Trump eyes AI crackdown after hands-off push falters
EU is talking with Anthropic to test banks with Mythos, DHS intelligence office staff failed to secure smartphones, A Latvian was sentenced to 8.5 years for role in Karakurt ransomware, A Romanian was indicted for bank fraud scheme dating to 2009, CISA unveils CI Fortify for CI entities, much more


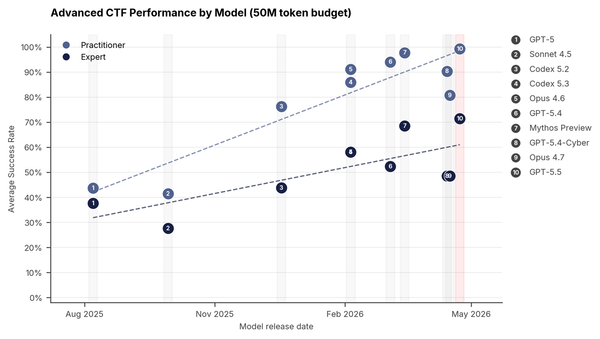
Check out my latest CSO news item that explains how, as Anthropic’s Mythos model raises alarms over AI-enabled cyberattacks, the White House is reconsidering an oversight approach it abandoned on day one of Trump’s second administration.
Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
Donald Trump, who promoted a hands-off approach to artificial intelligence and gave Silicon Valley free rein to roll out the technology, is considering the introduction of government oversight over new AI models, according to US officials and people briefed on the deliberations.
The administration is discussing an executive order to create an AI working group that would bring together tech executives and government officials to examine potential oversight procedures, according to US officials, who declined to be identified in order to discuss deliberations over sensitive policies. Among the potential plans is a formal government review process for new AI models.
In meetings last week, White House officials told executives from Anthropic, Google, and OpenAI about some of those plans, people briefed on the conversations said.
The working group is likely to consider a number of oversight approaches, officials said. But a review process could be similar to one being developed in Britain, which has assigned several government bodies to ensure that AI models meet certain safety standards, people in the tech industry and the administration said.
The discussions signal a stark reversal in the Trump administration’s approach to AI. Since returning to office last year, Trump has been a major booster of the technology, which he has said is vital to winning the geopolitical contest against China. Among other moves, he swiftly rolled back a Biden administration regulatory process that asked AI developers to perform safety evaluations and report on AI models with potential military applications.
Trump has increasingly found himself isolated on the issue of AI. As public concerns mount about the threat that the technology poses to jobs, energy prices, education, privacy, and mental health, Democrats and Republicans have found common ground on the topic. A Pew Research Center poll last year found that 50 percent of Republicans and 51 percent of Democrats said they were more concerned than excited about the increased use of AI. in daily life.
The noninterventionist policy also began changing last month after the start-up Anthropic announced a new AI model called Mythos. Mythos is so powerful at identifying security vulnerabilities in software that it could lead to a cybersecurity “reckoning,” said Anthropic, which declined to release the model to the public. (Tripp Mickle, Julian E. Barnes, Sheera Frenkel, and Dustin Volz / New York Times)
Related: Wall Street Journal, Axios, Engadget, The Information, Tom's Hardware, Mashable, Yahoo Finance, Tom's Guide, Hacker News, r/ArtificialInteligence, r/politics, r/singularity, r/Anthropic, r/OpenAI, r/technology, r/LocalLLaMA, Slashdot
The European Union is in talks with Anthropic PBC about getting its companies and banks tested for any vulnerabilities that the new Mythos AI model uncovers.
“Indeed there are contacts with Anthropic,” said EU Economy Minister Valdis Dombrovskis, speaking Monday night after a meeting of Eurogroup finance ministers in Brussels.
Dombrovskis said Anthropic had briefed the European Commission, the EU’s executive, on the unreleased tool’s “cyber capabilities and risks.” Ultimately, he wants European companies “to have possibilities for this cyber resiliency testing.”
Mythos, which can identify unknown flaws in IT systems, has sent a wave of anxiety across Europe, as Anthropic is limiting access to it. Officials are worried that without any information, Europe’s financial system may become exposed to digital attacks if the technology falls into the wrong hands.
“There are concerns about potential misuse,” Dombrovskis said. “That’s why it is tightly controlled how this model is being used.”
During the gathering, finance ministers pushed for European companies to see the new AI model, according to people familiar with the discussions, who spoke on the condition of anonymity as the talks are private. (Kamil Kowalcze, Nick Heubeck, and Jorge Valero / Bloomberg)
Related: The Next Web, Reuters, Commonwealth Magazine
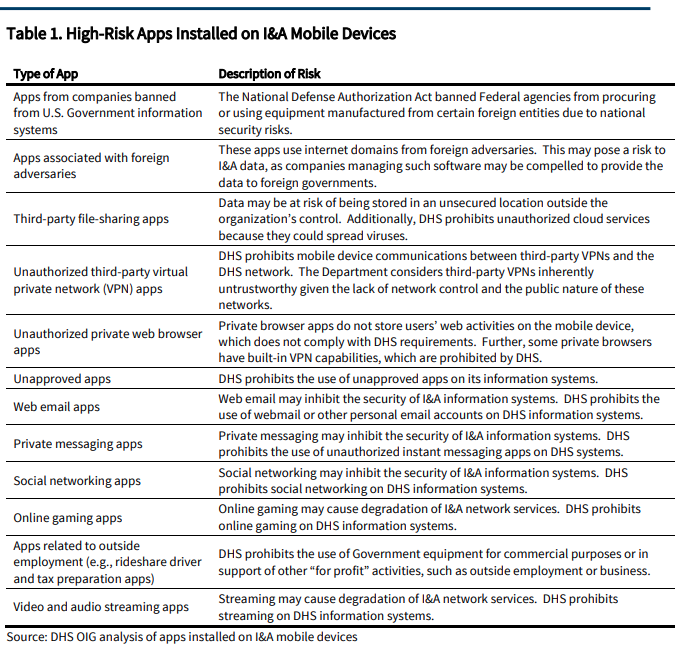
The Department of Homeland Security failed to effectively secure smartphones used by staff in its intelligence office, raising the risk of cyberattacks and unauthorized access to sensitive information, the department’s inspector general said in a report.
The independent watchdog found that the department did not require certain security settings and allowed the office’s employees to download “high-risk apps” on mobile devices, including apps used for streaming or “associated with foreign adversaries.”
The report underscores security vulnerabilities at an office that helps identify national security threats and provides intelligence to state and local partners. Although immigration has been at the forefront of the department under the Trump administration, it was created in the wake of the Sept. 11 attacks and has a broader mission of preventing terrorism and protecting the country from a variety of threats.
In a letter responding to the report, the Department of Homeland Security said it concurred with the watchdog’s recommendations and that it had already made some changes to secure its mobile devices better. The department also cast blame on the Biden administration in a statement. (Madeleine Ngo and Hamed Aleaziz / New York Times)
A Latvian national extradited to the United States was sentenced to 8.5 years in prison for his "cold case" negotiator role in the Russian Karakurt ransomware group.
Deniss Zolotarjovs (Денисс Золотарёвс) of Moscow, Russia, was arrested in Georgia, Eastern Europe, in December 2023, and pleaded guilty in July 2025 to conspiracy to commit wire fraud and money laundering charges filed against him in August 2024 after he was transferred to US custody.
According to court documents, Zolotarjovs (also known online as "Sforza_cesarini") was a member of the Karakurt extortion operation (led by former Conti ransomware gang leaders) that compromised company systems, stole data, and demanded ransom from victims under threat of publicly leaking or selling the data to other cybercriminals.
The FBI linked Zolotarjovs with at least six cases of extortion against American organizations between August 2021 and November 2023, and said that his role was to negotiate so-called "cold case extortions," when communication with the victims had halted without a ransom being paid.
Zolotarjovs played a key role in coercing victims to reconsider their stance against ransom demands, conducting thorough research on targeted companies and analyzing stolen personal and health information to increase psychological pressure. (Sergiu Gatlan / Bleeping Computer)
Related: Justice Department, WHIO, Eurasia Review, Cincinnati Enquirer, WCPO, WLWT, Local12
Gavril Sandu, a Romanian man, was indicted for an extensive bank fraud scheme dating back to 2009, Russ Ferguson, US Attorney for the Western District of North Carolina, announced.
On Nov. 14, 2017, a federal grand jury in Charlotte returned a criminal indictment on Sandu for one count of conspiracy to commit bank fraud and one count of bank fraud.
According to allegations made in the indictment, Sandu was part of a conspiracy that carried out a “vishing” bank fraud scheme.
The indictment states that from May 2009 to October 2010, Sandu and his co-conspirators executed the scheme by hacking into small businesses’ Voice over Internet Protocol (VOIP) systems and then deploying a script to contact financial institution customers and defraud them.
The indictment alleges that Sandu assisted in the conspiracy by obtaining victims’ debit card numbers and PINs from his co-conspirators, which he then used to make magnetic stripe cards with the victims’ fraudulently obtained debit card numbers.
Sandu also allegedly operated as a ‘money mule’, traveling to ATMs to withdraw money and funds from the banks and credit union accounts of the victims of the scheme. Sandu then allegedly provided his co-conspirators with a percentage of the fraudulently obtained victims’ money and kept a portion for himself.
Sandu was arrested in Romania on Jan. 9 and extradited to the US on April 30. He appeared in court on Monday to face a judge for his charges. Following the hearing, Sandu was placed into federal custody.
If convicted, he faces a maximum penalty of 30 years in prison. A federal district court judge will determine any sentence after considering the US Sentencing Guidelines and other statutory factors. (Arri Woodhouse / Queen City News)
Related: Justice Department
The US Cybersecurity and Infrastructure Security Agency (CISA) released guidance to help critical infrastructure (CI) entities across all sectors prepare to operate through a crisis or conflict, continuing vital service delivery even as their systems are under attack.
The new initiative, CI Fortify, strengthens resilience and helps CI entities and their partners maintain a baseline of continuity for critical services during a cyberattack.
The key points in this guidance urge CI entities to start now, if they have not already, to invest and develop isolation and recovery capabilities. When a cyberattack occurs, these two emergency capabilities help ensure the affected organization can still deliver critical services. (CISA)
Related: CI Fortify
The Department of Homeland Security tried to obtain a Canadian man’s location information, activity logs, and other identifying information from Google after he criticized the Trump administration online following the killings of Renee Good and Alex Pretti by federal immigration agents in Minneapolis early this year.
Lawyers for the man, who has not been named, are alarmed in part because they say that the man has not entered the United States in more than a decade. “I don’t know what the government knows about our client’s residence, but it’s clear that the government isn’t stopping to find out,” says Michael Perloff, a senior staff attorney at the American Civil Liberties Union of the District of Columbia who is representing the man in a lawsuit against Markwayne Mullin, the Secretary of DHS, over the summons.
The lawsuit alleges that DHS violated the customs law that gives the agency the power to request records from businesses and other parties.
Perloff argues that the government is using the fact that big tech companies are based in the US to request information it would not otherwise be able to get. “It’s using that geographic fact to get information that otherwise would be totally outside of its jurisdiction,” he says. “I mean, we’re talking about the physical movements of a person who lives in Canada.” (Maddy Varner / Wired)
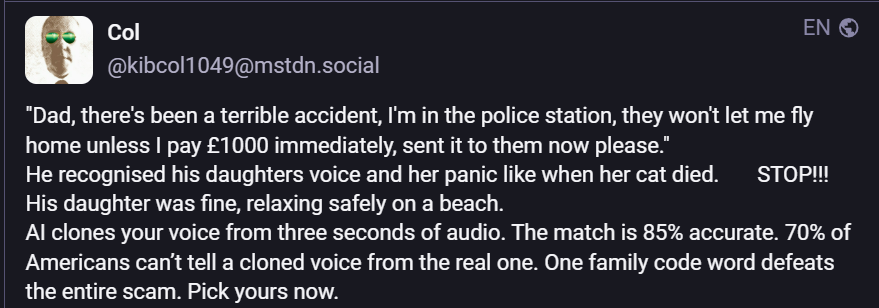
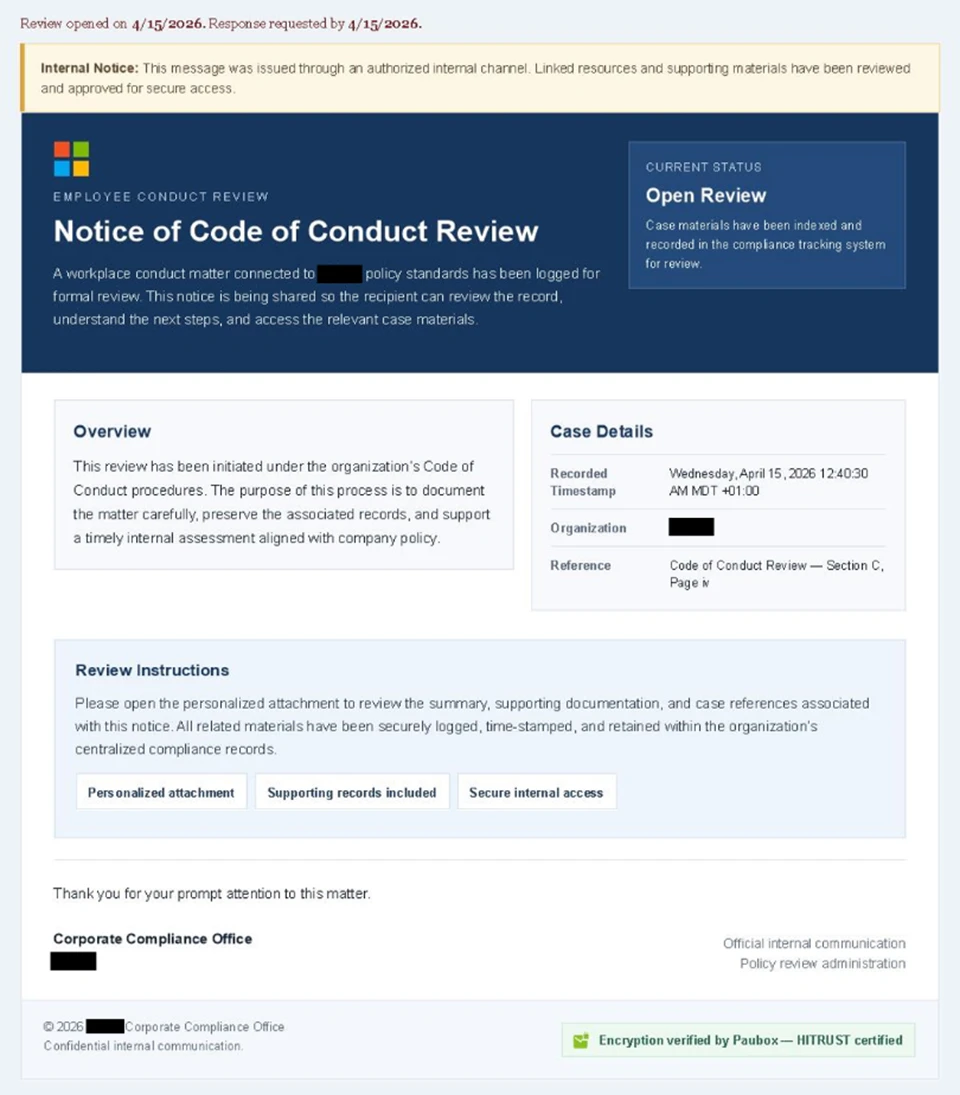
Researchers at Microsoft report that attackers used fake “code of conduct” emails sent through legitimate platforms to trick recipients into visiting bogus sites that stole authentication tokens.
“The campaign targeted tens of thousands of users, primarily in the United States, and directed them through several stages of CAPTCHA and intermediate staging pages designed to reinforce legitimacy while filtering out automated defenses, Microsoft said. “The lures in this campaign used polished, enterprise-style HTML templates with structured layouts and preemptive authenticity statements, making them appear more credible than typical phishing emails and increasing their plausibility as legitimate internal communications. “
Attackers used alarming, time-sensitive messages to pressure victims into action, leading them to a fake but legitimate-looking sign-in page. This adversary‑in‑the‑middle (AiTM) phishing flow lets attackers intercept authentication tokens in real time, bypassing weak MFA. Microsoft urges training, anti-phishing tools, secure browsers, and SmartScreen protections to defend against such threats.
Most victims (92%) were in the US, mainly in healthcare and finance. (Pierluigi Paganini / Security Affairs)
Related: Microsoft, Help Net Security
Cryptocurrency Ripple announced that it is now sharing its internal threat intelligence on North Korean hackers with the Crypto ISAC, in a move that reframes how the sector is responding to a shift in DPRK attack methodology.
Ripple is now feeding Crypto ISAC the kind of profile data that makes that pattern legible across companies. LinkedIn profiles, email addresses, locations, contact numbers — or the connective tissue that lets a security team recognize the candidate they just interviewed as the same operative who failed background checks at three other firms last week.
Lazarus Group's reach across the crypto sector is now visible enough that it has begun reshaping legal proceedings as well as security ones.
On Monday, an attorney representing victims of North Korean terrorism served restraining notices on Arbitrum DAO, arguing that the 30,765 ETH frozen after April's Kelp bridge exploit is North Korean property under US enforcement law.
Lending company Aave has since disputed that filing in support of Arbitrum, arguing that a "thief does not gain lawful ownership of stolen property simply by taking it."
The Kelp breach had drained $292 million in ether (ETH) and was also publicly attributed to Lazarus Group operatives, putting April's Drift and Kelp losses together at more than half a billion dollars tied to a single state actor in the span of a single month. (Shaurya Malwa / CoinDesk)
Related: CryptoISAC, CoinGape, crypto.news, The Crypto Times, CryptoPotato, Blockonomi, The Block, Forklog, Bitcoin Foundation, Intellectia, Cryptopolitan, Crypto Economy
A potential cyberattack on the San Diego Community College District network was thwarted over the weekend, according to messages from the district.
San Diego City College students received an alert with details about the attack on Monday morning.
“SD CITY COLLEGE ALERT: Our IT team stopped a cyberattack on our network this weekend. Systems and websites may be intermittently unavailable today while we restore services. Your data is secure. No action needed. We’ll update you as services come back online. Thank you for your patience,” the message read.
In a subsequent message, the district detailed that its network was down and that some offices may be closed until the issue is resolved.
In a message sent district-wide at 4:14 p.m., Chancellor Greg Smith announced the network outage may carry over into tomorrow, calling the efforts to access the system “highly sophisticated and coordinated.” (Rosemary Archer / City Times Media)
Related: KUSI News, San Diego Union Tribune
The UK's National Health Service (NHS) is ordering all of its technology leaders to temporarily wall off the organization's open source projects over concerns relating to advanced AI and Anthropic's Mythos.
According to guidance shared internally within the organization and seen by The Register, GitHub repositories must be set from public to private by May 11.
The guidance reads: "Public repositories materially increase the risk of unintended disclosure of source code, architectural decisions, configuration detail, and contextual information that may be exploited – particularly given rapid advancements in AI models capable of large-scale code ingestion, inference, and reasoning (e.g. developments such as the Mythos model)."
It also states GitHub repos should not be public "unless there is an explicit and exceptional need." The NHS's Engineering Board approved the decision.
An NHS England spokesperson said this was merely a temporary measure enacted while the organization shores up its cybersecurity posture. (Connor Jones / The Register)
Related: Linuxiac, Terence Eden's Blog, New Scientist, Digital Health
Sistemi Informativi, a company wholly owned by IBM Italy that provides IT infrastructure management for key public and private institutions, was hit by a significant breach in late April, IBM confirmed.
Sistemi Informativi is central to Italy’s digital infrastructure, managing systems for public agencies and key industries. Its outage quickly raised alarms among cybersecurity authorities and critical infrastructure operators.
IBM said that it had “identified and contained a cybersecurity incident” and had activated incident response protocols involving both in-house and external specialists. The company said systems are now stable and services restored, but gave no details on the breach’s scope. Its website stayed offline for hours during containment.
While forensic investigations are still ongoing, multiple intelligence sources cited by La Repubblica point to the China-linked cyber espionage group Salt Typhoon. If confirmed, this would mark one of the most ambitious cyberattacks on the backbone of Italy’s public infrastructure in recent years. (Pierluigi Paganini / Security Affairs)
Related: Repubblica, SC Media
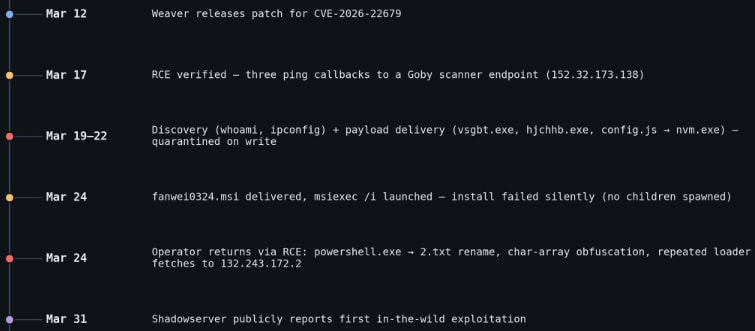
Researchers at threat intelligence company Vega report that hackers have been exploiting a critical vulnerability (CVE-2026-22679) in the Weaver E-cology office automation since mid-March to run discovery commands.
Weaver E-cology is an enterprise office automation (OA) and collaboration platform used for workflows, document management, HR, and internal business processes. Chinese organizations primarily use the product.
The attacks started five days after the software vendor released a security update to address the issue, and two weeks before disclosing it publicly.
Vega documented the malicious activity and reported that the attacks lasted roughly a week, each with several distinct phases.
Users of Weaver E-cology 10.0 are recommended to apply the security updates available through the vendor’s site as soon as possible. (Bill Toulas / Bleeping Computer)
Related: Vega, Weaver, Security Week
A new disclosed cPanel flaw tracked as CVE-2026-41940 is being mass-exploited to breach websites and encrypt data in "Sorry" ransomware attacks.
This week, an emergency update for WHM and cPanel was released to fix a critical authentication bypass flaw that allows attackers to access control panels.
WHM and cPanel are Linux-based web hosting control panels for server and website management. While WHM provides server-level control, cPanel provides administrator access to the website backend, webmail, and databases.
Soon after its release, it was reported that the flaw was being actively exploited in the wild as a zero-day, with exploitation attempts dating back to late February.
Internet security watchdog Shadowserver now reports that at least 44,000 IP addresses running cPanel have since been compromised in ongoing attacks. (Lawrence Abrams / Bleeping Computer)
Related: Security Week, Bleeping Computer, Security Affairs, TechCrunch
A 19-year-old woman is suing the makers of a dating app, alleging they took a video she posted online, repurposed it without her consent into an advertisement for the app, then used geofencing to target that ad to people in her area.
According to the lawsuit filed Apr. 28 in Tennessee and an interview with her lawyer, the company allegedly used geotargeting to serve the ads on platforms like Snapchat to users near her, including men in her own dormitory.
The allegations, if proven, offer another example of how modern technology has made it easier than ever today for bad actors to imitate, objectify, profit from, and harass individuals, often women. Recent laws like the Take It Down Act have focused particularly on the use of AI to create sexualized imagery of their victims. In this case, the lawsuit alleges that Meete used not AI, but simple video editing, a voiceover, and geofencing to create the same kind of deception. (Derek B. Johnson / CyberScoop)
The UK online safety group Internet Matters surveyed over 1,000 UK children and their parents about the new requirements mandating stronger age checks under the Online Safety Act and discovered that many children saw age verification as an easy-to-bypass hurdle rather than something that kept them genuinely safe.
A full 46 percent of children even said that age checks were easy to bypass, while just 17 percent said that they were difficult to fool. The methods kids use to fool age gates vary, but most are pretty simple: There's the classic use of a video game character to fool video selfie systems, while in other instances, children reported just entering a fake birthday or using someone else's ID card when that was required.
The report even cites cases of children drawing a mustache on their faces to fool age detection filters. (Brandon Vigliarolo / The Register)
Related: Internet Matters
Cisco announced the completion of its acquisition of Israeli cybersecurity company Astrix Security.
Calcalist has learned that the final purchase price is approximately $400 million. Astrix’s capabilities will be integrated into Cisco’s broader security platform, including Cisco Identity Intelligence and its Zero Trust applications such as Duo and Secure Access. (Meir Orbach / CTech)
Related: Cisco Blogs, The Information, Network World, CRN, Security Week, Silicon Angle, MSSP Alert
Best Thing of the Day: Never Cross a Cybersecurity Journalist
TechCrunch cybersecurity journalist Zack Whittaker sued the DOJ and FBI in the US District Court for the District of Columbia to compel the release of files that he had originally requested under the Freedom of Information Act to learn why the FBI visited him regarding a story he wrote about a hack of one of Mexico's embassies.
Worst Thing of the Day: Meet the New Media, Same as the Old Media
According to NewsGuard, Anthropic’s AI chatbot Claude repeated false claims 15 percent of the time when it was asked about pro-Kremlin falsehoods in the voice of typical users, citing Russian state-affiliated media every time.
Closing Thought