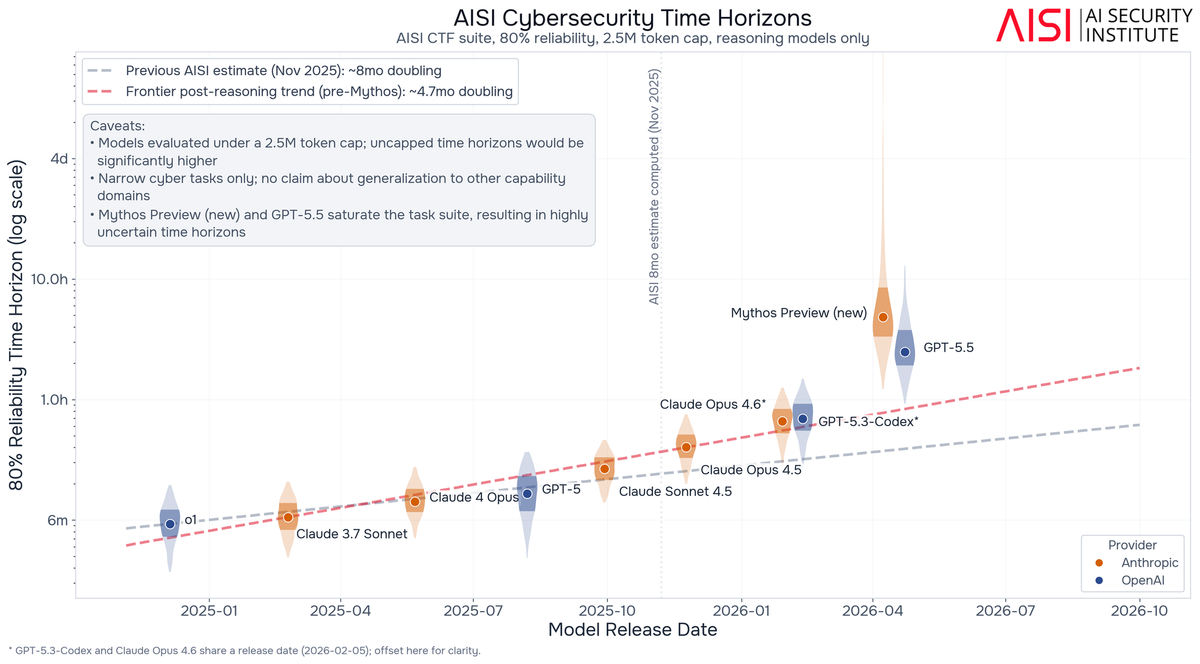
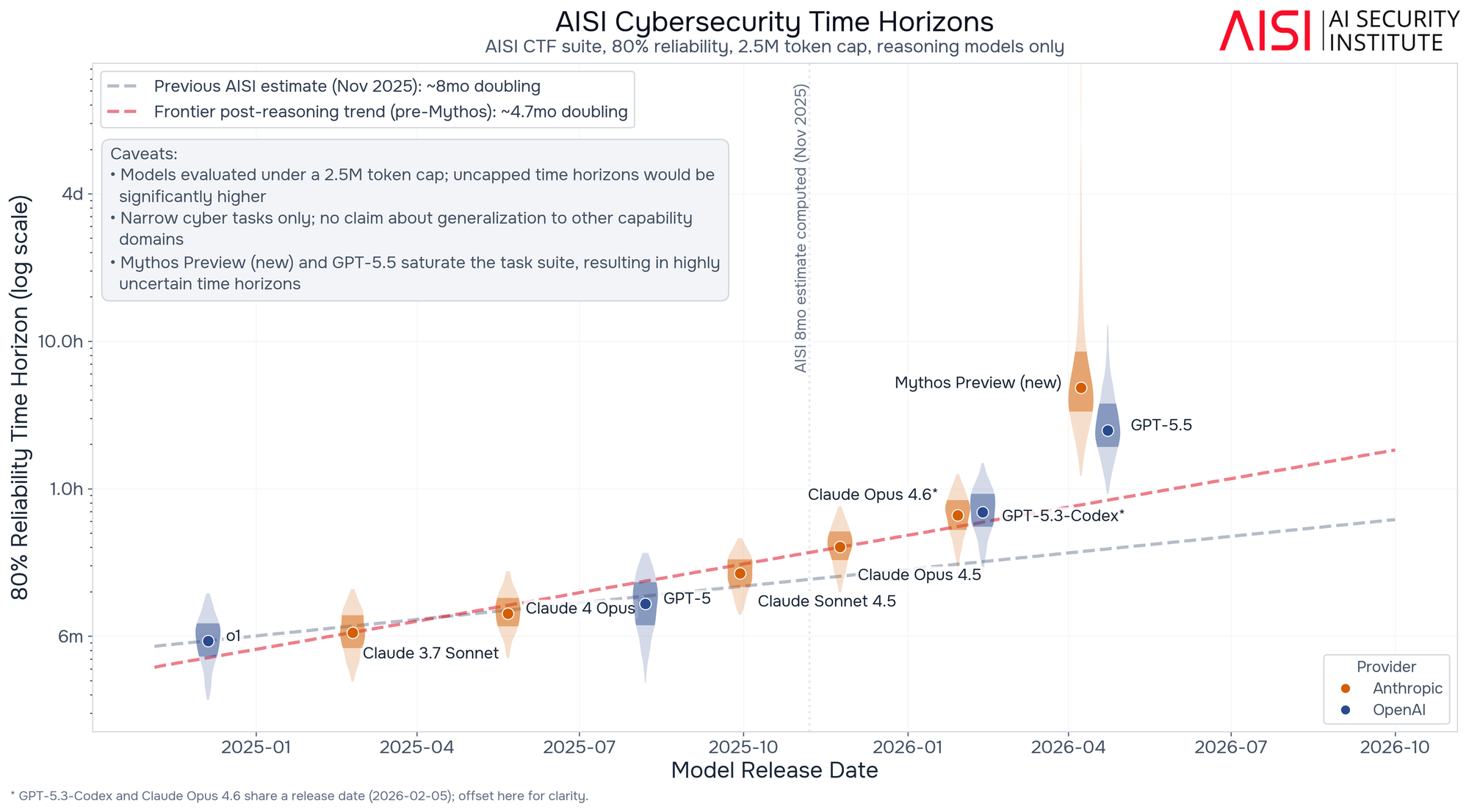
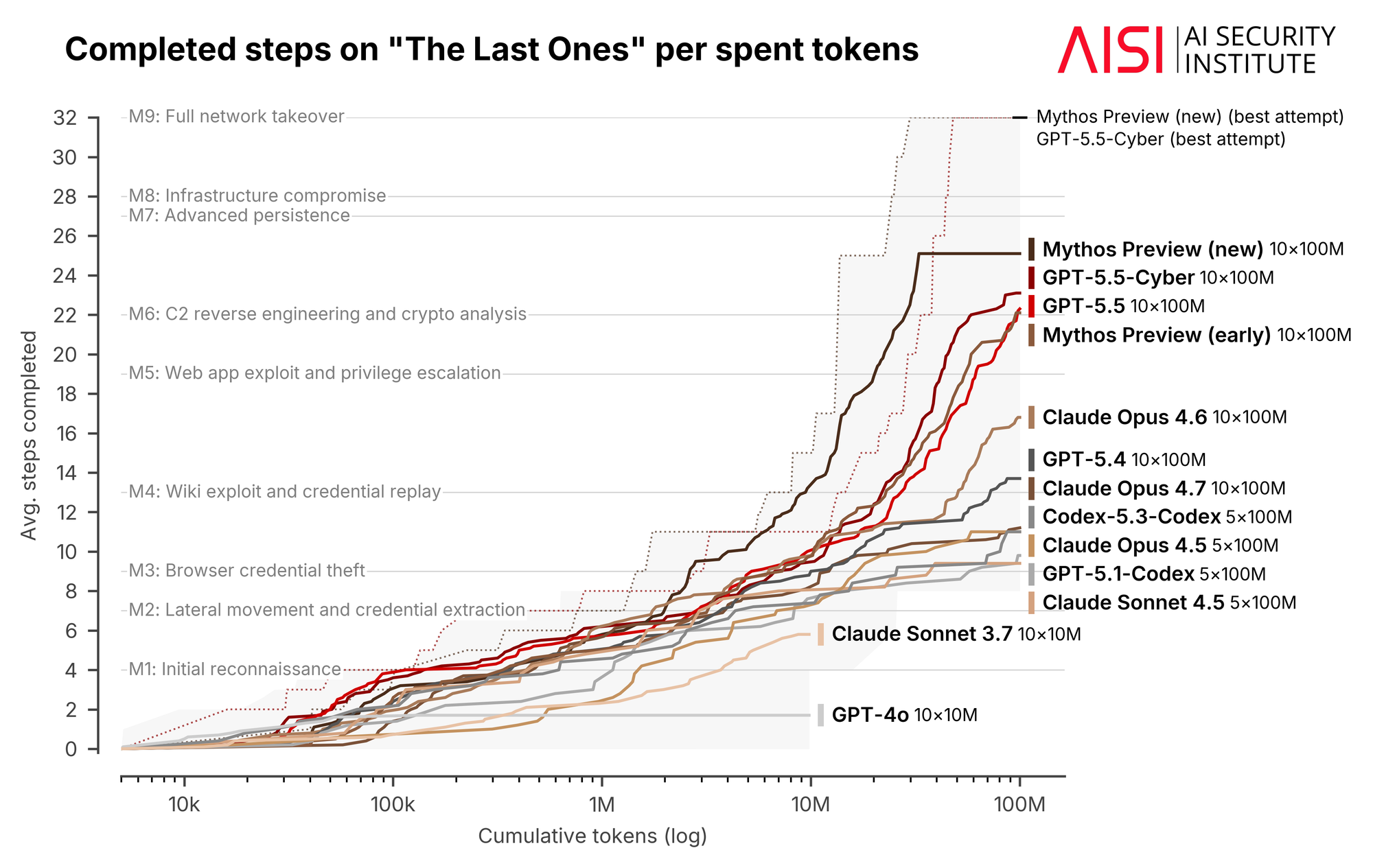
Two of the most advanced artificial intelligence models — Anthropic’s Claude Mythos Preview and OpenAI’s GPT-5.5 — have significantly surpassed the already-accelerating pace at which AI systems are completing autonomous cybersecurity tasks, according to separate findings published by the United Kingdom’s AI Security Institute (AISI) and Palo Alto Networks.
The AISI, which conducts pre-deployment evaluations of frontier AI models on behalf of the British government, said both Claude Mythos Preview and GPT-5.5 have substantially exceeded the doubling trend the institute had been tracking since late 2024. Whether the results represent an isolated capability jump or the start of a new, faster trajectory remains unclear.
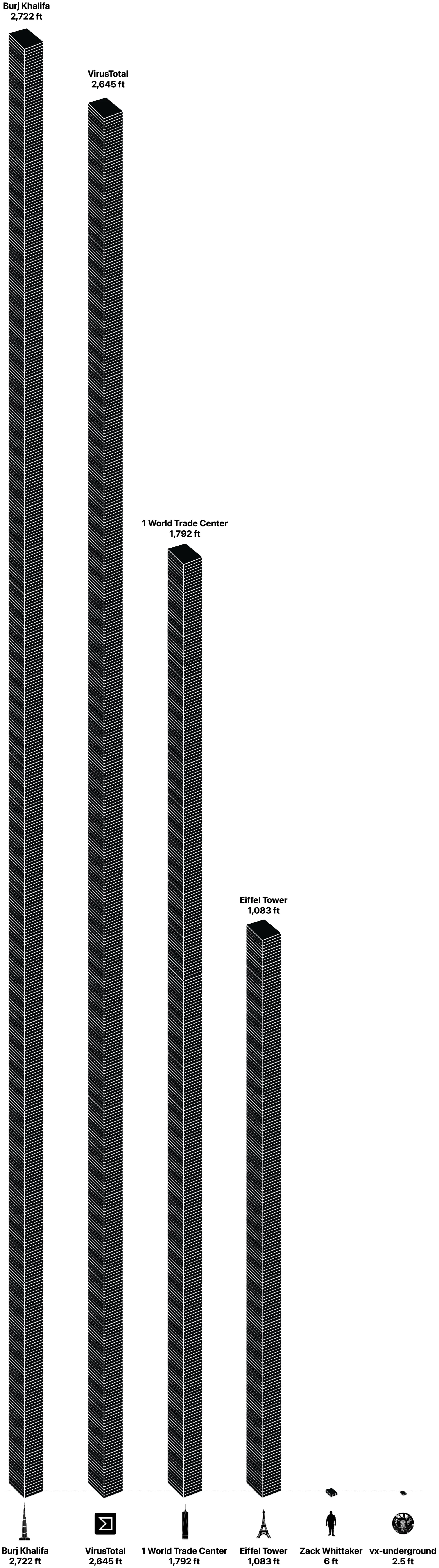
The AISI estimated earlier this year that frontier models’ 80% reliability cyber time horizon — a measure of how long a task takes a human expert, used as a proxy for AI autonomy — had been doubling approximately every five months. That was itself roughly half the eight-month doubling time the institute estimated in November 2025. Now Mythos Preview and GPT-5.5 have since outperformed any trend lines the institute has measured.
“Frontier AI’s autonomous cyber and software capability is advancing quickly: the length of cyber tasks that frontier models can complete autonomously has doubled on the order of months, not years,” the AISI wrote.
Palo Alto Networks reached similar conclusions through its own testing. The company said it began testing Claude Mythos in April as a launch partner for Anthropic’s Project Glasswing, and has since tested Claude Opus 4.7 and OpenAI’s GPT-5.5-Cyber as part of OpenAI‘s Trusted Access for Cyber program.
“The latest models are extraordinarily capable at finding vulnerabilities and changing them into critical exploit paths in near-real-time,” Palo Alto Networks wrote.
The company released security advisories covering 26 CVEs representing 75 issues — compared to a typical monthly volume of fewer than five CVEs — that were identified through AI model scanning across more than 130 products. All important vulnerabilities in its SaaS products had been patched, with patches available for all customer-operated products. (Greg Otto / Cyberscoop)
Related: AISI, The Register, XBOW, Axios, Palo Alto Networks, Security Week, CNBC, CyberScoop
Microsoft unveiled a new AI-driven vulnerability discovery system that identified 16 previously unknown Windows vulnerabilities, including four critical remote code execution flaws, in what security analysts say could mark a major shift in how software vulnerabilities are discovered and remediated.
The system, codenamed MDASH, was developed by Microsoft’s Autonomous Code Security team alongside the Windows Attack Research and Protection group.
The platform will enter private preview for enterprise customers next month, Microsoft said in a blog post announcing the system.
The vulnerabilities were patched as part of Microsoft’s May 12 Patch Tuesday release. (Gyana Swain / CSO Online)
Related: Microsoft Security Blog, BleepingComputer, The Hacker News, PCMag, SiliconANGLE, Lyrie Research, SecurityWeek, Help Net Security, Infosecurity, iTnews, ComputerWeekly.com, Neowin, Cybergym
French artificial intelligence startup Mistral AI is in discussions with European banks about deploying its answer to Anthropic PBC’s Mythos, the limited-access AI model that can uncover cybersecurity vulnerabilities at unprecedented speed and scale.
Mistral has been developing its own cybersecurity-focused AI model, according to people familiar with the matter. It isn’t clear when the model will be released, but the company has held discussions about it with the European banking sector, the people said, asking not to be identified as the information is private. Europe’s banks, lacking access to Mythos, are under pressure to detect and fix vulnerabilities that AI tools could exploit.
The French company was already working with its banking customers on using AI to uncover security flaws prior to Mythos’s release, but is now working on an off-the-shelf version of a product it can roll out more widely, one of the people said. (Claudia Cohen and Benoit Berthelot / Bloomberg)
Related: Semafor, Politico, PYMNTS, Reuters, Nikkei Asia, nltimes.nl
German and US authorities arrested Owe Martin Andresen, the alleged administrator behind Dream Market, a popular dark web forum that shut down in 2019.
An indictment unsealed this week by the DOJ accused Andresen of being the main administrator of Dream Market. The Justice Department did not respond to requests for comment about whether it will ask for him to be extradited from Germany, where he also faces charges.
US Attorney Theodore Hertzberg said Andresen “will be prosecuted in both Germany and the United States as a result of his actions.”
“Andresen allegedly channeled commissions earned from selling illegal drugs, stolen personally identifiable information, counterfeit identification documents, and other items through cryptocurrency wallets and even converted his ill-gotten gains into gold bars,” Hertzberg said.
Court documents said Dream Market was launched in 2013 by Andresen and others before becoming one of the biggest criminal marketplaces online. At its peak, the site had more than 100,000 listings, and prosecutors said the site enabled the sale of 90 kilograms of heroin, 450 kilograms of cocaine, 25 kilograms of crack cocaine, 36 kilograms of fentanyl, and other drugs. (Jonathan Greig / The Record)
Related: Justice Department, DEA, Bleeping Computer, RegTechTimes, 11Alive, WSB, AMB Crypto, Bleeping Computer
French authorities are examining whether a foreign interference campaign aimed at a hard-left party ahead of March's municipal elections was carried out at least in part by an obscure Israeli firm called BlackCore, according to three sources familiar with the matter.
French intelligence agencies are now investigating who may have commissioned the alleged BlackCore campaign to smear three France Unbowed candidates in a campaign that included deceptive websites and social media accounts alleging criminal behavior, as well as disparaging digital ads, two of the sources said.
BlackCore has described itself on its website and LinkedIn page as "an elite influence, cyber, and technology company built for the modern era of information warfare." It said it provided governments and political campaigns with "cutting-edge strategies, advanced tools, and robust security to shape narratives."
The operation targeted Marseille mayoral candidate Sébastien Delogu, Toulouse contender François Piquemal, and their Roubaix counterpart David Guiraud, according to French authorities and the candidates themselves.
Its broad outlines were first exposed, opens new tab by the newspaper Le Monde in March, when Viginum revealed a "foreign digital interference" scheme with "limited" reach targeting a "French political party" and its candidates in Marseille, Toulouse, and Roubaix.
Satirical and investigative news outlet Le Canard Enchaine later reported that authorities suspected an Israeli firm, but did not name it. (Gabriel Stargardter and Raphael Satter / Reuters)
Related: The Arab Weekly
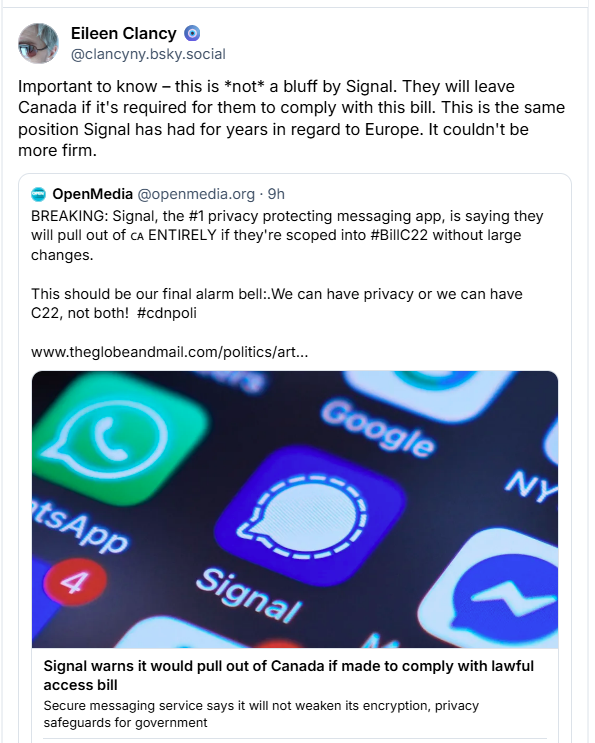
Secure messaging service Signal, which uses end-to-end encryption, is warning that it would withdraw from Canada if asked to compromise its users’ privacy under Bill C-22, Ottawa’s proposed lawful access legislation.
Udbhav Tiwari, Signal's vice-president of strategy and global affairs, said the company has deep concerns about measures in the bill, including its potential to introduce security vulnerabilities.
Tiwari said that Signal “would rather pull out of the country than be compelled to compromise on the privacy promises we have made to our users.”
He expressed fears that Bill C-22, which is currently being scrutinized by the Commons committee, could threaten encryption.
Tiwari also warned that changes to systems required under the bill could make private messaging services a potential target for cyberattacks. (Marie Woolf / The Globe and Mail)
Related: Lookout
The House Homeland Security Committee is digging into Anthropic’s AI model Mythos in a series of briefings and hearings, as questions proliferate on whether and how the federal government will make use of the technology touted for its ability to uncover cyber vulnerabilities autonomously.
Wednesday brought a closed-door briefing for the House Homeland Security Committee from Anthropic. The chairman of the panel’s cybersecurity subcommittee said he is planning to hold a hearing on the topic. And committee Democrats are requesting a classified briefing with Anthropic.
A committee aide who attended the briefing said it included a live demonstration of Mythos, “allowing members to see firsthand how advanced AI can identify and reason through software vulnerabilities. What we saw reinforced the urgency of ensuring that federal agencies, including our civilian cyber defenders, can responsibly access and deploy the most advanced US models to find and patch vulnerabilities before foreign adversaries or criminal actors exploit them.”
A number of key lawmakers, including top committee Democrat Bennie Thompson of Mississippi and GOP cyber subcommittee chair Andy Ogles of Tennessee, told CyberScoop they weren’t able to attend Wednesday’s briefing. A second source who attended said it was a “productive” meeting.
“Members on both sides were focused on preserving US advantage in AI, which basically came down to preserving our edge on compute power,” the source said. “They were also asking questions about whether the federal government was using Mythos, including about where CISA is and the impact of the supply chain risk designation.”
The Hill reported that Wednesday’s briefing was led on the Anthropic side by Logan Graham, from the company’s frontier red team, and Josh Tilstra, from the firm’s national security programs and policy team. It follows another recent closed briefing with Anthropic and OpenAI for the House Homeland Security Committee. (Tim Starks / CyberScoop)
Related: The Hill
Hospitality group BWH Hotels is informing some guests that hackers had access to reservation data for more than six months.
BWH Hotels operates more than 4,000 hotels worldwide, including brands such as WorldHotels, Best Western Hotels & Resorts, and Sure Hotels.
Emails sent to customers affected by the data breach reveal that the intrusion was discovered on April 22, and an investigation showed that threat actors had access since October 14, 2025.
The company said the attackers gained access to a web application housing some guest reservation data, including names, email addresses, phone numbers, and reservation details.
“Importantly, payment and other financial information was not stored in the affected system and therefore was not accessed,” BWH Hotels stated. (Eduard Kovacs / Security Week)
Related: r/bestwestern, SC Media, TechRadar, Security Affairs
Symantec's Threat Hunting Team reports that the Iran-linked hacking group MuddyWater (a.k.a. Seedworm, Static Kitten) launched a broad cyber-espionage campaign targeting at least nine high-profile organizations across multiple sectors and countries, including a major South Korean electronics manufacturer, government agencies, an international airport in the Middle East, industrial manufacturers in Asia, and educational institutions.
They say the threat actor “spent a week inside the network of a major South Korean electronics manufacturer in February 2026.”
The researchers believe the attacker was intelligence-driven, focusing on industrial and intellectual property theft, government espionage, and access to downstream customers or corporate networks. (Bill Toulas / Bleeping Computer)
Related: Symantec
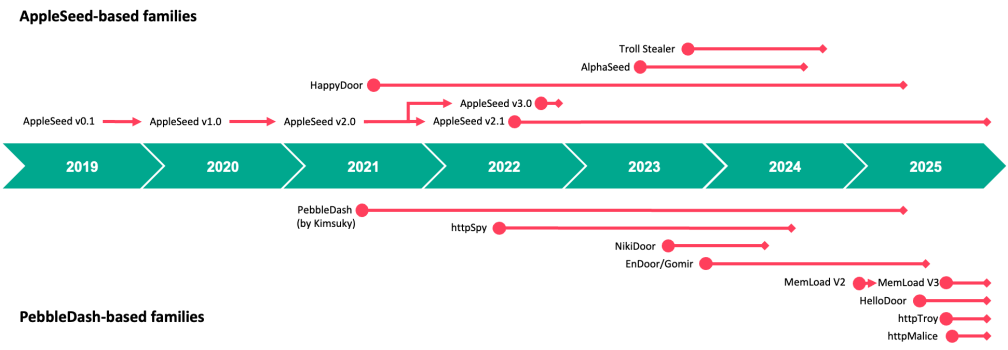
Researchers at Kaspersky report that a North Korea-linked hacking group known as Kimsuky (aka APT43, Ruby Sleet, Black Banshee, Sparkling Pisces, Velvet Chollima, and Springtail) is leveraging artificial intelligence (AI) technology to develop malicious software targeting the South Korean government's electronic authentication system.
Kaspersky said its researchers discovered that "HelloDoor," a backdoor malware program first identified last August, was linked to the North Korean hacking group Kimsuky.
"We found comments in the code that appear to have been generated by a large language model (LLM) service rather than a human developer. This is based on traces that include emojis used for logging debugging messages," the report said.
Kimsuky's arsenal includes proprietary malware such as PebbleDash, BabyShark, AppleSeed, and RandomQuery, as well as open-source RATs like xRAT, XenoRAT, and TutRAT. This blog post examines the evolving PebbleDash-based malware (referred to as the PebbleDash cluster) and its connections to the AppleSeed-based malware (referred to as the AppleSeed cluster).
Since last year, Kimsuky has been using a feature called "Visual Studio Code Remote Tunneling" instead of deploying malware directly to establish covert remote access to victims' devices, according to the report.
The report noted that these advancements pose greater threats, particularly to South Korean government institutions, which have been the primary targets of the hacking group. (Yohnap News and Securelist)
Related: ChosunBiz
XBOW researcher Federico Kirschbaum discovered that a critical vulnerability affecting certain configurations of the Exim open-source mail transfer agent could be exploited by an unauthenticated remote attacker to execute arbitrary code.
Identified as CVE-2026-45185, the security issue impacts some Exim versions before 4.99.3 that use the default GNU Transport Layer Security (GnuTLS) library for secure communication. It is a user-after-free (UAF) flaw triggered during the TLS shutdown while handling BDAT chunked SMTP traffic.
Exim frees a TLS transfer buffer but later continues using stale callback references that can write data into the freed memory region, which can lead to unauthenticated remote code execution (RCE).
Exim is a widely deployed open-source mail transfer agent (MTA) used to send, receive, and route email on Linux and Unix servers. It is used on Linux servers, in shared hosting environments, enterprise mail systems, and on Debian- and Ubuntu-based distributions, where it has historically been the default mail server.
Attackers exploiting the vulnerability could execute commands on the server as well as access Exim data and emails, and potentially pivot further into the environment depending on server permissions and configuration.
XBOW reported the vulnerability to the Exim maintainers on May 1st and received an acknowledgment on May 5th. Impacted Linux distributions were notified three days later.
A fix for CVE-2026-45185 was released in Exim version 4.99.3. (Bill Toulas / Bleeping Computer)
Related: XBOW, Cyber Security News
The number of reported technology-based crimes in Hong Kong dipped over the past year, but financial losses from hacking more than doubled to HK$62.6 million (US$8 million), prompting police to urge companies to bolster their cybersecurity checks.
Carmen Leung Oi-lam, senior superintendent of the force’s cybersecurity and technology crime bureau, attributed the surge in money lost, despite the overall drop in technology cases, to several high-value cyberattacks on financial institutions and cryptocurrency platforms.
“Even though [hacking and ransomware] cases may seem to only take up 0.3 percent of all technology crime, each case can cause a serious impact on the organizations affected,” Leung warned.
Police recorded 31,571 technology crime cases in 2025, a category covering a range of online crimes such as scams and hacking. The figure represented a 6.9 percent drop from 33,903 cases in 2024.
Among last year’s cases were 52 instances of hacking and 43 reports of ransomware, with reports of both crimes decreasing from 2024.
But police figures showed that financial losses from hacking had more than doubled from HK$25.5 million in 2024 to HK$62.6 million last year.
Total losses from all technology crimes in 2025 stood at HK$6.32 billion, which was 23.2 percent higher than HK$5.13 billion the year before. (Jess Ma / South China Morning Post)
Related: Maeil Business, DimSum Daily
Best Thing of the Day: Think of Humanity First
Pope Leo XIV is expected to sign his first encyclical as soon as Friday, positioning artificial intelligence as the defining moral and labor challenge of a new industrial revolution, an appeal to place human dignity, labor rights, and ethics at the center of the AI race.
Worst Thing of the Day: Turning Respected Brands Into Tech Astroturf Boosters
Meta and Google enlisted trusted children's brands such as Sesame Street, Girl Scouts, and Highlights magazine to teach kids to use technology in moderation - even as the companies designed apps that made it difficult for those same young users to unplug, public statements and internal documents show.
Closing Thought