Five Eyes warn that agentic AI is already in critical systems—and security isn’t keeping up
Trellix hit by significant breach, 15-year-old was busted for French gov't hack, CISA warns of Copy Fail exploits in the wild, Defender flags some legit DigiCert root certs as malware, Sri Lanka arrests 37 Chinese cyberscam operators, US health insurance exchanges share data with big tech, much more


Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
Cybersecurity agencies from the United States, Australia, Canada, New Zealand, and the United Kingdom jointly published guidance urging organizations to treat autonomous AI systems as a core cybersecurity concern, warning that the technology is already being deployed in critical infrastructure and defense sectors with insufficient safeguards.
The guidance by the so-called Five Eyes nations focuses on agentic AI — software built on large language models that can plan, make decisions and take actions autonomously. In order for this software to function, it needs to connect to external tools, databases, memory stores, and automated workflows, allowing it to execute multi-step tasks without human review at each stage.
The agencies’ central message is that agentic AI does not require an entirely new security discipline. Organizations should fold these systems into the cybersecurity frameworks and governance structures they already maintain, applying established principles such as zero trust, defense-in-depth, and least-privilege access. (Greg Otto / CyberScoop)
Related: CISA, The Register, Insurance Business
Cybersecurity firm Trellix disclosed a significant security breach involving unauthorized access to part of its internal source code repository.
The company revealed the incident in an official statement, confirming that unknown threat actors gained access to sensitive development resources.
Trellix, known for its endpoint security and extended detection and response (XDR) solutions, serves thousands of enterprise customers worldwide. Because of this, its internal systems are considered high-value targets for cybercriminals.
According to Trellix, attackers accessed a portion of its internal source code repository. Source code is one of the most sensitive assets for any technology company, as it contains the logic and structure behind its products.
However, the company clarified that the breach appears limited in scope. There is currently no evidence suggesting that critical systems or production environments were compromised. (AnuPriya / CyberPress)
Related: Trellix, Security Affairs, Cyber Security News
A fifteen-year-old hacker is suspected of breaching a French government agency responsible for identity documents and attempting to sell millions of citizens’ personal data, Paris prosecutors said.
The minor was taken into police custody on April 25 on suspicion of involvement in a data breach affecting the National Agency for Secure Documents (ANTS), which processes applications for passports, national identity cards, residence permits, and driver’s licenses.
French authorities did not reveal the suspect’s identity but said he may have operated online under the pseudonym “breach3d,” an alias used to advertise between 12 million and 18 million records for sale on cybercriminal forums earlier this month.
The cybercrime unit of the Paris prosecutor’s office was alerted to the ANTS intrusion last month after the data appeared on underground marketplaces. The agency later confirmed unusual activity on its network and acknowledged that the information being circulated appeared authentic.
Authorities opened an investigation into fraudulent access to and extraction of data from a state-run automated personal data processing system — offenses that carry penalties of up to seven years in prison and a €300,000 ($350,000) fine under French law. (Daryna Antoniuk / The Record)
Related: Tribunal de Paris, France24, The European Conservative, Help Net Security
The US Cybersecurity and Infrastructure Security Agency warned that threat actors have started exploiting the "Copy Fail" Linux security vulnerability in the wild, one day after Theori researchers disclosed it and shared a proof-of-concept (PoC) exploit.
Tracked as CVE-2026-31431, this security flaw was found in the Linux kernel's algif_aead cryptographic algorithm interface and enables unprivileged local users to gain root privileges on unpatched Linux systems by writing four controlled bytes to the page cache of any readable file.
Theori researchers disclosed it on Thursday and shared what they described as a "100% reliable" Python-based exploit that can be used to root Ubuntu 24.04 LTS, Amazon Linux 2023, RHEL 10.1, and SUSE 16 devices.
CISA added the Copy Fail security flaw to its Known Exploited Vulnerabilities (KEV) Catalog, ordering Federal Civilian Executive Branch (FCEB) agencies to patch their Linux endpoints and servers within two weeks, by May 15, as mandated by Binding Operational Directive (BOD) 22-01.
"This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise," the U.S. cybersecurity agency warned. (Sergiu Gatlan / Bleeping Computer)
Related: CISA, Copy Fail, Security Week, Forbes, Heise Online, CyberScoop, crypto.news
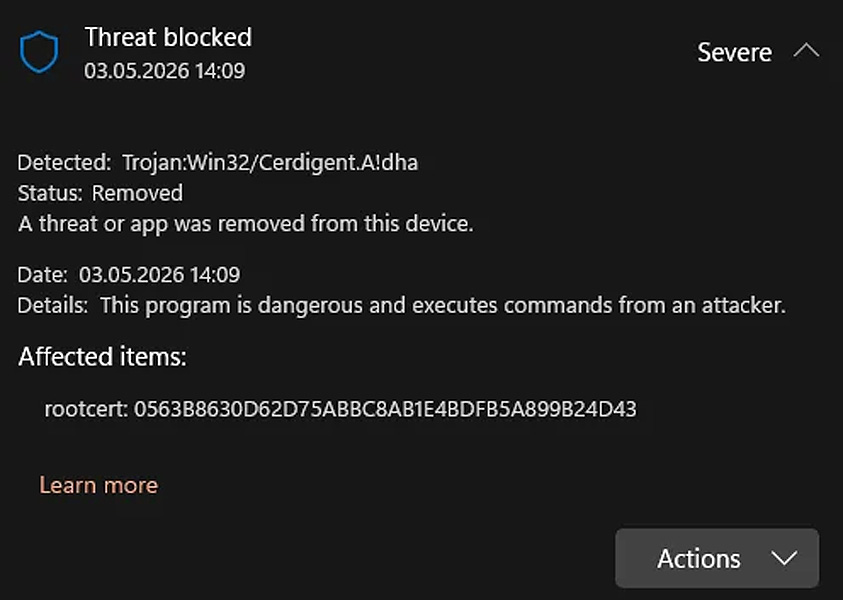
Microsoft Defender is detecting legitimate DigiCert root certificates as Trojan:Win32/Cerdigent.A!dha, resulting in widespread false-positive alerts, and in some cases, removing certificates from Windows.
According to cybersecurity expert Florian Roth, the issue first appeared after Microsoft added the detections to a Defender signature update on April 30th.
Administrators worldwide began reporting that DigiCert root certificate entries were flagged as malware and, on affected systems, removed from the Windows trust store.
These false positives have led to concern among Windows users, with some thinking their devices were infected and reinstalling the operating system to be safe.
Microsoft has reportedly fixed the detections in Security Intelligence update version 1.449.430.0, and the most recent update is now 1.449.431.0. Microsoft confirmed that the false positives were linked to detections for compromised certificates from a recent DigiCert breach. (Lawrence Abrams / Bleeping Computer)
Related: r/cybersecurity, Piunikaweb, Neowin, CyberPress, Bugzilla
Sri Lankan police have arrested 37 Chinese nationals suspected of running a cyberscam center in the capital Colombo, a spokesman said, in the latest crackdown on foreign-run online fraud.
The suspects, aged between 23 and 44 and including one woman, were arrested after a tip-off.
A local police source said 35 tablet computers, 147 mobile phones, and 100 SIM cards were seized at the suspected scam center in the Colombo suburb of Talangama.
The arrests came a month after 152 foreign nationals, mostly Chinese, were detained for allegedly running a cyberscam operation out of a hotel in the island’s northwest. (AFP)
Related: Malay Mail, The Straits Times
Nearly all of the 20 state-run health insurance exchanges in the US have added advertising trackers that transmit user activity back to big tech companies, in some cases sending more data than state officials realized.
The Washington. DC exchange sent applicants’ sex and citizenship responses to TikTok, as well as some race data that the tracker failed to filter out. Virginia’s tool to estimate premiums sent ZIP codes to Meta Platforms. In New York, the marketplace shared the pages applicants visited during enrollment with TikTok, Meta, Snap, and Microsoft's LinkedIn, including when they provided details about incarcerated family members.
No federal data privacy law applies to these enrollment sites. State laws define sensitive data under a patchwork of rules, which privacy experts say are inadequate and inconsistent.
“It is very harmful that these tracking technologies are so embedded in these sites because people would expect this information to be private,” said Sara Geoghegan, senior counsel at the Electronic Privacy Information Center, citing research that indicates people alter their behavior online when they know they’re being surveilled.
The Federal Trade Commission and states can enforce consumer protection laws against unfair practices and misuse of sensitive information, said Geoghegan. “But this case-by-case approach has proven insufficient.” (Tanaz Meghjani, Dhruv Mehrotra, and Surya Mattu / Bloomberg)
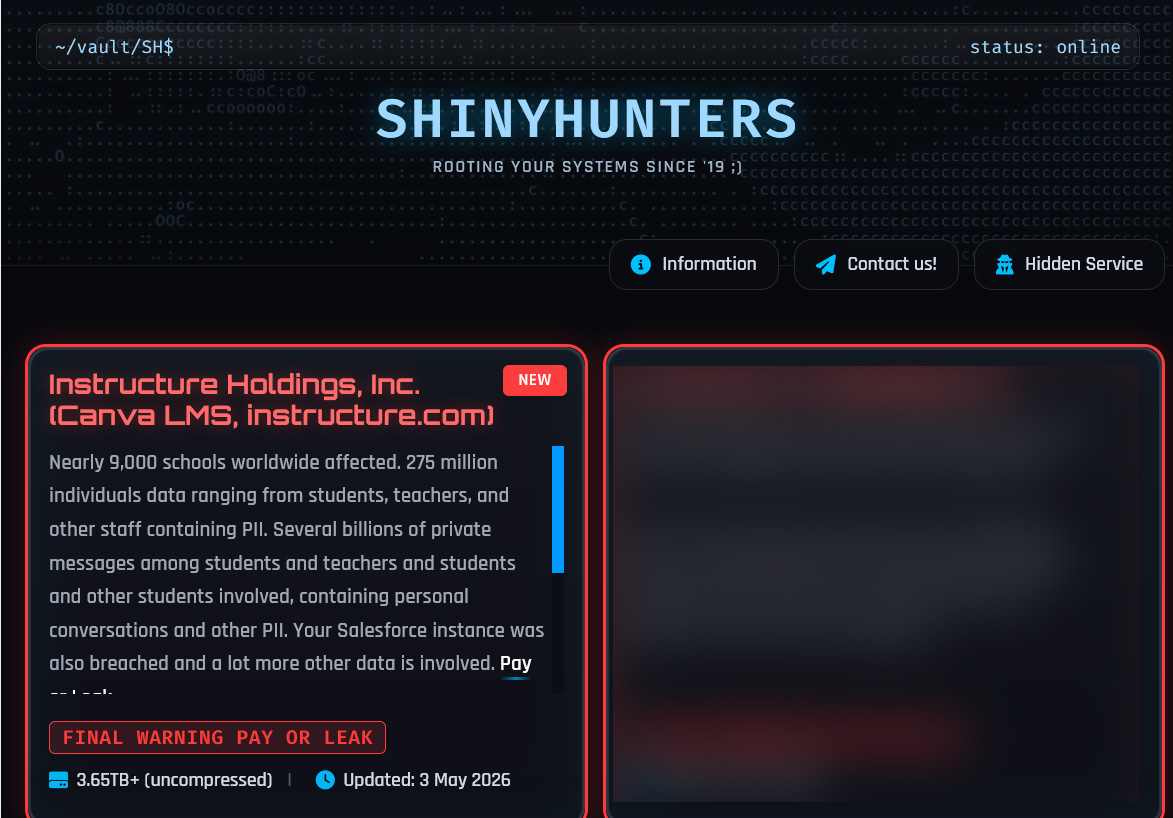
Educational tech giant Instructure has confirmed that data was stolen in a cyberattack, with the ShinyHunters extortion gang claiming responsibility.
Instructure is a U.S.-based education technology company best known for developing Canvas, a widely used learning management system that helps schools, universities, and organizations manage coursework, assignments, and online learning.
On Friday, Instructure disclosed that it suffered a cybersecurity incident and is working with third-party cybersecurity experts and law enforcement to investigate it. On Saturday, the company issued an update stating that the personal information of users was exposed in the breach.
"While we continue actively investigating, thus far, indications are that the information involved consists of certain identifying information of users at affected institutions, such as names, email addresses, and student ID numbers, as well as messages among users," reads the updated statement. (Lawrence Abrams / Bleeping Computer)
Related: Infrastructure, Techzine, Security Week
Cyber security firm Huntress spotted a first-of-its-kind case of a popular server monitoring tool being used to install a backdoor in a Windows system.
Researchers at the company observed a threat actor employing the Komari agent to drop a system-level backdoor without using any malicious infrastructure.
“Huntress SOC and Hunt analysts have spent the last two years documenting the steady drift of open-source DFIR and systems-administration tools into the adversary toolbox: Velociraptor, SimpleHelp, Net Monitor for Employees, ScreenConnect, AnyDesk, Nezha, and Atera,” Huntress said.
What made this particular intrusion possible was the use of stolen VPN credentials, which allowed the threat actor to enable Remote Desktop Protocol, install Komari disguised as a Windows Update Service via NSSM, which then established a persistent WebSocket connection.
In this case, which occurred on 16 April, Huntress was able to contain the incident without any data loss or lateral movement, but other victims may not be so lucky. (David Hollingworth / Cyber Daily)
Related: Huntress
The Pentagon has struck agreements with more technology companies for expanded use of advanced artificial intelligence tools on classified military networks, according to a Defense Department statement and two defense officials briefed on the matter.
NVIDIA, Microsoft, Reflection AI, and Amazon have all newly struck agreements with the US Defense Department “for lawful operational use,” according to the statement. On Friday, the Pentagon posted on X that Oracle Corp. had also joined the roster of technology companies that had agreed to deploy their AI tools on classified networks.
The deals provide the Pentagon with wide leeway to potentially use powerful advanced AI technologies for secret combat operations, such as assisting with targeting. The new terms of usage, including “lawful operational use,” substantially water down some of the limits sought by Anthropic PBC that torpedoed its pact with the Pentagon earlier this year. (Katrina Manson / Bloomberg)
Related: Bloomberg Law, The Hill, SiliconANGLE, New York Times, Reuters, Wall Street Journal, Breitbart, Associated Press, GeekWire, The Tech Portal, Gizmodo, The Next Web, ClearanceJobs, Federal News Network, Engadget, The Guardian, Forbes, Agence France-Presse, crypto.news, NewsMax.com, Barron's Online, Techstrong.ai, Washington Post, Financial Times, Blockonomi, Newser, RTÉ, Washington Times, PYMNTS
RightsCon, the world’s largest conference on human rights and technology, has been canceled just days before it was due to start after the Zambian government told organizers it did not align with “national values."
Zambia’s government had originally welcomed the RightsCon 2026 summit on “human rights in the digital age”, due to be held in the capital, Lusaka, on 5-8 May, but Thabo Kawana, permanent secretary for the Ministry of Information & Media, said last week that the conference would not go ahead to allow time to ensure the gathering “aligns with Zambia’s national values, policy priorities, and broader public interest considerations”.
More than 2,600 activists, technologists, academics, and policymakers were expected to begin arriving in Lusaka over the weekend. The event was to address issues of human rights in the digital age, including online hate, internet shutdowns, AI, surveillance, the militarisation of tech, and disinformation at a time when democratic, women’s, and LGBTQ+ rights are under intense assault.
Rights campaigners have called the decision a blatant act of censorship and part of a broader pattern of suppression of legitimate debate.
Zambian news reports have suggested pressure from China could be behind the surprise move – several Taiwanese delegates had been due to attend, and the conference was being held in a venue donated by China. The conference, now in its 14th year, was held in Taipei last year. (Isabel Choat / The Guardian)
Related: RightsCon, Diggers News, The Cyber Express, Tech Policy Press, Taiwan, Wired, 404 Media
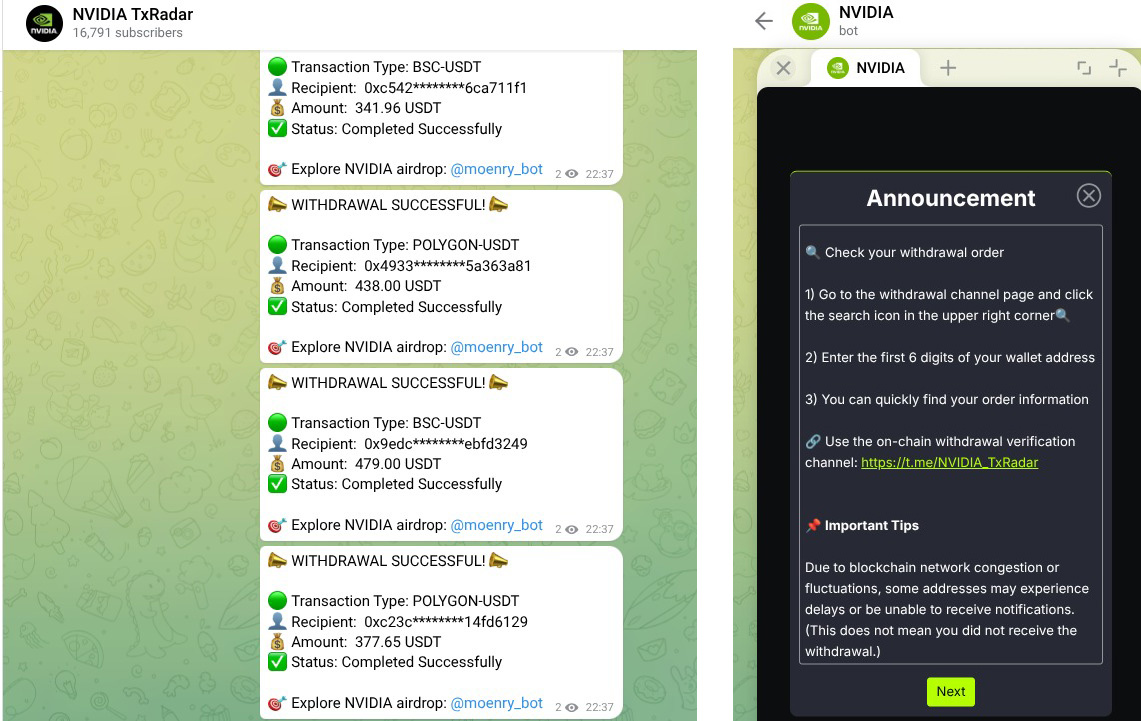
Researchers at CTM360 uncovered a large-scale fraud operation that uses Telegram’s Mini App feature to run crypto scams, impersonate well-known brands, and distribute Android malware.
The platform, dubbed FEMITBOT, is based on a string found in API responses and uses Telegram bots and embedded Mini Apps to create convincing, app-like experiences directly within the messaging platform.
The FEMITBOT platform is used to conduct multiple types of scams, including fake cryptocurrency platforms, financial services, AI tools, and streaming sites.
In various campaigns, threat actors impersonated widely recognized brands to increase credibility and engagement, while using the same backend infrastructure with different domains and Telegram bots. Some of the brands impersonated in this campaign include Apple, Coca-Cola, Disney, eBay, IBM, Moon Pay, NVIDIA, and YouKu. (Lawrence Abrams / Bleeping Computer)
Related: CTM 360, Dataconomy
Several people were falsely identified as thieves by shops using the Facewatch app, a live facial recognition system being rolled out across the UK to clamp down on retail crime.
The company’s website claims that its system has a 99.98% accuracy rate and that last month it sent 50,288 alerts of “known offenders” to shops including B&M, Home Bargains, Sports Direct, Farm Foods, and Spar, which all now use the software.
But those who have been wrongly identified and forced to leave shops, either via the technology itself or human error, say they were given no support, and did not know how to complain about their treatment or prove their innocence.
As facial recognition spreads across police forces and retail stores, UK biometrics commissioners are warning that national oversight is lagging far behind the technology’s rapid expansion. (Jessica Murray / The Guardian)
According to sources, Tom Parker, a security services lead at IBM with some two decades of experience in the cybersecurity industry, has emerged as a potential contender to lead the Cybersecurity and Infrastructure Security Agency after the most recent nominee withdrew from consideration for the role.
Parker does not have prior government experience. As of now, he is the preferred choice for the Trump administration, one of the people said. Homeland Security Secretary Markwayne Mullin has been favoring a CISA director with only private sector experience, one source said.
Parker has held a number of roles in the industry throughout his career. He founded cyber solutions firm Hubble, which was acquired in 2024. He was also inducted as a technology pioneer at the World Economic Forum, and he has for years been a speaker and panelist at Black Hat, an annual cybersecurity conference held in Las Vegas. (David DiMolfetta / NextGov)
US-based cybersecurity company Palo Alto Networks will acquire AI infrastructure startup Portkey for a reported $120 million to $140 million, as it looks to expand its capabilities in protecting AI agents that enterprises are increasingly adopting.
The deal is expected to close in the fourth quarter of Palo Alto Networks’ fiscal year, subject to approvals. (Economic Times)
Related: Palo Alto Networks, CRN, Inc42, Entrackr, InfoRiskToday.com, Pulse 2.0
Best Thing of the Day: Detecting Fake Satellite Signals
Oak Ridge National Laboratory has developed new portable technology that detects GPS spoofing in real time to secure transportation.
Worst Thing of the Day: It's Not Like OT Is Important to Critical Infrastructure or Anything
Operational technology companies have been denied special access to powerful new models from the two major AI leaders, Anthropic and OpenAI.
Bonus Worst Thing of the Day: Flock's Black Eye Just Keeps Getting Darker
Police officers seem to be using Flock data to stalk their exes, partners, and potential love interests.
Closing Thought