GPT-5.5 aces UK cyber trials, tops rivals in AISI tests
NSA is testing Mythos, Anthropic publishes Claude Security for Claude Enterprise, Flock spied on a kid's gym room, DPRK hackers have stolen $577m in crypto year-to-date, Rhysida demands ransom from Stelia Aerospace NA, Two ransomware negotiators sentenced to prison, much more
Metacurity is the only daily cybersecurity briefing built for clarity, not agendas—no vendor spin, no echo chamber, just sharp, original aggregation and analysis of what actually matters to security leaders.
If you rely on Metacurity to cut through the noise on policy, industry shifts, and security research, consider supporting us with a paid subscription. Independent coverage like this only exists because readers decide it’s worth it.
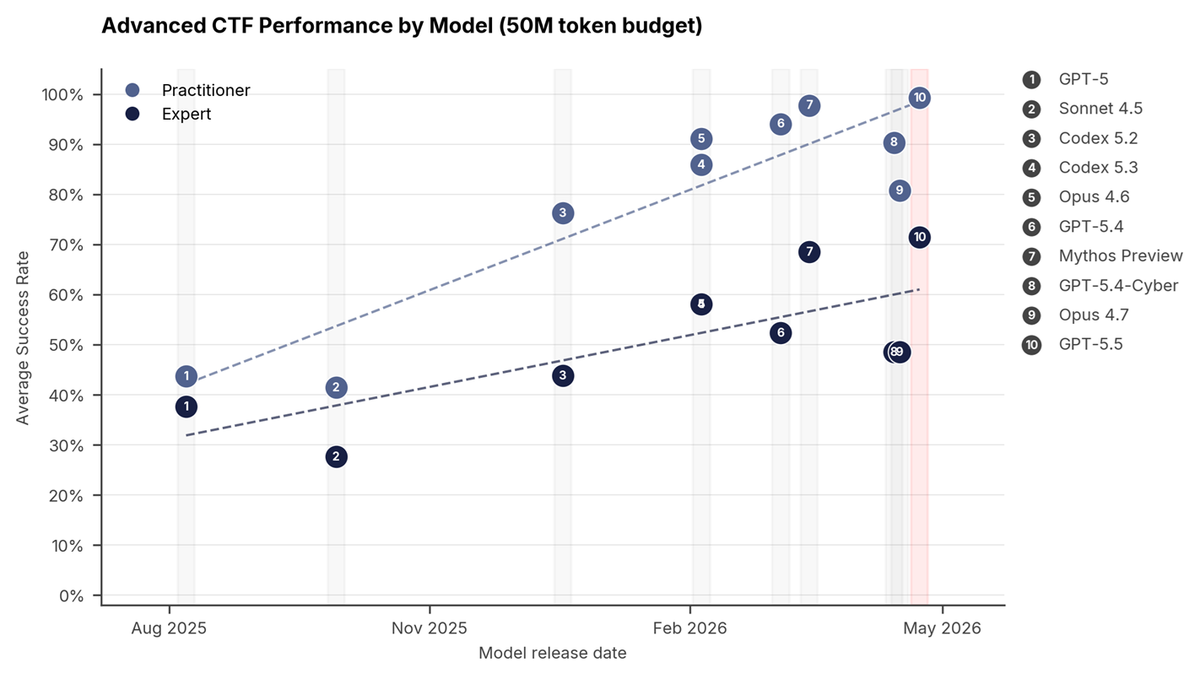
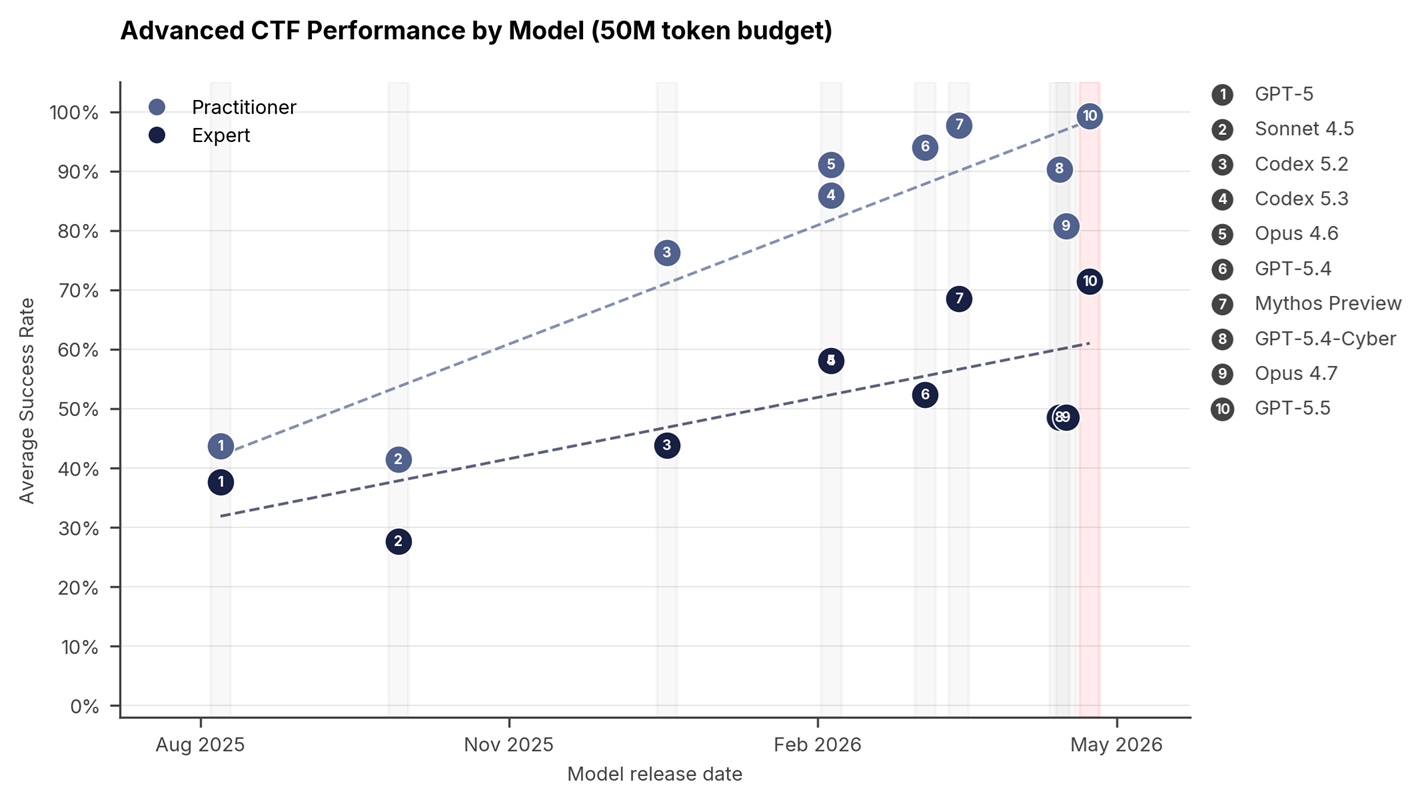
The UK AI Security Institute (AISI) reports that its evaluations on OpenAI's GPT-5.5. shows that it is one of the strongest models it has tested on its cyber tasks and is the second model to solve one of our multi-step cyber-attack simulations end-to-end.
AISI used a suite of 95 narrow cyber tasks across four difficulty tiers, which test a broad range of cybersecurity skills. Its cyber tasks are built in the capture-the-flag (CTF) format and are designed to evaluate key capabilities like vulnerability research and exploitation by testing the model on tasks such as reverse engineering, web exploitation, and cryptography.
AISI's advanced suite comprises two levels: Practitioner and Expert. On the Expert-level tasks, GPT-5.5 achieves an average pass rate of 71.4% (±8.0%, 1 standard error of the mean), compared to 68.6% (±8.7%) for Mythos Preview, 52.4% (±9.8%) for GPT-5.4, and 48.6% (±10.0%) for Opus 4.7.
On this measure, GPT-5.5 may be the strongest model AISI has tested. (AISI)
Related: Simon Willison's Weblog, Rohan's Bytes, r/OpenAI, r/singularity, The Information, The Decoder
According to sources, the National Security Agency has been testing the capabilities of Anthropic PBC’s new artificial intelligence model to find cybersecurity vulnerabilities in popular software, including Microsoft products.
NSA officials studying the Mythos model have been impressed by its speed and efficiency in searching for potential security flaws, the sources said.
A group of NSA employees has been examining Mythos, as have cybersecurity professionals at major technology companies and financial institutions, the person and official said.
The NSA staff, including members of its cybersecurity directorate, have been testing the tool’s power to find security flaws in Microsoft programs and widely used software from other companies, said the US officials, declining to identify the other firms.
The NSA is comparing the results from those Mythos tests with the agency’s other tools and processes for cybersecurity research, said the sources. (Jake Bleiberg / Bloomberg)
Related: The Information, XM Cyber
Anthropic has published Claude Security today for Claude Enterprise customers globally, according to company materials.
The public beta turns the February Claude Code Security research preview into a dedicated defensive product powered by Claude Opus 4.7. The release gives security teams codebase scanning, validated findings, and patch workflows, while Anthropic faces government scrutiny over who should receive its more powerful Mythos model.
Claude Security can scan a full repository or a targeted directory, Anthropic said in the launch materials. Rather than search only for known vulnerable patterns, the product is meant to read source code across files, trace data flows, examine module interactions, and reason through logic flaws that simpler scanners can miss.
The April 30 beta also adds scheduled scans, documented dismissals, and CSV or Markdown exports for audit and ticketing systems. That turns Claude Security from a one-off scan into something security teams can retest, triage, close, and explain later.
Claude Security is not Mythos Preview, the restricted model Anthropic placed at the center of Project Glasswing. That distinction matters because Mythos remains behind a limited program, while Claude Security is moving into public beta for Claude Enterprise customers. (Marcus Schuler / Implicator.AI)
Related: Claude, The Economic Times, Inc, ZDNET, SiliconANGLE, The New Stack, The Verge, SecurityWeek, DevOps.com
Residents of Atlanta suburb Dunwoody have been rocked by the revelation that sales employees at Flock have been accessing sensitive cameras in the town to demonstrate the company’s surveillance technology to police departments around the country.
The cameras accessed have included surveillance tech in a children’s gymnastics room, a playground, a school, a Jewish community center, and a pool.
Flock has taken issue with the way that residents and activists have characterized the access, but confirmed that the camera access did happen as part of its sales demonstrations. A blog post by Jason Hunyar, a Dunwoody, Georgia resident who learned about Flock accessing the city’s cameras by obtaining Flock access logs via a public records request, is called “Why Are Flock Employees Watching Our Children?”
Flock has pushed back against this characterization on social media, in a blog post, at city council meetings, and in a statement to 404 Media: “The city of Dunwoody is one city in our demo partner program,” a Flock spokesperson told 404 Media. “The cities involved in this program have authorized select Flock employees to demonstrate new products and features as we develop them in partnership with the city. Moreover, select engineers can access accounts with customer permission to debug or fix any issues that may arise. No one is spying on children in parks, as the substack incorrectly asserts.” (Jason Koebler / 404 Media)
Related: Flock, Jason Hunyar
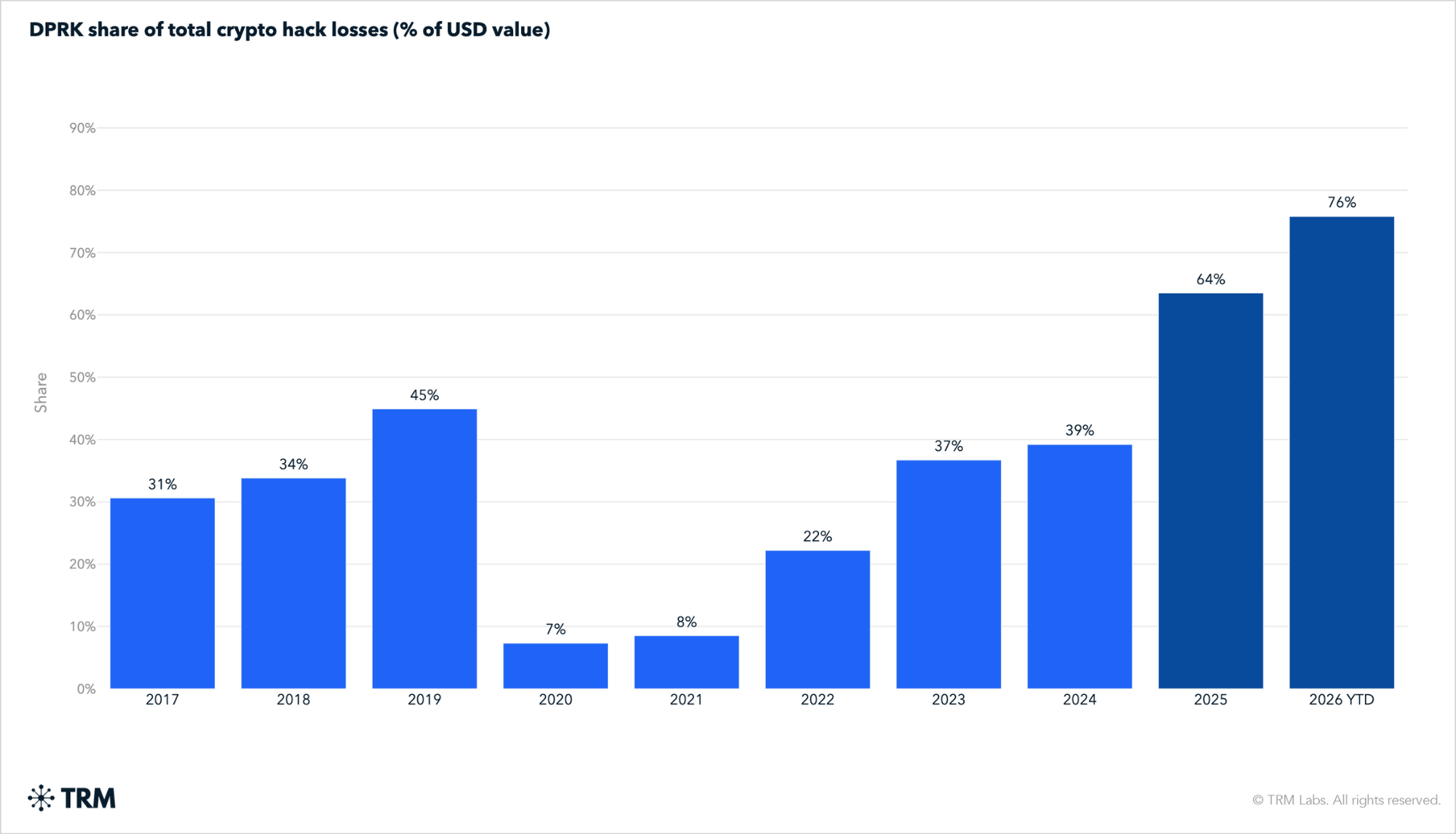
According to TRM Labs, North Korean hackers have stolen over $6 billion in cryptocurrency since 2017, with approximately $577 million stolen year-to-date in 2026, accounting for 76% of all crypto hack losses this year, highlighting the severe threat posed by state-sponsored cybercrime to the digital asset industry.
According to TRM Labs, North Korean hackers have stolen over $6 billion in cryptocurrency since 2017, with approximately $577 million stolen year-to-date in 2026, accounting for 76% of all crypto hack losses this year, highlighting the severe threat posed by state-sponsored cybercrime to the digital asset industry. (Ohris M. Greyoon / Intellectia)
Related: TRM Labs, CoinDesk, International Business Times, Decrypt, NewsBTC, Blockchain.News, GovInfoSecurity.com
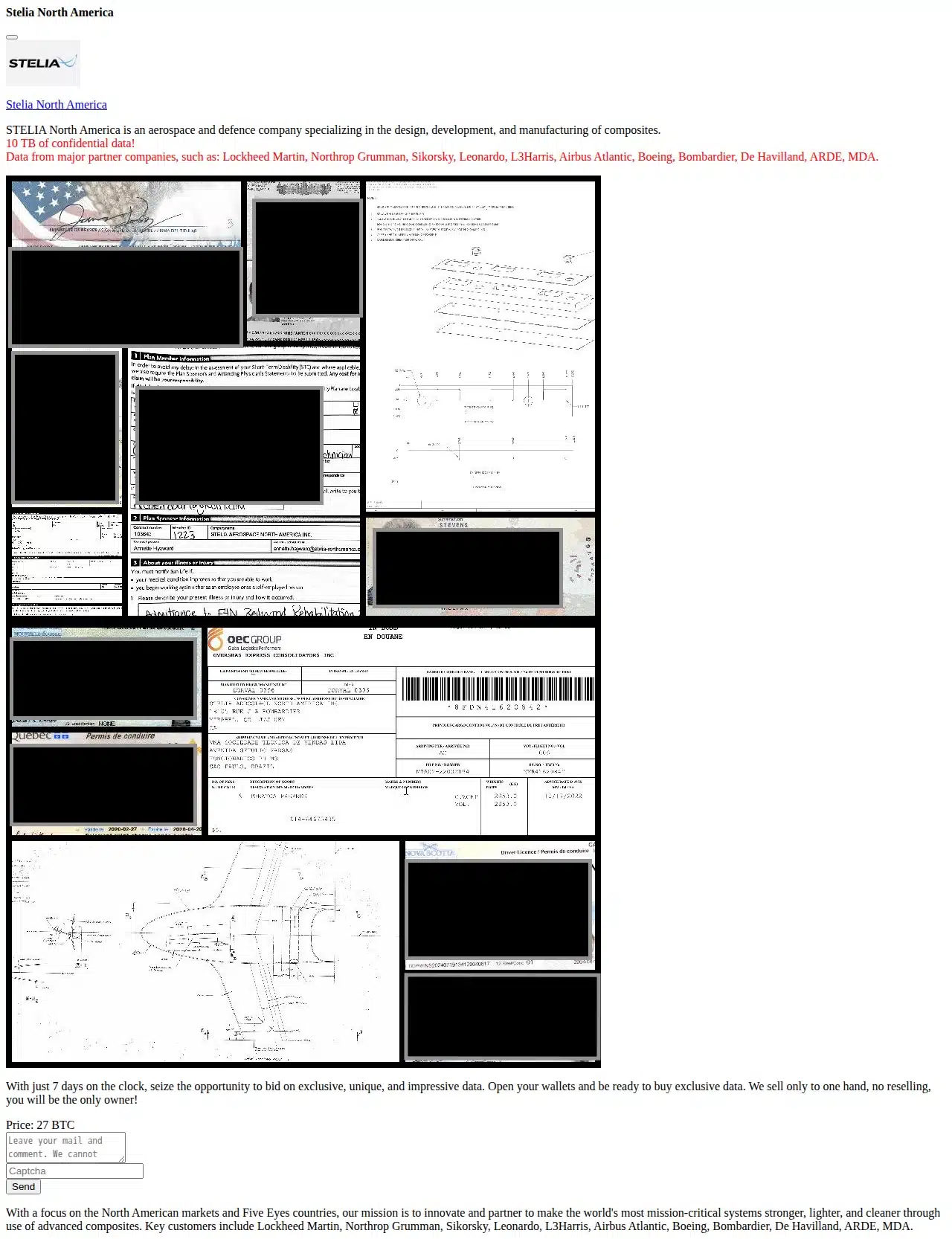
Ransomware group Rhysida added STELIA Aerospace North America to its data leak site, issuing a 27 bitcoin ($2.07 million) ransom demand for 10 TB of data to be paid within seven days, an attack that STELIA has confirmed.
The company said: “We confirm that Stelia North America (a subsidiary of Airbus Atlantic based in Nova Scotia) recently detected a cybersecurity incident and is currently investigating claims made online by a third party.
“Upon detection, we immediately activated our cyber defence protocols and took proactive measures, including isolating affected systems, to mitigate the threat.
“We can confirm this incident is strictly contained to the Stelia North America IT environment and does not impact the broader Airbus Atlantic network.
As part of its proof pack, Rhysida uploaded various documents, including screenshots of identity documents, an employee benefit plan form, and several technical drawings.
It also lists the customers STELIA works with, suggesting data was also stolen from these major partners, including Lockheed Martin, Northrop Grumman, Sikorsky, Leonardo, L3Harris, Airbus Atlantic, Boeing, Bombardier, De Havilland, ARDE, and MDA. (Rebecca Moody / Comparitech)
Related: Aviation Business, Manufacturing.net
Two former employees of cybersecurity incident response companies Sygnia and DigitalMint, Ryan Clifford Goldberg (a former Sygnia incident response manager) and Kevin Tyler Martin (a DigitalMint ransomware negotiator), were sentenced to four years in prison each for targeting US companies in BlackCat (ALPHV) ransomware attacks.
Together with 41-year-old Angelo Martino, a third accomplice who also pleaded guilty in April, the two acted as BlackCat ransomware affiliates between May 2023 and November 2023, breaching the networks of multiple victims across the United States.
According to court documents, they paid a 20% share of ransoms in exchange for access to BlackCat's ransomware and extortion platform.
The list of victims includes a Maryland pharmaceutical company, a Tampa medical device manufacturer, a California engineering firm, a Virginia drone manufacturer, and a California doctor's office. (Sergiu Gatlan / Bleeping Computer)
Related: Justice Department, CyberScoop
The US Federal Bureau of Investigation (FBI) warned the transportation and logistics industry of a sharp rise in cyber-enabled cargo theft, with estimated losses in the United States and Canada reaching nearly $725 million in 2025.
This represents a 60% surge in losses compared to the previous year, fueled by criminals increasingly using hacking and impersonation tactics to hijack high-value freight. Confirmed cargo theft incidents have risen 18 percent last year alone, while the average value per theft grew 36 percent to $273,990, due to more selective targeting of high-value loads.
The bureau said in a public service announcement on Wednesday that threat actors have been infiltrating the computer systems of freight brokers and carriers through spoofed emails and fake web links since at least 2024.
Once inside, criminals post fraudulent listings on online load boards (digital marketplaces used by shippers, brokers, and carriers) and impersonate legitimate companies to divert shipments. (Sergiu Gatlan / Bleeping Computer)
Related: IC3, Security Week, Freight Waves, The Record, Cyber Press

Over 1,800 developers were affected by the Mini Shai-Hulud supply chain attack that hit the PyPi, NPM, and PHP ecosystems over the past two days.
Attributed to the TeamPCP hacking group, the campaign was first spotted on April 29, after malicious versions of four SAP NPM packages were caught delivering information-stealing malware and attempting to propagate to other packages.
The malware would collect credentials, keys, tokens, and other secrets from the infected machines and publish the data to GitHub repositories containing the hardcoded description “A Mini Shai-Hulud has Appeared”.
The same description has been used in a fresh round of infections linked to the compromise of the Lightning PyPi package and the intercom-client NPM package, which have a combined monthly download count of nearly 10 million.
According to Ox Security, over 1,800 repositories containing stolen developer credentials have been created as part of the Mini Shai-Hulud attacks. The campaign appears to be a continuation of the Shai-Hulud supply chain attacks from late 2025. (Ionut Arghire / Security Week)
Related: Ox Security, Wiz, Aikido, Sophos, Dark Reading, The Register
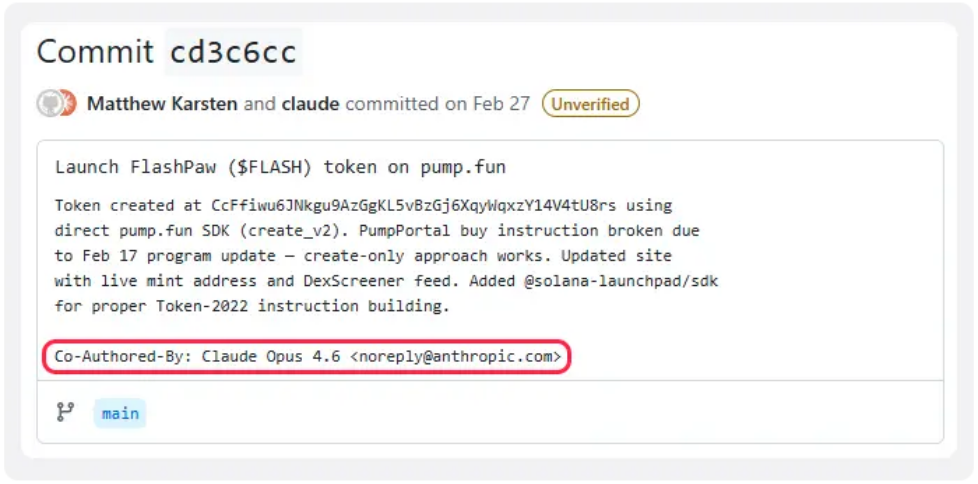
Researchers at ReversingLabs report that a malicious npm dependency linked to an AI-assisted code commit has been found stealing sensitive data and exposing crypto wallets.
The package, disguised as a validation tool, enabled attackers to exfiltrate secrets from infected environments and access funds.
The activity, tracked as PromptMink, involved the package @validate-sdk/v2, which was added to an autonomous trading agent in February 2026. Anthropic's Claude Opus model reportedly co-authored the commit.
Attribution points to a North Korean state-sponsored actor, Famous Chollima (also known as APT37 or Reaper), which has been active since 2018 and is known for targeting cryptocurrency developers. The group relied on a two-layer package strategy that separates legitimate-looking tools from hidden malicious payloads.
Packages presented as useful Web3 utilities were used to attract adoption, while secondary dependencies quietly delivered the malware. This approach allowed attackers to maintain trust in widely visible components even as malicious elements were repeatedly replaced behind the scenes.
Across a seven-month period, the researchers tracked more than 60 packages and over 300 versions tied to the campaign, indicating sustained activity and refinement of delivery techniques. (Alessandro Mascellino / Infosecurity Magazine)
Related: ReversingLabs, Cyber Security News, Cyber Press
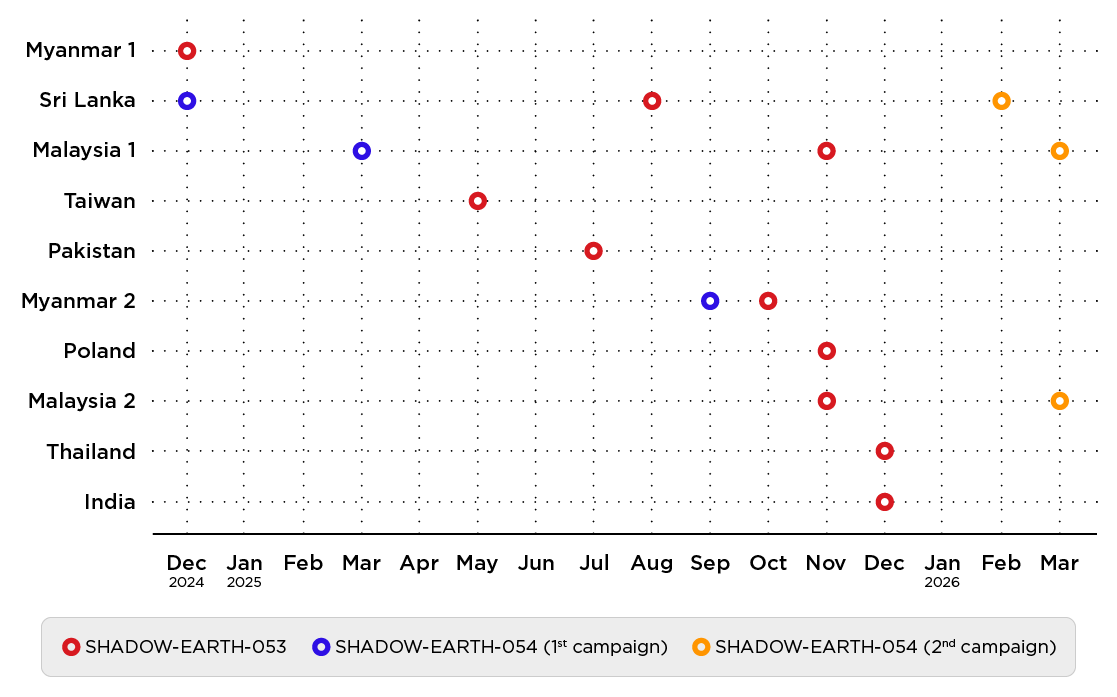
Trend Micro researchers report that a novel China-linked threat group infiltrated more than a dozen critical networks in Poland, Asian countries, and possibly beyond, beginning in December 2024 and with activity uncovered as recently as this month.
They say the new group, which they track as Shadow-Earth-053, targeted government agencies, defense contractors, technology firms, and the transportation industry. The Chinese spies typically gain initial access to victim environments via vulnerable Microsoft Exchange Servers.
In "multiple" of these intrusions, they compromised victim organizations up to 8 months before deploying ShadowPad, a custom backdoor used by China's APT41 for almost a decade. They have been shared among multiple China-aligned groups since 2019.
About half of the victims were also compromised by a related group, Shadow-Earth-054, which exploited the same vulnerabilities and shared identical tool hashes and overlapping techniques with Shadow-Earth-053. The 054 group has some network overlaps with Chinese crews tracked as CL-STA-0049 by Palo Alto Networks' Unit 42, REF7707 by Elastic Security Labs, and Earth Alux. (Jessica Lyons / The Register)
Related: Trend Micro, Cyber Security News, Cyber Press, Crypto News
The Federal Communications Commission proposed new restrictions that seek to block companies flagged as national security threats from gaining easy access to the US telecom market.
The agency voted to launch a rulemaking that would bar entities on its “Covered List” from receiving automatic authorization to provide domestic telecom services under Section 214 of the 1934 Communications Act, a process many carriers have relied on for decades to begin operating without a full commission review.
The change would mark a notable expansion of how the FCC uses its national security authorities. Under the proposal, Covered List entities would be cut off from so-called “blanket” Section 214 authority and instead face case-by-case review if they attempt to provide service, the agency said.
The Covered List, created under the 2019 Secure and Trusted Communications Networks Act, already blocks the use of federal funds to buy or maintain equipment from designated companies. But it doesn’t automatically prevent those firms from securing FCC approvals or offering service in the United States.
The FCC is also seeking input on whether to revoke existing authorizations for companies already operating under that framework and whether US carriers should be barred from interconnecting — or directly linking their networks to exchange traffic — with Covered List providers unless they receive explicit approval. (David DiMolfetta / NextGov/FCW)
Related: FCC
The US Federal Communications Commission approved new regulations designed to crack down on robocalling, protect telecommunications networks from cyberattacks, and further vet equipment-testing labs based overseas.
Commissioners unanimously passed a measure to strengthen telecom companies’ “Know Your Customer” requirements for verifying callers’ identities. Among the potential solutions being considered are requiring telecoms to verify a customer’s name, address, government ID, and alternative phone numbers prior to enabling their service.
In a statement ahead of the vote, FCC Chair Brendan Carr said that under current rules, some telecoms “do the bare minimum” to verify callers and have “become complicit in illegal robocalling schemes.”
“As we have continued to investigate the problem of illegal robocalls over the last year, it has become clear that some originating providers are not doing enough to vet their customers, allowing bad actors to infiltrate our U.S. phone networks,” he said.
Current rules require telecoms to take “affirmative, effective” measures to verify callers and block illegal calls, but in practice, this system has largely relied on self-attestation from the companies. Because a single call can traverse multiple networks, carriers must also often rely on identity verification performed by other telecoms. (Derek B. Johnson / CyberScoop)
Related: FCC, ACA International
The Minnesota Senate passed the country’s first ban on “nudification” apps 65-0, addressing one of the main sources of nonconsensual deepfakes.
The bill was passed by the state House last week and now needs the governor’s signature to become law.
Advocates are optimistic that Gov. Tim Walz, a Democrat, will sign legislation soon.
This bill was the first attempt in the country to ban websites or apps that promote digital undressing, where photographs of fully clothed people can be uploaded and manipulated with generative AI to appear nude. (Jasmine Mithani / 19th News)
Related: Kare11, Patch, Marshall Radio, MPR
The US House passed a 45-day clean extension of Section 702 of FISA — the government's warrantless surveillance authority — after the Senate failed to accept the House's long-term extension of the program, kicking yet another fight just weeks down the road.
Congressional leaders now have an additional 45 days to try to break the impasse. (Kate Santaliz / Axios)
Related: CNBC, CNN, Politico, The Guardian, The New York Times, The Hill, NPR, The Record, The Verge, CyberScoop
A database belonging to an Alberta separatist group was shut down as elections officials and Mounties probe an alleged voter-list privacy breach affecting up to three million Albertans.
“The RCMP has initiated an investigation and is working with other law enforcement partners in the province to determine if any offences have been committed,” Alberta’s Mounties said in a statement.
Elections Alberta officials were in court, where they argued for and were granted an injunction to have the group, called the Centurion Project, be ordered to take down the database.
Redman said the agency believes the list was originally given legally to the pro-independence Republican Party of Alberta. But that list allegedly ended up in the hands of the Centurion Project, which created a publicly accessible database of the private information. (The Canadian Press)
Related: The Hamilton Spectator, CBC, Calgary Herald, The Globe and Mail, CTV News
The Senate Foreign Relations Committee advanced Adam Cassady to be Donald Trump’s pick to be the country’s next cyber ambassador.
Cassady, who was nominated last month to helm the State Department’s Bureau of Cyberspace and Digital Policy, was approved by a vote of 17-5. Five panel Democrats voted against him. His nomination now goes to the full Senate.
The bureau, which by statute must be helmed by an ambassador, has been without a leader since the start of the second Trump administration and has seen its portfolio divided up between three offices as part of a larger department reshuffle.
During his confirmation earlier this month, Cassady, a senior leader at the National Telecommunications and Information Administration, said the digital infrastructure that underpins the global economy, such as subsea cables, semiconductors, and satellites, “is now as strategically significant as sea lanes, airspace, and energy routes were in earlier eras.”
Safeguarding that infrastructure is “central to preserving American power and prosperity,” he added. (Martin Matishak / The Record)
Related: Politico Pro
Palo Alto Networks announced its intent to acquire Portkey.
According to the announcement, Portkey delivers a critical centralized control plane to manage and protect autonomous AI agents, already processing trillions of tokens per month with the low latency required for agent-to-agent communication. (PR Newswire)
Related: sdxCentral, CRN
Best Thing of the Day: A Very Stupid Period That Threatened National Security Has Mercifully Ended
Donald Trump signed a bill to fund much of the Department of Homeland Security, but not its immigration enforcement operations, shortly after the package won final approval in the House, ending the longest agency shutdown in history, leaving DHS without routine funds since Feb. 14.
Bonus Best Thing of the Day: It's Never Too Late to Leave the Dark Side
Wayne Kenney, who masterminded a cyberattack on the town of Auburn, NH, has turned a leaf, graduating magna cum laude with a degree in cybersecurity from Southern New Hampshire University and developing products to protect people from phishing.
Worst Thing of the Day: It's All Stalkerware, Really
Security researcher Mark Esler discovered that an app called Cerberus Anti-theft, sold by LSDroid SRL of Milan, Italy, and available on the Google Play store, is actually stalkerware.
Closing Thought