Scattered Spider’s ‘Bouquet’ nabbed after globe-trotting luxury hacker spree
White House is trying to get Anthropic back on board while lawmakers come up to speed, Paragon not cooperating with Italian prosecutors, Polymarket denies breach reports, Syndicate was hacked for about $400k, FIDO Alliance forms AI agent standards groups, Vimeo admits breach through, much more
Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
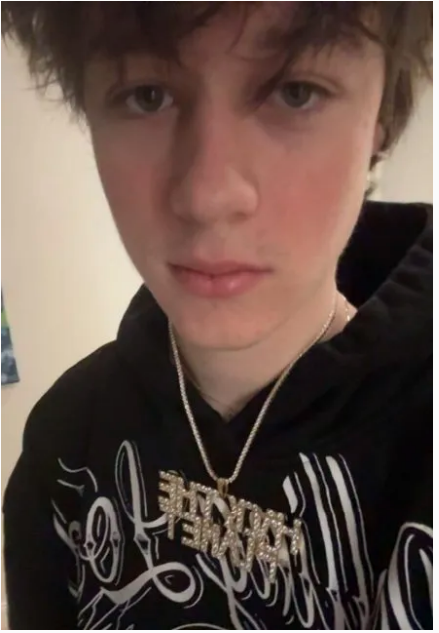
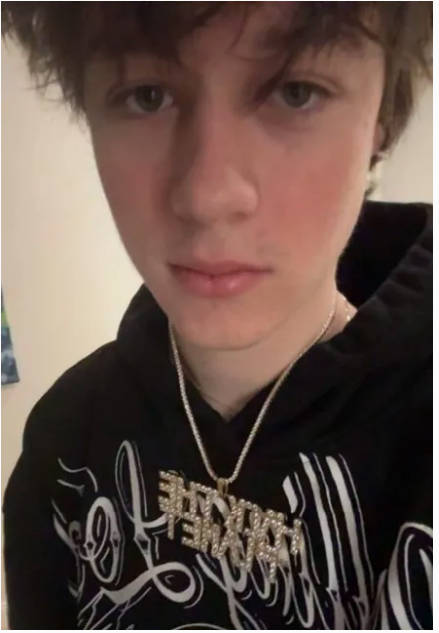
US federal authorities busted Peter Stokes, a teen who goes by the online moniker “Bouquet” and who jetted around the world from Dubai to Thailand to New York, staying in five-star hotels and flashing cash and jewels, alleging he is a prolific member of the loosely connected, international group of sophisticated hackers known as Scattered Spider.
Nineteen-year-old Stokes, a dual citizen of the U and Estonia, was arrested earlier this month in Finland attempting to board a flight to Japan.
At the time he was approached at the airport in Helsinki on April 10, Stokes “was in possession of, among other electronics, two two-terabyte hard drives,” alleged a criminal complaint that the Tribune obtained when it was briefly made public last week.
Authorities are seeking to have Stokes extradited to Chicago to face charges, according to the complaint, which has since been resealed. The US attorney’s office declined to comment.
A number of Scattered Spider members have been arrested in the past several years. Among them was Tyler Robert Buchanan, a 24-year-old British national described as a “senior member” of the group, who pleaded guilty last week in federal court in California to using text message phishing attacks to hack US companies and steal at least $8 million in virtual currency from individual victims.
Stokes, meanwhile, was charged in a six-count complaint filed under seal in December with wire fraud, conspiracy, and computer intrusion. The charges alleged that Stokes personally participated in at least four Scattered Spider hacks, including one when he was just 16 years old, that have cost victim companies millions of dollars.
According to the complaint, Stokes, the son of a prominent European businessman, “in recent years has exhibited substantial wealth for a person his age,” posting images on Facebook and Snapchat of his travels in Europe as well as to Mexico, Thailand, and Dubai. (Jason Meisner / Chicago Tribune)
Related: Bleeping Computer, Databreaches.net, HackRead, Patch, Hoodline
Sources say the White House is developing guidance that would allow agencies to get around Anthropic's supply chain risk designation and onboard new models, including its most powerful yet, Mythos.
A draft executive action that is currently in the works could, among other steps related to the government's use of AI, give the administration a way to dial down the Anthropic fight, two sources said.
The White House is convening companies across various sectors this week to inform them of the potential executive action and best practices for deploying Mythos. Those meetings include "table reads" of possible guidance that could walk back the Office of Management and Budget's directive on not using Anthropic in the government.
Separately, OpenAI and Anthropic briefed House Homeland Security Committee staff on their new cyber-capable AI models and their implications for cybersecurity.
This is one of the first briefings that lawmakers have had with the AI giants about the cyber threats posed by their new models, including to under-resourced critical infrastructure sectors. (Maria Curi, Ashley Gold / Axios, Sam Sabin, Ashley Gold / Axios)
Related: Benzinga, TechCrunch, Reuters
Following a spyware scandal in Italy last year involving the Israeli American surveillance tech maker Paragon Solutions, Paragon has been uncollaborative in working with the government, according to Wired Italy.
Italian prosecutors sent a formal request for information to Paragon, via the Israeli government, but a year after the investigations were opened, the company has yet to respond.
Following the eruption of the spyware scandal in Italy, Paragon publicly called out the Italian government, claiming it refused the company’s offer to investigate whether a journalist was hacked and spied on with its Graphite spyware. The company went so far as to cancel its contract with Italy’s two spy agencies, AISE and AISI, in part because the Italian government turned down the company’s offer to help.
It’s unclear why Paragon has not responded to the prosecutor’s request. It’s possible that the Israeli government intervened. In 2024, The Guardian reported that the Israeli government seized documents from NSO’s office to prevent the company from complying with demands in the lawsuit against WhatsApp. (Lorenzo Franceschi-Bicchierai / TechCrunch)
Related: Wanted in Rome, Wired Italy
Prediction market platform Polymarket has denied claims of a security breach after reports surfaced that more than 300,000 records and an exploit kit were leaked on a cybercrime forum.
The disclosure, flagged by Dark Web Informer in an X post, attributes the incident to an actor identified as “xorcat.” The dataset is said to have been extracted on April 27, 2026, using a combination of undocumented API access points and misconfigurations.
Polymarket pushed back on the characterization of the incident, stating that the data referenced in the leak is publicly accessible by design.
In a post on X, the platform said its on-chain architecture makes data auditable and available through public endpoints. It added that no private data was compromised and that the same information can be accessed freely through its APIs, framing the claims as a misrepresentation of how its system works. (Shubham Soni / Crypto Times)
Related: Cryptonews.net, Yellow, Coinpaper
Blockchain infrastructure platform provider Syndicate confirmed that its Commons bridge was compromised, allowing an attacker to steal around 18.5 million SYND tokens and sell them for an estimated $330,000–$400,000 before bridging funds to Ethereum.
Following the exploit, SYND plunged roughly 35% as panic selling hit the market.
Syndicate says it is working with security firms to trace the attacker and has enough reserves to compensate affected users. (Nidhi Kolhapur / Coinpedia)
Related: Crypto News, Cryptopolitan, The Block
Working with initial contributions from Google and Mastercard, the authentication-focused industry association known as the FIDO Alliance said that it will launch a pair of working groups to develop industry standards for validating and protecting payments and other transactions carried out by AI agents.
The goal is to produce a protective baseline that can be adopted across industries. This way, users can authorize agent actions using mechanisms that can't easily be phished or taken over by a bad actor to give an agent rogue instructions.
The standards would also include cryptographic tools that digital services could use to confirm agents are accurately and legitimately carrying out an authenticated person's instructions, as well as privacy-preserving frameworks to give users, merchants, and other service providers the ability to validate transactions being initiated by agents.
In other words, the goal of the work is to create protections against agent hijacking or other rogue behavior, as well as a transparency and accountability mechanism for recourse in the event of a dispute. (Lily Hay Newman / Wired)
Related: PYMNTS.com, The Keyword, FIDO Alliance, Google Cloud Blog, Help Net Security
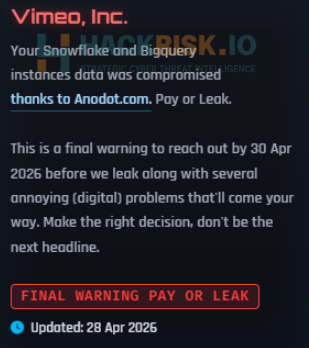
Video hosting platform Vimeo said user and customer data were stolen from a third-party analytics vendor during a recent data breach.
A Vimeo spokesperson confirmed that recent claims of a data breach by a cybercriminal gang were related to a security incident at Anodot, a popular business analytics company.
In a blog post, the company tied the recent attack on Anodot to the longer string of attacks by Shinyhunters and related cybercriminal factions. Anodot did not respond to requests for comment.
“We have identified that, as a result of the Anodot breach, an unauthorized actor accessed certain Vimeo user and customer data. Our initial findings suggest that the databases accessed primarily contain technical data, video titles, and metadata, and, in some cases, customer email addresses,” Vimeo’s security team wrote.
“Upon learning of the incident, we promptly disabled all Anodot credentials, removed the Anodot integration with Vimeo systems, and engaged third-party security experts to assist with the investigation. We have also notified law enforcement.”
The hackers did not access video content, user logins, or payment card information. There was no disruption to Vimeo’s services, according to the statement. The investigation into the attack is ongoing, they added.
Shinyhunters added Vimeo to its leak site on Tuesday morning, threatening the company with a data leak if a ransom was not paid by Thursday. The cybercriminals did not say how much data was stolen. (Jonathan Greig / The Record)
Related: Vimeo, Bleeping Computer, PCMag, Cybersecurity Insiders, Security Affairs, Security Week
The Canadian federal government announced it is planning to ban crypto ATMs in order to protect Canadians from scammers using the machines to defraud victims.
The Liberals' spring economic update on Tuesday referred to crypto ATMs as a “primary method for scammers to defraud victims and for criminals to place their cash proceeds of crime.”
Crypto ATMs might look a lot like a traditional banking machine, but instead of dispensing cash from your bank account, the majority of these machines allow customers to deposit cash and then convert it into cryptocurrency, like Bitcoin. Then, they can send it to a virtual wallet anywhere in the world.
Last year, CBC News spent months looking into this industry, speaking with law enforcement, financial regulators, cryptocurrency experts, former crypto ATM company employees, the operators themselves, and fraud victims for a three-part series, Feeding Fraud: The Crypto ATM Problem.
The investigation revealed that these machines, which currently operate legally in Canada, have become the main vehicle fraudsters use to get money from scam victims across the country. Canada's financial intelligence agency, FINTRAC, came to that conclusion in a February 2023 analysis of suspicious transaction reports submitted to the agency. (Nicole Brockbank, Angelina King / CBC News)
Related: CoinDesk, PYMNTS, Coinpedia, r/CryptoCurrency, The Block, Crypto Briefing
Sri Lanka’s government has disclosed a payment lapse involving funds due to the US Post, days after revealing a separate cyberattack, raising fresh questions about its financial safeguards as it continues to recover from an unprecedented default.
Authorities said they are probing the whereabouts of a payment of about $600,000 after the US Post said it had not been received. The island nation is also investigating the theft of $2.5 million by hackers who breached the finance ministry’s computer systems, officials said last week.
The back-to-back revelations have heightened concerns about oversight. Opposition parties have called for greater scrutiny and a parliamentary debate on the cyberattack, saying it threatens economic stability and security, according to local media reports. (Anusha Ondaatjie / Bloomberg)
Related: Daily FT, Daily Mirror
Illinois Rep. Delia Ramirez is taking over as the top Democrat on the House Homeland Security panel’s cybersecurity subcommittee, replacing former Rep. Eric Swalwell after his resignation.
Committee Democrats approved the change at a meeting prior to a “shadow hearing” without the GOP majority, focused on protecting elections from Trump administration interference.
Ramirez first won election to Congress in 2022 and was reelected in 2024. She has served as the vice ranking member of the committee since 2023. She is now the ranking member of the Subcommittee on Cybersecurity and Infrastructure Protection.
She has leveled criticisms during committee hearings about the Trump administration’s personnel cutbacks at the Cybersecurity and Infrastructure Security Agency, and was critical of how data was secured under the administration’s Department of Government Efficiency initiative led by Elon Musk. (Tim Starks / CyberScoop)
Related: Representative Delia Ramirez
The patient data stolen during a hack at software provider ChipSoft has not been published anywhere, and the data has since been destroyed, the company reported in a statement on its own website.
ChipSoft, which supplies software for the storage of patient records to Dutch hospitals and house doctors, announced the hack earlier this month. Patient data, including medical records, was stolen during the attack. The affected institutions included rehabilitation centers and general practitioners’ practices.
According to the company, this stolen data has now been destroyed. “Our cybersecurity experts have confirmed that this destruction was carried out in a technically correct manner,” the company said. (NL Times)
Related: Techzine, Dutch News
Browsers like Mozilla Firefox and Tor Browser contained a vulnerability where websites could create a hidden ID from browser sessions without using cookies or other obvious tracking methods.
The vulnerability was discovered by security researchers Dai Nguyen and Martin Bajanik of Fingerprint. In an in-depth report published earlier this week, the duo said the issue allowed websites to derive a “unique, deterministic, and stable process-lifetime identifier” from the order of entries returned by IndexedDB, even when users expect “stronger isolation”.
IndexedDB is a built-in browser database that lets websites store large amounts of structured data (like files or app data) directly on the device. It allows web apps to work faster and even offline without constantly talking to a server. However, when a site asked the browser for a list of stored items, the order of that list wasn’t random. Instead, it reflected internal browser behavior, which could be turned into a unique fingerprint.
While this sounds bad for more privacy-oriented users, it gets even worse since the vulnerability persisted even when using the private browsing mode.
Fingerprint responsibly disclosed the issue to both Mozilla and the Tor Project, and patches were quickly released. Mozilla addressed it in Firefox 150 and ESR 140.10.0, while tracking the patch in Mozilla Bug 2024220. Tor fixed it indirectly by pulling Mozilla’s fix. According to available reports, Tor Browser version 15.0.10 includes the same security update that solved the issue in Mozilla Firefox. (Sead Fadilpašić / TechRadar)
Related: Security Affairs, SC Media, Security Week, Penligent
Cosmetics manufacturer Estée Lauder has reached a proposed settlement in a class-action lawsuit relating to two data breaches.
The lawsuit relates to two separate data breaches in May and July of 2023 that “potentially compromised the personal and financial information of individuals across Canada,” according to Montreal-based Concilia Services, which specializes in class action administration.
Under the proposed settlement, Estée Lauder will pay $1,515,000 to resolve all claims and denies all allegations and liability. The parties agreed to settle to avoid the risk and expense of continued litigation, Concilia said. (Uday Rana / Global News)
Related: Global Cosmetics News, Cosmetics Business, Daily Hive
Researchers at Check Point have found that Vect 2.0 ransomware wipes large, compromised files instead of merely encrypting them, making recovery impossible – even for the attackers.
This is due to a critical flaw in the encryption implementation, which is likely a coding error.
Vect is a ransomware-as-a-service (RaaS) program that first appeared in December 2025 on a Russian-language cybercrime forum and was discovered by security researchers in early January 2026.
The group quickly grabbed headlines after it announced on BreachForums that it was partnering with TeamPCP, the threat group behind several supply-chain attacks, such as Trivy, Checkmarx’s KICS, LiteLLM, and Telnyx, in March and April 2026.
Additionally, Check Point reported that Vect also announced a partnership with BreachForums itself, promising that every registered forum user will become an affiliate and be granted use of the Vect ransomware, negotiation platform, and leak site for operations. (Kevin Poireault / Infosecurity Magazine)
Related: Check Point, Cyber Daily, SC Media, Computer Weekly
According to Europol's latest annual Internet Organised Crime Threat Assessment (IOCTA), ransomware remains a dominant threat across the EU, with more than 120 active ransomware brands observed by Europol in 2025.
Criminal actors continue to exploit vulnerabilities in the digital supply chain and employ increasingly sophisticated social engineering techniques. The extortion model is shifting away from data encryption toward pure data theft, with attackers increasingly relying on the threat of exposure to force payment.
The IOCTA 2026 report added that while financial gain remains the primary driver of cyberattacks, the relationship between hybrid threat actors and cybercriminals is blurring. Hybrid threat actors are increasingly using cybercriminal networks as proxies for disruptive operations, including DDoS attacks, intrusions, and ransomware attacks. (Anna Ribeiro / Industrial Cyber)
Related: Europol
The US Cybersecurity and Infrastructure Security Agency (CISA) has ordered federal agencies to secure their Windows systems against a vulnerability exploited in zero-day attacks.
Tracked as CVE-2026-32202, this security flaw was reported by cybersecurity firm Akamai, which described it as a zero-click NTLM hash leak vulnerability left behind after Microsoft incompletely patched a remote code execution flaw (CVE-2026-21510) in February.
As CERT-UA revealed, the Russian APT28 (aka UAC-0001 and Fancy Bear) cyberespionage group exploited CVE-2026-21510 in attacks against Ukraine and EU countries in December 2025 as part of an exploit chain that also targeted a LNK file flaw (CVE-2026-21513).
Microsoft says that remote attackers who successfully exploit the CVE-2026-32202 vulnerability in low-complexity attacks by sending "the victim a malicious file that the victim would have to execute," could "view some sensitive information" on unpatched systems.
Akamai further explained in a report that this security flaw can be exploited in pass-the-hash attacks to steal NTLM hashes (hashed passwords), which are later used to authenticate as the compromised user, allowing attackers to spread laterally across the network or steal sensitive data. (Sergiu Gatlan / Bleeping Computer)
Related: Security Week, Cyber Press, Akamai
Representatives from leading AI security standardization initiatives have formed MOSAIC (Multi-Organization Secure AI Coordination), the first collaboration of its kind among AI security standard organizations.
The group took shape on April 21, 2026, at the AI Security Policy Forum, held alongside the SANS AI Cybersecurity Summit.
Founding participants in MOSAIC include the Open Worldwide Application Security Project (OWASP), SANS Institute, National Institute of Standards and Technology (NIST), Cloud Security Alliance (CSA), Center for Internet Security (CIS), Coalition for Secure AI (CoSAI), and the Berryville Institute of Machine Learning (BIML). Other stakeholders participating in the forum included members of the International Telecommunication Union (ITU), the Aspen Institute, and various public policy leaders. (SANS Institute)
Related: Berryville Institute of Machine Learning
Best Thing of the Day: Always Fun to Smack Meta
The European Commission issued preliminary findings against the company, saying Meta-owned Facebook and Instagram fell short of their own minimum age restriction of 13 years old.
Worst Thing of the Day: We Will Have to Rebuild Everything in a Few Years
A just-released GAO report found that the US Treasury gave a DOGE employee access to sensitive payment data last year without following IT security rules, giving the staffer temporary access that would allow them to “create, modify, and delete data” for one of the three Bureau of Financial Services systems.
Closing Thought