Russia’s hidden hacker academy exposed in massive document leak
US-China weigh AI risk talks, Wiles says Trump won’t pick AI winners, Vibe-coded apps lack security, GothFerrari fraudster gets 78 months, MuddyWater masks ops as Chaos ransomware, Phishing hits ManageWP via Google-sponsored search ads, Japan urges CI to do cyber better, much more


Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
According to 2,000 internal documents, a secret faculty inside a well-known Moscow-based university, Bauman Moscow State University, known simply as Department 4, or “Special Training," quietly prepares a select group of students for careers in the GRU – Russia’s military intelligence directorate, whose operatives have hacked western parliaments, poisoned dissidents on foreign soil, and interfered in elections across Europe and the US.
The documents were obtained by a consortium of journalists from six outlets: the Guardian, Der Spiegel, Le Monde, the Insider, Delfi, and VSquare.
The files, covering several years of activity up to 2025, include course syllabuses, exam records, staff contracts, and the career assignments of individual graduates, tracing their path from classroom exercises in hacking and disinformation to postings in some of the most notorious cyber-units in the Russian military intelligence apparatus.
Embedded within the university’s military training center, Department 4 is divided into three specialist streams, the documents suggest. The most prominent, bearing the code 093400, is titled the “Special Reconnaissance Service”.
The documents indicate that the GRU exerts direct control over the recruitment and grading process – sending its own officers to conduct exams, approve candidates, and oversee placements. The picture that emerges is of a program where the distinction between professor and handler and between teaching and recruitment is blurred.
The department is led by Lieutenant Colonel Kirill Stupakov, a signals intelligence officer who, according to the documents, signed a three-year contract in 2022 with GRU Unit 45807, one of the agency’s key units. It is not clear if he is still in active service.
At Bauman, Stupakov’s subjects include training students to master electronic eavesdropping and covert surveillance. PowerPoint slides, apparently designed to accompany his lectures and viewed by the consortium, amount to a catalog of deception: a smoke detector that is in fact a camera, a device that sits undetected between a keyboard and a computer logging every keystroke, a monitor cable that is also a silent screenshot machine storing its captures on a hidden flash drive.
Among the core courses is one titled “Defence against technical reconnaissance”. Over 144 hours across two semesters, students are taught the full toolkit of modern hacking, including password attacks, software vulnerabilities and so called trojans – malicious programs disguised as legitimate software that can grant unauthorised access to a system.
To pass the course, students are required to carry out “practical penetration tests”, while one module is devoted entirely to computer viruses. As part of the assessment, they must develop one themselves. (Pjotr Sauer and Shaun Walker / The Guardian)
Related: Le Monde, Der Spiegel, Der Spiegel, The Insider, VSquare
Washington and Beijing are weighing the launch of official discussions about artificial intelligence, said people familiar with the matter, as their AI competition threatens to become the arms race of the digital era.
What both sides have in mind, the people said, is a recurring set of conversations that could address the risks posed by AI models behaving unexpectedly, autonomous military systems, or attacks by nonstate actors using powerful open-source tools.
Treasury Secretary Scott Bessent is leading the American side on the AI track, said people familiar with the US position. The administration is waiting for Beijing to designate its counterpart, the people said. So far, Chinese vice finance minister Liao Min has been involved in discussions with Washington about setting up such a dialogue, people close to Beijing said.
Outside the administration, some private-sector analysts are already debating what such discussions might ultimately produce and whether more concrete crisis-management mechanisms could eventually follow, such as an AI hotline for communication between high-level leadership. The US and China already maintain a defense-telephone line and other crisis channels—though Beijing has often been reluctant to use them. (Lingling Wei / Wall Street Journal)
White House Chief of Staff Susie Wiles said the US government would refrain from choosing winners and losers in artificial intelligence, the latest signal from a top aide to President Donald Trump as his administration prepares new AI policy directives.
Wiles stated her new account on X, as questions swirl about whether the administration will seek to screen new models and if it will de-escalate its feud with Anthropic PBC.
“When it comes to AI and cyber security, President Trump and his administration are not in the business of picking winners and losers,” Wiles wrote. “This administration has one goal; ensure the best and safest tech is deployed rapidly to defeat any and all threats.”
She added that the administration “will continue to lead an America First effort that empowers America’s great innovators, not bureaucracy, to drive safe deployment of powerful technologies while keeping America safe.”
Wiles, who has taken a lead role in crafting the latest round of AI policy, offered no specifics about the scope or timing of any directive. (Josh Wingrove / Bloomberg)
Related: Startup Fortune
Security researcher Dor Zvi and his team at the cybersecurity firm he cofounded, RedAccess, analyzed thousands of vibe-coded web applications created using the AI software development tools Lovable, Replit, Base44, and Netlify and found more than 5,000 of them that had virtually no security or authentication of any kind.
Many of these web apps allowed anyone who merely found their web URL to access the apps and their data. Others had only trivial barriers to that access, such as requiring that a visitor sign in with any email address.
Around 40 percent of the apps exposed sensitive data, Zvi says, including medical information, financial data, corporate presentations, and strategy documents, as well as detailed logs of customer conversations with chatbots.
Zvi says RedAccess’s scouring for vulnerable web apps was surprisingly easy. Lovable, Replit, Base44, and Netlify all allow users to host their web apps on those AI companies' own domains, rather than the users’. So the researchers used straightforward Google and Bing searches for those AI companies' domains, combined with other search terms, to identify thousands of apps that had been vibe coded with the companies' tools.
Of the 5,000 AI-coded apps that Zvi says were left publicly accessible to anyone who typed their URLs into a browser, he found close to 2,000 that, upon closer inspection, seemed to reveal private data: Screenshots of web apps he shared with WIRED—several of which WIRED verified were still online and exposed—showed what appeared to be a hospital's work assignments with the personally identifiable information of doctors, a company's detailed ad purchasing information, what appeared to be another firm's go-to-market strategy presentation.
In the case of Lovable, Zvi says he also found numerous examples of phishing sites that impersonated major corporations, including Bank of America, Costco, FedEx, Trader Joe’s, and McDonald’s, that appeared to have been created with the AI coding tool and hosted on Lovable's domain. (Andy Greenberg / Wired)
Related: Axios
Marlon Ferro, a 20-year-old man also known as "GothFerrari," was sentenced in US federal court to 78 months in prison and was ordered to serve three years of supervised release and to pay $2.5 million in restitution for a scheme that blended online fraud with old-fashioned burglary to drain victims of over $250 million worth of crypto assets between late 2023 and early 2025.
A multi-year federal investigation found that members of the social engineering enterprise carried out a range of activities, including database hacking, target identification, fraudulent phone calls, money laundering, and residential burglary. The scheme generally targeted victims with large crypto holdings.
In February 2024, Ferro traveled to Texas and broke into a victim's home to steal a hardware wallet containing about 100 BTC worth over $5 million at the time. He also helped launder the criminal proceeds through crypto exchanges, according to the statement.
Also, in July 2024, Ferro broke into another residence in New Mexico in search of a hardware wallet. He was captured on the victim's home surveillance camera and arrested in May 2025. Authorities found him in possession of two firearms and a fake identification document.
Ferro pleaded guilty in October 2025 before Judge Colleen Kollar-Kotelly to one count of conspiracy to participate in a racketeer-influenced and corrupt organization. (Timmy Shen / The Block)
Related: Justice Department, Bleeping Computer, BeInCrypto, Channel News Asia, The Crypto Times, Databreaches.net
According to an account published by Strix, an open-source autonomous security testing project, Schemata, an AI-powered virtual training platform used in military and defense settings, exposed user records and military training materials through API endpoints that lacked meaningful authorization checks.
According to Strix, an ordinary low-privilege account was able to access data across multiple tenants, including user listings, organization records, course information, training metadata, and direct links to documents hosted on ,Schemata’s Amazon Web Services instances.
Strix said the exposed materials included a 3D virtual training course for naval maintenance personnel with documentation marked confidential and proprietary, a course containing Army field manuals on explosive ordnance handling and tactical deployment, and hundreds of user records linked to bases and training enrollments. Additionally, the exposed information included names, email addresses, enrollment details, and the military bases where US service members were stationed.
Schemata acknowledged the affected endpoints were exposed on ,May 1, after what Strix described as a 150-day disclosure process. Strix said it verified remediation before publication and published its account earlier this week, 152 days after its initial disclosure attempt. (Greg Otto / CyberScoop)
Related: Strix
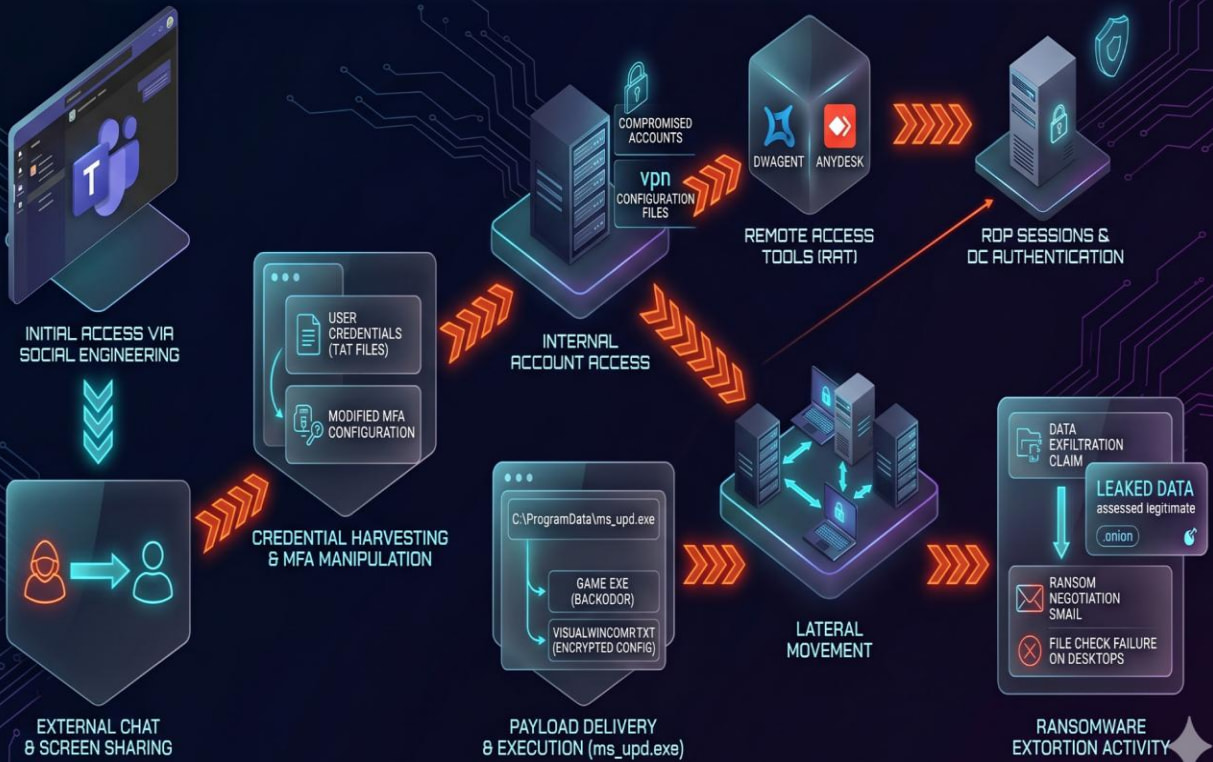
Researchers at Rapid7 report that the MuddyWater Iranian hackers disguised their operations as a Chaos ransomware attack, relying on Microsoft Teams social engineering to gain access and establish persistence.
Although the attack involved credential theft, persistence, remote access, data exfiltration, extortion emails, and an entry on the Chaos leak portal, the attackers used infrastructure and techniques associated with the MuddyWater attacks.
Rapid7 researchers believe that the ransomware component was likely used to conceal the actual cyber-espionage operation and to complicate attribution.
Despite the facade, Rapid7 has moderate confidence in attributing the incident to MuddyWater, a threat group also known as Static Kitten, Mango Sandstorm, and Seedworm.
Rapid7 notes that MuddyWater has used ransomware in the past to mask its cyber-espionage operations. In late 2025, the threat actor deployed Qilin ransomware in an attack against an Israeli organization. (Bill Toulas / Bleeping Computer)
Related: Rapid7, Computing, Security Week, Security Affairs, Infosecurity Magazine, Cyber Press
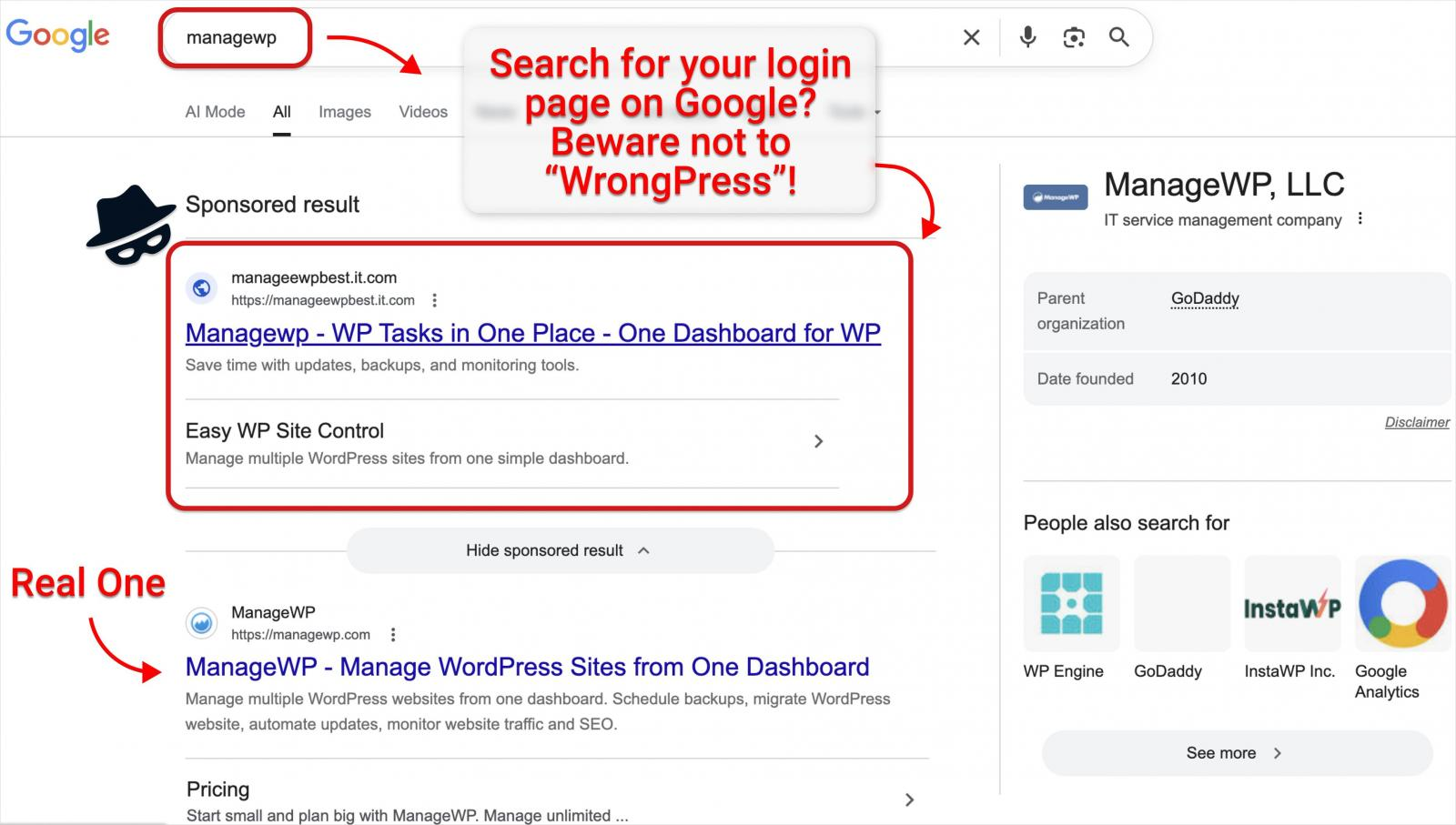
Researchers at Guardio Labs report that a phishing campaign delivered through Google-sponsored search results is targeting credentials for ManageWP, GoDaddy’s platform for managing fleets of WordPress websites.
The threat actor is using an adversary-in-the-middle (AitM) approach where the fake login page acts as a real-time proxy between the victim and the legitimate ManageWP service.
Guardio Labs warns that the fake result is displayed above the real one for the 'managewp' query, luring users who rely on Google to find the URL for logging into ManageWP.
Guardio Labs was able to infiltrate the attacker’s command-and-control (C2) infrastructure and observed a dropdown command system that enables an interactive and operator-driven phishing flow. (Bill Toulas / Bleeping Computer)
Japan's Economy, Trade and Industry Ministry has asked electric power and other infrastructure service providers to conduct emergency inspections of their information systems to counter potential cyberattacks that use Claude Mythos Preview, an artificial intelligence model released by US venture Anthropic.
Economy, Trade and Industry Minister Ryosei Akazawa met with executives from major power and energy firms, along with transmission and distribution companies and representatives from industry groups in sectors that are under the ministry’s jurisdiction: electricity, gas, petroleum, chemical, and consumer credit.
“I want you to recognize that cybersecurity is a top management priority to prevent serious incidents that could compromise public safety and security,” Akazawa said at the meeting.
In addition to inspecting information systems, Akazawa urged attendees to implement measures to ensure organization heads’ leading relevant efforts, to detect vulnerabilities in information systems and take necessary responses in a proactive manner, and to realize the transition of the systems to those that allow constant monitoring. (The Yomiuri Shimbun)
Related: Marketwatch, The Asahi Shibum
Canadian Public Safety Minister Gary Anandasangaree is facing mounting calls to amend his lawful access bill, amid concerns it will weaken digital encryption and introduce cyber vulnerabilities.
would allow police and security officials to more easily obtain Canadians’ private information and intercept communications as part of criminal and intelligence investigations.
The legislation would also require "electronic service providers" — a broad category that remains undefined but is largely assumed to include tech and telecommunication companies — to update their systems so they can seamlessly turn over information to law enforcement agencies and the Canadian Security Intelligence Service, if they have a warrant. They would also be required to retain metadata for up to one year.
Apple — which uses encryption to secure users' health data, the location of family members, messages, photos, financial data,, and more — has now publicly waded into the debate.
The company stressed it will work with law enforcement, but warned that Bill C-22 would allow the government to issue orders weakening encryption and create vulnerabilities that hackers and hostile nation states could exploit. (Catharine Tunney / CBC News)
Related: Globe and Mail, Michael Geist, Canadian Constitution Foundation, Mobile Syrup
Hungarian cops arrested a 20-year-old man in Nógrád County over an alleged swatting call that sent armed officers to a US residence nearly two years ago.
Hungary's National Bureau of Investigation (NNI) said the call was made to police in Tiverton, Rhode Island, on April 24, 2024, claiming a man had killed his family and was going to shoot his dog and himself.
The call prompted an armed response to the exact address given over the phone. However, the police realized the report was false and pertained to a fictional person after they arrived.
According to the NNI's account, the FBI had been hunting the man for two years and made a breakthrough after infiltrating the alleged swatter's Discord server, where they found a recording of him livestreaming the swatting call.
From that recording, the FBI suspected the man to be Hungarian, despite police describing him as a native English speaker. Investigators then began international cooperation in March 2026.
The FBI and NNI jointly identified the alleged swatter "through digital traces." The man admitted to the offense after police detained him last week. (Connor Jones / The Register)
Related: Police.huunauthorized
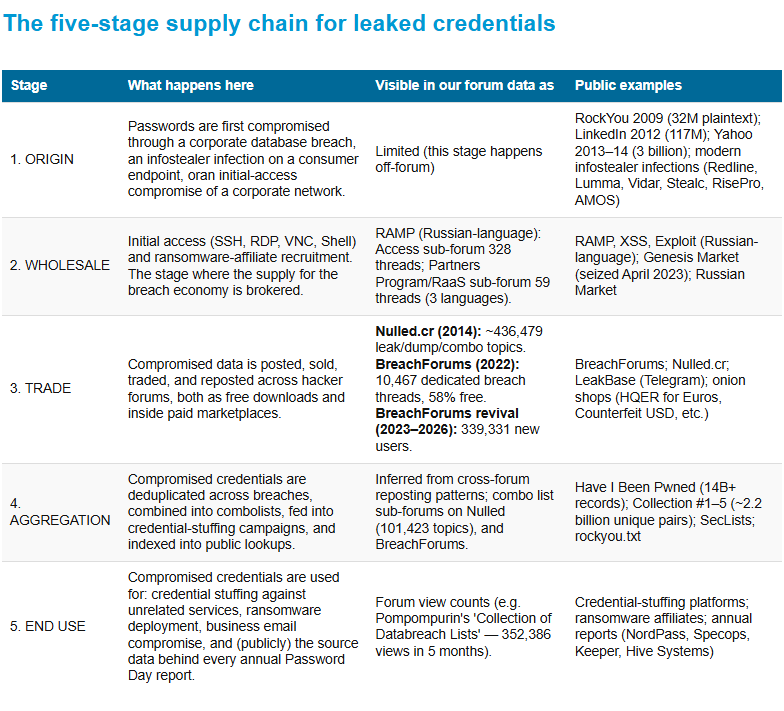
Comparitech researchers analyzed over 447,000 leaks, dumps, and breach threads across four forums, containing 1.1 million user records (from 2013 to 2026), including Nulled.cr (2013–2016), BreachForums (2022), the Russian-language ransomware forum RAMP (2021–2024), and the BreachForums revival (2023–2026) to find out how stolen passwords are accessed, traded, and aggregated before being used in cybercrime.
Among their findings: free data was posted on forums more often than paid data, forum administrators aren’t just ‘landlords’, they’re often top-volume suppliers, Indonesian and Chinese breaches attracted more views in 2022 than Western big-tech breaches, and takedowns of these forums might cause short-term delays, but they usually don’t last. (Paul Bischof / Comparitech)
Best Thing of the Day: Three Years Is Better Than Five (But Not as Good as One)
The Pentagon plans to require service members to complete cybersecurity training once every three years, a move that will scrap an annual mandate and is set to upend the Army’s recent shift to a five-year requirement.
Worst Thing of the Day: A Good Move If You Like Your AI to Be Racist
Anthropic and Elon Musk’s SpaceX said that the two entities have signed an agreement for Anthropic to use computing resources from xAI’s data center in Memphis, Tennessee.
Bonus Worst Thing of the Day: So Wrong at So Many Levels
Cybersecurity vendor Arctic Wolf has laid off 250 workers in a restructuring that it says is designed to position the company to invest more in AI through its superintelligence platform and agentic Security Operations Center (SOC).
Closing Thought