Nine Dubai scam centers raided in joint US-China operation, 276 arrested
White House opposes Anthropic's expansion of Mythos access, Oz government warns banks on AI cyberattacks, Ukraine arrests three people who allegedly hacked 610k+ Roblox accounts, European celebrity exposed cloud repo with 90k stalkerware screenshots, Chinese hackers breached Cuba's embassy, more


Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
At least nine scam centers in Dubai were raided in a joint operation between US and Chinese law enforcement agencies that led to 276 arrests.
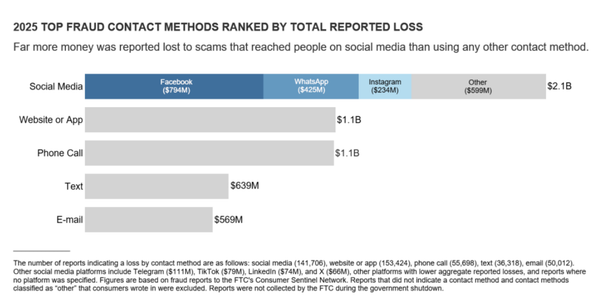
The Justice Department said the operation began last year following “numerous” victim complaints to the FBI by US victims who lost millions through cryptocurrency investment fraud schemes. With the help of information from social media giant Meta, financial data, and cryptocurrency records, federal agents traced the schemes back to Dubai.
Prosecutors announced federal fraud and money laundering charges against four people accused of running the scam centers, including 27-year-old Burmese national Thet Min Nyi and Indonesian nationals Wiliang Awang, Andreas Chandra, and Lisa Mariam. Two unnamed fugitive co-conspirators were also charged.
Thet Min Nyi allegedly served as a manager and recruiter for a front company called Ko Thet Company, while the others ran two organizations called Sanduo Group and Giant Company. All three were used to conduct pig-butchering schemes involving fake investment opportunities.
Wiliang Awang was arrested in Thailand by the Royal Thai Police while the Dubai Police Department conducted a coordinated raid on the nine scam centers that led to the arrests of Thet Min Nyi, Andreas Chandra, and Lisa Mariam. (Jonathan Greig / The Record)
Related: Justice Department, The Block, USA Today, Social Media Today, Crypto News, Coinpaper, The Crypto Times, RegTechTimes, AFP, The Filipino Times, Bleeping Computer
The White House opposes a plan from Anthropic to expand access to its powerful artificial-intelligence model Mythos, complicating the rollout of an AI tool capable of carrying out cyberattacks and sowing widespread disruptions online.
Anthropic recently proposed letting roughly 70 additional companies and organizations use Mythos, which would have brought the total number of entities with access to about 120, people familiar with the matter said. Administration officials told the company they oppose the move because of concerns about security, the people said.
Some White House officials also worried that Anthropic wouldn’t have access to enough computing power to serve that many more entities without hampering the government’s ability to use it effectively, one of the people said. (Robert McMillan and Amrith Ramkumar / Wall Street Journal)
Related: Bloomberg, The Next Web, The Verge, New York Times, MediaNama, Bloomberg Law, Digit, Reuters, Axios
The Australian Prudential Regulation Authority (APRA) said the country's banks were not keeping pace with AI industry developments, warning frontier AI systems such as Anthropic's Mythos had the potential to lead to larger and faster cyber attacks.
In a letter, the APRA said most of the industry's information security practices were struggling to match the rate of change in AI.
The regulator said the speed of AI development could pose a growing threat to Australia's financial services."It also warns frontier AI models such as Anthropic’s Claude Mythos, which could enhance the discovery of vulnerabilities by bad actors, are expected to further increase the probability, speed, and scale of cyber attacks," APRA said in a statement referencing a review that it had conducted.
APRA said its industry consultation had found banks were relying too heavily on AI model presentations and summaries from vendors without considering the risks that could emerge."APRA observed many boards are still developing the technical literacy required to provide effective challenge on AI-related risks and oversight," the letter said.
The regulator said while banks already had strict security procedures in place, some were not engineered to keep pace with the development of AI. (Scott Murdoch / Reuters)
Related: APRA, Financial Review, Bloomberg
The Ukrainian police arrested three individuals who hacked more than 610,000 Roblox gaming accounts and sold them for a profit of $225,000.
The arrests were made by the police in Lviv after conducting ten searches on targeted locations, seizing $35,000 in cash, 37 mobile phones, 11 desktop computers, seven laptops, five tablets, and four USB drives.
Although the police did not specify the game platform targeted by the hackers, aged 19, 21, and 22, the Prosecutor General’s Office stated that it was Roblox.
“Prosecutors of the Lviv region, together with the cyber police and the Security Service of Ukraine, have stopped the activities of a group that gained access to other people's gaming accounts and used them as a source of income,” the Prosecutor General's Office said.
“This concerns profiles in Roblox, where users create games, communicate, and purchase virtual items with in-game currency. For many, such accounts hold not only gaming value but also financial value due to accumulated resources and purchased items.”
The authorities state that, at least 357 of the 610,000 user accounts the hackers took over between October 2025 and January 2026, were high-value (“elite”) accounts.
The 19-year-old is identified as the leader of the threat group, who recruited the other two on gaming forums and set up the account-hacking scheme.
The scheme involved promoting info-stealing malware disguised as a game-enhancer tool, infecting victim devices, and collecting their login credentials. (Bill Toulas / Bleeping Computer)
Related: Prosecutor's General Office, PCMag, ghacks, Security Affairs

Security researcher Jeremiah Fowler discovered a cloud repository that was publicly accessible on the open internet with no access controls, containing nearly 90,000 screenshots showing a European celebrity’s private messages, photos, and phone usage—seemingly compiled using stalkerware.
“All the selfies were one person, all the chats were one person, and it was basically everyone they chatted with divided into Instagram, Facebook, TikTok, and WhatsApp,” Fowler said. “There was a lot of nudity, there were pictures that you wouldn’t want out in the public.”
Among the 86,859 images, Fowler’s analysis says, were ones capturing the celebrity talking privately with models, influencers, and other high-profile individuals, some of whom have millions of followers on their social media accounts. The screenshots, he says, captured business conversations with invoices and personal payment details, phone numbers, some partial credit card numbers, and huge volumes of sensitive information.
Fowler is not naming the apparent victim or their associates and says he reported the incident to local law enforcement. “Even though this is a very public person, even public people deserve privacy,” Fowler said. (Matt Burgess and Lily Hay Newman / Wired)
Related: ExpressVPN
Researchers at Gambit Security report that Chinese hackers breached Cuba’s embassy in Washington to spy on communications of dozens of diplomats as the island nation stared down a US naval blockade.
The campaign began in January and compromised the emails of 68 officials, including the Cuban ambassador and the deputy chief of mission, researchers said. The breach coincided with a period of intense geopolitical friction, occurring shortly after a US raid in Venezuela and roughly coinciding with the Trump administration’s decision to halt oil deliveries to Cuba, contributing to widespread blackouts across the country.
The intruders bypassed embassy security by exploiting two five-year-old vulnerabilities in outdated Microsoft Exchange email servers, according to the Gambit findings. Once inside, attackers downloaded entire inboxes belonging to political and intelligence officials.
Gambit researchers said they also observed the Chinese group targeting the Venezuelan government and the Ministry of Foreign Affairs around the same time. The hackers used tools, techniques, and infrastructure associated with Chinese state-sponsored cyber-espionage, according to Gambit. (Patrick Howell O'Neill / Bloomberg)
Related: Gambit Security on LinkedIn
The spouse of the founder of Andar, a Korean athleisure brand, has received a final one-year prison sentence for contacting a North Korean hacker to operate an illegal private server for an online game.
According to legal sources on Tuesday, the first division of the Supreme Court (presiding Justice Suh Kyung-hwan) recently upheld the lower court's ruling sentencing Oh, charged with violating the National Security Act, to one year in prison and one year of suspension of qualifications.
From July 2014 to May of the following year, Oh communicated with A, a North Korean program developer, through the Chinese messenger QQ, receiving executable files needed to operate a private server for a well-known online game and requesting virus resolution. Oh transferred a total of 23.8 million won ($17,000) to A in exchange for core executable files and other materials. Oh carried out these activities while knowing that A was a program developer affiliated with a North Korean institution.
A was reportedly a development team leader at the Rungrado Information Center of the Korea Rungrado Trading Corporation, which operates directly under Office 39 of the Workers' Party of Korea. The information center, disguised as a legitimate trading company, is known to actually produce and sell illegal programs that can be exploited for cyberattacks, serving as a channel to raise funds for the North Korean regime.
Oh appealed the ruling, but the appellate court and the Supreme Court both found no error in this judgment and dismissed the appeal. (Kim Sung-tae / Seoul Economic Daily)
Related: The Chosun Daily
Developers of major Linux distributions have begun shipping patches to address a local privilege escalation (LPE) vulnerability arising from a logic flaw.
The newly disclosed LPE, dubbed Copy Fail (CVE-2026-31431), comes from a vulnerability in the Linux kernel's authentication cryptographic template.
"An unprivileged local user can write four controlled bytes into the page cache of any readable file on a Linux system, and use that to gain root," the writeup from security biz Theori explains.
The kernel reads the page cache when it loads a binary, so modifying the cached copy amounts to altering the binary for the purpose of program execution. But doing so doesn't trigger any defenses focused on file system events like inotify.
The proof of concept exploit is a 10-line, 732-byte Python script capable of editing a setuid binary to gain root on almost all Linux distributions released since 2017.
Copy Fail is similar to other LPE bugs, such as Dirty Cow and Dirty Pipe, but its finders claim it doesn't require winning a race condition, and it's more broadly applicable.
It's not remotely exploitable on its own – hence LPE – but if chained with a web RCE, malicious CI runner, or SSH compromise, it could be relevant to an external attacker. The bug is of most immediate concern to those using multi-tenant Linux systems, shared-kernel containers, or CI runners that execute untrusted code.
According to Theori, the vulnerability also represents a potential container escape primitive that could affect Kubernetes nodes, because the page cache is shared across the host. (Thomas Claburn / The Register)
Related: Copy Fail, HackRead, IT News, Cyber Press, Cyber Security News, Koran Manado, Techzine, Cyber Kendra
Researchers at Snyk report that hackers are exploiting two authentication bypass vulnerabilities in the Qinglong open-source task scheduling tool to deploy cryptominers on developers' servers.
Exploitation started in early February, before the security issues were disclosed publicly at the end of the month.
The two security problems impact Qinglong versions 2.20.1 and older and can be chained to achieve remote code execution. The first is CVE-2026-3965, which is a misconfigured rewrite rule that maps ‘/open/’ requests to ‘/api/’, unintentionally exposing protected admin endpoints through an unauthenticated path.
The second is CVE-2026-4047, which is the authentication check that treats paths as case-sensitive (/api/), while the router matches them case-insensitively, allowing requests like ‘/aPi/...’ to bypass authentication and reach protected endpoints.
The root cause of both flaws is a mismatch between middleware authorization logic and Express.js routing behavior.
The maintainer acknowledged the vulnerability and urged users to install the latest update. However, the mitigation in pull release #2924 focused on blocking command injection patterns, which Snyk says was insufficient.
The researchers report that the effective fix came in PR #2941, which corrected the authentication bypass in the middleware. (Bill Toulas / Bleeping Computer)
Related: Snyk, CyberPress, GBHackers, Cyber Security News
A critical vulnerability affecting all but the latest versions of cPanel and the WebHost Manager (WHM) dashboard could be exploited to obtain access to the control panel without authentication.
The security issue, currently identified as CVE-2026-41940 and with a severity score of 9.8, has been addressed in an emergency update that requires running a command manually to retrieve a patched version of the software.
Owned by WebPros International, WHM and cPanel are Linux-based web hosting control panels for server and website management. While WHM provides server-level control, cPanel provides administrator access to the website backend, webmail, and databases.
To install a safe version, the vendor recommends that administrators execute the command /scripts/upcp –force, which runs the cPanel update process and forces it to execute even if the system thinks it already runs on the latest version.
Servers running an unsupported version of cPanel are ineligible for security updates. In this case, administrators are recommended to upgrade to a supported version as soon as possible. (Bill Toulas / Bleeping Computer)
Related: Cpanel, The Register, Heise Online
Sens. Chuck Grassley (R-IA) and Jim Banks (R-IN) are demanding answers from major tech and AI companies over concerns that employees with ties to China could access cutting-edge US AI systems.
The lawmakers are focusing on insider access — not just hacking — as a potential vulnerability, putting pressure on companies to demonstrate stronger safeguards.
Identical letters sent to the CEOs of Amazon, Anthropic, OpenAI, Google, Meta, Microsoft, Safe Superintelligence Inc., Thinking Machines Lab, and xAI ask for responses to nine questions by May 20. (Hans Nichols / Axios)
The House passed a three-year reauthorization of a key spy power on Wednesday, sending the extension to the Senate one day before it is set to expire.
A bipartisan coalition of lawmakers voted 235-191 to extend Section 702 of the Foreign Intelligence Surveillance Act after weeks of agonizing negotiations and intraparty disputes.
The Senate is unlikely to clear the House-passed extension, which will be sent over with an unrelated, permanent ban on the Federal Reserve’s ability to issue a digital currency attached.
That means the Senate could send its own version of a Section 702 extension back to the House with just hours to spare before the law expires tonight. (Mia McCarthy / Politico)
Related: The Record, CBS News, The Hill, NPR, Senator Dick Durbin, Roll Call, Axios
The growth of data centers — and adversaries’ targeting of them — left lawmakers at a hearing of the House Homeland Security Subcommittee on Cybersecurity and Infrastructure Protection contemplating whether the federal government has the right setup for defending them.
Several industry witnesses and experts testified that the answer might be to give data centers their own standalone designation as a critical infrastructure sector.
“If a major data center is attacked, disrupted, or taken offline, the consequences can reach far beyond one company or one sector,” Rep. Andy Ogles, R-Tenn., said in prepared opening remarks. “Yet our current framework does not provide a clear, unified approach to data center security. It does not clearly answer which federal agency is responsible for understanding the risk, coordinating with industry, or leading the response when this infrastructure is targeted.”
Three providers account for 63 percent of the market share of data centers: Amazon Web Services, Microsoft Azure, and Google Cloud Platform. (Tim Starks / CyberScoop)
Related: House Homeland Security Committee, Federal News Network
The City of Ardmore, OK, is alerting the public after a ransomware attack earlier this month that may have involved personal information.
According to a Facebook post from the city's account, staff say the incident was discovered on April 8, after attackers targeted some internal servers.
While not all systems were accessed, information tied to criminal complaints and investigations may have been involved — including names, addresses, and phone numbers.
Financial systems, like water billing, are stored separately and were not accessible during the attack. Emergency services also remained available.
City staff say they brought in outside IT specialists and federal agencies — including the FBI and Cybersecurity and Infrastructure Security Agency — to investigate.
The situation is believed to be contained, but the investigation is ongoing. (KTEN)
Related: City of Ardmore, EastTexasRadio, KXII
The Rural Municipality of Gimli, in Manitoba's Interlake, said its systems were affected by what it described as a "cybersecurity incident."
The RM did not provide additional details about the nature of the incident, but said it has hired a cybersecurity firm to investigate and assess the situation.
The municipality said it is "still determining the scope of the impact," and will provide updates when more information is available, according to the post.
For now, the RM said its office is unable to process bill payments, and advised residents that the "quickest and most reliable" option for bill payments currently is to make them directly at a bank.
The RM also said on its website it had canceled its scheduled Wednesday morning council meeting "on short notice due to unforeseen circumstances." (CBC News)
Best Thing of the Day: Finally, Goblins and Gremlins Are Getting Their Due
Starting with GPT‑5.1, OpenAI's models began developing a strange habit: they increasingly mentioned goblins, gremlins, and other creatures in their metaphors.
Worst Thing of the Day: 'Don't Be Evil' Is Just a Distant Memory Now
Google has told its employees it “proudly” works with the US military and will continue to do so, as the tech giant faces down opposition from hundreds of staff over a deal for its AI to be used in classified operations.
Closing Thought