US taps Microsoft, Google, xAI for pre-release AI testing as threat worries grow
FTC to ban Kochava from selling location data, State officials urge AI companies to include them in early-access testing, CISA wants CI firms to plan for essential service disconnection, DAEMON Tools software delivered backdoor to thousands, Breach forced Coupang to lose money, much more


Don't miss my latest CSO piece on how enterprise AI systems can be corrupted through data poisoned by accident, adversaries, or bad hygiene, altering those systems' understanding of reality itself.
Plus, don't miss my other latest CSO piece on CISA's new CI Fortify initiative that aims to help critical infrastructure providers maintain resiliency even when they are disconnected from essential services.
Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
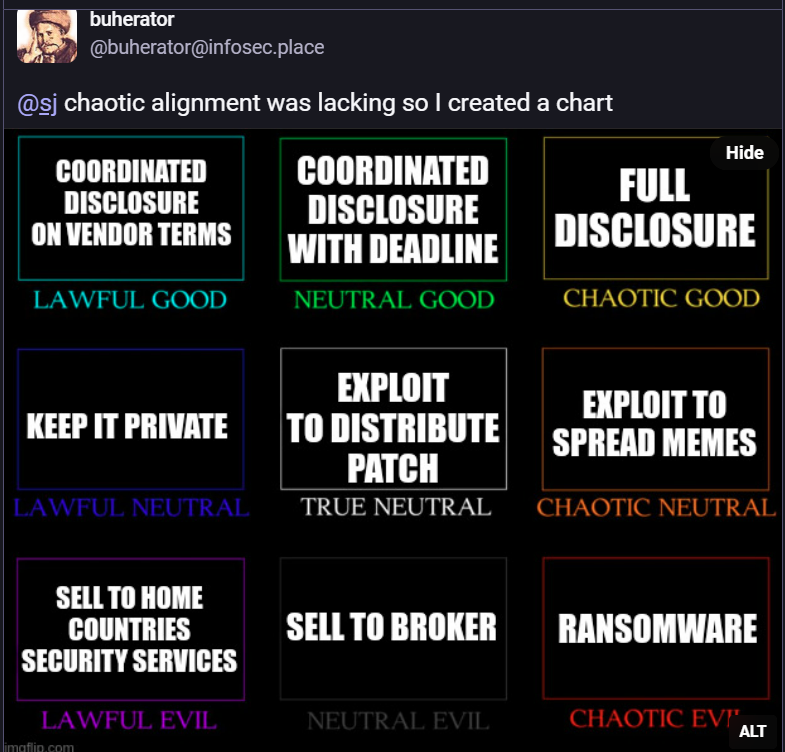
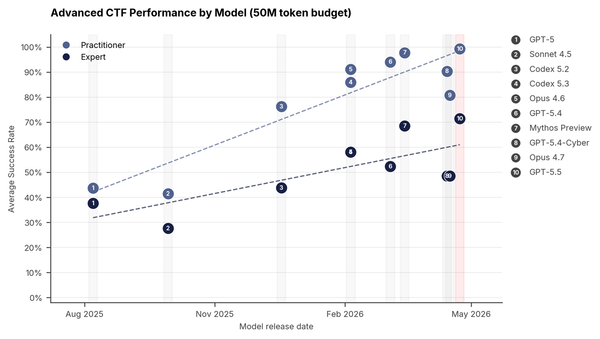
The Center for AI Standards and Innovation (CAISI) at the Department of Commerce said that Microsoft, Google, and Elon Musk’s xAI agreed to give the US government early access to new artificial intelligence models for national security testing, as US officials grow alarmed by the hacking capabilities of Anthropic’s newly unveiled Mythos.
CAISI said that the agreement would allow it to evaluate the models before deployment and conduct research to assess their capabilities and security risks. The agreement fulfills a pledge the Trump administration made in July 2025 to partner that the agreement would allow it to evaluate the models before deployment and conduct research to assess their capabilities and security risks.
Microsoft will work with US government scientists to test AI systems “in ways that probe unexpected behaviors,” the company said in a statement. Together they will develop shared datasets and workflows for testing the company’s models, the company said. Microsoft signed a similar agreement with the UK’s AI Security Institute, according to the statement.
The move builds on previous agreements with OpenAI and Anthropic, established in 2024 under the Biden administration when CAISI was known as the USD Artificial Intelligence Safety Institute. Under former President Joe Biden, the institute focused on developing AI tests, definitions, and voluntary safety standards.
It was led by Biden tech adviser Elizabeth Kelly, who has since joined Anthropic, according to her LinkedIn profile. CAISI, which serves as the government's main hub for AI model testing, said it had already completed more than 40 evaluations, including on cutting-edge models not yet available to the public. (Courtney Rozen and Aditya Soni / Reuters)
Related: NIST, NextGov/FCW, Techzine, Silicon Angle, Politico, BBC News, The Guardian, Microsoft, Washington Post, CNBC, Wall Street Journal, The Decoder
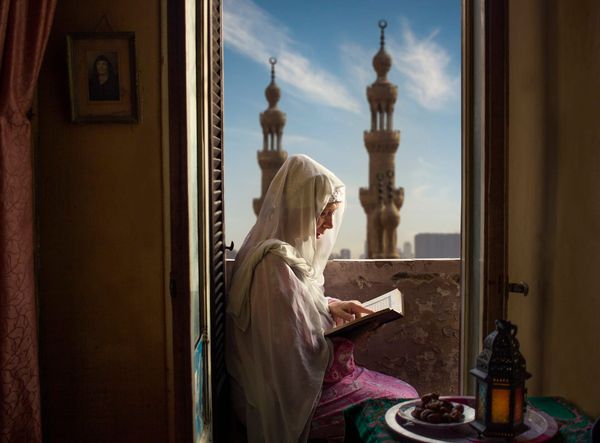
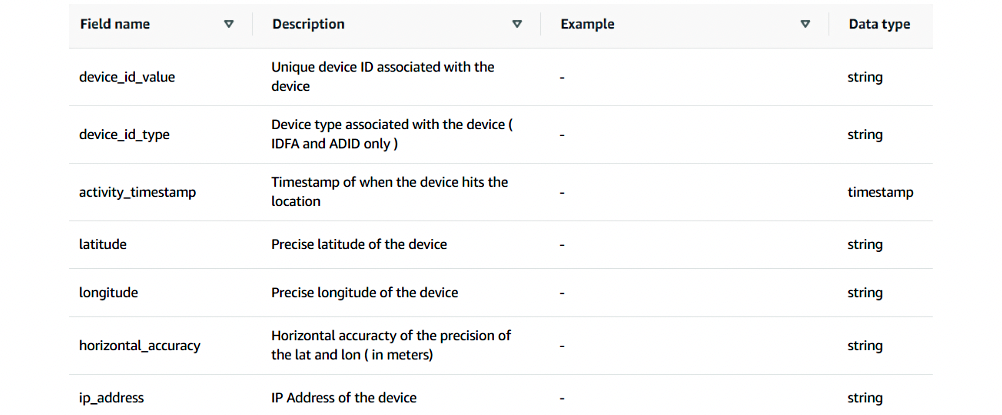
The Federal Trade Commission (FTC) will ban data broker Kochava and its subsidiary Collective Data Solutions (CDS) from selling location data without consumers' explicit consent to settle charges brought nearly four years ago.
The FTC sued Idaho-based Kochava in August 2022, alleging it collected and sold precise geolocation data from hundreds of millions of mobile devices. This information allowed Kochava's clients to track the mobile users' movements to and from sensitive locations, including mental health and addiction recovery facilities, reproductive health clinics, places of worship, and shelters for the homeless and domestic violence survivors.
According to the complaint, the company provided clients who paid a $25,000 subscription fee with access to this data through a user-friendly data feed via the Amazon Web Services (AWS) Marketplace, claiming it delivered "rich geo data spanning billions of devices worldwide."
Kochava also claimed that its location data feed "delivers raw latitude/longitude data with volumes around 94B+ geo transactions per month, 125 million monthly active users, and 35 million daily active users, on average observing more than 90 daily transactions per device."
The Commission said at the time that the affected consumers were unaware of and had not consented to the data sharing, leaving them with no means to avoid resulting harms, including stalking, discrimination, and physical violence.
Under the proposed order filed in the US District Court for the District of Idaho, Kochava and its subsidiary (which has since taken over Kochava's data broker business) will be prohibited from selling, licensing, transferring, or disclosing precise location data unless they have affirmative express consent, and the data is used to provide a service that the consumers directly requested. (Sergiu Gatlan / Bleeping Computer)
Related: FTC, FTC, BankInfoSecurity, The Record, Digiday, MediaPost, PPC Land, Cyber Insider
Senior security officials from more than a dozen states are urging artificial-intelligence companies to include them in frontier model testing, arguing that developers currently favor Washington and large technology firms.
In a letter to the chief executives of AI companies OpenAI and Anthropic, as well as Microsoft and Google, a group of state chief information security officers, homeland security advisers, and tech officials said states remain excluded from early-access programs.
“While we applaud the launch of new cyber defense projects, we are deeply concerned by the current framing that prioritizes federal partners and private-sector tech giants while largely excluding the state and local entities responsible for delivering and protecting many of the nation’s most essential services,” the letter said.
Signatories to the letter include senior security officials from Arizona, Georgia, Hawaii, Indiana, Kansas, Maine, Maryland, Missouri, Montana, Nevada, New Hampshire, New York, North Carolina, and Wisconsin. (James Rundle / Wall Street Journal)
In an initiative called CI Fortify, the Cybersecurity and Infrastructure Security Agency is urging critical infrastructure owners and operators to plan for delivering essential services under emergency conditions – potentially for months at a time.
The agency is now working with the private sector to protect operational technology – the systems that control the heavy machinery and equipment that powers most critical infrastructure – from attacks that enter through business IT systems or third-party vendor products.
The initiative will include CISA conducting targeted technical assessments of critical infrastructure entities and aims to create plans that “allow for safe operations for weeks to months while isolated” from IT networks and third-party tools, according to the agency’s website.
Nick Andersen, CISA’s acting director, told reporters that the goal is “service delivery [that] can still reach critical infrastructure after the asset owner has disconnected with IT and OT, disconnected from third-party vendors and service provider connections, and disconnected from third-party telecommunications equipment.” (Derek B. Johnson / CyberScoop)
Related: CISA, CSO, Security Week, Bank Info Security, Federal News Network, MeriTalk, NextGov/FCW, Industrial Cyber
Researchers at Kaspersky report that hackers trojanized installers for the DAEMON Tools software and, since April 8, delivered a backdoor to thousands of systems that downloaded the product from the official website.
The supply-chain attack led to thousands of infections in more than 100 countries. However, second-stage payloads were deployed only to a dozen machines, indicating a targeted attack aimed at high-value targets.
Among the victims receiving next-stage payloads are retail, scientific, government, and manufacturing organizations in Russia, Belarus, and Thailand.
Kaspersky notes that the attack is ongoing and that trojanized software includes DAEMON Tools versions from 12.5.0.2421 through 12.5.0.2434, specifically the DTHelper.exe, DiscSoftBusServiceLite.exe, and DTShellHlp.exe binaries.
In at least one case targeting a Russian educational institute, Kaspersky observed the deployment of a more advanced malware strain dubbed QUIC RAT, which supports multiple communication protocols and can inject malicious code into legitimate processes. (Bill Toulas / Bleeping Computer)
Related: Securelist, Kaspersky, Ars Technica, TechCrunch, Cyber Security News, Security Week, Neowin, Techzine, r/programming, The Record, TechRadar
US-listed e-commerce giant Coupang said it swung to a net loss in the first quarter amid fallout from a massive customer data breach in South Korea.
The company posted a net deficit of $266 million in the January-March period, compared with a net profit of $114 million a year earlier, Coupang said in a press release.
Coupang also turned to an operating loss of $242 million in the first quarter from a net profit of $154 million a year ago, while sales rose 8 percent on-year to $8.5 billion.
Coupang Korea, which generates more than 90 percent of the group's total revenue, has faced strong public backlash following the disclosure of a data breach in November 2025 involving some 33.6 million customers. (Yohnap News)
Related: Bloomberg, The Asia Business Daily, Korea Joongang Daily, Seoul Economic Daily, The Investor, The Korea Bizwire, The Korea Times, The Chosun Daily, Pulse
ShinyHunters, the hacking gang behind a breach at education technology giant Instructure, claims to have stolen 280 million records tied to students and staff from 8,809 colleges, school districts, and online education platforms.
The threat actors have now published a list of 8,809 school districts, universities, and educational platforms whose Canvas instances were allegedly impacted by the attack, sharing record counts per institution with BleepingComputer.
The threat actor claims the data was stolen using Canvas data export features, including DAP queries, provisioning reports, and user APIs, and that they harvested hundreds of gigabytes of user records, messages, and enrollment data. (Lawrence Abrams / Bleeping Computer)
Related: Inside Higher Ed, TechCrunch, ABC.net.au, Mashable
Nearly $14 billion has been pulled from the so-called decentralized finance space, according to data firm DefiLlama, after North Korean-linked hackers stole $290mn from Aave, the largest lender in the sector, triggering an industry bailout.
That came just weeks after hackers stole $280mn from DeFi exchange Drift last month.
The episodes mark a big blow for DeFi, where automated contracts are used to replace traditional intermediaries, such as banks and brokers, and where the security of the underlying blockchains is seen as critical. It also comes as traditional financial institutions explore the adoption of blockchain technology. (Jill R Shah and Nikou Asgari / Financial Times)
Related: CoinDesk
Australia announced it is establishing a board to conduct independent reviews following major cyberattacks, joining a small number of other jurisdictions that have created similar programs.
The Cyber Incident Review Board will carry out no-fault, post-incident reviews of significant cyberattacks on the Australian government and industry, focusing on systemic lessons rather than individual or corporate culpability.
Tony Burke, the Australian home affairs and cybersecurity minister, announced seven appointments to the board, which is majority female — a rarity in a field that skews heavily male at senior levels.
Narelle Devine, the global chief information security officer at Telstra, will chair it. Other members are drawn from Boeing Australia, NBN Co, the University of New South Wales, law firm Allens, Toll Group, and SA Power Networks. (Alexander Martin / The Register)
Related: Australian Department of Home Affairs, The Cyber Express, Cyber Daily
Palo Alto Networks warned customers that a critical-severity unpatched vulnerability in the PAN-OS User-ID Authentication Portal is being exploited in attacks.
Also known as the Captive Portal, the User-ID Authentication Portal is a PAN-OS security feature that authenticates users whose identities cannot be automatically mapped by the firewall.
Tracked as CVE-2026-0300, this zero-day bug stems from a buffer overflow weakness that allows unauthenticated attackers to execute arbitrary code with root privileges on Internet-exposed PA-Series and VM-Series firewalls via specially crafted packets.
"Limited exploitation has been observed targeting Palo Alto Networks User-ID™ Authentication Portals that are exposed to untrusted IP addresses and/or the public internet," Palo Alto Networks said.
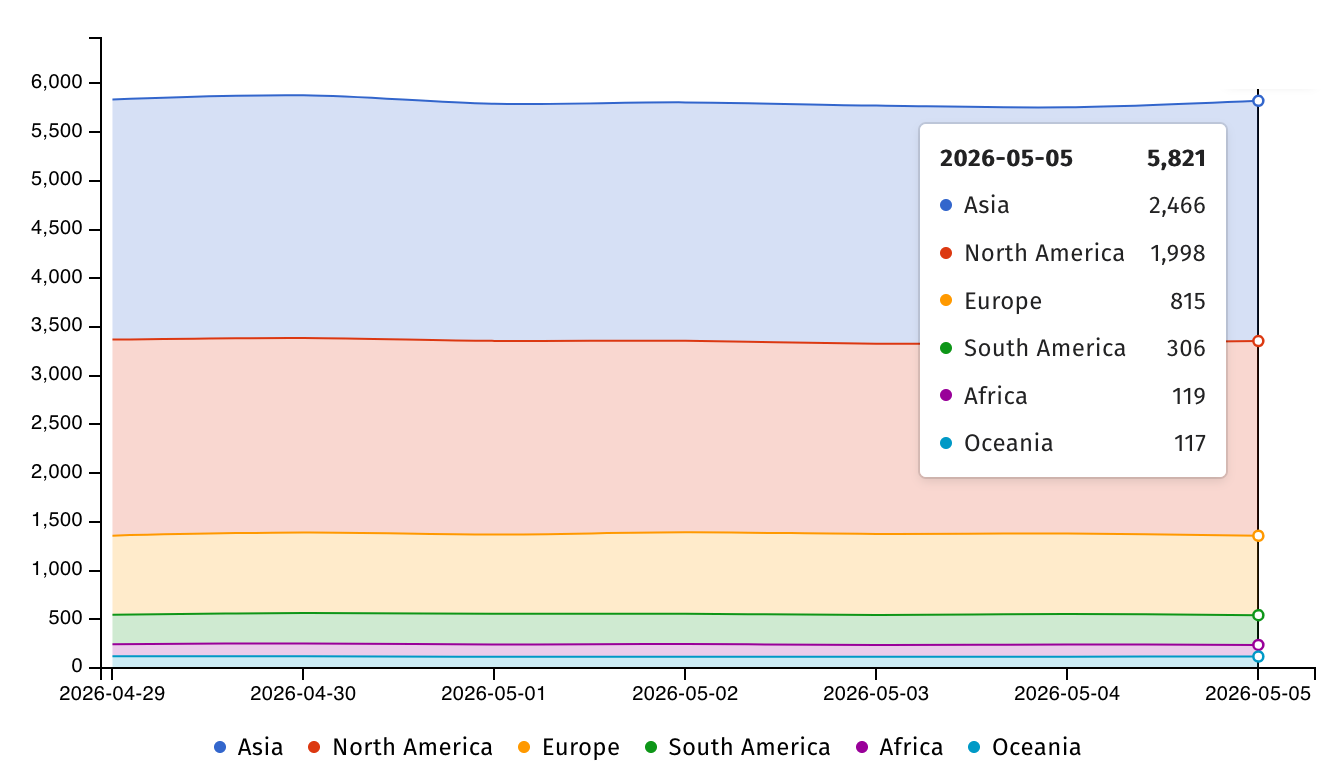
Internet threat watchdog Shadowserver is tracking over 5,800 PAN-OS VM-series firewalls exposed online, most of them in Asia (2,466) and North America (1,998). (Sergiu Gatlan / Bleeping Computer)
Related: Palo Alto Networks, Security Week, Cyber Press
A 23-year-old university student in Taiwan was arrested for interfering with the TETRA communication system used by the country's high-speed railway network (THSR).
According to local media reports, the student halted four trains for 48 minutes on April 5 by using software-defined radio (SDR) communications and handheld radios to transmit a high-priority “General Alarm” signal, triggering emergency braking procedures.
THSR is a high-speed railway network in Taiwan that runs a single 350 km (217 miles) two-way line along the western coast of the country, with trains reaching speeds of up to 300 km/h (186 mph).
Before the attack, the student, who is referred to by his surname Lin, intercepted and decoded TETRA (Trans-European Trunked Radio) radio parameters using SDR equipment he bought online, and then programmed them into handheld radios to impersonate legitimate beacons.
The police also found that a 21-year-old accomplice provided Lin with some critical THSR parameters that enabled the attack. (Bill Toulas / Bleeping Computer)
Related: The Register, SQ Magazine, Cyber Press, Newtalk
Real estate giant Cushman & Wakefield has confirmed a data breach after two cybercrime groups, ShinyHunters and Qilin, separately claimed responsibility for attacks on the company.
A spokesperson said the attack was "limited" in scope and stemmed from vishing (voice phishing), suggesting an employee was socially engineered.
The representative said, "Cushman & Wakefield recently became aware of a limited data security incident due to vishing. We have activated our response protocols, including taking steps to contain the unauthorized activity and engaging third-party expert advisors to support a comprehensive response.
"Our systems and operations continue to run normally, and we are working diligently to investigate the incident. We recognize the trust placed in us to protect sensitive data, and we take this responsibility very seriously."
Cushman & Wakefield (C&W) did not address the apparent dual targeting by both ShinyHunters, which operates a pay-or-leak model, and Qilin, currently viewed as the world's most prolific ransomware group.
There is no previously established coalition between ShinyHunters and Qilin, which suggests the two alleged attacks are separate but coincidentally timed. (Connor Jones / The Register)
Related: Cyber Daily, r/pwnhub
Researchers at ESET report that the North Korean hacker group APT37 has been delivering an Android version of a backdoor called BirdCall in a supply-chain attack through a video game platform.
While BirdCall is a known backdoor for Windows systems, APT37, also known as ScarCruft and Ricochet Chollima, has developed a variant for Android that doubles as spyware.
According to ESET, the threat actor created BirdCall for Android around October 2024 and developed at least seven versions.
The attacks that ESET observed delivered the malware through sqgame[.]net, a Chinese site hosting games for Android, iOS, and Windows. However, the researchers found that only Android and Windows are targeted by the ScarCruft attacks.
The particular platform caters to Koreans in the autonomous Yanbian region in China, which acts as a crossing point for North Korean defectors and refugees.
ScurCraft is notorious for using a broad range of custom malware, including THUMBSBD, which targets air-gapped Windows systems, the KoSpy Android malware that previously infiltrated Google Play, the M2RAT malware used in targeted espionage attacks, and the Dolphin mobile backdoor. (Bill Toulas / Bleeping Computer)
Related: We Live Security, Cyber Security News, Help Net Security, Cyber Press, The Record, Infosecurity Magazine

The ShinyHunters extortion gang stole personal information belonging to over 119,000 people after hacking the Vimeo online video platform in April, according to data breach notification service Have I Been Pwned.
The company disclosed on April 27 that customer and user data had been accessed without authorization following a recent breach at Anodot, a data anomaly detection company.
"Our initial findings suggest that the databases accessed primarily contain technical data, video titles, and metadata, and, in some cases, customer email addresses," Vimeo said.
However, the company said the attack didn't cause any disruptions and that the threat actors didn't gain access to affected individuals' credentials or financial information. Vimeo also disabled all Anodot credentials after detecting the breach and removed the Anodot integration with its systems to cut off the attackers' access. (Sergiu Gatlan / Bleeping Computer)
Related: HaveIBeenPwned, Computing, The Register
A malicious version of the PyTorch Lightning package published on the Python Package Index (PyPI) delivers a credential-stealing payload targeting browsers, environment files, and cloud services.
The developer disclosed the supply-chain attack on April 30, saying that version 2.6.3 of the package included a hidden execution chain that downloads and executes a JavaScript payload.
PyTorch Lightning is a deep learning framework used for pretraining and fine-tuning AI models. It is a popular package, amassing more than 11 million downloads last month.
The security advisory from the maintainer notes that the malicious execution chain triggers automatically on import and silently spawns a background process.
In an X post over the weekend, Microsoft Threat Intelligence says that Defender detected and prevented the malicious routine in customer environments, and notified the package maintainer. (Bill Toulas / Bleeping Computer)
Related: GitHub, Security Affairs
A group of civil society organizations and tech companies has banded together to call on UK politicians to rethink their age-verification plans.
The entities, including Mozilla, Tor, and the Open Rights Group, have warned that the measures will force all users to prove their age and undermine the open internet.
The joint statement, led by the Open Rights Group, Mozilla, Tor, and other organizations such as ExpressVPN, IPVanish, Tuta, Proton, and the Electronic Frontier Foundation, opposes the idea of putting online services behind age gates. They warn that it could affect social media, video games, VPNs, livestreams, feeds, and even static websites.
The open letter warns that now that the Children’s Wellbeing and Schools Bill has been passed, ministers are looking at which platforms and specific features should require age verification. The signatories say that this will result in all UK internet users having to verify their age, not just children, which will result in the creation of large databases full of sensitive ID data.
Instead of blanket bans, the signatories are urging the government to adopt “thoughtful” policy interventions that address the root causes of online harm, such as the business models of large platforms built on extensive data collection, behavioral targeting, and engagement-maximizing design. (Paul Hill / Neowin)
Related: Open Rights Group
Google overhauls its Android and Chrome vulnerability rewards programs, offering bounties of up to, for the most difficult exploits while scaling back payouts for flaws that artificial intelligence (AI) has made easier to find.
The top reward of $1.5 million is reserved for zero-click Pixel Titan M2 security chip full-chain exploits with persistence, the most technically demanding attack scenario in the program, while the same exploits, but without persistence, are also eligible for up to $750,000.
On the Google Chrome side, full-chain browser process exploits on up-to-date operating systems and hardware now come with rewards of up to $250,000, plus an additional $250,128 bonus for successfully exploiting MiraclePtr-protected memory allocations. (Sergiu Gatlan / Bleeping Computer)
Related: Google, Forbes, Cybersecurity Insiders, Hot Hardware
Best Thing of the Day: Help Those Pushed Out by AI
Lord Gus O’Donnell, Britain’s former top civil servant, argues that people and businesses that benefit from AI will have to “compensate the losers” by funding retraining through taxes.
Worst Thing of the Day: That's a Golden Retriever, Not a Burglar
AI descriptions from security cameras, designed to give customers more detail than generic motion alerts, are mistaking brake lights for house fires and humans for bears.
Bonus Worst Thing of the Day: No More Encrypted Messages for You
Instagram will remove end-to-end encryption for direct messages between users on May 8, 2026.
Closing Thought