The new infosec battleground is human: This week's best infosec long reads 5/2/26
Journalist surveillance is a global industry, China retaliated against reporters through surveillance, AI jailbreaking takes a toll on the soul, Fraudsters targeted vulnerable immigrants, DHS has built a vast surveillance system, Memory-safe programming languages are critical to AI attack defense


Full access to Metacurity's curated infosec long reads is available to paid subscribers. Our goal is simple: make it financially viable to keep investing the time and expertise required to find, vet, and contextualize the most important security journalism each week. Free readers will still get highlights, but subscribers will get the complete, deeply curated set.
Please help support Metacurity achieve our goal by upgrading your subscription to gain full access to this issue and all content published on Metacurity, including the archives.
May 2: Taken together, this week’s long reads point to a clear shift in infosec from a discipline focused on systems and software to one increasingly defined by the targeting, manipulation, and surveillance of people, where governments, criminals, and even defenders are all operating in a blurred environment shaped by AI, data aggregation, and psychological leverage.
A few common threads emerge:
First, surveillance is no longer episodic or exceptional—it’s ambient and industrialized. The IFJ and ICIJ pieces show that journalists are being persistently monitored through a mix of spyware, impersonation, and coordinated intelligence tactics, while the WSJ reporting suggests a similar normalization of large-scale surveillance in US domestic immigration enforcement.
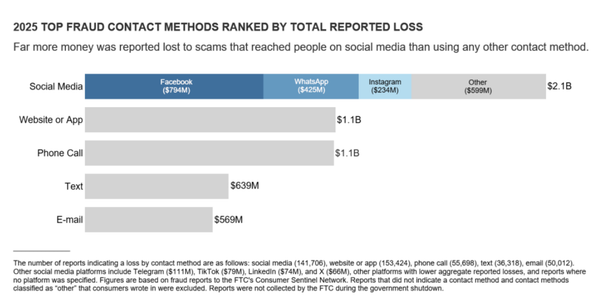
Second, identity has become a primary attack surface. Whether it’s fake journalists targeting reporters, scammers impersonating officials to exploit migrants, or jailbreakers probing AI systems by mimicking malicious intent, the throughline is that trust itself is being systematically weaponized. Technical compromise is often secondary to social and psychological manipulation.
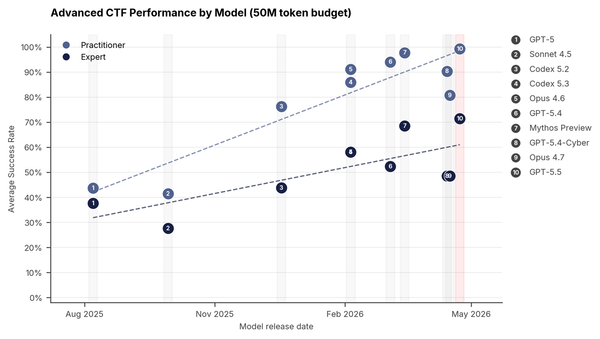
Third, AI is accelerating both offense and defense—but not symmetrically. The Guardian piece shows how even those trying to secure AI systems must immerse themselves in the worst outputs imaginable, while the IEEE Spectrum article highlights how foundational technical fixes like memory-safe code are still catching up to an environment where exploitation can be automated and scaled.
Finally, there’s a growing asymmetry of burden: individuals—journalists, migrants, researchers—are expected to absorb the risk created by these systems. They are the ones being surveilled, deceived, or psychologically strained, while institutions struggle to keep pace or, in some cases, actively contribute to the environment.
Global Surveillance of Journalists: A Technical Mapping of Tools, Tactics, and Threats
For the International Federation of Journalists (IFJ), Samar Al Halal and Lukasz Olejnik report that surveillance of journalists has evolved into a global, systemic industry—combining commercial spyware, state intelligence, and AI-driven data analysis—creating pervasive risks that undermine press freedom and accountability.
Over the past decade, digital surveillance targeting journalists has shifted from scattered, state-run monitoring to a full-fledged commercial industry that spans continents.
This study, commissioned by the International Federation of Journalists (IFJ), investigates the technical infrastructure behind this transformation and the human consequences it produces. Drawing on interviews with cybersecurity experts, forensic analysts and journalists from diverse parts of the world, as well as technical documentation and verified investigations between 2021 and 2025, it paints a detailed picture of how the act of reporting has become intertwined with the risk of being watched, tracked or hacked.
The findings show that surveillance against journalists is now industrial in scale. Sophisticated spyware, once reserved for military intelligence – such as Pegasus, Predator and Graphite – has been repackaged as ‘lawful intercept’ technology and marketed to governments around the world. These tools give their operators the power to penetrate phones and computers silently, reading encrypted conversations, listening through microphones, and extracting data in real time. Pegasus, developed by Israel’s NSO Group, and Predator, a product of the European Intellexa alliance, are among the most well-known examples, but they are only part of a broader ecosystem. Surveillance programmes have been deployed against journalists in democracies and authoritarian states alike. The reasons invoked for these actions are often vague, insufficiently substantiated, or not made public.
Technically, the ecosystem is layered and global. Spyware vendors exploit vulnerabilities in phones and messaging apps, bypassing encryption entirely by taking control of the device itself. Telecom infrastructure adds another dimension: weaknesses in the SS7 and Diameter protocols make it possible to locate, intercept and clone mobile communications without a trace. Deep Packet Inspection and network-injection systems allow service providers or governments to tamper with web traffic, redirecting users to malware-laden sites or filtering entire categories of information. Forensic tools such as Cellebrite and Oxygen Forensics, commonly used in police work, can clone a seized device within minutes, sometimes before reinstalling spyware to maintain long-term access. Increasingly, the data harvested through these mechanisms is fed into artificial intelligence (AI) dashboards that correlate calls, messages, geolocation data, and online activity –automating surveillance at a scale once unimaginable. In conflict zones, AI systems now fuse telecom and drone feeds to identify and track journalists, blurring the line between observation and physical targeting.