Canvas chaos: ShinyHunters breach throws schools into disarray
Firefox bug fixes soar after using Mythos, Virginia man found guilty of destroying government databases, OpenAI rolls out GPT 5.5 to vetted cyber defenders, PCPJack steals cloud creds while removing TeamPCP access, Ivanti urges patches for Endpoint Manager Mobile (EPMM) zero day bug, much more


Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
The widely used digital learning platform Canvas was put into “maintenance mode” on Thursday after its maker, the education tech giant Instructure, suffered a data breach and faced an extortion attempt by attackers using the recognizable moniker "ShinyHunters."
Though the hackers have been advertising the breach and attempting to extract a ransom payment from Instructure since May 1, the situation took on additional immediacy for regular people across the US and beyond on Thursday because the Canvas downtime caused chaos at schools, including those in the midst of finals and end-of-year assignments.
Universities like Harvard, Columbia, Rutgers, and Georgetown sent alerts to students about the situation in recent days; other institutions, including school districts in at least a dozen states, also appear to have been affected. In a list published by the hackers behind the attack on their ransom-focused dark web site, they claim the breach affected more than 8,800 schools. The exact scale and reach of the breach is currently unclear, though. And the fact that Canvas was down throughout Thursday afternoon and evening further complicated the picture.
In a running incident update log that began on May 1, Steve Proud, Instructure's chief information security officer, said that the company had “recently experienced a cybersecurity incident perpetrated by a criminal threat actor.” He added on May 2 that “the information involved” for “users at affected institutions” included names, email addresses, student ID numbers, and messages exchanged by users on the platform.
The situation was ultimately marked as “Resolved” on Wednesday, with Proud writing that “Canvas is fully operational, and we are not seeing any ongoing unauthorized activity.” At midday on Thursday, though, the Instructure status page registered an “issue” where “some users are having difficulties logging into Student ePortfolios.” Within a few hours, the company had added another status update: “Instructure has placed Canvas, Canvas Beta, and Canvas Test in maintenance mode.” Late Thursday evening, the company said that Canvas was available again “for most users.”
The chaos appears to have been caused when the hackers apparently compromised Instructure for a second time.
A message was published by the cybercrime group ShinyHunters on the Canvas login pages of three separate schools. A review of the defaced portals shows that the hackers injected an HTML file that altered the login screens to display their message.
The message says the hackers will publish the stolen data on May 12 if the company does not “negotiate a settlement.” (Lily Hay Newman and Andy Greenberg / Wired and Lorenzo Franceschi-Bicchierai and Zack Whittaker / TechCrunch)
Related: Bleeping Computer, Dutch News, Krebs on Security, CNN, DNYUZ, The Verge, CyberInsider, The Harvard Crimson, TechRadar, eSecurity Planet, WTTG-TV, KFMB, nltimes.nl, Inside Higher Ed, PCMag, CBS News, ABC7, The Cornell Daily Sun, Reuters, New York Times, Memeburn, Hackread, NBC Los Angeles, EdScoop, San Francisco Chronicle, Fox News, KEYT-TV, The Georgetown Voice, WJBK-TV, Wall Street Journal, Information Age, OX 4 News Dallas-Fort Worth, Collegiate Times, r/cybersecurity, Artthreat, Indiana Daily Student, OU Daily, The Brown Daily Herald, KCUR, WBAY, WXII, KSBW, WTKR, WFTV, The Stanford Daily, RACGP.org, NL Times, Techzine, The International News, The Conversation, NBC San Diego, The Guardsman, News.az, 12News, SuperTalk, KOIN, Economic Times, Daily Jang, The University News, KLTV, DeSoto County News, The UWM Post, CBS8, Politico, The Princetonian, WRAL, ClickOnDetroit, The Next Web
Security researchers for Mozilla’s Firefox browser are providing a closer look at what Mythos's bug-sniffing process looks like in practice, and what Mythos’s powers mean for software security at large.
Mozilla said Mythos has unearthed a wealth of high-severity bugs, including some that had lain dormant in the code for more than a decade.
That’s a significant improvement from what AI security tools were capable of even six months ago. Until now, AI bug-finding tools have come with severe drawbacks, often inundating security teams with low-quality reports and false positives. But Mozilla’s researchers say the latest generation of tools has turned a corner, particularly now that agentic systems can assess their own work and filter out bad results.
“It is difficult to overstate how much this dynamic changed for us over a few short months,” the researchers wrote. “First, the models got a lot more capable. Second, we dramatically improved our techniques for harnessing these models.”
The results are striking: In April 2026, Firefox shipped 423 bug fixes, compared to just 31 exactly a year earlier. The researchers have also published details on 12 of the bugs, which range from a pair of unusual sandbox vulnerabilities to a 15-year-old error in how the browser parses an HTML element. (Russell Brandom / TechCrunch)
Related: Mozilla Hacks, Ars Technica, The Decoder, Implicator.ai, Cyber Security News, The Register, Digit, Simon Willison's Weblog, Help Net Security

A Virginia man, Sohaib Akhter, was found guilty of conspiring to destroy dozens of government databases after getting fired from his job as a federal contractor.
In 2016, Sohaib Akhter and his twin brother and co-defendant Muneeb Akhter were also sentenced to several years in prison after pleading guilty to accessing US State Department systems without authorization and stealing the personal information of dozens of co-workers and a federal law enforcement agent who was investigating their crimes.
After serving their sentences, the two brothers were rehired as government contractors by a company that worked with more than 45 federal agencies and hosted government data on servers in Ashburn.
"When the company discovered Sohaib Akhter's felony conviction, it terminated both brothers' employment during an online remote meeting on Feb. 18, 2025," the Justice Department said. "Immediately after being fired during this meeting, the brothers sought to harm their employer and its US government customers by accessing computers without authorization, write-protecting databases, deleting databases, and destroying evidence of their unlawful activities."
In November 2025, Muneeb and Sohaib were again charged with destruction of records, aggravated identity theft, computer fraud, and theft of government information.
Sohaib Akhter will be sentenced on September 9, 2026, and is facing a maximum penalty of 21 years in prison.
His brother, Muneeb Akhter, also faces a maximum of 45 years for two counts of computer fraud, conspiring to commit computer fraud and destroy records, two counts of aggravated identity theft, and theft of US government records. (Sergiu Gatlan / Bleeping Computer)
Related: Justice Department, The Alexandria Brief
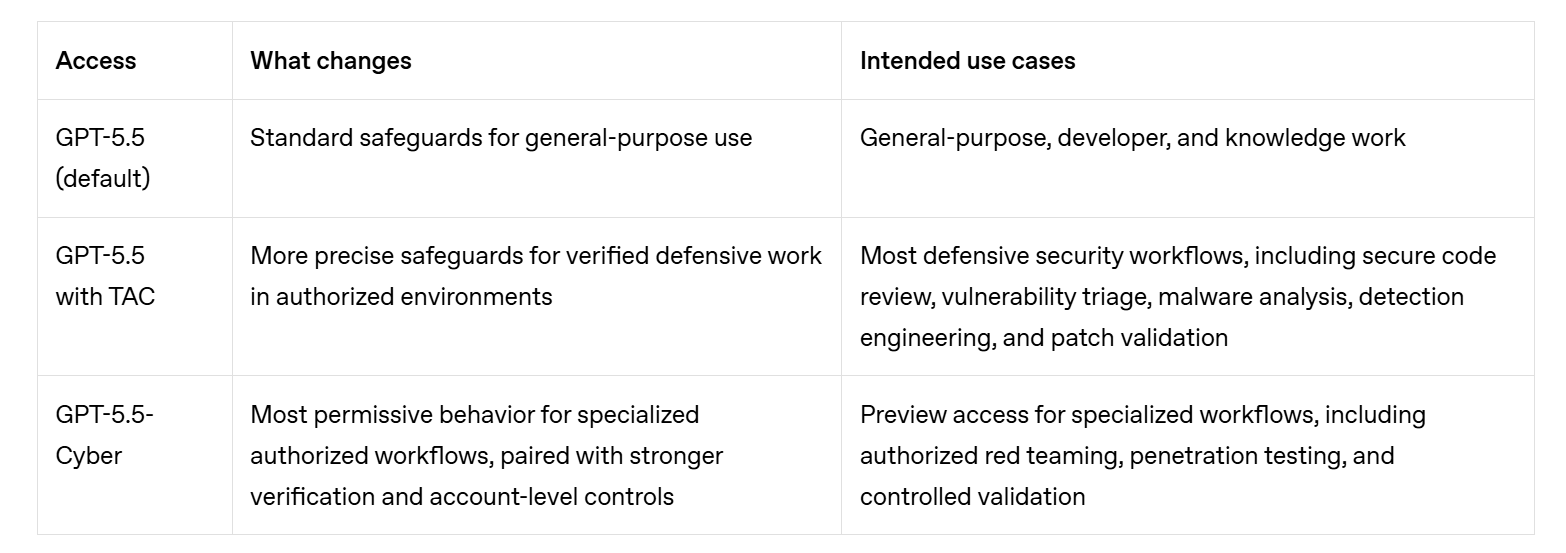
OpenAI is rolling out a more permissible version of GPT-5.5 — aka "Spud" — to vetted cyber defenders who are "responsible for securing critical infrastructure."
Cyber defenders who are vetted and approved for the highest tier of OpenAI's Trusted Access for Cyber program will receive a version of GPT-5.5 that has fewer guardrails than the publicly available model. They will be able to use it to hunt for bugs, study malware, and reverse engineer attacks.
Defenders will still be blocked from certain tasks like credential theft and writing malware, but the new abilities are designed to help them automate popular cybersecurity workflows, OpenAI noted in the press release.
The new GPT-5.5-Cyber model is specifically designed to help defenders write proofs of concept for the bugs they can find or run simulations to test their organization's security posture.
OpenAI has also made another version of GPT-5.5 available to other members of its Trusted Access for Cyber program that can help with understanding unfamiliar code, mapping affected surfaces, or reviewing patches for software flaws. (Sam Sabin / Axios)
Related: OpenAI, Moneycontrol, Help Net Security, OpenAI, Neowin, CNBC, Politico
Researchers at Sentinel Labs report that a new malware framework called PCPJack is stealing credentials from exposed cloud infrastructure while actively removing TeamPCP's access to the systems.
Among the targeted services are Docker, Kubernetes, Redis, MongoDB, RayML, and vulnerable web applications. In many cases, the threat actor moves laterally on the network.
SentinelLabs researchers say that PCPJack appears designed for large-scale credential theft, and likely monetizes its activity via financial fraud, spam operations, credential resale, or extortion.
TeamPCP is a cloud-focused threat group known for high-profile supply-chain breaches against Aqua Security’s Trivy scanner, the LiteLMM and Telnyx PyPI packages, and more recently, SAP npm packages.
Because of the similarities with TeamPCP attacks, SentinelLabs believes that PCPJack may have been developed by a former TeamPCP affiliate or member who started their own operation.
To mitigate this risk, the researchers recommend enforcing multi-factor authentication (MFA), using IMDSv2 in AWS, ensuring proper authentication for Docker and Kubernetes services, following least-privilege principles, and avoiding storing secrets in plaintext. (Bill Toulas / Bleeping Computer)
Related: SentinelOne, TechCrunch, Cyber Press, IT News, Infosecurity Magazine, Dark Reading, Security Week
Ivanti warned customers today to patch a high-severity remote code execution vulnerability in Endpoint Manager Mobile (EPMM), which has been exploited in zero-day attacks.
The security flaw (tracked as CVE-2026-6973) stems from an Improper Input Validation weakness that allows remote attackers with administrative privileges to execute arbitrary code on targeted systems running EPMM 12.8.0.0 and earlier.
Ivanti says customers can mitigate the zero-day by installing Ivanti EPMM 12.6.1.1, 12.7.0.1, and 12.8.0.1, and advises customers to review accounts with Admin rights and rotate those credentials where necessary.
"At the time of disclosure, we are aware of very limited exploitation of CVE-2026-6973, which requires admin authentication for successful exploitation. We are not aware of any customers being exploited by the other vulnerabilities disclosed today," the company said.
"The issues only affect the on-prem EPMM product, and are not present in Ivanti Neurons for MDM, Ivanti's cloud-based unified endpoint management solution, Ivanti EPM (a similarly named, but different product), Ivanti Sentry, or any other Ivanti products."
The US Cybersecurity and Infrastructure Security Agency (CISA) has given US federal agencies four days to secure their networks against a high-severity vulnerability in Ivanti Endpoint Manager Mobile (EPMM) that has been exploited in zero-day attacks. Sergiu Gatlan / Bleeping Computer and Sergiu Gatlan / Bleeping Computer)
Related: CISA, Ivanti, Security Affairs, Cyber Security News, CyberScoop, Security Week
The Australian Cyber Security Center (ACSC) is warning organizations of an ongoing malware campaign using the ClickFix social engineering technique to distribute the Vidar Stealer info-stealing malware.
The attack typically tricks users into executing PowerShell commands to bypass security controls and deliver malware, typically info-stealers.
Australian organizations and infrastructure entities are being targeted in attacks that involve compromised WordPress websites that redirect to malicious payloads.
Users visiting these websites are shown a fake Cloudflare verification or CAPTCHA prompt that instructs them to copy and manually execute a malicious PowerShell command on their system, which leads to a Vidar Stealer infection.
ACSC recommends that organizations restrict PowerShell execution and implement application allow-listing to reduce the risk from these attacks.
WordPress site administrators should apply available security updates for themes and add-ons, and remove any unused themes/plugins from their platforms. (Bill Toulas / Bleeping Computer)
Related: ACSC, Infosecurity Magazine, IT News, Cyber Daily
A new Linux zero-day vulnerability, named Dirty Frag, allows local attackers to gain root privileges on most major Linux distributions with a single command.
Security researcher Hyunwoo Kim, who disclosed the flaw earlier today and published a proof-of-concept (PoC) exploit, says this privilege escalation flaw was introduced roughly nine years ago in the Linux kernel's algif_aead cryptographic algorithm interface.
Dirty Frag works by chaining two separate kernel flaws, the xfrm-ESP Page-Cache Write vulnerability and the RxRPC Page-Cache Write vulnerability, to modify protected system files in memory without authorization and achieve privilege escalation.
Also, while Dirty Frag belongs to the same class as the Dirty Pipe and Copy Fail Linux vulnerabilities, it exploits the fragment field of a different kernel data structure.
"As with the previous Copy Fail vulnerability, Dirty Frag likewise allows immediate root privilege escalation on all major distributions, and it
chains two separate vulnerabilities," Kim said. (Sergiu Gatlan / Bleeping Computer)
Related: Openwall, GitHub, AWS, Techzine, Tom's Hardware, Phoronix, Heise Online, Cyber Security News, The Cyber Express
Software vulnerabilities recently discovered by Anthropic’s new Claude Mythos Preview artificial intelligence model have raised alarms in the cybersecurity community, but Katie Sutton, assistant secretary of defense for cyber policy, sounds upbeat about the benefits of frontier AI technology.
Speaking at the AI+ Expo, Sutton said "As an engineer and as somebody who works to develop tools and has over my career in this space, the first word that I see when I think of Mythos is actually ‘success,’ and it talks to one of the biggest initiatives that I’m going to be leading in the department is how do we leverage what is our number one competitive strength in the United States?"
She noted that frontier AI technology can be used to help develop more secure code.
“One of the challenges of cybersecurity is we’re largely patching vulnerabilities, which is getting after the fact that there are problems in the code. So having tools that are going to help us build that more robust code is a huge opportunity. There’s also huge opportunity to take these tools and be able to learn where our vulnerabilities are so that we can mitigate them and patch them,” Sutton said. (Jon Harper / DefenseScoop)
Related: NextGov/FCW, Breaking Defense
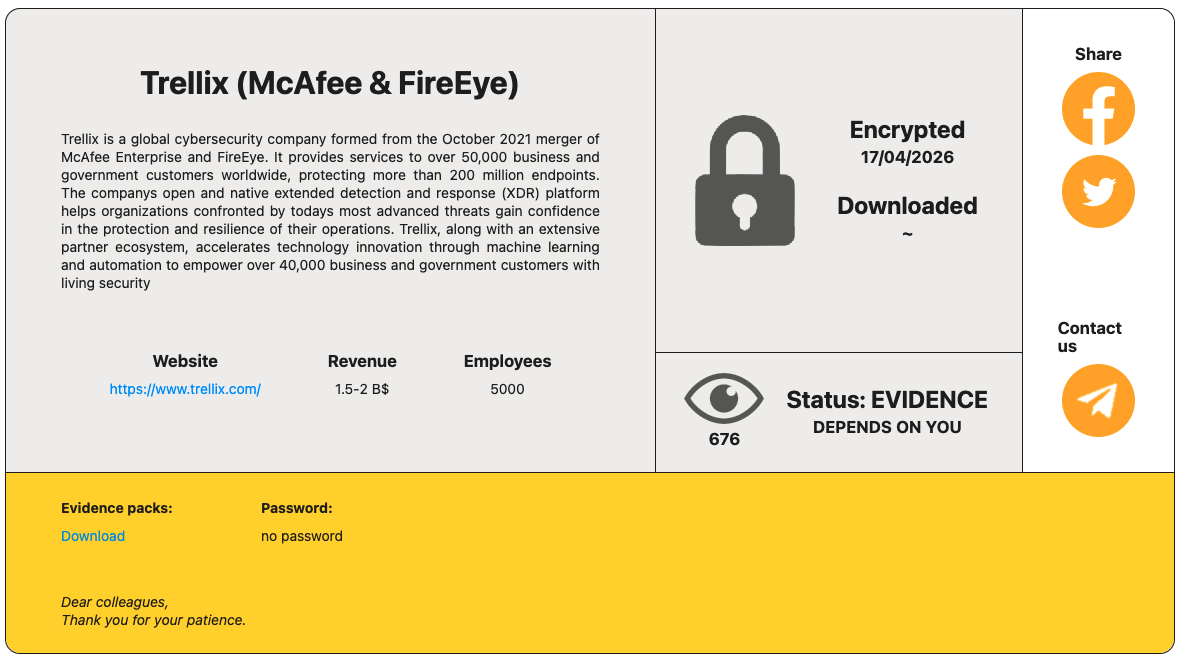
The RansomHouse ransomware group has taken credit for the recent attack on the cybersecurity firm Trellix.
The RansomHouse group named Trellix on its leak website on Thursday. The hackers have not specified how much data they stole from the cybersecurity company, but have published several screenshots that appear to show they had access to internal services and management dashboards.
The hackers have not made any claims regarding the type of data they have stolen from Trellix. (Eduard Kovacs / Security Week)
Related: TechNadu
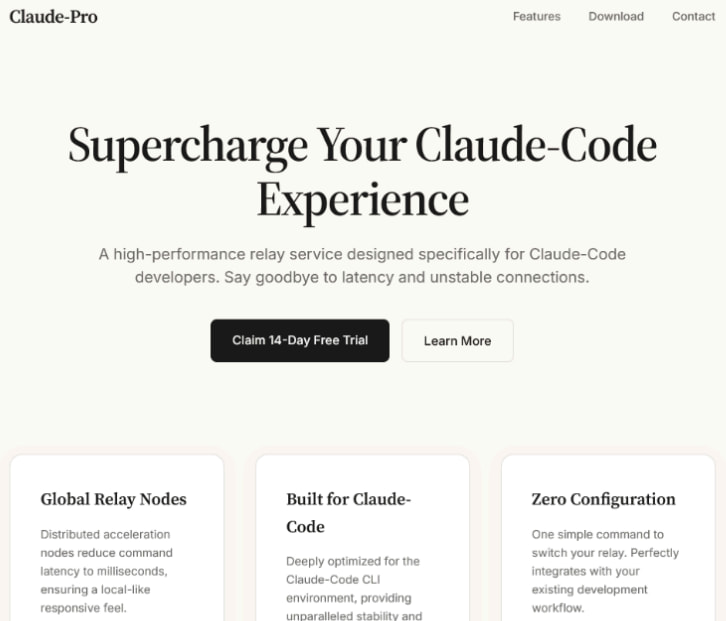
Researchers at Sophos report that a fake version of the Claude AI website offers a malicious Claude-Pro Relay download that pushes a previously undocumented backdoor for Windows named Beagle.
The threat actor advertises Claude-Pro as a "high-performance relay service designed specifically for Claude-Code" developers.
The fake website is a simplistic attempt at mimicking the legitimate site for the popular Claude large language model (LLM) and an AI assistant, using similar colors and fonts.
However, the facade falls apart when it comes to links, as they are mere redirects to the front page, the researchers say.
Although Sophos was unable to attribute the campaign to a threat actor confidently, the researchers suggest that the same operators behind PlugX might be experimenting with a new payload.
To mitigate this risk, users should ensure they are downloading Claude from the official portal and skip or hide sponsored search results. The presence of ‘NOVupdate’ files on a system is a strong indication of compromise. (Bill Toulas / Bleeping Computer)
Related: Sophos, HackRead, Infosecurity Magazine, IT Pro
European data protection authorities fined Yango operator MLU B.V. €100 million ($117 million) after an investigation found the company transferred personal data of taxi users to Russia without safeguards required under EU law.
Regulators also ordered the company to stop all transfers of European user data to Russia with immediate effect.
The case marks the first coordinated European ruling focused on data transfers to Russia.
The decision followed a joint investigation led by the Dutch Data Protection Authority with participation from regulators in Finland and Norway. Authorities opened the inquiry in 2023 after concerns emerged over how Yango handled personal information from passengers and drivers using the taxi platform in Finland and Norway. (Helsinki Times)
Related: Autoriteitpersoonsgegevens.nl
real-time and fraud, one that the public and tech companies may not be ready for, where criminals are able to change their appearance in real time to trick people, including Americans, into handing over their money.
Romance scams, tax fraud, and virtual kidnappings all stand to be amplified by live deepfake software, which continues to improve in quality.
404 Media’s experimentation with Haotian AI marks the first time a journalist has managed to test this software to see how it really works, how effective it is, and what its existence means for the present and very near future of scams.
Their investigation finds that Haotian AI demonstrates its tool as a way to impersonate at least one US police department. They link Haotian AI to Chinese money laundering networks and the ecosystem providing services to massive scam compounds in South East Asia, and find that Haotian AI has brought in more than $4 million dollars for its creators.
Their investigation also reveals that Haotian AI is likely based on open-source face swap tools, meaning the true value of the software is its sophisticated technical support. With that, even the least tech-savvy criminals can now access real-time deepfake software, opening up the possibility for more fraudsters around the world to use this powerful technology. (Joseph Cox / 404 Media)
Related: r/technology
Cloudflare's stock fell in premarket trading on Friday after the company said it would slash jobs and gave a forecast for revenue that fell short of analysts’ expectations.
It projected revenue of $664 million to $665 million for the second quarter, down from the $666.1 million that Wall Street was anticipating.
Shares fell more than 17% in premarket trading on Friday after closing at $256.79 in New York.
The company also said it would slash its current workforce by roughly 1,100 people — about a fifth of the total — as it prioritizes artificial intelligence tools in its operating model. (Margi Murphy / Bloomberg)
Related: Cloudflare, Reuters, Barron's, The Register, Wall Street Journal, Los Angeles Times
Best Thing of the Day: Vive La France!
French prosecutors are seeking charges against Elon Musk and his social platform X for child sexual abuse images on the platform, deepfakes, disinformation, and complicity in denying crimes against humanity by the platform’s artificial intelligence system, Grok.
Worst Thing of the Day: Just Say No
A South Korean fintech company is betting that payment by facial recognition will go mainstream after it signed up nearly 10 percent of the country’s population for its service.
Bonus Worst Thing of the Day: Robbing Peter to Pay Paul
The Trump administration said the CyberCorps Scholarship For Service program would now be known as CyberAI SFS, redirecting funds to artificial intelligence and away from cybersecurity.
Extra Bonus Worst Thing of the Day: Giving Pervert Glasses to Some of the Worst People
Immigration and Customs Enforcement (ICE) is exploring developing a pair of smart glasses that would “supplement” the agency’s facial recognition Mobile Fortify application, which lets officers scan someone’s face to verify their citizenship.
Closing Thought